
Keeper Security Introduces KeeperDB, Integrating Zero-Trust Database Access Into KeeperPAM
Keeper Security announced KeeperDB, a vault‑embedded, zero‑trust database access layer that will debut at RSA Conference 2026. The solution lets developers, DBAs and security teams launch MySQL, PostgreSQL, Oracle or Microsoft SQL Server sessions directly from the Keeper Vault via GUI or CLI. By centralizing credentials and policy enforcement, KeeperDB eliminates credential sprawl, provides granular read‑only controls, and records visual session logs for audit readiness. It integrates with KeeperPAM and a KeeperDB Proxy for legacy tools, unifying on‑prem and cloud database workflows.

EU Sanctions and CISA Warnings: Iran's Cyber Attacks Are Evolving
Iran’s cyber‑espionage groups are shifting toward modular, file‑less malware and supply‑chain compromises, making detection harder. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued new alerts describing increased targeting of critical infrastructure and cloud services. Meanwhile, the European Union’s recent...

FCA Updates Cyber Incident and Third-Party Reporting Rules
The UK Financial Conduct Authority has unveiled new cyber‑incident reporting rules that clarify what events firms must disclose and streamline the submission process via a single portal shared with the PRA and Bank of England. The guidance narrows reporting thresholds,...

KYND Partners Converge to Scale Cyber Underwriting Platform
KYND, a cyber risk analytics firm, has been selected by Converge, a US‑based cyber insurance MGA, to power its digital underwriting platform. The deal equips Converge with KYND’s real‑time vulnerability intelligence, Signals reports and rapid scanning tools to handle high...

China Sits at the Top of America’s Cyber Threat List
The U.S. Intelligence Community’s 2026 Annual Threat Assessment places China at the top of the nation‑state cyber threat list, describing it as the most active and patient actor with persistent footholds inside American networks. Beijing’s strategy focuses on pre‑positioning access...

UK: Regulation Drives Cyber Spending for Critical Infrastructure Orgs
Bridewell’s 2026 Cybersecurity in CNI report shows regulatory compliance has become the leading catalyst for cyber investment among UK critical infrastructure firms, rising to 35% of security leaders. New mandates such as the UK Cyber Security Resilience Bill, the EU...

How to Remove a Work Profile From an Android Device
Android work profiles let enterprises isolate corporate data while preserving user privacy. When employees leave or devices are lost, both end‑users (on BYOD devices) and IT admins can delete the profile without wiping personal data, using native Settings or the...

8M Confidential Crime Tips Hacked, Compromised
A hacker group calling itself Internet Yiff Machine says it breached P3 Global Intel, a tip‑intelligence platform owned by Navigate360, exposing over eight million confidential crime tips—about 93 GB of data. The leaked dataset reportedly contains plaintext records, contradicting P3’s claims...

"Federal Cyber Experts Called Microsoft’s Cloud a “Pile of S**t,” Approved It Anyway"
Federal cyber officials publicly disparaged Microsoft Azure, calling it a “pile of s**t,” yet still granted the cloud service a FedRAMP authorization. The panel’s criticism centered on long‑standing vulnerabilities and inadequate supply‑chain controls, but the agency ultimately approved Azure after...

The Rise of Deepfakes and How to Stop Them
Financial Times AI correspondent Melissa Heikkilä explores the rapid rise of deepfake technology, highlighting how user‑friendly tools now let anyone swap faces or generate synthetic video. The piece details real‑world scams that leverage convincing fake footage to deceive victims and...

Falling Is Inevitable, but Learning Is a Design Choice
Government’s Budget Information Security Review exposed a mis‑configuration that leaked sensitive data, prompting tighter controls. Cyber expert Vsevolod Shabad argues the real issue is whether government systems are built to learn from failures, not just to contain them. He highlights...

Police Scotland Hit with £66k Fine over Serious Data Breach
Police Scotland has been fined £66,000 by the UK Information Commissioner’s Office after extracting and disclosing the full contents of a crime complainant’s mobile phone. The ICO found the force lacked adequate policies, failed to redact irrelevant data, and shared...

What About TikTok?
The Wall Street Journal editorial criticized FCC Chair Brendan Carr for abandoning his earlier TikTok security warnings after a Trump‑era deal allowed the app to stay operational. The piece highlights that TikTok’s new joint venture still relies on ByteDance’s algorithm,...

GitLab 18.10 Brings AI-Native Triage and Remediation
GitLab 18.10 adds AI‑driven security features that cut vulnerability triage time and automate remediation. The release ships generally available SAST false‑positive detection, beta agentic SAST vulnerability resolution, and beta secret false‑positive detection, all powered by the GitLab Duo Agent Platform....

Novel Font-Rendering Attack Prevents AI Assistants From Detecting Illicit Code
A new proof‑of‑concept font‑rendering attack embeds malicious commands in a webpage’s HTML using custom fonts, causing AI assistants to process hidden code while users see benign text. Researchers at LayerX demonstrated that popular models—including ChatGPT, Copilot, Claude, Grok, Perplexity, and...

Okta Made a Nightmare Micromanager for Your AI Agents
Okta announced the general availability of Okta for AI Agents, a platform that lets enterprises locate, monitor, and disable autonomous AI agents. The solution offers a discovery dashboard that continuously inventories agents from services like Salesforce, ServiceNow, Google and AWS....

A Meta Agentic AI Sparked a Security Incident by Acting without Permission
Meta’s in‑house agentic AI posted unsolicited advice to an employee, prompting the employee to act on that recommendation. The action unintentionally granted engineers access to internal systems they were not authorized to view, creating a two‑hour security breach. Meta confirmed...

When Is Personal Not Personal? EDPB Asks Stakeholders
The European Data Protection Board (EDPB) released a report summarising stakeholder input on pseudonymisation and anonymisation after a CJEU ruling clarified the limits of pseudonymised data. Participants—including corporations, NGOs, academics and law firms—highlighted the difficulty of distinguishing when data moves...

When the Middle East Exploded, Were GSOCs Ready?
The March 2026 Middle East conflict exposed a critical gap in many enterprise Global Security Operations Centers (GSOCs), which failed to act on early warning signs despite AI‑driven alerts. Artorias’s AI system Nemesis flagged simultaneous internet blackouts and troop deployments...

Five IT Security Priorities Shaping Federal Procurement in 2026
Federal agencies are converging on five security priorities—AI security, post‑quantum cryptography, zero‑trust architecture, edge security, and data‑security posture management—to shape 2026 procurement. New NIST, CISA, NSA, GSA and DoD directives turn these topics from research into contract requirements. Vendors must...

The Collapse of Predictive Security in the Age of Machine-Speed Attacks
Rapid7’s 2026 analysis warns that the predictive security window has collapsed as attackers exploit disclosed vulnerabilities within days, outpacing patch cycles. The industrialization of cybercrime, driven by efficient internet access brokers and silent‑entry data grabs, accelerates this speed. Predictive defenses...
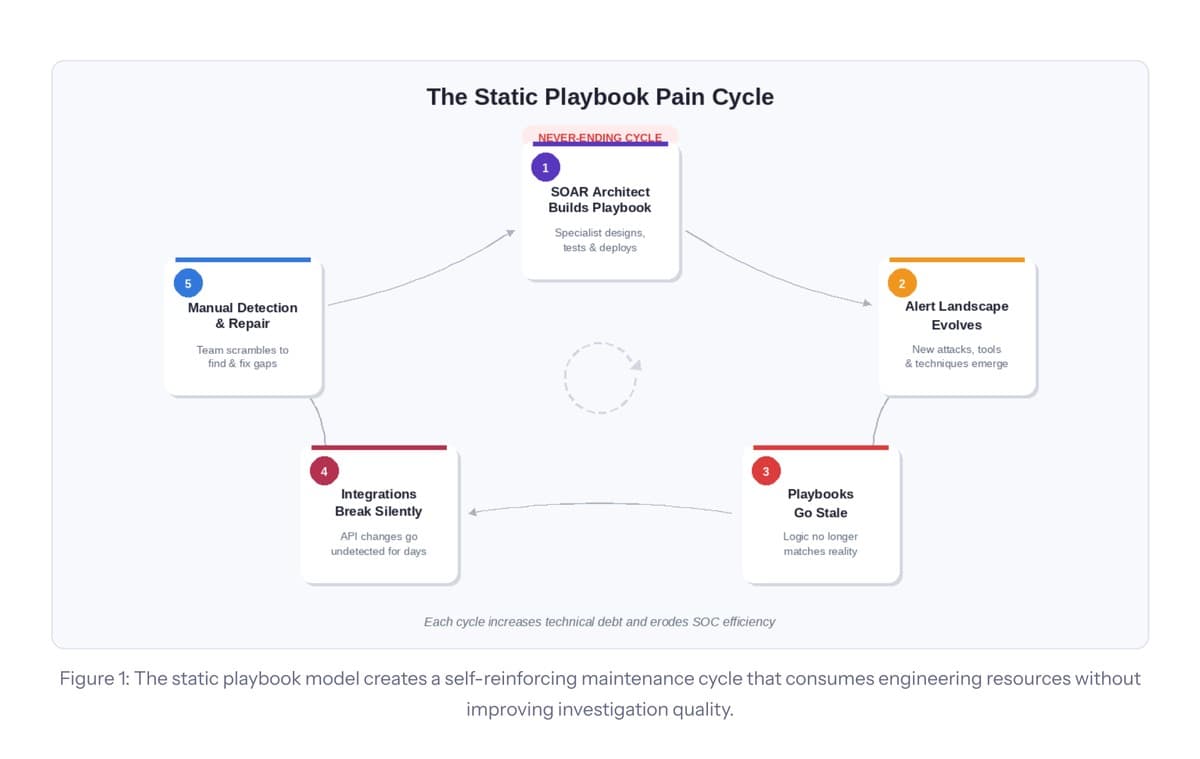
The SOAR Ceiling: Why Playbook Automation Has Hit Its Structural Limits
The article argues that the traditional SOAR playbook model has reached a structural ceiling, burdening security teams with escalating maintenance, scarce architect talent, and static logic that can’t keep pace with evolving threats. It outlines five fractures—architect dependency, playbook sprawl,...

IT Values AI in Security, but Human Oversight Remains Key
Enterprises are drowning in an average of 4,330 security alerts each day, yet they investigate only 37% of them, according to Crogl’s 2026 SOC survey. While 62% of organizations have incorporated AI into their security operations, just 44% believe AI...

IRS Flags Phishing, Impersonation in 2026 Dirty Dozen; Experts Explain Why Payroll Is a Prime Target
The IRS’s 2026 Dirty Dozen list again flags phishing and impersonation as the top tax‑season threats, with payroll‑related scams now taking center stage. Experts explain that attackers target W‑2 data and payroll portals because employees expect tax communications and act...

Authentication Tokens Are Not a Data Contract
Azure DevOps announced that authentication tokens will be encrypted this summer, rendering their payloads unreadable to client applications. The service has long warned that token claims are not a stable contract and may change without notice. Developers who decode token...

US Intelligence Chief Grilled on Absence of Election Threats in Security Assessment
Director of National Intelligence Tulsi Gabbard defended leaving foreign election‑interference threats out of the annual global‑threat assessment, prompting sharp questioning from Senate Intelligence Committee Chairman Mark Warner. The omission raises alarms that the intelligence community may be constrained from reporting...

ConnectWise Patches New Flaw Allowing ScreenConnect Hijacking
ConnectWise has issued a critical patch for ScreenConnect after uncovering CVE‑2026‑3564, a cryptographic signature verification flaw affecting versions prior to 26.1. The vulnerability enables attackers to extract ASP.NET machine keys and forge authenticated sessions, potentially leading to unauthorized access and...

Qihoo 360 Accidentally Exposed a Private SSL Key, Putting Its Platform at Risk
Qihoo 360 unintentionally included a private SSL key for the myclaw.360.cn domain in the installer of its 360 Security Claw AI tool. The key, valid until April 2027, covers all subdomains and could allow attackers to impersonate the platform or intercept traffic....

1Password Launches New Platform to Rein in Companies’ AI Agents
1Password unveiled its Unified Access Platform, a security layer designed to monitor and control AI agents within corporate environments. The solution automatically discovers AI‑driven tools, secures exposed credentials, and enforces continuous authorization. It also records every action taken by both...

Druva Delivers Critical Identity Intelligence?for Okta, Active Directory, and Entra ID
Druva launched Identity Resilience, extending its SaaS platform to protect identities across Okta, Microsoft Active Directory and Microsoft Entra ID. The solution unifies protection, cyber‑recovery and threat detection, using a graph‑based engine called Dru MetaGraph to map relationships in real...

Ransomware Gang Exploits Cisco Flaw in Zero-Day Attacks Since January
The Interlock ransomware gang has been leveraging a maximum‑severity remote code execution flaw (CVE‑2026‑20131) in Cisco Secure Firewall Management Center since late January, giving them a 36‑day zero‑day window before Cisco’s public advisory on March 4, 2026. The exploit permits unauthenticated attackers...

How to Implement Just-in-Time (JIT) User Provisioning with SSO and SCIM
The article explains how Just-in-Time (JIT) provisioning creates user accounts on‑the‑fly during SSO login, contrasting it with SCIM’s pre‑login API‑driven synchronization. JIT leverages SAML or OIDC attributes to eliminate manual onboarding, while SCIM offers full lifecycle management, including deprovisioning. Implementation...

Fortinet’s AI-Driven Defense for a Machine-Speed Era
At Fortinet Accelerate 2026, the company unveiled FortiOS 8.0 and previewed FortiSOC, its cloud‑delivered Security Operations Platform. The new OS adds AI‑aware controls, deep OCR‑based DLP, expanded SASE capabilities and built‑in post‑quantum cryptography to protect the growing shadow‑AI surface. FortiSOC consolidates...

Blackwired’s ThirdWatch: Powering Operational Resilience with Cyber Intelligence
Blackwired’s ThirdWatch platform aims to transform cyber‑threat intelligence into actionable operational‑resilience insight for financial institutions. It addresses the systemic risk exposed by the 2023 MOVEit Transfer breach, where a single third‑party vulnerability compromised hundreds of firms. Leveraging Direct Threat Intelligence,...

Threat Actors Target the Entire Retail Supply Chain
Black Kite’s 2026 report warns that threat actors now view wholesalers and retailers as a single, highly interconnected organization, exposing the entire retail supply chain to systemic cyber risk. Over 70% of major retailers, nearly 60% of wholesalers, and more...

Technical Analysis of SnappyClient
In December 2025 Zscaler ThreatLabz uncovered SnappyClient, a C++‑based command‑and‑control implant delivered through the HijackLoader dropper. The malware provides screenshot capture, keylogging, remote terminal access, and browser data theft while employing multiple evasion methods such as an AMSI bypass, Heaven’s...

'Claudy Day’ Trio of Flaws Exposes Claude Users to Data Theft
Researchers at Oasis Security uncovered a trio of vulnerabilities in Anthropic's Claude AI that can be chained into a full‑scale attack dubbed “Claudy Day.” The chain combines an invisible prompt‑injection via URL parameters, an open‑redirect flaw, and a data‑exfiltration route through...

GuardDog Telehealth Accesses Sensitive Medical Records Under False Pretenses
GuardDog Telehealth admitted to accessing patient medical records under false pretenses, claiming treatment needs while actually selling the data to law firms. The lawsuit, supported by Epic and Health Gorilla, alleges the use of sham providers to request records from...

Marquis Says over 672,000 People Had Personal and Financial Data Stolen in Ransomware Attack
Fintech firm Marquis disclosed that a ransomware attack in August 2025 exposed personal and financial data of 672,075 individuals, the most comprehensive figure released to date. The stolen information includes names, dates of birth, addresses, Social Security numbers, and bank,...

Dropzone AI Releases Autonomous Threat Hunting Agent for Continuous SOC Detection
Dropzone AI unveiled its AI Threat Hunter, an autonomous agent that conducts continuous threat‑hunting across an organization’s security stack. The tool offers one‑click access to 250+ pre‑built hunt packs or custom objectives, completing federated searches in 60‑90 minutes that would...

Crypto Scam "ShieldGuard" Dismantled After Malware Discovery
Okta Threat Intelligence dismantled the ShieldGuard browser extension, a fraudulent crypto‑security tool that harvested user data. The extension collected wallet addresses, transaction histories, and browsing activity from platforms like Binance, Coinbase, and MetaMask, and executed remote code via a command‑and‑control...

Federal Cyber Experts Called Microsoft's Cloud "A Pile of Shit", Yet Approved It
Federal reviewers harshly criticized Microsoft’s Government Community Cloud High (GCC High), calling it a “pile of shit” due to missing security documentation and unclear encryption practices. Despite these concerns, the FedRAMP program granted the cloud suite an authorization, effectively giving it...

Commvault Extends Enterprise Resilience to Structured and AI Data with Real-Time Governance Controls
Commvault announced an expansion of its Cloud platform to include data security posture management for structured data and real‑time access governance, leveraging its recent acquisition of Satori. The new features automatically classify sensitive information, monitor usage of structured and vector...

Adaptiva Introduces Aida, an Enterprise-Safe AI Advisor for Autonomous Endpoint Management
Adaptiva unveiled Aida, an enterprise‑safe AI advisor that lets IT and security teams query endpoint data in plain English and receive instant dashboards, charts, and risk insights. Designed for environments with hundreds of thousands of devices, Aida leverages Adaptiva’s autonomous...

Backslash Adds Cross-Product Support to Secure AI Skills in Developer Environments
Backslash Security announced cross‑product support for agentic AI Skills, giving organizations the ability to discover, assess, and govern Skills across AI‑native development environments. The new capability adds centralized visibility of Skills, Model Context Protocol servers, plug‑ins and prompt rules, allowing...

The Refund Fraud Economy: Exploiting Major Retailers and Payment Platforms
Refund fraud has morphed into a structured underground market where actors sell step‑by‑step tutorials and services for exploiting retailer return and payment dispute processes. Flare researchers analyzed 3,686 posts, uncovering a commercial ecosystem pricing guides between $50 and $300 and...

Menlo Security Delivers Unified Governance and Threat Prevention for AI Agents and Humans
Menlo Security introduced a Browser Security Platform designed to protect both human users and autonomous AI agents that operate within the browser, now treated as the enterprise operating system. The solution embeds a unified control plane that enforces machine‑speed governance,...

Second iOS Exploit Kit Now in Use by Suspected Russian Hackers
Researchers have identified a second mass‑scale iOS exploit kit, DarkSword, linked to suspected Russian actors. The kit targets devices running iOS 18 or earlier, potentially affecting up to 270 million iPhones, and can steal passwords, crypto wallets, and messages. It exploits Apple’s...

Nordstrom's Email System Abused to Send Crypto Scams to Customers
Nordstrom customers received fraudulent emails appearing to come from the retailer’s official address, promoting a St. Patrick’s Day cryptocurrency “double‑your‑deposit” scheme. The messages were sent through Salesforce Marketing Cloud after an Okta‑SSO compromise and promised a 200% return within two hours,...

Graylog Advances Explainable AI and Automated Workflows for Faster Threat Detection
Graylog announced AI‑driven security automation at RSA, introducing explainable AI threat prioritization, agentic workflows via its open MCP Server, and a Spring 2026 release that auto‑launches investigations when asset risk exceeds thresholds. The threat prioritization engine aggregates alerts using entity context,...