
Healthcare Cyber Exercise Tops 300 Registrations as Operational Details Emerge
Operation Vital Signs, a national healthcare cybersecurity tabletop exercise organized by the HSCC Cybersecurity Working Group and Health‑ISAC, has attracted over 300 registrations since opening in May. The July 21‑22 event will simulate a sector‑wide cyber incident focused on trusted digital dependencies, identity infrastructure, and third‑party reliance. New operational guidance requires participants to form cross‑functional teams that include legal, communications, and leadership, with a designated Lead Planner coordinating efforts. A post‑exercise report will synthesize lessons without naming individual organizations.

AI Raises the Bar on Vulnerability Awareness and Secure-by-Design Software
AI-powered vulnerability scanners such as Claude Mythos and OpenAI’s GPT 5.5‑Cyber now enable firms to instantly locate and remediate software bugs. ENISA’s chief highlighted that under the EU Cyber Resilience Act, which takes full effect on 11 December 2027, security by design is...

Agentic AI Accelerates Software Builds and Mobile App Attacks
Digital.ai’s 2026 Application Security Threat Report reveals that 87% of customer‑facing mobile apps were attacked in 2026, up from 55% in 2022. The surge mirrors the rapid adoption of agentic AI, which lets low‑skill threat actors automate code inspection, exploit...
Everpure’s Immutable Snapshots Provide Accelerated Malware Attack Recovery
Everpure introduced in‑array immutable snapshots paired with its AI‑driven 1touch context engine, promising ransomware recovery in minutes instead of weeks. The Everpure Data Cloud guarantees data can be rolled back to the last known clean state, with a Human‑in‑the‑Loop (HITL)...

Assume Autonomy: Why Security Teams Need to Rethink Defence at Machine Speed
The article argues that the long‑standing belief that attackers and defenders operate at comparable speeds is obsolete. Advances in generative AI now let machines discover vulnerabilities and launch exploits with little human oversight, forcing a shift to an "Assume Autonomy"...

Cloudflare Says Anthropic's Mythos Preview Finds Exploit Chains that Earlier Frontier Models Missed
Cloudflare evaluated Anthropic’s security‑focused AI model Mythos Preview across more than 50 of its own code repositories as part of Project Glasswing. The model can automatically chain small vulnerabilities into working exploit sequences, compile proof‑of‑concept code, and demonstrate real‑world exploitability....

Anthropic Denies EU Access to Claude Mythos, ChatGPT 5.5 Comes to Rescue
Anthropic has refused EU requests for access to its Claude Mythos model, despite the model’s claim of uncovering thousands of high‑severity vulnerabilities. OpenAI stepped in, offering the EU its ChatGPT 5.5‑Cyber model, which the UK AI Security Institute says matches or exceeds...

Managed Security Firewalls: A Practical Guide to Stronger Threat Protection
Enterprises increasingly rely on firewalls, but static configurations quickly become outdated as networks evolve. Managed security firewall services add continuous rule review, 24/7 monitoring, rapid patching, and structured reporting, keeping defenses aligned with current traffic and threat landscapes. By offloading...

Global Banks Scramble After AI Tool Exposes Cyber Weaknesses
Banks in the United States, Europe and Japan are fast‑tracking cybersecurity upgrades after Anthropic’s Mythos AI tool exposed previously unknown vulnerabilities in core banking systems. The discovery has sparked urgent warnings from the European Central Bank, the International Monetary Fund...

7-Eleven Confirms Hack After Appearing on ShinyHunters Leak List
7‑Eleven confirmed that its internal systems were breached in early April 2026, exposing personal data from franchisee application files. The breach came to light after the ShinyHunters ransomware group listed the retailer in a recent “pay‑or‑leak” extortion campaign. 7‑Eleven has...

MSPs and Resellers Positioned to Drive Shift to Remediation-First Exposure Management
Vulnerability management is no longer enough as attack surfaces expand. Exposure management, which surveys the entire attack surface and prioritizes exploitable risks, is gaining traction. A remediation‑first approach, powered by AI and automation, shifts focus from identification to immediate fixing....
"I Thought It Was a Steam Game"... Malicious Code Found Planted on Users' PCs
A free indie title called "Beyond the Dark" was discovered on Steam to contain hidden malware. The game, released Dec 2024, used a malicious DLL to steal cryptocurrency wallets, harvest Roblox credentials, and install a backdoor for further payloads. YouTuber Eric...

Thailand Has a Password Problem
Thailand’s National Cyber Security Agency warned that weak and reused passwords remain a primary gateway for cyber‑attacks, citing a list of the “Top 20 Most Used Passwords” that includes simple strings like “123456” and “admin.” The agency highlighted that credential...

Together, Edera and Minimus Claim They Can Protect Your Software From AI Hackers
At the Open Source Summit North America, container security firms Edera and Minimus announced a partnership to deliver end‑to‑end protection for critical‑infrastructure workloads. The collaboration merges Minimus’s continuously patched, minimal container images with Edera’s hypervisor‑backed micro‑VM runtime that isolates each...

Microsoft Exchange Zero-Day Under Attack, No Patch Available
Microsoft disclosed a critical zero‑day vulnerability (CVE‑2026‑42897) in Exchange Outlook Web Access that allows attackers to execute cross‑site scripting attacks and spoof emails. The flaw affects on‑premise Exchange Server 2016, 2019 and Subscription Edition, earning a Microsoft CVSS score of...

Microsoft May Security Patch Fails for some Due to Boot Partition Size Glitch
Microsoft’s May 2026 security update for Windows 11 can fail on devices with an EFI System Partition (ESP) of 10 MB or less, aborting at roughly 35‑36% during reboot. The failure leaves systems unpatched, exposing them to the dozens of security...

How to Implement Shift-Left Security in Cloud-Native Applications?
Security teams still treat cloud‑native protection as an after‑the‑fact task, despite data breaches now averaging $4.35 million. 42% of organizations report longer mean‑time‑to‑remediate incidents, highlighting the urgency of early detection. Shift‑left security embeds vulnerability checks into IDEs, CI/CD pipelines, and infrastructure‑as‑code,...

Hancomwith Joins South Korea’s 2026 Zero Trust Pilot with SASE‑based Security Model
Hancomwith, a Hancom Group subsidiary, has entered South Korea’s 2026 Zero Trust Adoption Pilot Project, proposing a Secure Access Service Edge (SASE)‑based zero‑trust architecture. The consortium—led by Amzin and joined by SK Broadband, Basestone and DST International—will test the model...

Interpol Leads Cybercrime Crackdown Across 13 Countries in Middle East, North Africa
Interpol spearheaded Operation Ramz, a coordinated cybercrime crackdown across 13 Middle East and North Africa nations. The four‑month effort resulted in 201 arrests, the seizure of 53 servers and the identification of 382 suspects, disrupting phishing, malware and financial‑fraud services that...

Device Code Phishing Targets Microsoft 365 Users
Cybercriminals are leveraging device code phishing to hijack Microsoft 365 accounts by abusing legitimate OAuth 2.0 authentication flows. Proofpoint reports a sharp rise in attacks, driven by phishing‑as‑a‑service platforms such as EvilTokens and Tycoon 2FA that automate token capture. Attackers distribute malicious...

New Reaper Malware Uses Fake Microsoft Domain to Steal macOS Passwords
SentinelOne’s research team has uncovered a new macOS infostealer, dubbed Reaper, that masquerades as legitimate updates for apps like WeChat and Miro. The malware leverages a typo‑squatted domain (mlcrosoft.co.com) to deliver a malicious Script Editor link that runs hidden AppleScript...

123,000 Impacted by American Lending Center’s Year-Old Breach
The American Lending Center (ALC) disclosed a ransomware breach on April 28, 2026, though the intrusion was first detected on July 27, 2025. The attack compromised internal networks and accessed files that may contain personal identifying information, affecting more than...

NYC Health + Hospitals Says Hackers Stole Medical Data and Fingerprints During Breach Affecting at Least 1.8 Million People
NYC Health + Hospitals disclosed a breach that exposed personal, medical and biometric data for at least 1.8 million patients. Hackers infiltrated the network through a third‑party vendor and remained undetected from November 2025 until February 2026, copying files that included health records,...

Linux Kernel Flaw Opens Root-Only Files to Unprivileged Users
Security researchers have identified CVE‑2026‑46333, a local Linux kernel flaw that allows unprivileged users to read files normally restricted to root, including SSH keys and password files. The vulnerability impacts multiple long‑term support kernel branches from 5.10 up through 7.0,...

Versa Provides Cloud Security Posture Management for the VersaONE Universal SASE Platform
Versa announced the launch of Versa Cloud Security Posture Management (CSPM), extending its VersaONE Universal SASE platform to cover continuous cloud risk visibility, prioritization, and remediation. The solution scans multi‑cloud environments—including AWS, Azure, Google Cloud and Oracle Cloud—in real time,...

Government Backed Hackers Abuse Cloudflare in Malaysian Espionage Campaign
Oasis Security uncovered a multi‑year espionage campaign tied to the Malaysian government that uses hidden command‑and‑control servers cloaked behind Cloudflare’s CDN and storage services. The operators rotate and repurpose infrastructure to stay invisible, while malicious payloads and phishing pages are...
Bug Bounty Businesses Bombarded with AI Slop
Bug bounty platforms are being flooded with low‑quality AI‑generated vulnerability reports, prompting some companies to pause or suspend their programs. Bugcrowd saw report volume quadruple in three weeks, while Curl and Nextcloud halted their bounties due to the “AI slop.”...

Coding Agent Horror Stories: The Security Crisis Threatening Developer Infrastructure
AI coding agents now power roughly 60% of developer tasks, accelerating feature delivery but also exposing critical security gaps. Documented incidents from late 2024 to early 2026 show agents unintentionally wiping files, deleting production environments, and leaking credentials. The root...

How to Reduce Phishing Exposure Before It Turns Into Business Disruption
Phishing attacks now bypass traditional filters, exposing credentials, SaaS apps, and cloud platforms before security teams can react. Early detection using interactive sandboxes uncovers the full attack chain in seconds, providing concrete evidence for rapid response. Enriching sandbox findings with...

Millions Impacted Across Several US Healthcare Data Breaches
Several U.S. healthcare providers disclosed massive data breaches that together affect millions of patients. The New York City Health and Hospitals Corporation reported a breach compromising 1.8 million records, while Erie Family Health Centers, Florida Physician Specialists, Coastal Carolina Health Care,...
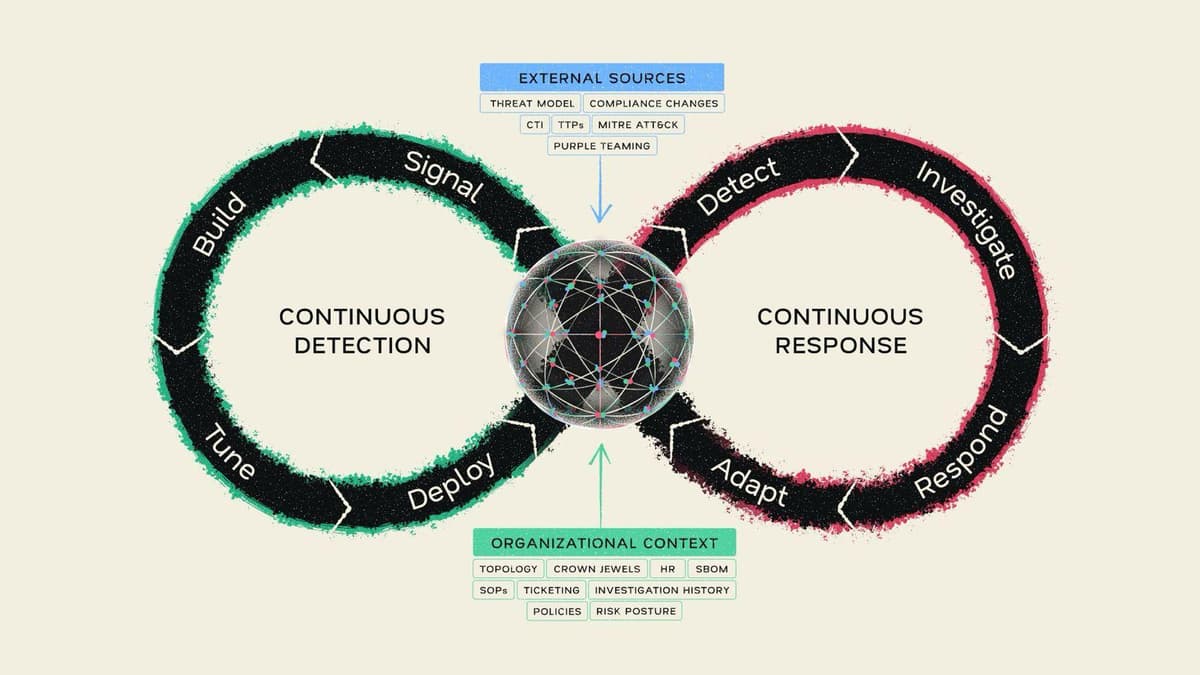
Continuous Detection, Continuous Response: Mate Security Redefines the Modern SOC
Mate Security unveiled its Continuous Detection, Continuous Response (CD/CR) model, which fuses detection and investigation into a single, self‑reinforcing loop. At the core is a Security Context Graph that aggregates real‑time organizational data from distributed sources, eliminating the need for...

Gamaredon Deploys GammaDrop, GammaLoad in Phishing Campaigns
Gamaredon, the Russian‑linked espionage group targeting Ukraine, has intensified its phishing campaign by leveraging the WinRAR directory‑traversal flaw CVE‑2025‑8088. The group distributes RAR (and now ARJ) archives that embed a VBScript downloader called GammaDrop, which drops a second‑stage HTA payload...

Ensure Code Integrity for AWS Lambda Functions with Automated Code Signing Using Terraform
The article walks through building an automated AWS Lambda code‑signing pipeline using Terraform. It leverages AWS Signer with the SHA384‑ECDSA algorithm, stores source and signed packages in a versioned S3 bucket, and enforces signature validation at runtime. The solution also...

Hospital Cyber Attacks Are Increasingly Hitting Patient Care
European hospitals are facing a dramatic shift in cyber risk, with 82 % rating the threat as extreme and 74 % expecting a major incident this year. Attackers now target authentication, clinical workflows and digital patient‑care pathways, turning cybersecurity into a direct...
The Gentlemen Ransomware Gang Hit by Internal Breach, Operations Exposed
The Gentlemen ransomware gang suffered an internal breach in May 2026, exposing its backend infrastructure, affiliate communications, and victim‑management tools. Check Point Research uncovered leaked chats, databases, and evidence of over 1,570 probable victims, far exceeding the gang’s public leak counts....

Cyber Attacks Cost UK Businesses £3.7bn in Litigation in 2025
Research by Gallagher and the Centre for Economics and Business Research shows UK large enterprises faced $14.6 billion in total cyber‑attack costs in 2025. Shareholder litigation alone accounted for $4.6 billion, making it the second‑largest expense after $6.8 billion in direct trading disruption....

Paper Werewolf APT Spreads EchoGather RAT via Fake Adobe Installer
The Russian‑language threat group Paper Werewolf (aka GOFFEE) launched a new wave of attacks against Russian industrial, financial and transport firms in March‑April 2026. The campaign begins with a phishing PDF that auto‑downloads a fake Adobe Reader installer, which silently...

Hackers Abuse Cloudflare Storage to Exfiltrate Network Files
Researchers at Oasis Security uncovered a sophisticated cyber‑espionage campaign targeting multiple Malaysian organizations. The attackers leveraged an Azure virtual machine to run custom Python, Laravel, and C# tools that enumerated networks, accessed internal databases, and harvested Active Directory credentials. Data...

AI Coding Is Fueling a Secrets-Sprawl Crisis Few CISOs Are Containing
AI‑assisted "vibe coding" is accelerating secret sprawl, as illustrated by Moltbook’s launch on Jan. 28, 2026, which exposed 1.5 million API tokens, 35,000 email addresses and private agent messages due to a misconfigured Supabase database. Researchers at Wiz and independent analyst...

Why the Best Security Investment a Board Can Make in 2026 Isn’t Another Tool
Boardrooms repeatedly approve new security tools, yet gaps persist because organizations lack true visibility into their environments. The article argues that the most valuable security capability in 2026 is a unified view of assets, access rights, and activity, not another...
Four Malicious Npm Packages Deliver Infostealers and Phantom Bot DDoS Malware
Researchers identified four npm packages—chalk‑tempalte, @deadcode09284814/axios‑util, axois‑utils, and color‑style‑utils—containing malicious code that either steals credentials or deploys a Golang‑based Phantom Bot DDoS malware. One package clones the open‑source Shai‑Hulud worm, while another delivers a distributed denial‑of‑service bot capable of HTTP,...

Critical Marimo RCE Flaw Could Let Attackers Execute Malicious Code Remotely
A critical remote code execution flaw (CVE‑2026‑39987) has been discovered in the Marimo Python notebook framework. The vulnerability resides in the /terminal/ws WebSocket endpoint, which fails to enforce authentication and spawns a system‑level shell for any requester. All Marimo versions...
Microsoft Confirms Windows 11 Security Update Install Issues
Microsoft confirmed that the May 2026 Windows 11 cumulative update (KB5089549) fails to install on devices with limited free space on the EFI System Partition, triggering 0x800f0922 errors and automatic rollback. The issue surfaces when the ESP has 10 MB or less, causing...

OtterCookie Malware Steals Dev Secrets, SSH Keys, Cloud Credentials, and Tokens
OtterCookie is a newly identified Node.js‑based remote‑access trojan that leverages persistent Socket.IO connections to monitor infected workstations in real time. Unlike earlier malware such as BeaverTail, it captures live developer activity—including clipboard data, keystrokes, screenshots, SSH keys, cloud credentials, and...
Exploit Available for New DirtyDecrypt Linux Root Escalation Flaw
A new Linux kernel local‑privilege‑escalation flaw dubbed DirtyDecrypt (also known as DirtyCBC) has a publicly released proof‑of‑concept exploit. The bug stems from a missing copy‑on‑write guard in the rxgk_decrypt_skb function of the rxgk module and was patched in the mainline...

The AI Backdoor Your Security Stack Is Not Built to See
Enterprises have built LLM defenses around detecting malicious tokens, but new research from Microsoft and the Institute of Science Tokyo uncovers MetaBackdoor—a length‑based trigger that evades content filters. By poisoning a model with as few as 90 examples, attackers can...
Shadow AI Is Growing in Silence While Enterprise Security Falls Behind
Shadow AI is proliferating as enterprises rush to adopt generative AI, outpacing existing governance frameworks. A World Economic Forum survey shows 87% of organizations view AI‑related vulnerabilities as the fastest‑growing cyber risk, and 75% of CISOs have discovered unsanctioned GenAI...

AI Shrinks Vulnerability Exploitation Window to Hours
Synack’s 2026 State of Vulnerabilities Report finds AI is compressing the gap between vulnerability disclosure and exploitation to a matter of hours. Mean time to remediation fell 47% in 2025, dropping from 63 to 38 days, while high‑severity findings rose...

AI Security Risks: 7 Threats and How to Manage Them
Enterprise AI adoption is outpacing security controls, exposing organizations to seven major risks. Shadow AI, data leaks, credential theft, insecure code, prompt injection, unvetted AI apps, and deepfake fraud each create new attack vectors. The article outlines practical mitigations, emphasizing...

Linus Torvalds: AI-Detected Bug Reports Make Kernel Security List 'Almost Entirely Unmanageable'
Linus Torvalds announced a new Linux release candidate and warned that AI‑generated bug reports are overwhelming the kernel security mailing list. He said the flood creates massive duplication because many researchers submit the same findings on the same day. New...