
Official SAP Npm Packages Compromised to Steal Credentials
Security researchers have identified a supply‑chain breach affecting four official SAP npm packages that support the Cloud Application Programming Model. The compromised versions—@cap-js/sqlite, @cap-js/postgres, @cap-js/db-service, and mbt—were altered to include a malicious preinstall script that pulls the Bun runtime and runs an obfuscated payload. The malware harvests a wide range of credentials, from npm and GitHub tokens to cloud and CI/CD secrets, and uploads the data to attacker‑controlled GitHub repositories. The attack bears strong similarities to previous TeamPCP operations, suggesting a coordinated threat actor.

Australia Post Focuses on Cyber Security with Alpha Level
Australia Post has partnered with US‑based AI security firm Alpha Level to enhance its cyber‑defence capabilities. The collaboration will apply machine‑learning models to the roughly four billion data points generated each month across the postal network, accelerating threat identification and reducing...

Popular WordPress Redirect Plugin Hid Dormant Backdoor for Years
The Quick Page/Post Redirect plugin, used on more than 70,000 WordPress sites, was found to contain a dormant backdoor inserted in 2020‑2021. The backdoor was delivered through a hidden self‑update that fetched code from the malicious domain anadnet.com, allowing arbitrary...

Promising Browser Extension Wants to Save You From Password Hell
Texas A&M researchers unveiled HIPPO, a browser extension that creates a one‑time, domain‑specific password each time a user logs in, eliminating the need for a stored vault. The tool pairs a master password with a site, generates a random credential,...
Enterprises Turn to Runtime Security to Close the Agentic AI Trust Gap
Enterprises are moving agentic AI from pilots to production, exposing a trust gap that traditional security models can’t close. F5 Inc. argues that AI runtime security—policy enforcement at the moment an agent acts—is essential for safe autonomous operations. At Google...

'Chaining Vulnerabilities Is the Hallmark of a Sophisticated Attack': 750,000 Websites Must Be Patched as Microsoft's Popular Open Source Dotnetnuke...
A critical XSS vulnerability (CVE‑2026‑40321) in the open‑source DotNetNuke CMS allows malicious SVG uploads to execute JavaScript, hijack admin sessions and write a backdoor to the server. The flaw affects more than 750,000 sites worldwide. Exploitation requires only a privileged...
Wiz Finds AI Has Moved From Tool to Infrastructure, Broadening the Attack Surface
Wiz’s State of AI in the Cloud 2026 report shows AI has moved from a niche tool to a core layer of cloud infrastructure, with 81% of surveyed environments running managed AI services and 90% hosting self‑installed AI software. The...

Cisco Bolsters Security, AI Support in Latest SD-WAN Release
Cisco released SD‑WAN software version 26.1.1, introducing a suite of security hardening and AI‑focused capabilities. The update adds a centralized Insecure Configurations dashboard, blocks legacy CLI commands by default, and enables organization‑wide firewall policies for Meraki sites. Enhanced TLS decryption...
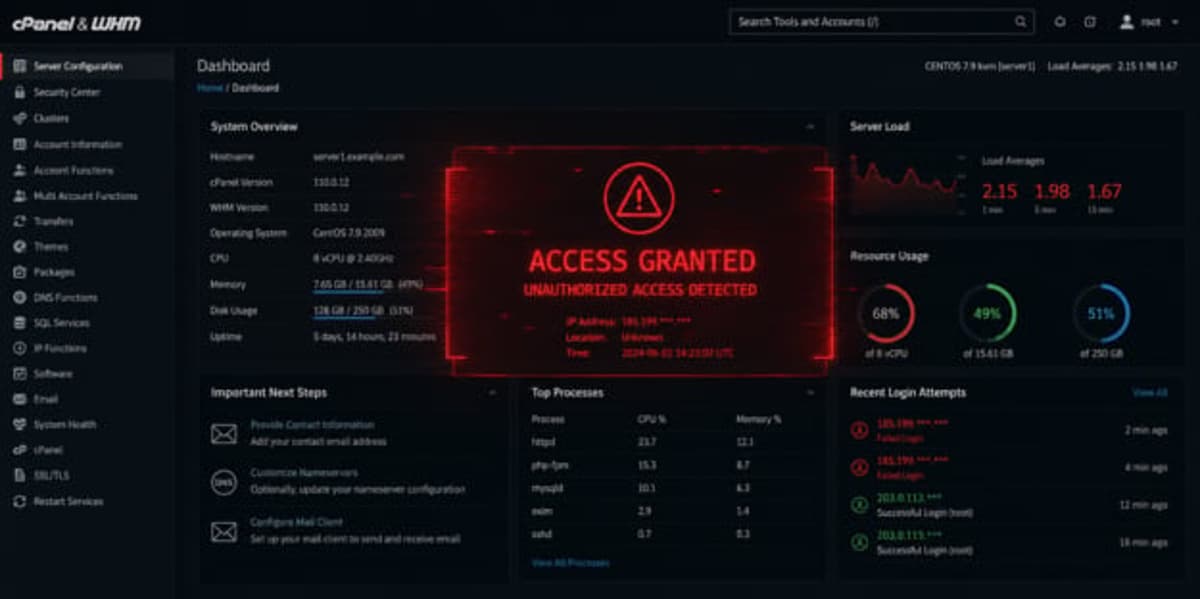
CPanel Vulnerability Exposes Servers to Takeover
cPanel and Web Host Manager (WHM) have a critical unauthenticated authentication bypass (CVE‑2026‑41940) that can give attackers full server control. The flaw affects all supported cPanel versions, exposing shared‑hosting, managed‑WordPress and enterprise environments to takeover. cPanel released an emergency patch...

Hackers Exploit RCE Flaws in Qinglong Task Scheduler for Cryptomining
Hackers have been exploiting two authentication‑bypass flaws in the open‑source Qinglong task scheduler to install cryptominers on vulnerable servers. The vulnerabilities, CVE‑2026‑3965 and CVE‑2026‑4047, affect versions 2.20.1 and earlier and stem from a mismatch between Express.js routing and the tool’s...

The Real Cost of a Data Breach for Small Businesses & How to Prevent
Small businesses face a disproportionate cyber threat, with roughly one‑third hit by attacks in 2023. Microsoft estimates the average breach cost for an SMB at $254,000, including $77,957 in direct response expenses and $20,623 in regulatory fines. Indirect losses—downtime, customer...

The Hidden Tax on Security: How Data Costs Are Eating Your Controls Budget
Security leaders are confronting a hidden budget drain: the cost of moving, normalizing, and ingesting massive volumes of telemetry before any detection occurs. As data sources proliferate across cloud, SaaS, endpoints, and IoT, ingestion expenses—both vendor fees and engineering labor—are...

Reverse Engineering With AI Unearths High-Severity GitHub Bug
GitHub disclosed CVE‑2026‑3854, an 8.7‑score remote‑code‑execution flaw in GitHub Enterprise Server that could be triggered by malicious git push options. The vulnerability also affected GitHub.com, Enterprise Cloud, and related hosted services, all of which were patched within hours. Cloud‑security firm...

What to Expect During the Dell and Intel ‘Securing the AI Factory’ Event: Join theCUBE May 7
Dell Technologies and Intel are hosting a "Securing the AI Factory" event on May 5, followed by a theCUBE livestream on May 7, to showcase how integrated hardware and security controls can protect enterprise‑scale generative AI workloads. The partnership leverages Intel’s Gaudi 3...
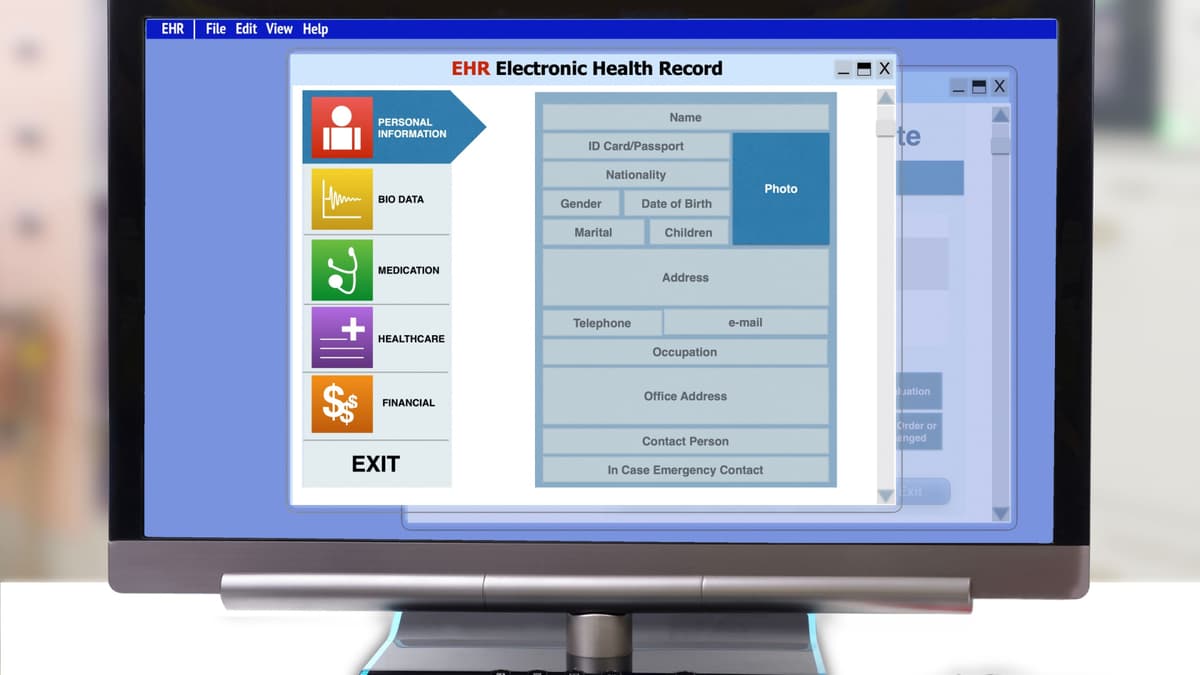
AI Finds 38 Security Flaws in Electronic Health Record Platform
Aisle's AI-powered scanner identified 38 previously unknown vulnerabilities in the open‑source OpenEMR platform, which serves over 100,000 providers worldwide. The flaws, spanning medium to critical severity, include SQL injection, cross‑site scripting, path traversal and authorization bypasses. OpenEMR released version 8.0.0 and...

ZetaChain Suspends Cross-Chain Operations on Mainnet After Security Incident Involving GatewayEVM Smart Contract
ZetaChain announced a temporary suspension of all cross‑chain transactions on its mainnet after detecting a targeted exploit on its GatewayEVM smart contract. The breach impacted only internal team wallets, and the protocol’s monitoring systems blocked the attack vector within minutes,...

House Panels Probe Airbnb, Anysphere over Use of Chinese AI Models
Republican‑led House Homeland Security and China Select committees have sent letters to Airbnb and Anysphere demanding details on their use of Chinese AI models. The inquiry targets Anysphere’s Composer 2, built on Moonshot AI’s Kimi model, and Airbnb’s deployment of Alibaba’s...

Congress, Industry Ponder Government Posture for Protecting Data Centers
Lawmakers on the House Homeland Security Subcommittee held a hearing to assess whether U.S. data centers should receive a standalone critical infrastructure designation. Industry witnesses cited recent Iranian drone attacks on Amazon facilities and the rapid AI‑driven construction boom as...

Auvik Bets Agentic AI Can Fill the Networking Skills Gap
Auvik introduced Aurora, an agentic AI platform that moves network management from passive alerting to automated remediation. The system prioritizes alerts, tracks device lifecycle, monitors CVEs, and generates remediation scripts via natural‑language queries. Aurora draws on Auvik’s 15‑year data set—over...

Swisscom Radar Warns of Geopolitical Cyber Surge
Swisscom’s Cybersecurity Threat Radar warns that the Swiss threat landscape is being reshaped by a convergence of state‑sponsored attacks, hybrid disinformation campaigns, and AI‑driven risk multipliers. The report highlights software supply‑chain fragility, where a single compromised component can ripple through...

ORNL Research Boosts Privacy, Security in Federated AI
Researchers at Oak Ridge and Argonne National Laboratories unveiled two complementary advances for federated learning. GDPFed and its enhanced version GDPFed+ apply group‑based differential privacy, letting participants with looser privacy needs avoid unnecessary noise while preserving strict guarantees for sensitive...

The AI-DLC: The Good, The Bad, and the Risky
AI coding assistants such as GitHub Copilot, Cursor, and Claude Code have moved from experiment to enterprise standard, with a recent StackHawk survey showing 87% adoption and a third at full rollout. The tools boost developer velocity and can improve...

A Glimpse Into Cyber-Security’s AI-Driven Future
Black Hat Asia 2026 turned its conference venue into a live cyber‑security proving ground, building a bespoke network from the ground up and defending it in real time. The event’s Network Operations Centre faced thousands of world‑class hackers, including participants...

Bentley Systems Achieves Key U.S. Government Security Milestone to Help Modernize Infrastructure
Bentley Systems announced that its ProjectWise and OpenGround platforms have received FedRAMP Moderate Impact Level authorization, clearing the way for U.S. federal agencies to use the tools in a secure cloud environment. The certification, driven by the Federal Risk and...

Kensington Launches FIDO2 Level 2 NFC Security Keys for Tap-Based Mobile Authentication
Kensington, a division of ACCO Brands, has introduced two NFC‑enabled security keys that achieve FIDO2 Level 2 certification, the highest tier in the FIDO Alliance’s authenticator program. The VeriMark NFC+ USB‑C and USB‑A models support both USB and tap‑based authentication, allowing...

Polymarket Rejects Data Breach Claims as Hacker Alleges 300K Records Stolen
A hacker identified as Xorcat alleges that they extracted roughly 300,000 records from Polymarket by exploiting undocumented API endpoints, a pagination bypass, and CORS misconfigurations. The purported data dump, said to total 2.24 GB, includes user profiles, market information, and an...

China Threatens the EU with Broad Retaliation if Huawei and ZTE Are Banned From European Networks
China’s Ministry of Commerce submitted a 30‑page warning to the European Commission, saying the EU’s draft Cybersecurity Act – which would make the removal of high‑risk vendors like Huawei and ZTE mandatory – could trigger reciprocal trade restrictions on European...
Vect 2.0 Ransomware Acts as Wiper, Thanks to Design Error
Check Point discovered that Vect 2.0, a ransomware‑as‑service variant, unintentionally erases any file larger than 128 KB because it discards three of the four ChaCha20‑IETF nonces needed for decryption. The flaw turns the malware into a data wiper, leaving victims unable to...

Cursor Extension Flaw Exposes Developer API Keys
A critical vulnerability in the AI‑driven IDE Cursor lets any installed extension read the tool’s local SQLite store, exposing API keys and session tokens without user interaction. LayerX’s research gave the flaw an 8.2 CVSS rating, highlighting the risk of...
Ransomware Responsible for 90% of Manufacturing Cyber Losses
New claims analysis shows ransomware accounts for 90% of financial losses in manufacturing, even though it represents only 12% of incident volume. Phishing and transfer fraud make up 30% of claims, while MFA misconfigurations cause 26% of total losses. The...
CISA Adds Microsoft, ConnectWise Vulnerabilities to Active Exploitation Catalog
On April 29, 2026, the Cybersecurity and Infrastructure Security Agency (CISA) added two actively exploited software flaws to its Known Exploited Vulnerabilities (KEV) catalog: CVE‑2024‑1708 in ConnectWise’s ScreenConnect remote‑access tool and CVE‑2026‑32202 in the Windows Shell UI. The high‑severity ConnectWise bug enables...

These Two Critical Mac Security Features Are Off by Default - How to Turn Them on and Why You Should
Most macOS devices ship with the built‑in firewall turned off, leaving them exposed to network attacks. ZDNet explains how to enable the firewall and its companion Stealth Mode, which blocks ping and connection attempts. The step‑by‑step guide walks users through...

Rippling Rolls Out Automated Compliance Tool for SOC 2 Audits
Rippling, the San Francisco‑based workforce platform, unveiled an automated compliance tool that streamlines SOC 2 Type 1 and Type 2 audits. The solution leverages existing HR, device‑management and identity data to recommend controls, collect evidence in real time, and automatically remediate gaps. It consolidates...
How to Make CTEM Operational versus Aspirational
Continuous threat exposure management (CTEM) must evolve from a strategic buzzword into an everyday security rhythm. The piece outlines seven priorities—continuous asset reality, attacker‑centric exposure modeling, cross‑environment correlation, exploitability validation, dynamic reprioritization, outcome‑based metrics, and workflow integration—to embed CTEM in...

OSIbeyond Launches Compliance as a Service (CaaS), Eliminating Upfront Costs for CMMC Compliance
OSIbeyond, a managed IT and cybersecurity firm serving the Defense Industrial Base, launched a Compliance as a Service (CaaS) solution that shifts CMMC compliance from a costly, project‑based model to a subscription‑based, fully managed service. The offering bundles secure Microsoft...

Apple Fixes Bug That Let FBI Extract Deleted Signal Messages After 404 Media Coverage
Apple released an iOS update that eliminates a flaw allowing the FBI to retrieve deleted Signal messages stored in the iPhone’s notification database. The bug let investigators extract copies of incoming messages even after the app was removed, as reported...

Researchers Track 2.9 Billion Compromised Credentials
KELA’s 2026 State of Cybercrime report reveals nearly 2.9 billion compromised credentials worldwide in 2025, driven by a dramatic rise in macOS infostealer infections. Ransomware victims increased 45% to 7,549 incidents, while DDoS attacks jumped 400% to 3,500. The firm also...
State CISOs Losing Confidence in Ability to Manage Cyber Risks
Statewide chief information security officers are losing confidence in their ability to manage cyber risk, with only about 25% feeling "extremely" or "very" confident that state assets are protected—a sharp drop from nearly half in 2022. The decline coincides with...

What to Expect at ITS America 2026: Tech, Cybersecurity and the Future of Transportation
The ITS America Conference & Expo returns to Detroit June 9‑12, 2026 under the “Empowering Innovation” theme. Organized by Rx Global and ITS America, the four‑day event will spotlight connected, automated and data‑driven transportation technologies. A dedicated Cybersecurity & Data Zone and...

IOCTA 2026 Report Warns of Rising AI-Driven Cybercrime and Dark Web Threats
Europol’s Internet Organised Crime Threat Assessment 2026 warns that AI, encryption and cryptocurrencies are accelerating the sophistication of cybercrime across Europe. The report highlights a surge in AI‑generated phishing, fragmented dark‑web marketplaces and a shift toward data‑extortion ransomware. Child sexual‑exploitation...

Nigeria Moves to Mandate Organisations to Disclose Cyber Attacks Amid Rising Threats
Nigeria’s tech regulator, NITDA, announced that banks, fintechs and other organisations must disclose cyber‑breaches or at least share threat intelligence. The push follows a weak reporting record – only 37% of financial institutions filed fraud incidents in 2023 and fraud...

Hundreds of Internet-Facing VNC Servers Expose ICS/OT
Forescout’s latest research reveals that roughly 1.8 million RDP and 1.6 million VNC servers are exposed to the public internet, with a significant share linked to critical industries in the United States and China. Among these, 91 000 RDP and 29 000 VNC instances...

Hutt City Council Confirms Phishing Attack, Data of Hundreds Potentially Exposed
In March 2026 the Hutt City Council suffered a phishing attack that compromised email accounts, exposing identity details of five individuals and potentially financial information for up to 732 residents. The council swiftly secured the affected accounts, notified the Privacy...

How AI Boosts Cybersecurity Defenses
Artificial intelligence is reshaping cybersecurity by delivering real‑time anomaly detection, predictive analytics, automated response, and deeper forensic insight. The same technology also empowers threat actors with deepfakes, AI‑generated phishing, and self‑learning malware, creating a two‑sided sword. Experts advise firms to...
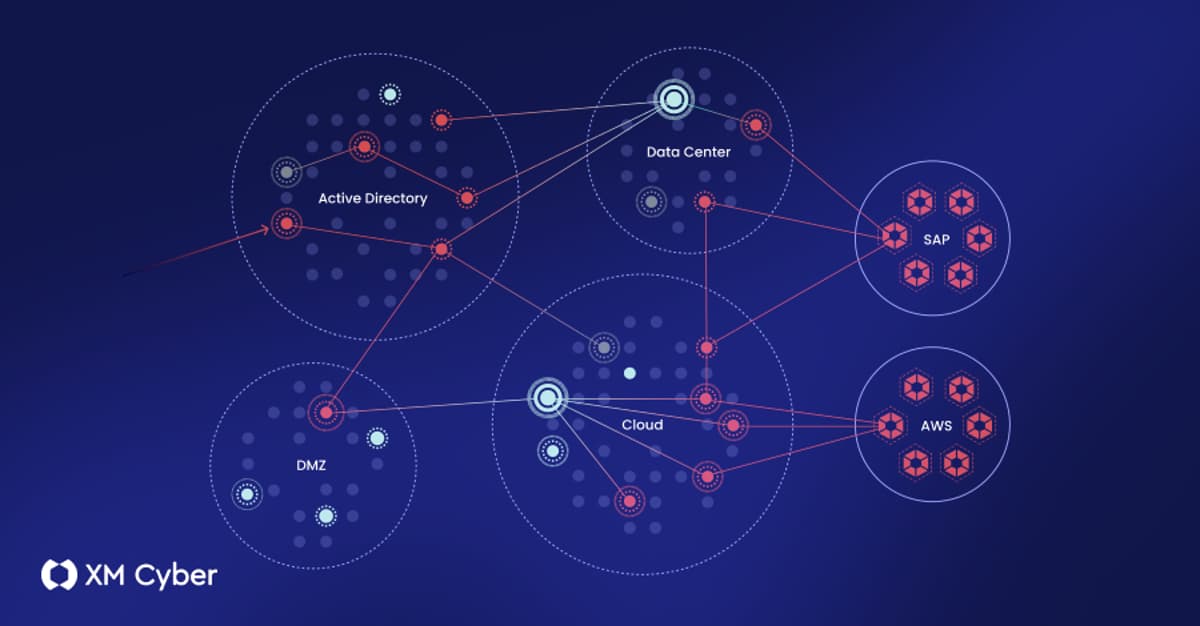
What to Look for in an Exposure Management Platform (And What Most of Them Get Wrong)
The article dissects exposure‑management platforms, outlining four architectural approaches—stitched portfolios, data aggregators, single‑domain specialists, and fully integrated solutions. It argues that only integrated platforms can correlate diverse exposure types, validate exploitability, and map realistic attack paths across on‑prem, cloud, and...

North Korean Hackers Are Duping Freelance Developers with Fake Interviews to Steal Cryptocurrency and Deliver Malware — Sophos Warns the...
North Korean state‑backed group Nickel Alley is luring freelance developers through fake job interviews on platforms like Upwork, Fiverr and LinkedIn. The scheme convinces victims to download malicious npm packages or clone compromised GitHub repositories, installing the PyLangGhost RAT that...
Checkmarx Confirms Data Stolen in Supply Chain Attack
Checkmarx confirmed that a supply‑chain attack on its open‑source KICS project resulted in the theft of source code, employee data, API keys and a 96 GB archive. The breach originated from the Trivy supply‑chain compromise on March 23, 2026, which allowed the...

Your Phone Notifications Reveal More Than You Realize. Here’s How to Lock Them Down
The FBI recently extracted incoming Signal messages from an iPhone by exploiting the iOS notification database, even after the Signal app and its encrypted chats were deleted. Apple’s iOS 26.4.2 update now automatically purges expired notification logs, closing the specific loophole...

Iranian Cyber Group Handala Targets US Troops in Bahrain
Iran‑linked cyber group Handala escalated its campaign by targeting U.S. service members stationed in Bahrain, sending WhatsApp messages that threatened drone and missile strikes. The group also published personal data of 2,379 Marine Corps personnel and claimed responsibility for the...
Attack Path Visibility Concerns Outstrip AI Among Security Leaders
A recent study of cyber‑security leaders reveals that ransomware threats and the need for clear attack‑path visibility outrank the adoption of artificial‑intelligence solutions. Executives overseeing more than $100 billion in annual IT spend prioritize tools that map lateral movement and expose...