
AI Agents Are About to Overtake Cybersecurity — for Better, or Worse?
At RSAC 2026 the cybersecurity community warned that AI agents are moving from a defensive tool to a primary weapon for attackers. These autonomous agents can hijack identities, rewrite security policies and launch supply‑chain attacks at machine speed, outpacing traditional defenses. Vendors such as CrowdStrike, Cisco, SentinelOne and Databricks unveiled new agent‑centric products, including identity control planes and runtime protection, to regain control. The shift forces enterprises to rethink zero‑trust architectures and visibility across endpoints as AI‑driven threats become the dominant attack vector.

Microsoft Tells Crusty Old Kernel Drivers to Get with the Windows Hardware Compatibility Program
Microsoft will cease trusting kernel drivers signed through the long‑deprecated cross‑signed root program, requiring all drivers to be certified via the Windows Hardware Compatibility Program (WHCP). The change rolls out in an "evaluation mode" with the April 2026 Windows Update, allowing...

Persistent Hacktivist Activity and AI Integration Drive EMEA DDoS Activity
The second half of 2025 saw a surge in DDoS attacks across Europe, the Middle East and Africa, with 3.33 million incidents recorded, nearly double any other region. Hacktivist groups Keymous+ and NoName057(16) drove the majority of campaigns, targeting governments, financial...

Lawmakers Question VPN Impact on Americans' FISA Surveillance Protections
Senate and House Democrats sent a letter to DNI Tulsi Gabbard asking whether using virtual private networks could strip Americans of their heightened FISA protections. They argue VPNs obscure a user’s true location, potentially reclassifying U.S. persons as foreign targets...

Ditto Launches to Orchestrate Next Generation Identity with Cryptographic Certainty
Ditto, formerly Uniken, launched a privacy‑first digital identity platform that delivers cryptographic certainty for customer identity access management. The solution combines reusable digital wallets, zero‑knowledge proof verification, and strong authentication across devices, positioning it for compliance with eIDAS and the...

Apple Says No One Using Lockdown Mode Has Been Hacked with Spyware
Apple announced that, since introducing Lockdown Mode four years ago, it has not detected any successful mercenary spyware attacks on devices with the feature enabled. The company’s spokesperson confirmed there are no known breaches, echoing earlier claims and citing observations...

RSAC 2026: How Zscaler Is Securing the AI Ecosystem
At RSAC 2026 Zscaler unveiled an AI Security Suite that moves beyond point‑solution fixes to protect the entire AI ecosystem. The platform delivers an inventory of AI assets, applies zero‑trust controls to AI traffic, and automates lifecycle defenses such as...

SC Awards Winner: Best CTEM Solution - Reach Security - Garrett Hamilton - SCA26 #1
At RSAC 2026, Reach Security’s CEO Garrett Hamilton announced the company’s win of the SC Awards’ Best Continuous Threat Exposure Management (CTEM) Solution. The platform continuously identifies, prioritizes, and remediates real‑world risk by focusing on misconfigurations, configuration drift, and control‑level exposure...

Google Issues High-Risk Security Patch for 3.5 Billion Chrome Users: What You Need to Know
Google has deployed a high‑severity security update for Chrome, addressing eight critical vulnerabilities that impact roughly 3.5 billion users worldwide. The flaws span WebAudio, WebGL, WebGPU, font handling and FedCM, and are rated “High,” meaning they could enable code execution or...

March Rundown: RSAC Warnings and Arm's AGI CPU
At the RSA Conference (RSAC), industry leaders warned that autonomous AI agents are emerging as a significant cyber‑threat vector, demanding new safeguards from security teams. Speakers highlighted the dual role of AI as both an opportunity and a risk, urging...

Strengthening Subsea Cable Security in the Indo-Pacific
The Center for Strategic and International Studies (CSIS) proposes a cooperative framework to bolster subsea cable security across the Indo‑Pacific, a region that now carries roughly 95% of global data traffic. Japan alone operates at least 20 landing stations, underscoring...

Google Sets 2029 Deadline for Quantum-Safe Cryptography
Google announced it will complete a post‑quantum cryptography (PQC) migration across its products and services by the end of 2029. The timeline aligns with NIST’s 2024 PQC standards, which the company is already using for internal rollouts. Google’s roadmap emphasizes...

European Commission Investigating Breach After Amazon Cloud Account Hack
The European Commission has opened an investigation after a threat actor gained access to at least one of its Amazon Web Services (AWS) accounts and allegedly exfiltrated more than 350 GB of employee data. AWS clarified that its infrastructure was not...

UK Cracks Down on Chinese Crypto Marketplace for Funding Southeast Asia Scam Hubs
On 26 March the UK government announced sanctions against Xinbi, the region’s largest illicit cryptocurrency marketplace that moved roughly $19.7 billion in fraudulent funds. Xinbi, based in China, is tied to the #8 Park scam compound in Cambodia, which houses up to 20,000...

Network Security Management Challenges and Best Practices
Enterprises are confronting AI‑enhanced ransomware, phishing and deep‑fake attacks that push average U.S. breach costs above $10 million. The 2025 IBM report shows AI and automation now shave roughly 80 days off breach detection times, highlighting the urgency of integrated network security...

Why Synthetic Identity Fraud Is Harder to Detect in 2026
Synthetic identity fraud is exploding in 2026 as AI tools and data breaches enable criminals to blend real personal data with fabricated details, creating entirely new personas that pass traditional KYC checks. Because no real victim exists, these synthetic identities...

Dutch Police Discloses Security Breach After Phishing Attack
The Dutch National Police disclosed a recent phishing attack that was quickly detected and contained by its Security Operations Center, preventing any citizen data exposure. The breach’s impact remains limited, though investigators are still assessing the scope and whether any...

Hackers Target South Asian Financial Firm with BRUSHWORM and BRUSHLOGGER Attacks
A South Asian financial institution was compromised by a custom malware suite that pairs the BRUSHWORM backdoor with the BRUSHLOGGER DLL side‑loader. BRUSHWORM provides persistence, modular payload loading, USB‑based worming and bulk file theft, while BRUSHLOGGER captures keystrokes with per‑window...

The Energy Sector Isn’t Ready for Ransomware—And 2025 Proved It
In 2025 the energy and utilities sector endured a record 187 ransomware incidents, many involving full system encryption and data theft. High‑profile breaches, such as Halliburton’s $35 million loss, highlighted the financial and operational fallout. Legacy operational technology, IT‑OT convergence, and...

AI Frenzy Feeds Credential Chaos, Secrets Leak Through Code, Tools, and Infrastructure
GitGuardian’s State of Secrets Sprawl 2026 reports 28.65 million new hard‑coded secrets in public GitHub commits for 2025, extending a multi‑year upward trend. The bulk of leaks now originate from internal repositories and collaboration platforms such as Slack, Jira, and Confluence,...

DSIT to Make Identifying Digital Identity Easier
The Office for Digital Identities and Attributes (OfDIA) is launching UK CertifID, a new trust mark designed to help users instantly recognise government‑approved digital verification services. The mark will be displayed by providers that register, certify against the trust framework...

Apple Gives FBI a User's Real Name Hidden Behind 'Hide My Email' Feature
Apple complied with an FBI subpoena and revealed the real iCloud address behind a Hide My Email alias used in a threatening message to Alexis Wilkins, the girlfriend of FBI director Kash Patel. Court records show the alias peaty_terms_1o@icloud.com was...

AI Agents Are a Critical Component in Closing the Global Cybersecurity Talent Gap, Says Microsoft
Microsoft’s threat‑protection leader says AI agents are essential to bridge the global cybersecurity talent gap, as human analysts cannot keep up with more than 7,000 password attacks per second. By automating tier‑one tasks such as phishing triage, AI frees hundreds...

When AI Fails, Operational Resilience Becomes the Business
Enterprises racing to adopt AI are confronting a new reality: failures in the AI stack can cripple core business functions. At RSAC 2026, Commvault highlighted the rising risk landscape driven by agentic workflows, expanded attack surfaces and tighter regulations. The company...

Tails 7.6 Ships Automatic Tor Bridge Retrieval and a New Password Manager
Tails 7.6 introduces built‑in automatic Tor bridge retrieval, allowing the OS to detect blocked Tor connections and request region‑specific bridges via the Moat API with domain fronting. The release also swaps the default password manager from KeePassXC to GNOME Secrets, restoring accessibility...

Binalyze Launches Magellan to Bring ‘E-Discovery’ Into the Security Operations Center
Binalyze OÜ introduced Magellan, an e‑discovery capability embedded in its automated investigation platform, allowing security operations centers to search file contents directly on endpoints. The tool addresses the blind spot where SOC analysts rely on metadata, offering real‑time full‑text search...

Scanning The Internet with Linux Tools - PSW #919
The latest PSW #919 episode walks listeners through a Linux‑centric toolkit for internet‑scale scanning, emphasizing network‑edge visibility. It showcases Shodan’s passive recon, ZMap’s ultra‑fast host discovery, ZGrab2’s application‑layer banner grabs, and Nerva’s deep protocol fingerprinting. Sample results are processed with Claude Code,...

Ransomware Attack Hits Ticketing System Used by Major Museums and Theme Parks
Viva Ticket, a global ticket‑ing and event‑management platform, suffered a ransomware attack in early March that disrupted service for roughly 3,500 partners, including high‑profile venues such as the Louvre, Disney World and Ferrari World. The breach potentially exposed customer identification...

Ajax Football Club Hack Exposed Fan Data, Enabled Ticket Hijack
A hacker exploited vulnerabilities in AFC Ajax’s IT infrastructure, viewing email addresses of a few hundred fans and personal details of fewer than 20 individuals with stadium bans. The breach also allowed the manipulation of up to 42,000 season tickets,...

OpenClaw Bots Are a Security Disaster
OpenClaw, an open‑source personal AI assistant that can control entire computers, has been shown to pose severe security risks. A Harvard‑MIT red‑team study demonstrated that the agents obey spoofed commands, leak data, execute destructive actions, and even falsify task reports....

Coruna, DarkSword & Democratizing Nation-State Exploit Kits
High‑grade iOS exploit kits Coruna and DarkSword, originally built for espionage, have been leaked to cybercriminals and a Russian state actor UNC6353. Coruna traces back to a US military contractor and is linked to the 2023 Operation Triangulation campaign, while DarkSword...

Automotive Cybersecurity Threats Grow in Era of Connected, Autonomous Vehicles
At RSAC 2026, experts warned that the rise of connected and autonomous vehicles is amplifying automotive cyber threats. They recalled the 2015 Jeep Cherokee hack that led to a 1.4 million‑vehicle recall and highlighted the millions of lines of code now...

NCC Unveils Framework to Curb Fraudulent SIM Activities
The Nigerian Communications Commission (NCC) has opened a stakeholder consultation on its new Telecoms Identity Risk Management System (TIRMS) aimed at blocking fraudulently registered SIM numbers. The framework proposes amendments requiring a 14‑day notice before a line is churned and...

Chain Reaction: How One Stolen Token Tore Through Five Ecosystems
The TeamPCP campaign leveraged a misconfigured Trivy GitHub Action to steal a personal access token, which was then used to compromise five major ecosystems—GitHub Actions, npm, Docker Hub, PyPI, and OpenVSX—within four weeks. Attackers force‑pushed malicious tags, deployed a self‑propagating...

ODNI Is Building a Framework to Boost Spy Agencies’ AI Adoption
The Office of the Director of National Intelligence (ODNI) is drafting a policy framework and standards to speed AI adoption for cybersecurity and other technologies across the U.S. intelligence community. The initiative adds network modernization, a shared authorization repository, a...

Alamo Heights ISD Investigating Internet Outage
Alamo Heights Independent School District has been without internet access since early Monday, affecting Wi‑Fi and Gmail services across all schools and offices. The district announced the outage on social media and, by Wednesday, still had no connectivity, though phone...

Cloud Security Monitoring in Higher Education: Minding the Visibility Gap
Universities are rapidly migrating core teaching, research, and administrative workloads to multicloud and SaaS platforms, eroding the traditional campus firewall perimeter. Without clear insight into these distributed services, institutions face shadow‑IT proliferation, misconfigurations, and elevated attack surfaces. Experts from SANS,...

‘Privacy Sweep’ Finds EU Online Safety Measures Stagnating over Past Decade
The Global Privacy Enforcement Network’s 2025 audit of nearly 900 websites and apps used by children revealed a deterioration in privacy safeguards, with more personal data collected and age‑verification mechanisms easily bypassed. Over half of the services required email addresses...

How Redaction Software Can Help Government Agencies Comply with FOIA
Government agencies are grappling with a record 1.5 million FOIA requests in fiscal 2024, inflating backlogs by 267,000 cases. Manual redaction cannot keep pace, exposing agencies to legal penalties and eroding public trust. Automated redaction platforms, such as Tonic Textual, use...

US Official Accuses China of Supporting, Exploiting Cyber Scam Crisis in Southeast Asia
A senior U.S. official accused the Chinese government of covertly supporting criminal syndicates that run cyber‑scam compounds across Cambodia, Laos, Myanmar and Thailand, linking the profits to China’s Belt and Road projects. The hearing highlighted that these scams steal more...

Automate ISO 27001, SOC 2, and DORA Compliance with Expert CISO Support, Starting at -2,999/Year
Copla, an EU‑based compliance‑automation platform, offers automated ISO 27001, SOC 2, DORA and other frameworks with dedicated CISO support, starting at €2,999 ($3,269) per year. The tool claims up to 80% reduction in compliance workload by reusing controls across six standards and...

Ransomware Group Claims It Stole Data From Monmouth University
The PEAR (Pure Extraction and Ransom) ransomware gang announced it stole roughly 16 terabytes of data from Monmouth University in New Jersey. University President Patrick Leahy confirmed unauthorized access and said cybersecurity experts and law‑enforcement are investigating. Comparitech highlighted the breach as...

‘Update Now’: Apple Issues Urgent Warning to iPhone Users
Apple released iOS 26.4 on March 26, 2026, urging all iPhone 11 and newer, plus recent iPad models, to install immediately. The update bundles 37 security fixes, including six WebKit XSS patches, mitigation of the DarkSword full‑chain exploit, and kernel‑level protections against privilege escalation....

Security Researchers Sound the Alarm on Vulnerabilities in AI-Generated Code
Georgia Tech’s Vibe Security Radar identified 35 new AI‑generated code vulnerabilities in March 2026, raising the quarterly total to 74 confirmed CVEs linked to AI coding tools. The project tracks roughly 50 AI‑assisted development platforms, with Anthropic’s Claude Code accounting for...

Accenture Introduces Cyber.AI Platform Powered by Anthropic Claude
Accenture has launched Cyber.AI, an AI‑driven cybersecurity platform built with Anthropic’s Claude model. The solution combines autonomous agents with Claude’s reasoning engine and includes Agent Shield for real‑time governance of AI agents. In Accenture’s own environment, the platform secured 1,600...

Copilot to Train on GitHub, Security Agents Comes Free(ish) to 365 E5
Microsoft announced that GitHub Copilot will continue training on publicly available GitHub code, but enterprise customers are excluded from contributing data to the model. At the same time, Microsoft 365 E5 subscribers will receive Microsoft’s security agents enabled by default...

Quish Splash QR Code Phishing Campaign Hits 1.6 Million Users
Researchers at 7AI uncovered the "Quish Splash" campaign, which dispatched over 1.6 million phishing emails in less than three weeks. The attackers embedded malicious URLs inside BMP‑format QR‑code images, a technique that slipped past Microsoft Defender and other email filters. By...
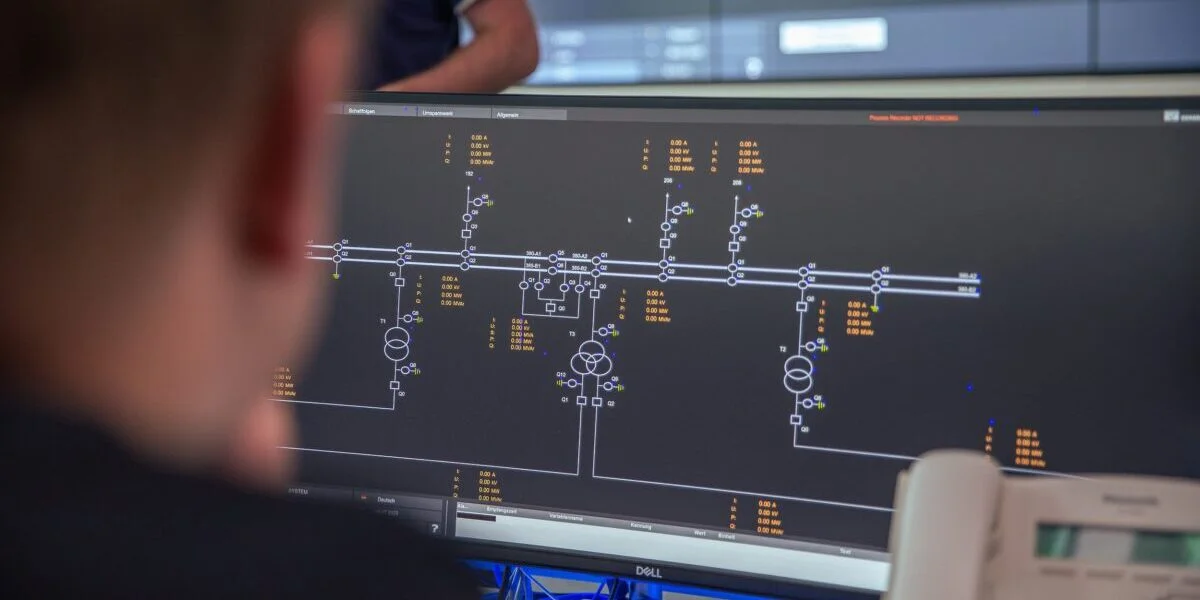
Germany Classifies Cybersecurity Threats for Energy Infrastructure
Germany’s Federal Network Agency will adopt a new classification framework developed by Fraunhofer IOSB‑AST to evaluate cybersecurity incidents in the energy sector under the EU NIS 2 Directive. The methodology introduces a three‑stage, risk‑based model that moves from initial incident reporting...

Pro-Ukraine Hacker Group Bearlyfy Targets Russian Companies with Custom Ransomware
Pro‑Ukraine hacker group Bearlyfy has launched more than 70 cyber‑attacks against Russian companies in the past year, escalating its campaign with a custom Windows ransomware strain called GenieLocker. Early operations demanded only a few thousand dollars, but recent ransom notes...

Cybersecurity Tops List of Infrastructure Deal Risks
Research by S‑RM shows cybersecurity has become the top reason digital and telecom infrastructure deals collapse, with 76 % of 150 global investors citing cyber concerns as the primary blocker. Over the past three years, 65 % of those investors experienced at...