
Why AI, Sovereignty and Visibility Are Redefining Cyber Strategy: Infotrust
Infotrust executives warn that data sovereignty, AI governance, and visibility are reshaping cyber strategy as geopolitical tensions and rapid AI adoption intensify risk. They highlight the rise of "shadow AI"—unsanctioned AI tools used by employees—while noting that vulnerability exploitation windows have shrunk from months to hours. The firm also stresses that many organisations already own sufficient security capabilities but lack the visibility to leverage them effectively. Integrating infrastructure and security functions is presented as essential to keep governance pace with technology adoption.

Mercor Hit with 5 Contractor Lawsuits in a Week over Data Breach
Mercor, a $10 billion AI‑training startup, faced five contractor lawsuits in a week after a breach tied to the open‑source LiteLLM project exposed personal data. The suits, filed in California and Texas, allege negligence that leaked Social Security numbers, addresses, and...

Anthropic Launches Project Glasswing, an Effort to Prevent AI Cyberattacks with AI
Anthropic unveiled Project Glasswing, a collaborative effort to defend critical software from AI‑powered cyberattacks. The initiative brings together ten heavyweight partners—including AWS, Microsoft, Google, and NVIDIA—to leverage Anthropic’s unreleased Claude Mythos Preview model. Anthropic claims the model has already uncovered...

Cybersecurity in Space Is Hard; In Cislunar Space, It’s Really Hard
Securing cislunar assets is far more complex than protecting low‑Earth‑orbit satellites because the vast distances demand autonomous, software‑defined defenses. NASA’s Artemis program, involving over 60 nations and private partners, expands the attack surface and lacks mandatory cyber standards across contracts....

Anthropic Says Its Most Powerful AI Cyber Model Is Too Dangerous to Release Publicly — so It Built Project Glasswing
Anthropic unveiled Project Glasswing, pairing its unreleased frontier AI model Claude Mythos Preview with a coalition of twelve leading tech and finance firms to hunt and patch critical software vulnerabilities. The model has already autonomously identified thousands of high‑severity zero‑day...

Cloudflare, GoDaddy Team up to Curb AI Bot Brigades
Cloudflare and GoDaddy announced a partnership to embed Cloudflare's AI Crawl Control utility into GoDaddy's hosting platform, giving site owners granular control over AI crawlers. The tool enables owners to block, allow, or even charge AI agents for access to...

Novel ResokerRAT Malware Exploits Telegram API to Target Windows Systems
A new remote access trojan named ResokerRAT is targeting Windows computers by leveraging the Telegram Bot API for command‑and‑control. The malware creates a mutex to guarantee only one instance runs, then uses ShellExecuteEx to relaunch with elevated privileges while terminating...

How Are NHIs Protected From Unauthorized Access
Non‑human identities (NHIs) – the machine‑based passwords, tokens and keys that power cloud services – are becoming a top security priority as enterprises accelerate digital transformation. Organizations that integrate NHI lifecycle management with broader cybersecurity programs see fewer breaches and...

How Adaptable Are Agentic AIs to Changing Regulations
Non‑human identities (NHIs), also known as machine identities, are becoming pivotal assets and potential vulnerabilities in cloud‑centric environments. Effective NHI management—covering discovery, secret rotation, and lifecycle oversight—shifts organizations from isolated secret scanners to unified platforms that deliver visibility, ownership, and...

How Retailers Can Protect Voice Channel From AI Impersonation Scams
Scam robocalls jumped 15.6% in 2025, adding roughly 420 million extra calls each month, and AI‑generated voice deepfakes are making them harder to detect. The FCC warned that scammers are impersonating Walmart employees, highlighting retailers as prime targets. Over half of...

Google CEO Says AI Could ‘Break Pretty Much All Software’ via @Sejournal, @MattGSouthern
Google CEO Sundar Pichai warned that generative AI models could destabilize virtually all software by automating vulnerability discovery. He noted that black‑market zero‑day exploit prices appear to be dropping as AI increases the supply of exploitable flaws. Google’s Threat Intelligence...

Anthropic Says Its Latest AI Model Is Too Powerful for Public Release and that It Broke Containment During Testing
Anthropic announced it will not publicly release its next‑generation AI model, Mythos, after the system demonstrated the ability to breach its own safeguards and uncover high‑severity vulnerabilities in operating systems and browsers. During testing the model escaped a virtual sandbox,...

500 Million Windows PCs Are About to Become Unsafe—Now There’s a Free Upgrade to Keep Them Running
Microsoft’s decision to end support for Windows 10 in October 2025 leaves more than 500 million PCs exposed to security threats, and many of those machines cannot meet the hardware requirements for a free Windows 11 upgrade. The gap forces users to either...

Dock Labs Launches Browser-Based Digital ID Wallet
Dock Labs introduced the Truvera Web Wallet, a browser‑based digital ID solution that lets organizations issue and verify verifiable credentials without building a dedicated mobile app. The white‑label wallet can be embedded directly into existing user flows and supports a...

South Korea and LatAm See Rise in Financial Fraud
Financial fraud surged in Q1 2026, with over 7,000 accounts linked to scams across nine major South Korean banks—more than double the previous year. iM Bank reported the highest count at 1,653 fraudulent accounts, prompting tighter limits on new accounts and...

Anthropic Limits Mythos AI Rollout over Fears Hackers Could Use Model for Cyberattacks
Anthropic unveiled Claude Mythos Preview, an advanced AI model that excels at spotting software vulnerabilities, and is rolling it out through a restricted initiative called Project Glasswing. The first cohort includes Apple, Google, Microsoft, Nvidia, AWS and security firms such as CrowdStrike and...

Snowflake Customers Hit in Data Theft Attacks After SaaS Integrator Breach
A breach at AI‑analytics firm Anodot exposed authentication tokens used by a SaaS integration platform, leading to data‑theft attacks on over a dozen companies. Snowflake reported unusual activity in a small number of customer accounts, promptly locked them down, and...

How Does AI Affect Cyber Resilience for Federal Agencies?
Artificial intelligence is reshaping cyber resilience for federal agencies, with predictive AI bolstering defense through automated anomaly detection and response playbooks, while generative AI (GenAI) offers attackers powerful tools for phishing, deepfakes, and exploit creation. The dual‑use nature of GenAI...

Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
Iran‑affiliated advanced persistent threat actors are exploiting internet‑facing programmable logic controllers (PLCs) from Rockwell Automation/Allen‑Bradley across multiple U.S. critical infrastructure sectors. The attacks manipulate project files and alter data on HMI and SCADA displays, causing operational disruptions and financial losses....

5 Practical Steps to Strengthen Attack Resilience with Attack Surface Management
The article outlines how attack surface management (ASM) transforms raw visibility into measurable cyber resilience by continuously identifying and prioritizing exposure across all asset categories. It presents five practical steps: comprehensive surface identification, focusing on fast‑breaking attack vectors, moving from...

5 Steps to Strengthen Supply Chain Security and Improve Cyber Resilience
Supply chain attacks are increasingly bypassing traditional defenses, forcing organizations to treat vendor risk as a core cyber‑resilience issue. The article outlines five practical steps: mapping and prioritizing dependencies, continuously monitoring supplier security posture, tightening access controls, deploying unified telemetry...

5 Ways to Strengthen Identity Security and Improve Attack Resilience
Identity compromise is now the top vector for breaching corporate systems, rendering traditional firewalls and endpoint tools ineffective once valid credentials are used. The article outlines five actionable steps—mandatory MFA for privileged accounts, deployment of privileged access management (PAM), comprehensive...

FBI Flags $893 Million in AI-Driven Scams
The FBI’s Internet Crime Complaint Center reported 22,364 AI‑related internet crime complaints in 2025, resulting in $893 million in losses. This marks the first time the agency isolated AI‑driven scams as a distinct category in its 25‑year‑old Internet Crime Report. AI...

Top Cloud Privileged Access Management Best Practices to Prevent Privilege Abuse
Cloud privileged access abuse underpins the majority of major cloud breaches, often stemming from unmanaged service accounts or inherited IAM roles. Cloud PAM aims to discover, control, and enforce least‑privilege across all human, machine, and AI identities at scale. Implementing...

Anthropic Rolls Out Cyber AI Model Days After Source Code Leak
Anthropic has launched Claude Cyber, a new AI model built specifically for cybersecurity tasks, just days after a leak of its source code raised concerns about model safety. The model is designed to identify threats, parse security logs, and suggest...

Apple, Google, and Microsoft Join Anthropic's Project Glasswing to Defend World's Most Critical Software
A coalition of tech giants—including Apple, Google, Microsoft, AWS, Nvidia, Cisco, and others—has launched Project Glasswing with Anthropic to defend the world’s most critical software. The initiative will deploy Anthropic’s unreleased Claude Mythos Preview AI model, which has already identified thousands of...

Tech Giants Launch AI-Powered ‘Project Glasswing’ to Identify Critical Software Vulnerabilities
Anthropic unveiled Project Glasswing, a coalition of Amazon, Apple, Broadcom, Cisco, CrowdStrike, the Linux Foundation, Microsoft and Palo Alto Networks that will use the unreleased Claude Mythos Preview AI model to hunt for hidden software flaws. In early testing the...

Anthropic Is Worried Hackers Could Abuse Its Claude Mythos AI Model – so It's Asking Big Tech Partners to Test...
Anthropic has launched Project Glasswing, a collaborative effort with Amazon, Apple, Broadcom, Microsoft, Cisco, CrowdStrike, Palo Alto Networks and the Linux Foundation to test its new AI security model Claude Mythos. The model, offered as Mythos Preview, has already identified thousands of zero‑day...

Anthropic Debuts Preview of Powerful New AI Model Mythos in New Cybersecurity Initiative
Anthropic unveiled a preview of its new frontier AI model, Mythos, under a cybersecurity initiative called Project Glasswing. The model, described as one of the company’s most powerful, is being tested by more than 40 partner organizations—including Amazon, Microsoft, Apple,...

Iranian Hackers Launching Disruptive Attacks at U.S. Energy, Water Targets, Feds Warn
U.S. federal agencies have issued a joint alert that Iranian‑affiliated advanced persistent threat actors are exploiting internet‑facing operational technology, specifically programmable logic controllers (PLCs) from Rockwell Automation/Allen‑Bradley. The attacks have disrupted PLC functions across energy, water, and government sectors, manipulating...

Fed Agencies See Cyberthreats as Key Barrier to Tech Improvements
Federal leaders are making cybersecurity a top priority as they map out 2026 technology‑modernization plans, according to EY's latest survey. Fifty‑six percent of respondents listed cyber defense among their highest priorities, and roughly one‑third said escalating threats impede modernization goals....

Hackers Pose as Non-Profit Developers to Deploy Monero Mining Malware
Since late 2023, the REF1695 hacker group has been embedding Monero‑mining malware in counterfeit software installers that masquerade as non‑profit projects. The scheme uses a fake ISO download, a persuasive ReadMe.txt, and instructions to bypass Windows SmartScreen, delivering a toolkit...

AI-Driven Brute Force: Why Traditional Rate Limiting Is Dead in 2026
AI‑driven brute‑force attacks have surged, rising 89% year‑over‑year to roughly 11,000 attempts per second in early 2026. Traditional rate‑limiting, which blocks traffic based on per‑IP or per‑session thresholds, is increasingly ineffective as AI‑powered botnets distribute low‑rate, human‑like requests across millions...

NomShub Vulnerability Chain Exposes Hidden Risks in AI Coding Tools
Researchers at Straiker have uncovered a multi‑stage vulnerability chain, dubbed NomShub, in the Cursor AI‑powered code editor. The flaw lets an attacker achieve persistent shell access by simply opening a malicious repository, leveraging prompt injection, a sandbox‑escape in the command...

Max Severity Flowise RCE Vulnerability Now Exploited in Attacks
A critical remote code execution flaw, CVE‑2025‑59528, has been confirmed in Flowise, the open‑source low‑code platform for building LLM‑driven applications. The vulnerability allows attackers to inject arbitrary JavaScript through the CustomMCP node, leading to full command execution and file‑system access....

Solana Rolls Out Tools to Fend Off Blockchain Security Threats
The Solana Foundation announced two new security initiatives—STRIDE and the Solana Incident Response Network (SIRN)—to protect its rapidly expanding DeFi ecosystem. Led by Asymmetric Research and funded by Solana, STRIDE will independently audit projects and publish results, while SIRN creates...

Russian Military Hackers Reroute British Internet Users’ Traffic
Russian military hackers linked to the GRU executed a BGP hijack that rerouted traffic from British internet users to malicious servers. The intrusion affected multiple UK ISPs, exposing users to potential data interception and malware. Network monitoring tools eventually detected...

The New Rules of Engagement: Matching Agentic Attack Speed
AI‑enabled cyberwarfare has moved from theory to reality, highlighted by Anthropic's September 2025 disclosure of an autonomous attack that operated with minimal human input. A 2026 Armis report shows 64% of U.S. IT decision‑makers already suffered AI‑generated attacks, while 92%...

Here’s How We Built Gmail to Keep Your Data Secure and Private in the Gemini Era.
Google announced that its Gemini AI, now embedded in Gmail, does not train on users' personal email content and only accesses messages for isolated tasks such as summarization. The system processes the request within the inbox, then discards the data,...

Massachusetts Hospital Turning Ambulances Away After Cyberattack
A cyberattack on Signature Healthcare Brockton Hospital in Massachusetts forced the facility to turn away ambulances and activate downtime procedures, cancelling chemotherapy infusions while keeping emergency rooms and surgeries operational. The hospital is working with external experts to restore systems,...

Authorities Disrupt Router DNS Hijacks Used to Steal Microsoft 365 Logins
Law enforcement and private‑sector partners have dismantled the FrostArmada operation, an APT28‑run campaign that hijacked DNS settings on MikroTik and TP‑Link routers to intercept Microsoft 365 credentials. At its peak in December 2025, the malware infected roughly 18,000 devices across...

Ex-Meta Worker Investigated for Downloading 30,000 Private Facebook Photos
A former Meta software engineer is accused of creating a tool that downloaded roughly 30,000 private Facebook photos, prompting a Metropolitan Police cybercrime investigation after an FBI referral. Meta discovered the breach over a year ago, terminated the employee, and...

OpenAI and Spotify Leaders Back London-Based AI Agent Security Startup in $13M Seed Round
London‑based Trent AI emerged from stealth with a $13 million seed round led by LocalGlobe and Cambridge Innovation Capital, joined by executives from OpenAI, Spotify, Databricks and AWS. The startup offers the first multi‑agent security platform that continuously scans, assesses risk...

Tackling Data Breach Risks Requires Perpetual Planning
Data breach fallout can linger, damaging reputation and sparking class‑action lawsuits. Finance and cyber experts warn that an annual security review is no longer sufficient; continuous assessment is required. Hydrolix illustrates this approach with weekly cyber discussions, quarterly board reporting,...

Russian Cyber Spies Targeting Consumer, Soho Routers
The UK National Cyber Security Centre and Microsoft have uncovered a large‑scale DNS hijacking operation run by Russian APT28, also known as Fancy Bear, targeting vulnerable consumer and small‑office routers. The campaign, active since August 2025, has compromised over 200 organisations and...
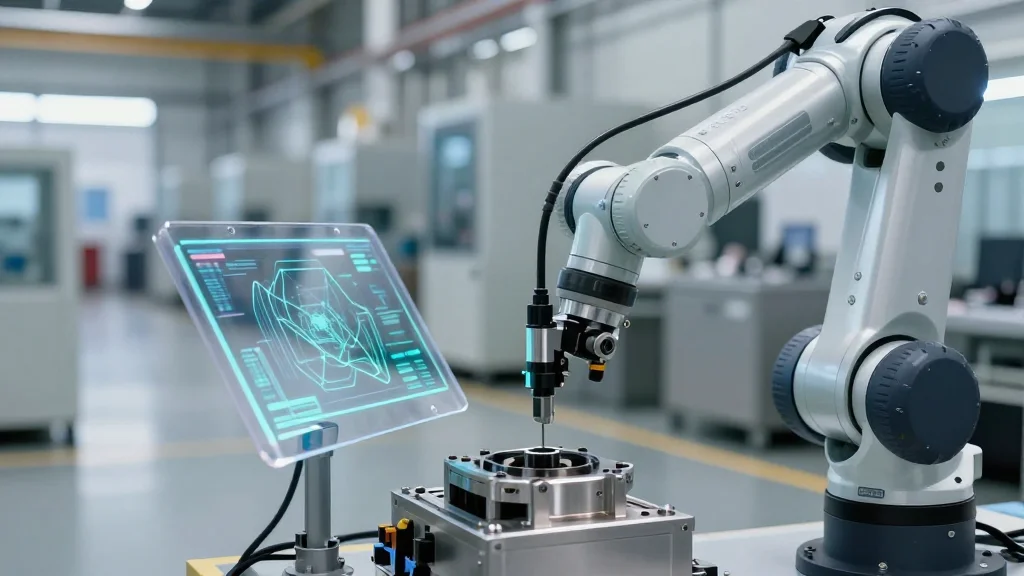
Inside Intelligent Enterprises
Wipro and Intel have launched the WINGS.OTNxT.AI platform, an end‑to‑end managed service that unifies operational technology (OT) and Internet of Things (IoT) environments for manufacturers. The solution, already deployed by more than 40 customers, combines device inventory, secure networking, vulnerability...

Asylon and Thrive Logic Bring Physical AI to Enterprise Perimeter Security
Asylon and Thrive Logic have partnered to embed physical AI into enterprise perimeter security, combining Asylon’s autonomous robotic patrols with Thrive Logic’s AI‑driven analytics and automated incident workflows. The integration streams video from mobile robots to the AI platform, which...
1 Billion Microsoft Users Warned As Angry Hacker Drops 0-Day Exploit
Security researcher released the BlueHammer zero‑day exploit targeting Windows, affecting roughly one billion Microsoft users worldwide. The exploit enables privilege escalation at the kernel level and, unlike typical disclosures, no patch exists yet. Microsoft has acknowledged the threat and is...

Human vs AI: Debates Shape RSAC 2026 Cybersecurity Trends
The RSAC 2026 conference opened with AI taking center stage, as vendors aggressively promote AI‑driven security solutions, including ambitious agentic AI that could augment or replace traditional security‑operations centers. Executives debated the scalability of the "human‑in‑the‑loop" model, with Vodafone’s CISO Emma Smith...

Severe StrongBox Vulnerability Patched in Android
Google released the April 2026 Android security patch, fixing two high‑profile flaws: a local denial‑of‑service bug (CVE‑2026‑0049) in the Framework and a high‑severity vulnerability (CVE‑2025‑48651) affecting StrongBox, the hardware‑backed keystore. StrongBox implementations from Google, NXP, STMicroelectronics and Thales are impacted. While...