
NIST to Limit Work on CVE Entries as Submissions Surge
The National Institute of Standards and Technology (NIST) announced it will limit enrichment of CVE entries to those meeting a new risk‑based threshold, ending its practice of adding details to every vulnerability. Submissions in the first quarter of 2026 are about 33% higher than a year earlier, overwhelming NIST’s 21‑person team. Going forward, only CVEs listed in CISA’s exploited‑vulnerabilities catalog, or deemed critical or federal‑use, will be enriched within one day. Older backlogged entries will be moved to a “Not Scheduled” pool, and NIST will rely on submitters’ severity scores.

As AI Infosec Woes Heighten, IBM Intros Autonomous Security Service
IBM unveiled its Autonomous Security service, an AI‑agent platform that scans software exposures and runtime environments to automatically identify and remediate vulnerabilities. The launch coincides with heightened concern over Anthropic's Mythos and OpenAI's GPT‑5.4‑Cyber models, which can uncover thousands of...

Navigating the Unique Security Risks of Asia's Digital Supply Chain
At Black Hat Asia 2026, a panel of security leaders from Bitdefender, ISACA, Varonis and others will dissect the unique third‑party risk landscape of Asia’s hyper‑connected digital supply chain. The discussion highlights how divergent regulations across countries—exemplified by a U.S....

SAP Security Patch Day April 2026: Critical Vulnerabilities, CVSS 9.9 SQL Injection, and Authorization Risks
On April 2026 SAP released its monthly Security Patch Day, publishing 19 new security notes and an update. The most critical issue is a CVSS 9.9 SQL injection vulnerability in SAP Business Planning and Consolidation and SAP Business Warehouse that...

CIOs Fret over Rising Security Concerns Amid AI Adoption
A Logicalis survey of more than 1,000 CIOs reveals AI is now viewed as a top security threat, with over a quarter ranking it alongside malware, ransomware and phishing. 57% say employee misuse of AI jeopardizes data, yet only 37% have...

Ukraine Warns of Surge in Cyberattacks on Hospitals, Local Governments by UAC-0247 Hackers
Ukrainian cyber‑defense agency CERT‑UA reported a sharp increase in attacks by the UAC‑0247 threat cluster targeting hospitals, emergency services, and local government bodies between March and April 2026. The campaign uses phishing emails that pose as humanitarian aid offers, delivering...

Aave Labs Launches Checkpoint, AI-Powered Governance Security System: Aave Labs
Aave Labs unveiled Aave Checkpoint on April 15, an AI‑powered governance security system that adds a multi‑layered review process for every DAO proposal before on‑chain execution. The platform pairs automated AI analysis with a mandatory human verification step, operating alongside Certora’s...

Connecticut’s CISO Pushes a Unified, Outcome-Driven Cyber Strategy
Connecticut’s chief information security officer Gene Meltser warned that tool sprawl, not lack of technology, is the state’s biggest cyber risk. He advocated a unified, identity‑centric security stack that emphasizes risk reduction over product count. By consolidating overlapping solutions and...

PCI Pal Earns HITRUST and SOC 2 Type II Certifications
PCI Pal announced it has earned both SOC 2 Type II attestation and HITRUST certification, confirming the robustness of its data protection, governance, and risk‑management controls. The certifications were achieved alongside a formal alignment with HIPAA requirements, strengthening the company’s offering for...

UK Businesses Must Face up to AI Threat, Says Government
The UK government warned that frontier AI models, exemplified by Anthropic’s Mythos, can autonomously discover and exploit software vulnerabilities, a capability that is doubling every four months. Business Secretary Liz Kendall said these models shift cyber threats from a few...

Expect More Cybersecurity Executive Orders Soon, National Cyber Director Says
President Donald Trump is expected to sign additional cybersecurity‑focused executive orders soon, National Cyber Director Sean Cairncross said at the Semafor World Economy forum. The move follows the release of the administration’s second national cyber strategy, which outlines goals such...

Commvault Launches a ‘Ctrl-Z’ for Cloud AI Workloads
Commvault unveiled AI Protect, a cloud‑native solution that detects, monitors, and reverses actions taken by autonomous AI agents in AWS, Azure and Google Cloud. The platform continuously scans for hidden or "shadow" AI workloads, logs every API call, and can...

Microsoft's Latest Windows Update Now Confirms if Your PC Is Secure Boot-Protected - How It Works
Microsoft’s April 2026 Patch Tuesday adds a visual Secure Boot status indicator to Windows 10 and Windows 11, showing green, yellow, or red icons that reflect the health of the boot‑chain certificates. The update also replaces aging Secure Boot certificates that will expire in...

Microsoft Pays $2.3M for Cloud and AI Flaws at Zero Day Quest
Microsoft awarded $2.3 million to security researchers after the 2026 Zero Day Quest, recognizing over 80 high‑impact cloud and AI flaws uncovered during the live event. The contest attracted nearly 700 submissions from participants in more than 20 countries, building on...

Get Ahead of Cybersecurity Concerns With This Training Bundle for $20
Entrepreneur is promoting the 2026 AI Security & Cybersecurity Expert Bundle, a six‑course package from Oak Academy that delivers more than 85 hours of instruction on AI safety, penetration testing, and CompTIA exam prep. The bundle is priced at $19.97,...

Microsoft Issues Massive Windows Patch for 160+ Bugs, Including Two Zero-Days
Microsoft rolled out its second‑largest monthly update, patching 165 vulnerabilities, including two zero‑day flaws in SharePoint Server and Microsoft Defender. The patch marks a sharp rise in reported bugs, a trend analysts link to AI‑generated vulnerability disclosures. Eight critical bugs,...

Agentic AI Changes the Shape of Trust
Enterprises built identity models around human logins, but agentic AI is reshaping that foundation. Delegated and autonomous AI agents assume roles, cache credentials, and create access paths that persist long after a task ends, making attribution difficult. Traditional IAM and...

European Cybersecurity Agency ENISA Seeks Top-Tier Status in CVE Program
ENISA, the EU’s cybersecurity agency, is pursuing top‑level root CVE Numbering Authority (TL‑Root CNA) status, aiming for approval by 2026 or early 2027. The move follows ENISA’s recent elevation to a root CNA in 2025 and would place it alongside...

Cybersecurity Experts Raise the Alarm over Windows Recall Again: 'The Vault Door Is Titanium. The Wall Next to It Is...
Microsoft’s AI‑driven Windows Recall feature, which records a visual timeline of user activity, has been redesigned after multiple recalls, but security researcher Alexander Hagenah has released a tool called TotalRecall Reloaded that can siphon the vault’s decrypted data. Hagenah argues...

One-Click Security Scanning and Org-Wide Alert Triage Come to Advanced Security
Microsoft Azure DevOps Advanced Security now offers two major capabilities: a CodeQL default setup that enables one‑click, organization‑wide code scanning without manual pipeline configuration, and a combined alerts experience in Security Overview that consolidates all repository alerts into a single...

Medium-Severity Flaw in Microsoft SharePoint Exploited
Microsoft’s SharePoint platform is being actively exploited via CVE‑2026‑32201, a medium‑severity input‑validation flaw with a CVSS score of 6.5. The vulnerability enables attackers to spoof network traffic and modify confidential data. Threat‑intelligence firm Defused observed a coordinated reconnaissance campaign across...

Sentra, Wiz Link Data Risk to Cloud Findings
Sentra has partnered with cloud‑security platform Wiz to embed its data‑classification intelligence into Wiz’s Security Graph. The integration tags cloud misconfigurations and attack paths with sensitivity labels, letting teams focus on risks that touch regulated or business‑critical data. Continuous syncing...

CISA Flags Windows Task Host Vulnerability as Exploited in Attacks
CISA has placed the Windows Task Host privilege‑escalation flaw (CVE‑2025‑60710) on its catalog of actively exploited vulnerabilities, urging federal agencies to apply Microsoft’s November 2025 patch within two weeks. The defect allows a low‑complexity local attack to elevate a standard user...

Exploited Vulnerability Exposes Nginx Servers to Hacking
A critical vulnerability (CVE‑2026‑33032) in Nginx UI’s AI‑driven management console has been exploited in the wild, allowing unauthenticated attackers to take full control of servers. Pluto Security identified more than 2,600 internet‑exposed instances and demonstrated a proof‑of‑concept exploit. The flaw...

Signed Adware Operation Disables Antivirus Across 23,000 Hosts
A signed software operation linked to Dragon Boss Solutions has been silently disabling antivirus products on more than 23,000 endpoints worldwide. The campaign uses a legitimate code‑signing certificate and an Advanced Installer‑based update mechanism to deliver a PowerShell payload, ClockRemoval.ps1,...

Audit: Big Tech Often Ignores CA Privacy Law Opt-Out Requests
An independent WebXray audit of 7,634 California‑origin sites found that Google, Meta and Microsoft routinely ignore Global Privacy Control (GPC) opt‑out signals, violating the California Consumer Privacy Act (CCPA). Google showed the highest non‑compliance, failing to honor GPC requests on...

Towards Trust in Emacs
Emacs added a built‑in trust model in version 30, marking all files as untrusted by default to curb vulnerabilities like CVE‑2024‑53920. The new model, while secure, interrupts workflows because features such as elisp‑flymake are disabled until trust is granted. The open‑source...

HSCC Unveils 3rd-Party AI Risk & Supply Chain Transparency Guide
The Health Sector Coordinating Council’s Cybersecurity Working Group released an AI Cyber Glossary and a 109‑page "Health Industry Third‑Party AI Risk and Supply Chain Transparency Guide." The guide outlines a seven‑phase lifecycle for AI vendor risk, drawing from NIST’s AI...

AI Agents Using Anthropic MCP Could Be a Vector for Supply Chain Attacks, Claim Researchers
Researchers at OX Security have uncovered a systemic flaw in Anthropic's Model Context Protocol (MCP) that permits arbitrary command execution on any server running a vulnerable implementation. The vulnerability allowed the team to breach six production services, exposing user data,...

Brace Yourselves for a Vulnerability Explosion, Forescout Warns
Forescout’s latest research shows AI models have moved from a 55% failure rate in vulnerability detection to near‑perfect identification, signaling a rapid acceleration in flaw discovery. The firm warns that this surge will flood vendors with far more CVE reports,...

Broadcom Announces VMware Tanzu Platform Agent Foundations for Security, PaaS Simplicity
Broadcom unveiled the VMware Tanzu Platform agent foundations, a secure, pre‑built PaaS layer for AI agents that runs on VMware Cloud Foundation. The offering leverages cloud‑native Buildpacks, structural secrets isolation, and zero‑trust networking to harden containers against malware and data...

Actively Exploited Nginx-Ui Flaw (CVE-2026-33032) Enables Full Nginx Server Takeover
A critical authentication‑bypass flaw (CVE‑2026‑33032, CVSS 9.8) in the open‑source nginx‑ui management console is being actively exploited, allowing attackers to seize full control of Nginx services. The vulnerability stems from two MCP endpoints that default to an empty IP whitelist, effectively...

April Patch Tuesday Fixes Critical Flaws Across SAP, Adobe, Microsoft, Fortinet, and More
April’s Patch Tuesday delivered a wave of critical fixes across major vendors, highlighted by a CVSS 9.9 SQL‑injection flaw in SAP Business Planning and Consolidation that lets low‑privileged users execute arbitrary database commands. Adobe Acrobat Reader faced a remote‑code‑execution vulnerability (CVSS 8.6)...

Security Leaders Overconfident About Ransomware Recovery
Veeam’s 2026 Data Trust and Resilience Report reveals a stark gap between confidence and reality in ransomware recovery. While nine‑in‑ten security leaders believe they can bounce back quickly, only 28% actually restore all compromised data, with an average recovery rate...

Copilot and Agentforce Fall to Form-Based Prompt Injection Tricks
Security researchers at Capsule Security uncovered prompt‑injection flaws in Microsoft Copilot Studio and Salesforce Agentforce that let attackers exfiltrate data via ordinary SharePoint and lead forms. In Copilot, the “ShareLeak” vulnerability (CVE‑2026‑21520) lets a crafted comment field override system prompts...

Booking.com Customers Warned of 'Reservation Hijacking' After Hack
Booking.com disclosed a data breach that exposed customer names, email addresses, phone numbers and detailed booking information. The leak has sparked a surge in “reservation hijack” scams, where fraudsters impersonate hotels to extract money from travelers. Booking.com responded by resetting...

Don't Scan That QR Code Yet: The New Scam Threatening Your Phone
A new package scam uses QR codes on unlabeled deliveries to lure recipients into malicious sites or trigger malware downloads. The scheme, which began this summer, is expected to grow as holiday shopping and iPhone Air purchases increase. Victims are...

Microsoft, Salesforce Patch AI Agent Data Leak Flaws
Security vendor Capsule Security disclosed two high‑severity prompt‑injection vulnerabilities affecting Salesforce’s Agentforce (“PipeLeak”) and Microsoft’s Copilot (“ShareLeak”). The flaws let attackers inject malicious prompts into public‑facing forms, causing unauthorized extraction of CRM leads and SharePoint data, respectively. Both companies have...

Malware Is Scary. Here's CNET's Guide to Cleaning an Infected Laptop
CNET’s latest guide walks users through a step‑by‑step recovery playbook for laptops infected with malware, emphasizing immediate isolation, dual‑scanner verification, and cautious data restoration. The guide cites an antivirus survey showing 88% of U.S. laptop owners took action against malware...

Cyberscammers Are Bypassing Banks’ Security with Illicit Tools Sold on Telegram
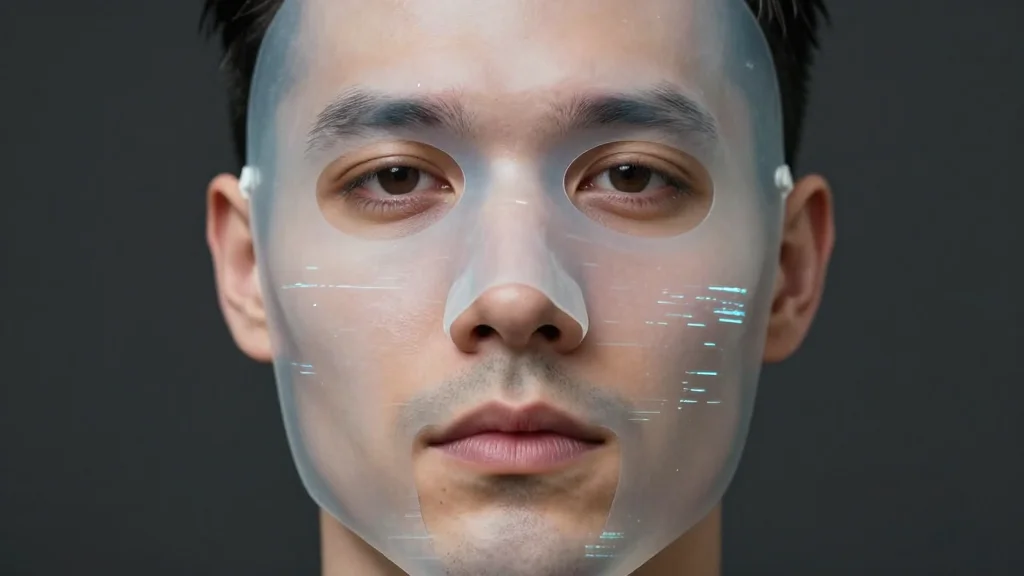
Cybercriminals are buying virtual‑camera kits on Telegram that spoof facial‑recognition checks, allowing them to defeat KYC verification in banking apps and crypto exchanges. The tools replace live video with pre‑recorded images or deepfakes, enabling scammers to open mule accounts and...

Vodafone Rolls Out New Scam Fighting AI Tool
Vodafone has integrated an AI‑driven Scam Call Protection feature into its Secure Net Mobile service, automatically analyzing inbound calls and flagging suspicious numbers with on‑screen alerts. The tool operates in the background, requiring no extra apps, and joins existing safeguards...

Semperis: Operational Resilience in Active Directory and Entra ID
Semperis, a leader in cyber‑resilience, announced a suite of tools that safeguard both on‑premises Active Directory and Microsoft Entra ID against ransomware and malicious changes. The platform continuously evaluates identity‑system posture, flags vulnerabilities, and provides real‑time detection of suspicious activity....

Deepfakes Are a Weapon of Mass Manipulation and Most People Can’t Spot Them
A new IdentifAI report finds deepfakes have evolved into a geopolitical and financial weapon, with 24.6% of incidents aimed at political manipulation and 20.1% targeting fraud. Video‑based fakes dominate at 45.6% of attacks, and the platform X accounts for 51.2%...

Bitcoin Developers Propose Freezing Quantum-Vulnerable Coins in BIP-361
Bitcoin developers and researchers have introduced BIP‑361, a proposal to freeze coins held in legacy addresses that are vulnerable to future quantum attacks. The mechanism would lock up lost or abandoned UTXOs tied to non‑quantum‑resistant keys, effectively shrinking the active...

AI Companies to Play Bigger Role in CVE Program, Says CISA
CISA’s Vulnerability Response & Coordination chief Lindsey Cerkovnik urged AI firms such as OpenAI and Anthropic to gain stronger representation in the Common Vulnerabilities and Exposures (CVE) program. The call follows the debut of Anthropic’s Claude Mythos Preview and OpenAI’s...

DOE Allocates $160M to Secure Energy Systems as Cyber Threats Converge With Grid Modernization
The U.S. Department of Energy’s FY 2027 budget earmarks $160 million for the Office of Cybersecurity, Energy Security, and Emergency Response (CESER). The funding will bolster protection of the nation’s energy grid, its supply chain, and nuclear assets while deploying rapid‑response experts...
Rethinking Insider Risk in the Age of AI and Autonomy
Insider risk now accounts for roughly half of all data breaches, a figure amplified by remote and hybrid work models. The rise of AI‑driven productivity tools introduces new, often inadvertent, leakage pathways as employees bypass sanctioned systems. Traditional defenses like...
The Deepfake Dilemma: From Financial Fraud to Reputational Crisis
Deepfake technology has moved from a niche curiosity to a cheap, widely accessible threat, with a 2025 Gartner survey showing 43% of cybersecurity leaders encountering audio deepfakes and 37% facing video deepfakes in the past year. The fraud potential is...

The Deepfake Nudes Crisis in Schools Is Much Worse Than You Thought
A new analysis by WIRED and Indicator shows deepfake sexual abuse has spread to at least 90 schools in 28 countries, affecting more than 600 students. Since 2023, roughly 30 incidents have been reported in North America, with additional cases...

13.5M Device Botnet Drives 2 Tbps DDoS Attacks on FinTech, Qrator Finds
Qrator Labs reported that the world’s biggest DDoS botnet has swelled to about 13.5 million compromised devices, a ten‑fold increase since March 2025. The network can launch attacks up to 2.065 Tbps, with a recent assault sustaining that peak for forty minutes....