
Cybersecurity at the Edge: Securing Rugged IoT in Mission-Critical Environments
Edge computing is now integral to defense, utilities and public safety, relying on rugged IoT devices that operate in extreme, disconnected environments. These deployments break traditional cybersecurity assumptions such as continuous connectivity and frequent patching, exposing critical infrastructure to heightened risk. Gartner reports a 400% surge in IoT‑related incidents over three years, with average OT breach costs exceeding $3 million. CIOs must adopt adaptive, decentralized security architectures to protect mission‑critical operations.
New DocuSign-Themed Phishing Scam Delivers Stealth Malware to Windows Devices
Researchers have uncovered a sophisticated phishing campaign that impersonates DocuSign to deliver the Vidar information‑stealing malware to Windows computers. The attack uses a look‑alike domain and a fake installer signed with a legitimate Chinese code‑signing certificate to bypass reputation filters....

Methodist Homes of Alabama and Northwest Florida Is Notifying Residents and Employees of Its Second Data Breach in Seven Months.
Methodist Homes of Alabama and Northwest Florida disclosed a second data breach, stemming from a compromised employee email account accessed between May 8 and May 21, 2025. The breach exposed personal identifiers such as Social Security numbers, dates of birth, Medicare numbers, and...

Embracing Uncertainty with AI Agents: Vulnerability Assessment Using Pydantic AI
The article demonstrates how AI agents built with Pydantic AI can use union‑type structured output to manage uncertainty in software vulnerability triage. By allowing the model to return either a detailed CriticalVulnerability record or an UnableToAssess response, agents avoid hallucinating fields...

How to Automate Safe Removal of Unused Code
Azul Intelligence Cloud now integrates with the open‑source OpenRewrite engine to automatically identify, flag, and safely remove unused or dead Java code. The solution combines runtime visibility from Azul Code Inventory with rule‑based refactoring, applying incremental annotations before code deletion....

ThreatsDay Bulletin: RustFS Flaw, Iranian Ops, WebUI RCE, Cloud Leaks, and 12 More Stories
This week’s ThreatsDay bulletin highlighted a surge in cyber threats across multiple fronts. CISA expanded its KEV catalog by 245 high‑risk flaws, while a critical hard‑coded token in RustFS exposed clusters to remote takeover. OpenAI faced a court order to...

Microsoft Exchange Online Outage Blocks Access to Mailboxes via IMAP4
Microsoft confirmed an Exchange Online outage that intermittently blocks mailbox access via IMAP4, first reported at 23:35 UTC on Wednesday. The issue stems from a code conflict that introduced an authentication misconfiguration, while other connection methods remain functional. Microsoft has deployed...

Researchers Expose WHILL Wheelchair Safety Risks via Remote Hacking
Security researchers from QED Secure Solutions uncovered a critical Bluetooth authentication flaw in WHILL’s Model C2 and Model F electric wheelchairs (CVE‑2025‑14346). The vulnerability allows attackers within range to pair with the device, seize control of movement, override speed limits,...

Fifth of Breaches Take Two Weeks to Recover From
A new Absolute Security report, based on a poll of 750 CISOs in the US and UK, finds that endpoint disruptions from cyber‑attacks often require 3‑6 days to remediate, with 19% taking up to two weeks. The average cost to...

Microsoft to Enforce MFA for Microsoft 365 Admin Center Sign-Ins
Microsoft announced that starting next month it will require multi‑factor authentication for every user who signs into the Microsoft 365 admin center. The policy applies to all admin‑level accounts, regardless of organization size or licensing tier. Existing MFA configurations will...

Creating a Safe Learning Environment in K-12 Schools Without Adding Complexity
Today's K‑12 schools must protect students across physical spaces, emotional climate, psychological trust, and digital platforms. Research shows that safety directly boosts engagement, participation, and academic achievement. Districts ignoring any safety dimension risk lower attendance, disrupted instruction, and eroding community...
React2Shell Vulnerability Hit by 8.1 Million Attack Attempts
The React Server Components “Flight” protocol remote code execution flaw (CVE‑2025‑55182), known as React2Shell, has become the focus of a massive exploitation campaign. GreyNoise has logged over 8.1 million attack sessions, with daily volumes stabilizing at 300‑400 k after a December peak...
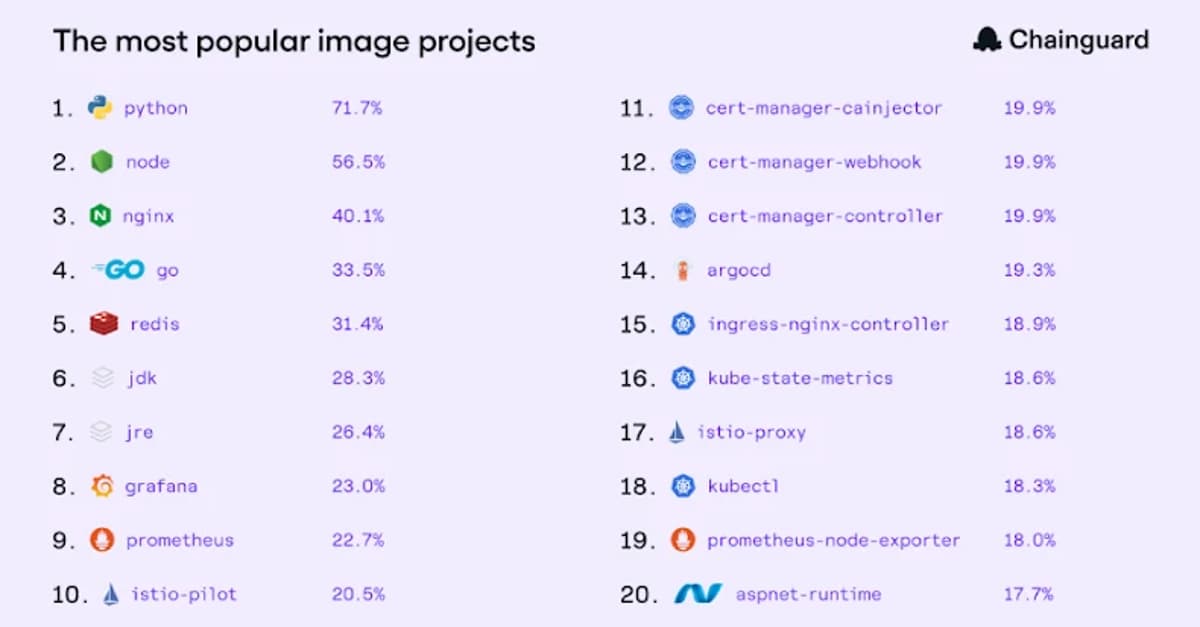
The State of Trusted Open Source
Chainguard’s quarterly “State of Trusted Open Source” report analyzes usage of over 1,800 container images across its customer base, revealing that Python is the most popular image and that the majority of production workloads rely on a long‑tail of less‑common...

PoC Released for Unauthenticated RCE in Trend Micro Apex Central (CVE-2025-69258)
Trend Micro issued a critical patch (Build 7190) for its on‑premise Apex Central platform, addressing three remotely exploitable flaws disclosed by Tenable. The most severe, CVE‑2025‑69258, enables unauthenticated attackers to inject a malicious DLL into MsgReceiver.exe and gain SYSTEM‑level code execution....

Report: China Breached Email Systems Used by U.S. Congressional Staff
According to a Financial Times investigation, Chinese state‑linked hackers breached email systems used by staff of several influential House committees. The intrusion gave the actors access to legislative drafts, policy discussions and potentially classified briefings. U.S. officials highlighted the vulnerability...

Bridging the Gap Between SRE and Security: A Unified Framework for Modern Reliability
Site reliability engineering (SRE) and security teams traditionally operate in separate silos, creating friction that stalls reliability initiatives and slows security controls. The article proposes a unified framework that merges reliability goals, risk budgets, joint observability, and integrated incident response...

US To Leave Global Forum on Cyber Expertise
The Trump administration signed an executive order on Jan. 7 withdrawing the United States from 66 international bodies, including the Global Forum on Cyber Expertise (GFCE) and the European Centre of Excellence for Countering Hybrid Threats (Hybrid CoE). Both organizations coordinate...

Trump Orders US Exit From Global Cyber and Hybrid Threat Coalitions
President Donald Trump signed a memorandum ordering the United States to withdraw immediately from three major cyber‑security coalitions: the European Centre of Excellence for Countering Hybrid Threats, the Global Forum on Cyber Expertise, and the Freedom Online Coalition. The exits...

How Attackers Hide Processes by Abusing Kernel Patch Protection
Researchers disclosed a new Windows rootkit technique that hides malicious processes by using the legitimate PsSetCreateProcessNotifyRoutineEx API to repair ActiveProcessLinks just before the kernel’s PspProcessDelete validation runs. This timing‑based bypass evades both PatchGuard and Hypervisor‑Protected Code Integrity, allowing processes to...

Credential Stuffing: What It Is and How to Protect Yourself
Credential stuffing exploits reused passwords by feeding leaked username‑password pairs into login forms across services. The technique surged as data breaches and infostealer malware supply vast credential caches, with 62% of Americans admitting frequent reuse. High‑profile incidents—35,000 PayPal accounts in...

Coolify Discloses 11 Critical Flaws Enabling Full Server Compromise on Self-Hosted Instances
Cybersecurity researchers disclosed eleven critical‑severity flaws in Coolify, an open‑source self‑hosting platform, that enable authenticated users to execute arbitrary commands as root and even escape containers. The vulnerabilities, catalogued as CVE‑2025‑66209 through CVE‑2025‑59158, carry CVSS scores from 9.4 to 10.0....

Cisco Warns of Identity Service Engine Flaw with Exploit Code
Cisco has released patches for a critical vulnerability (CVE‑2026‑20029) in its Identity Services Engine (ISE) that allows administrators to read arbitrary files via malformed XML uploads. A proof‑of‑concept exploit is publicly available, prompting Cisco to advise immediate upgrades to the...

IPFire Update Brings New Network and Security Features to Firewall Deployments
IPFire released Core Update 199, bringing Wi‑Fi 6 and Wi‑Fi 7 support, native LLDP/CDP discovery, and a Linux 6.12.58 kernel. The update upgrades Suricata to version 8.0.2 and refines OpenVPN handling, including multiple DNS/WINS pushes. It also patches a proxy‑related CVE and improves web‑interface...

Turning Data Security Into the Defining MSP Opportunity of 2026
Managed service providers (MSPs) are facing a market shift where cybersecurity is now a core expectation rather than an optional add‑on. Data Security Posture Management (DSPM) offers a continuous, automated view of sensitive data across tenants, turning security into a...

GitLab Patches Multiple Flaws Allowing Arbitrary Code Execution
GitLab has issued emergency patches—versions 18.7.1, 18.6.3 and 18.5.5—to close seven newly disclosed vulnerabilities affecting self‑managed instances. The flaws include two high‑severity stored and reflected cross‑site scripting bugs, missing authorization checks in AI GraphQL endpoints, and a runner‑removal issue that...

BlueDelta Hackers Target Microsoft OWA, Google, and Sophos VPN to Steal Credentials
Recorded Future’s Insikt Group uncovered a credential‑harvesting campaign by the Russian‑state backed BlueDelta group throughout 2025. The actors deployed phishing emails with legitimate‑looking PDFs to lure victims into fake Microsoft Outlook Web Access, Google, and Sophos VPN login portals, using...

CISA Tags Max Severity HPE OneView Flaw as Actively Exploited
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has designated a maximum‑severity vulnerability in Hewlett Packard Enterprise (HPE) OneView as actively exploited. Identified as CVE‑2025‑37164, the flaw permits unauthenticated code‑injection attacks that lead to remote code execution on any OneView...

PayPal Email Scam: How It Worked Before the Fix
In December 2025 scammers hijacked PayPal’s subscription feature to generate authentic‑looking notification emails from service@paypal.com, inserting fake purchase details and a phone number to lure victims into callback scams. The abuse relied on a paused subscription triggering a legitimate “payment no...

StackRox: Open-Source Kubernetes Security Platform
StackRox is an open‑source Kubernetes security platform that unifies build‑time image scanning, configuration analysis, and runtime telemetry. It ingests data from container images, Kubernetes APIs, and live cluster activity to drive policy checks covering vulnerabilities, privilege escalation, and network exposure....

Australian Insurer Prosura Confirms Cyber Incident, Takes Online Services Offline Amid Investigation
Australian insurer Prosura confirmed a cyber incident on Jan 3, 2026 after detecting unauthorized access to internal systems. The breach led the company to temporarily disable its self‑service portal, halting online policy purchases, claims and account management. Fraudulent phishing emails were sent...

Linux Battery Utility Vulnerability Allows Authentication Bypass and System Tampering
A vulnerability in the TLP power‑profiles daemon (version 1.9.0) lets local users bypass Polkit authentication and tamper with system power settings. The flaw stems from using Polkit’s deprecated “unix‑process” subject, creating a PID race condition that grants elevated control without admin...

What Happens to Insider Risk when AI Becomes a Coworker
In a Help Net Security video, Living Security CEO Ashley Rose explains that AI’s integration into everyday workflows expands the definition of insider risk to include autonomous agents and automated processes. She notes that most risky actions stem from broken...

OwnCloud Warns Users to Enable MFA After Credential Theft Incident
ownCloud issued an urgent advisory urging users to enable Multi‑Factor Authentication after a credential‑theft incident reported by Hudson Rock. Threat actors stole passwords via infostealer malware such as RedLine, Lumma and Vidar and accessed accounts lacking MFA. The breach did not...
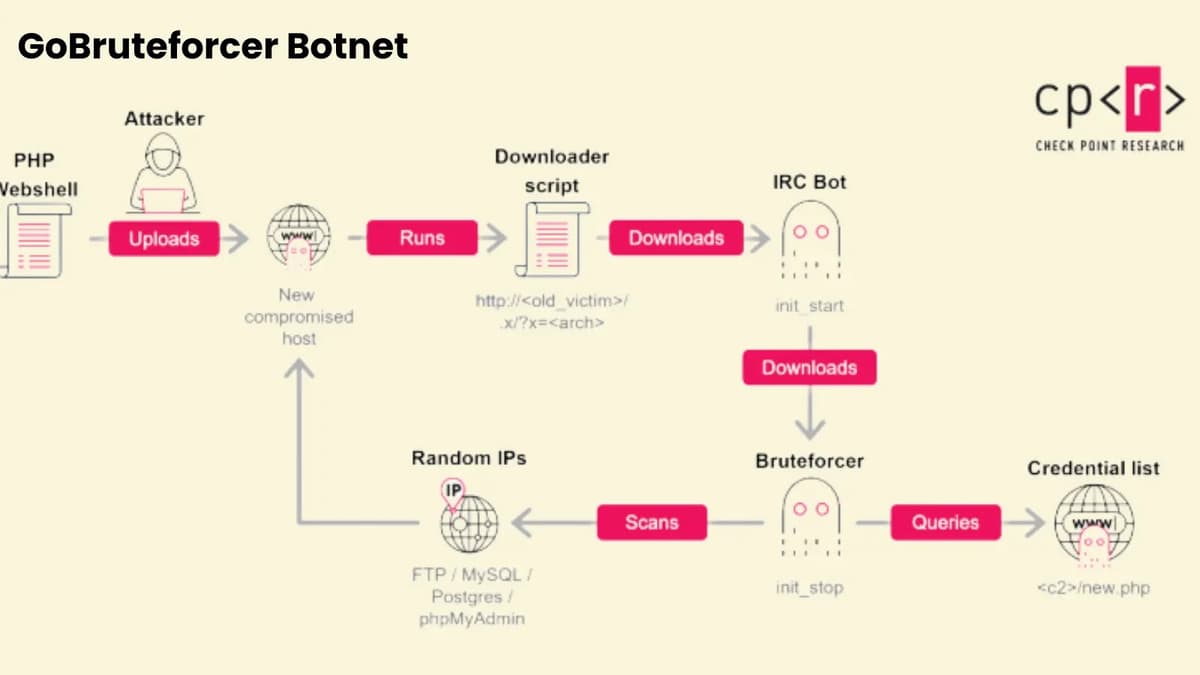
Global GoBruteforcer Botnet Campaign Threatens 50,000 Linux Servers
The GoBruteforcer botnet is actively compromising more than 50,000 internet‑facing Linux servers by brute‑forcing credentials for FTP, MySQL, PostgreSQL and phpMyAdmin services. Researchers note that AI‑generated deployment examples and legacy stacks like XAMPP have proliferated weak default passwords, expanding the...

Voice Cloning Defenses Are Easier to Undo than Expected
Researchers at a Texas university demonstrated that popular noise‑based voice‑protection tools can be stripped away, restoring speaker identity and enabling cloned voices to pass verification. They introduced VocalBridge, a diffusion‑based system that removes protective noise while preserving natural speech characteristics....
.jpg?height=635&t=1767630565&width=1200)
Is Email the Entry Point to a Well-Rounded Disinformation Attack?
Email remains the most exploited business communication channel, now serving as the entry point for coordinated disinformation attacks that blend text, voice and video. A recent $150 million funding round for Sublime Security highlights enterprise urgency, while Valimail’s 2025 report shows...
Cybercriminals Exploit VMware ESXi Vulnerabilities Using Zero-Day Toolset
Huntress researchers uncovered a sophisticated campaign that leverages a zero‑day toolkit, MAESTRO, to exploit three critical VMware ESXi vulnerabilities disclosed in VMSA‑2025‑0004. The attack chain begins with stolen Domain Admin credentials used to compromise a SonicWall VPN, followed by lateral...

Holes in Veeam Backup Suite Allow Remote Code Execution, Creation of Malicious Backup Config Files
Veeam disclosed four vulnerabilities in its Backup & Replication suite that let users with Backup Admin, Backup Operator or Tape Operator roles execute remote code or write files as root. The most severe flaw, CVE‑2025‑59470, carries a CVSS score of...
New GoBruteforcer Attack Wave Targets Crypto, Blockchain Projects
A new wave of GoBruteforcer botnet attacks is targeting cryptocurrency and blockchain projects by exploiting exposed FTP, MySQL, PostgreSQL and phpMyAdmin services. The malware uses compromised Linux servers to scan public IP ranges, brute‑force default credentials, and drop web shells...

Cybersecurity Predictions Are a Window Into a Vendor’s Roadmap and Business Priorities
Every November the cybersecurity sector launches a predictable wave of vendor‑authored prediction reports. While marketed as forward‑looking guidance, these pieces are timed to influence budgeting cycles and often reinforce the vendor’s existing value proposition or pre‑justify upcoming roadmap items. The...

NDSS 2025 – A Multifaceted Study On The Use of TLS And Auto-Detect In Email Ecosystems
Researchers from The Chinese University of Hong Kong presented a comprehensive analysis of TLS usage and auto‑detect features across email ecosystems at NDSS 2025. Testing 49 popular email clients revealed multiple vulnerabilities that enable covert security downgrades and credential leakage....

Critical RCE Flaw Allows Full Takeover of N8n AI Workflow Platform
Researchers disclosed a critical unauthenticated remote code execution flaw (CVE‑2026‑21858) in the n8n workflow automation platform. The vulnerability stems from improper Content‑Type validation in the formWebhook function, enabling arbitrary file reads, path traversal, and full system takeover. By stealing configuration...

Versatile Malware Loader Pkr_mtsi Delivers Diverse Payloads
ReversingLabs identified a Windows packer named pkr_mtsi that serves as a versatile malware loader in large‑scale malvertising and SEO‑poisoning campaigns. First seen in April 2025, it disguises fake installers for popular tools like PuTTY, Rufus and Microsoft Teams, then delivers...

Microsoft: Classic Outlook Bug Prevents Opening Encrypted Emails
Microsoft is investigating a bug in classic Outlook that blocks recipients from opening emails encrypted with the “Encrypt Only” permission after the Current Channel Version 2511 update (Build 19426.20218). Affected users see a message_v2.rpmsg attachment and a credential prompt instead of the email...

Ghost Tap Malware Fuels Surge in Remote NFC Payment Fraud
Group‑IB uncovered a new Android malware family, dubbed Ghost Tap, that enables criminals to perform unauthorized tap‑to‑pay transactions by remotely relaying NFC card data. Over 54 malicious APKs, disguised as legitimate finance apps, are sold on Chinese‑language Telegram channels where...

The Loudest Voices in Security Often Have the Least to Lose
The article argues that the most vocal cybersecurity commentators often lack accountability, leading to hype over substance. It illustrates five harmful personas—panic inducer, hype rider, Chicken Little, pessimist, and dismisser—who prioritize fear, trends, or dismissal instead of evidence‑based solutions. By...

How to Eliminate IT Blind Spots in the Modern, AI-Driven Enterprise
Enterprises that rely heavily on AI and multi‑cloud environments are confronting new security blind spots that stem from dynamic agent behavior, data‑poisoning, and mis‑configurations. Experts advise CSOs to shift from reactive defenses to unified visibility that normalizes telemetry across AI...

Why Legitimate Bot Traffic Is a Growing Security Blind Spot
Security teams have long focused on blocking malicious bots, but legitimate bots now account for a sizable portion of web traffic, exceeding 50%. Search‑engine crawlers, AI scrapers, and emerging agentic AI interact with applications at scale, creating hidden security, performance,...

Cyberattacks Likely Part of Military Operation in Venezuela
The United States’ Jan. 3 raid that captured Venezuelan President Nicolás Maduro was accompanied by a sudden power and internet outage in Caracas, prompting speculation that U.S. Cyber Command and other agencies deployed offensive cyber capabilities. President Trump hinted at "a...

DDoSia Powers Affiliate-Driven Hacktivist Attacks
Pro‑Russian hacktivist group NoName057(16) has been leveraging a volunteer‑distributed DDoS platform called DDoSia to launch coordinated attacks against government, media and institutional websites linked to Ukraine and Western interests. The tool, now modular and cross‑platform, enables participants with minimal technical...