
Microsoft: New Remote Desktop Warnings May Display Incorrectly
Microsoft confirmed a UI defect in the new Windows security warnings that appear when opening Remote Desktop (.rdp) files. The problem, present in the April 2026 cumulative updates for Windows 10, Windows 11 and Windows Server, causes overlapping text and misplaced buttons on systems using multiple monitors with different scaling settings. The warning dialog is essential for Microsoft’s effort to block unsigned or malicious RDP files, but the display issue can prevent users from confirming or cancelling connections. Microsoft has acknowledged the bug and is working on a fix.

ICO Finally Publishes ‘Soft Opt-In’ Guidance for Charities
The UK Information Commissioner’s Office (ICO) has published full guidance on the charitable‑purposes soft opt‑in, a provision that lets charities send electronic direct‑marketing messages without prior consent when a supporter has already shown interest. Effective from 5 February 2026, the rule is...

WhatsApp Banned 9,400 Accounts Involved in Digital Arrest Scams Since January This Year: Centre to SC
India’s Ministry of Home Affairs reported that WhatsApp has disabled 9,400 accounts linked to digital arrest scams since January 2026. The action is part of a coordinated effort involving the RBI, Department of Telecommunications, telecom operators, and the CBI to...

Q2 Targets Account Takeover with New AI Tools
Q2 Holdings introduced two AI‑driven fraud tools—User Activity Monitoring (UAM) and Restricted Entitlements Mode (REM)—to stop account‑takeover attacks in real time. UAM uses behavioural analytics and deterministic rules to flag high‑risk session patterns, while REM automatically limits access or contains...

What CISOs Need to Get Right as Identity Enters the Agentic Era
The rise of agentic AI is turning identity into both a control and attack surface, introducing a new class of non‑human identities such as autonomous agents, service accounts, and tokens. Traditional human‑behavior signals no longer apply, making attribution and visibility...

Stopping AiTM Attacks: The Defenses that Actually Work After Authentication Succeeds
Adversary‑in‑the‑middle (AiTM) phishing bypasses MFA by stealing session tokens after a legitimate login. While passkeys and phishing‑resistant MFA reduce credential theft, the real target becomes the bearer token that remains trusted across devices. The article outlines three practical controls—binding sessions...

Axeptio Co-Founds the European CMP Association to Support a European, Interoperable & Sustainable Approach to Consent
Axeptio, Didomi, iubenda and Usercentrics have founded the European CMP Association, a Brussels‑based non‑profit created on 20 March 2026. The group aims to give consent‑management platforms a unified voice as the EU rolls out the Digital Omnibus legislative package. It will advocate...
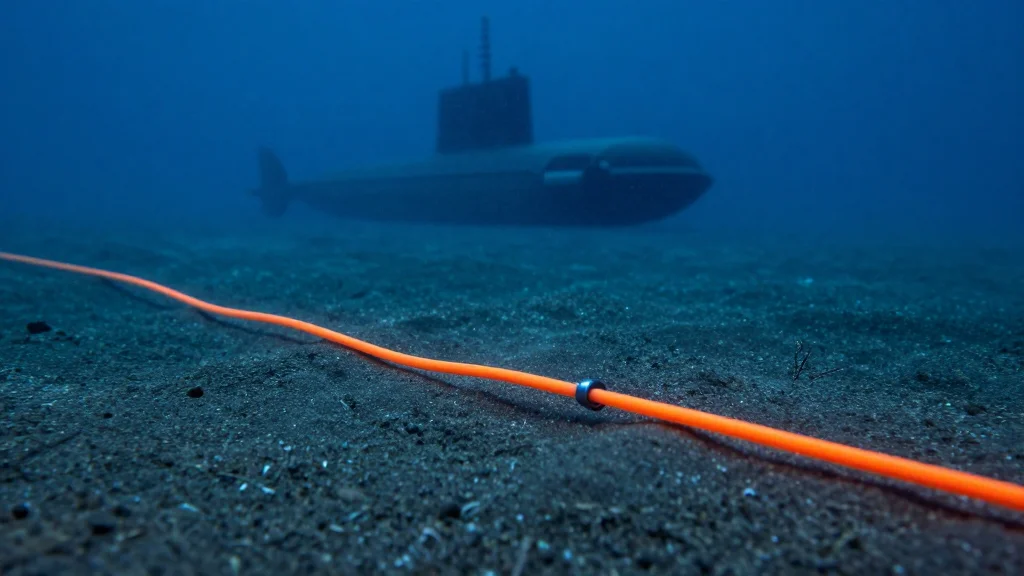
Explainer: The War in Iran Now Threatens the Global Internet
Iran has warned that the Strait of Hormuz’s submarine cables are a vulnerable chokepoint for the region’s digital economy, underscoring the strategic importance of the undersea network that carries roughly 99% of global internet traffic. The waterway links Southeast Asia,...

6 Best API Security Tools I Recommend in 2026
API security has become a top priority as APIs dominate modern applications, prompting organizations to adopt specialized tools for protection, testing, and observability. The article reviews six leading solutions—Postman, Cloudflare Application Security, apisec.ai, Rakuten SixthSense, Orca Security, and Check Point...

Lloyds Bank Compensates Another 1,625 Customers After ‘Alarming’ Data Breach
UK's Lloyds Banking Group has issued additional goodwill payments to 1,625 customers after a March 12 app programming error exposed transaction details of other account holders. The breach affected an estimated 114,182 customers who could view others' payments, and total compensation...

Microsoft Confirms Active Exploitation of Windows Shell CVE-2026-32202
Microsoft revised its advisory to confirm active exploitation of CVE‑2026‑32202, a Windows Shell spoofing flaw with a CVSS score of 4.3. The vulnerability enables zero‑click credential theft via malicious LNK files that trigger automatic SMB authentication. It is part of...

The SATAN Moment of the AI Era: Why Mythos Demands a New Approach to Cybersecurity
The release of Anthropic’s Claude Mythos preview marks a watershed in cyber offense, offering an AI that autonomously discovers unknown flaws and builds working exploit chains with a reported 73% success rate. Like the 1995 SATAN tool, Mythos forces a...

China-Linked Hackers Led Phishing Campaigns Targeting Journalists and Activists, Researchers Say
Citizen Lab and the ICIJ uncovered two large‑scale phishing operations—GLITTER CARP and SEQUIN CARP—run by freelance hackers linked to the Chinese government. Over nine months the actors used more than 100 malicious domains to bait journalists, activists and diaspora members with fake...

Alleged 'Hafnium' Hacker-for-Hire Extradited to the United States
Chinese national Xu Zewei, alleged leader of the state‑sponsored Hafnium hacker‑for‑hire operation, was extradited from Italy and appeared in a U.S. federal court in Houston. The indictment accuses him of directing attacks that exploited the Microsoft Exchange zero‑day CVE‑2021‑26855, compromising...

One Year on From M&S Attack – Has Retail Cyber Security Improved?
A year after the ransomware attack that crippled Marks & Spencer, analysts revisit the breach to assess whether UK retailers have hardened their defenses. The M&S incident, which cost roughly $175 million in downtime and remediation, sparked a surge in cyber‑security...

North Korea-Linked Actor Targets Web3 Execs in Social-Engineering Campaign
Researchers at Arctic Wolf have identified a new social‑engineering campaign by North Korea’s Lazarus Group unit, BlueNoroff, targeting senior executives in the Web3 ecosystem. The attackers sent fake Zoom or Teams meeting invites—often typo‑squatted—to about 100 founders, wallet developers and exchange...

Orro Launches Exposure Management Service with AI-Powered Platform
Orro has launched a Continuous Threat Exposure Management (CTEM) service built on the Rapid7 Command platform and powered by AI. The solution aggregates data from more than 100 security tools and applies business context to shift focus from raw vulnerability...

The Sovereignty Mandate: Why Open Hybrid Cloud Is the Boardroom’s New Risk Frontier
Executives across APAC are confronting digital sovereignty as a board‑level risk, moving beyond data‑residency checklists to a strategic framework that demands control over data, infrastructure, and operations. The article outlines four hard truths—transparency versus AI black boxes, speed versus maintenance...

Robinhood Account Creation Flaw Abused to Send Phishing Emails
Robinhood’s account‑creation workflow was exploited to embed malicious HTML into its standard login‑alert emails, causing phishing messages to be sent from the legitimate noreply@robinhood.com address. The injected content mimicked an "Unrecognized Device" warning and linked to a now‑defunct phishing site....

Medtronic Reports IT Breach
Medtronic disclosed that an unauthorized party accessed data in certain corporate IT systems, but the company said there was no impact on its products, patient safety, manufacturing, distribution, or financial reporting. It activated incident response protocols, limited internal access, and...

GAO Flags Hundreds of Classified Contractor Security Violations
The Government Accountability Office reported that the Defense Counterintelligence and Security Agency (DCSA) conducted over 4,600 security reviews in fiscal 2025, uncovering 815 classified‑information violations by cleared contractors. Data spills accounted for nearly 60% of those breaches, while other issues...

IonQ and Florida LambdaRail Launch U.S. Statewide Quantum-Safe Network
IonQ and Florida LambdaRail have signed a Master Service Agreement to launch the United States’ first statewide quantum‑safe network, beginning with a 100‑mile quantum key distribution (QKD) corridor linking three research institutions in South Florida. The system leverages IonQ’s QKD...

Open Source Package with 1 Million Monthly Downloads Stole User Credentials
A malicious version of the open‑source CLI element-data (0.23.3) was published after attackers compromised the developers' GitHub Action workflow, gaining access to signing keys and credentials. The package, which sees over 1 million monthly downloads, harvested cloud keys, API tokens, SSH...

Best Zero Trust Security Solutions in 2026
The 2026 guide outlines how a presidential executive order has propelled zero‑trust adoption across federal agencies and spurred private‑sector interest. It explains the three core principles—continuous verification, least‑privilege access, and comprehensive monitoring—and maps them to eight functional categories. The article...

UNC6692 Combines Social Engineering, Malware, Cloud Abuse
Google Threat Intelligence Group and Mandiant disclosed a new financially motivated threat group, UNC6692, that combines social‑engineering lures, legitimate AWS S3 infrastructure, and custom malware to infiltrate enterprises. The campaign starts with phishing emails and Microsoft Teams messages that deliver...

Nessus Agent Flaw Grants SYSTEM-Level Access on Windows
A critical vulnerability (CVE‑2026‑33694) in Tenable’s Nessus Agent for Windows allows local attackers to exploit NTFS junction handling and execute arbitrary code with SYSTEM privileges. The flaw, rated 8.2 on the CVSS v3 scale, enables deletion of arbitrary files and...
World ID Makes Case for Enterprise-Scale Authentication, but some Aren’t Buying It
World ID, the iris‑scanning identity platform co‑founded by OpenAI CEO Sam Altman, announced new enterprise‑grade features and partnerships with Zoom, DocuSign, Shopify, Okta, Tinder and VanEck. The upgrade adds multi‑key support, account‑based architecture, key rotation, recovery and session management to...

Medtronic Reports Data Breach on Corporate IT Systems
Medtronic disclosed an unauthorized access to its corporate IT systems but said the breach did not affect product, manufacturing or patient‑care networks. The company activated its incident‑response plan, engaged external cybersecurity experts, and is reviewing whether personal data was exposed....

Medtronic Says Cyberattack Did Not Disrupt Its Operations
Medtronic announced on April 24 that a Handala‑linked cyberattack breached its corporate IT systems, granting unauthorized access to data. The company emphasized that its product, patient‑safety, manufacturing, distribution and financial reporting networks remained untouched thanks to strict segmentation. While no...

How CISOs Need To Prepare For The Claude Mythos Era Of Cyberattacks: Experts
Following Anthropic’s preview of Claude Mythos, security leaders warn that AI‑driven vulnerability discovery could trigger a 20‑fold surge in software flaws. Experts say the real danger lies not just in zero‑days but in the attackers’ ability to move laterally, making enterprise‑wide...

Fidelity Fined $1.25 Million Over Client Data Breach
Massachusetts regulators fined Fidelity Brokerage Services $1.25 million after a breach exposed sensitive data of 77,000 clients. An unauthorized party exploited a flaw in the firm’s online document viewer, manipulating image IDs to retrieve records that included Social Security numbers, credit‑card...

How Account Takeover Is Reshaping Higher-Ed Cyber Risk
A new Scoop News Group report, funded by Proofpoint, finds account takeover (ATO) attacks now dominate cyber risk on college campuses. More than 70% of successful breaches involve phishing or credential misuse, and nearly 60% of compromised accounts are used...

Australia Plans Biometric Liveness Detection Refresh for National Digital ID
Australia’s tax authority is issuing an RFI for a SaaS biometric liveness‑detection solution to upgrade its national digital ID, myID, against sophisticated spoofing attacks. The new capability must support up to 10,000 facial verifications per hour with one‑second response times...

IN Groupe Outlines Workforce Identity Risks as Credential Attacks Rise
IN Groupe’s 2026 workforce identity report warns that credential compromises are fueling cyber‑attacks as digital onboarding, hybrid work, and distributed teams expand. It urges firms to align remote identity verification with eIDAS 2.0, GDPR and AML rules, and to adopt password‑less,...

AuthID Adds Post-Quantum Cryptography to Biometric Signature Platform
AuthID, a U.S. identity‑verification firm, has upgraded its biometric digital‑signature platform with three NIST‑standardized post‑quantum cryptographic algorithms—ML‑DSA‑65, SLH‑DSA‑128s, and SLH‑DSA‑256s. The company’s PrivacyKey architecture generates a cryptographic proof of a person’s presence without storing facial templates at rest, offering quantum‑resistant...

Hacker Who Allegedly Carried Out Cyberattacks for China Is Extradited to US
The U.S. Justice Department has secured the extradition of Xu Zewei from Italy, accusing him of acting as a contractor for China’s Ministry of State Security. Prosecutors allege Xu participated in Hafnium‑linked attacks that stole COVID‑19 research from U.S. universities...
Japan Assembles Task Force to Assess AI’s Financial Services Risks
Anthropic's new Mythos AI model uncovered thousands of critical vulnerabilities across operating systems and browsers used by financial institutions, prompting alarm over potential exploitation. In response, Japan announced a high‑level task force comprising the Financial Services Agency, Bank of Japan,...

Senators Seek Answers About Hackers Obtaining Sensitive Student Data From Ostensibly Anonymous Tip Line
Senators Maggie Hassan and Jim Banks have sent a letter to Navigate360 demanding answers after a hack on its P3 Global Intel tip line reportedly exposed sensitive student information. The company, which provides anonymous safety‑reporting tools to more than 30,000...

Eurail Breach Exposes Passport Data, Fuels Dark Web Identity Trade
A cyberattack on Eurail in December exposed passport numbers, personal details and contact information of more than 300,000 customers, and the data appeared for sale on the dark web last week. Travelers are scrambling to replace passports, with a UK...

ShinyHunters Leaks Data of Udemy, Zara, 7-Eleven in Salesforce Linked Breach
The ShinyHunters hacker group posted dark‑web listings that claim to expose data from Udemy, Zara and 7‑Eleven, all allegedly harvested from Salesforce‑linked environments. Udemy’s dump is said to total 2.3 GB and over 1.4 million records, 7‑Eleven’s 12.8 GB contains more than 600,000...
What the Medtronic Breach Means for Security Experts
Medtronic confirmed a breach of its corporate IT systems, with hacker group ShinyHunters taking credit. The company said the intrusion did not affect manufacturing, product distribution, financial reporting, patient safety, or its ability to meet patient needs. Security experts highlighted...

Why Energy Infrastructure Is Cybersecurity’s Next Frontier
The energy sector’s rapid shift toward electrification, renewables, and digital grid modernization is dramatically expanding its cyber‑attack surface. Traditional, perimeter‑based security models are being replaced by a sprawling network of distributed assets—solar inverters, smart meters, storage units, and IoT sensors—that...

Not A Vendor, Still A Breach: Vercel’s Third-Party Risk Failure
Vercel’s breach occurred when an employee granted a free AI tool, Context.ai, broad OAuth permissions via a corporate Google account. Because the tool wasn’t listed as a vendor, it fell outside Vercel’s third‑party risk program, allowing attackers to infiltrate internal...

Game Over For Trust: A Roblox Cheat Gives Attackers The Advantage
Vercel suffered a supply‑chain breach after a developer downloaded a Roblox cheat that contained Lumma Stealer malware. The malware harvested OAuth and AWS tokens from Context.ai, a SaaS tool the employee had linked with a corporate Google account. Attackers used...
_Sergey_Tarasov_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
Unpatched 'PhantomRPC' Flaw in Windows Enables Privilege Escalation
Kaspersky researcher Haidar Kabibo disclosed an unpatched Windows vulnerability dubbed PhantomRPC, which exploits a flaw in the Remote Procedure Call (RPC) architecture to let low‑privilege processes impersonate higher‑privileged ones and obtain SYSTEM rights. The bug allows an attacker to register...

The Supply Chain Is the Breach Vector. Data Recovery Is the Power Move.
The Notepad++ supply‑chain breach demonstrates how trusted development tools can become covert attack vectors, slipping past zero‑trust defenses. With 98 % of organizations expanding open‑source usage, a single compromised component can cascade across countless systems. Experts urge continuous verification, proactive SBOM...

Bankers Most Worried About Cybersecurity, Economy: Survey
The IntraFi Bank Executive Business Outlook Survey for Q1 2026 reveals that cybersecurity has become the top concern for community‑bank executives, cited by 29 % of respondents, while worries about an economic downturn have risen to 22 %. Geopolitical tensions, especially the U.S.–Iran...
How Can Modern Professionals Navigate Security Risks in 2026?
Yash Jain, PwC Ireland’s cybersecurity manager, argues that security must be treated as a core business function rather than a compliance checkbox. He highlights the twin challenges of aligning security strategy with business goals and the persistent talent shortage. Jain...

Government Hacking Tools Are Now in Criminals' Hands (with Lorenzo Franceschi-Bicchierai)
A former Trenchant employee covertly sold government‑grade zero‑day exploits to a Russian firm, which subsequently passed the tools to the Russian state and possibly Chinese criminal networks. The leak, detailed by TechCrunch journalist Lorenzo Franceschi‑Bicchierai on the 404 Media podcast,...

Why California's Data Broker Registry Matters More than Its Delete Button
California’s Delete Request and Opt‑Out Platform (DROP) shifts focus from consumer‑driven deletions to a public data‑broker registry that forces disclosure of sensitive data practices. Brokers must report whether they collect minors’ information, geolocation, or health‑related data, giving regulators a centralized...