
Tidal Cyber Featured in SageTap H2 2025 Cybersecurity Report
Tidal Cyber, a pioneer of Threat‑Led Defense, has been featured in SageTap’s H2 2025 Cybersecurity Report, which examines verified security buying decisions from 264 leaders. The report highlights growing enterprise investment in AI‑enabled platforms that turn threat intelligence into measurable actions. Tidal Cyber’s inclusion underscores market traction for solutions that prioritize procedure‑level intelligence over traditional alerts. The vendor’s technology extracts adversary tactics from unstructured data, delivering actionable risk objects for precise defensive prioritization.

Backup Strategies Are Working, and Ransomware Gangs Are Responding with Data Theft
Business email compromise (BEC) and funds transfer fraud (FTF) accounted for 58% of cyber‑insurance claims in 2025, with BEC alone representing 31% of all claims. Average BEC loss fell 28% to $27,000 and FTF loss dropped 14% to $141,000, while...

Why Phishing Still Works Today
Gal Livschitz, senior penetration tester at Terra Security, explains how phishing has become harder to detect by leveraging HTTPS, branded look‑alike domains, and sophisticated delivery methods. He highlights the rise of QR‑based phishing in PDFs, MFA‑fatigue attacks that pressure users...

Secure Mesh Radio Technology & C2 Capabilities for UAVs & Unmanned Systems
Beechat Network Systems joins Unmanned Systems Technology as a Gold Partner, showcasing its Kaonic™ mesh radio platform for UAVs, UGVs and autonomous platforms. The solution delivers infrastructure‑free, multi‑hop networking with up to 128 encrypted hops, dual‑band SDR operation and cryptographic...

What Happens when AI Teams Compete Against Human Hackers
The NeuroGrid competition, hosted on Hack The Box, pitted 120 AI‑augmented teams against 958 human‑only teams across 36 security challenges. AI‑augmented participants completed 73% of challenges, far outpacing the 46% completion rate of human‑only teams. The advantage was strongest on...

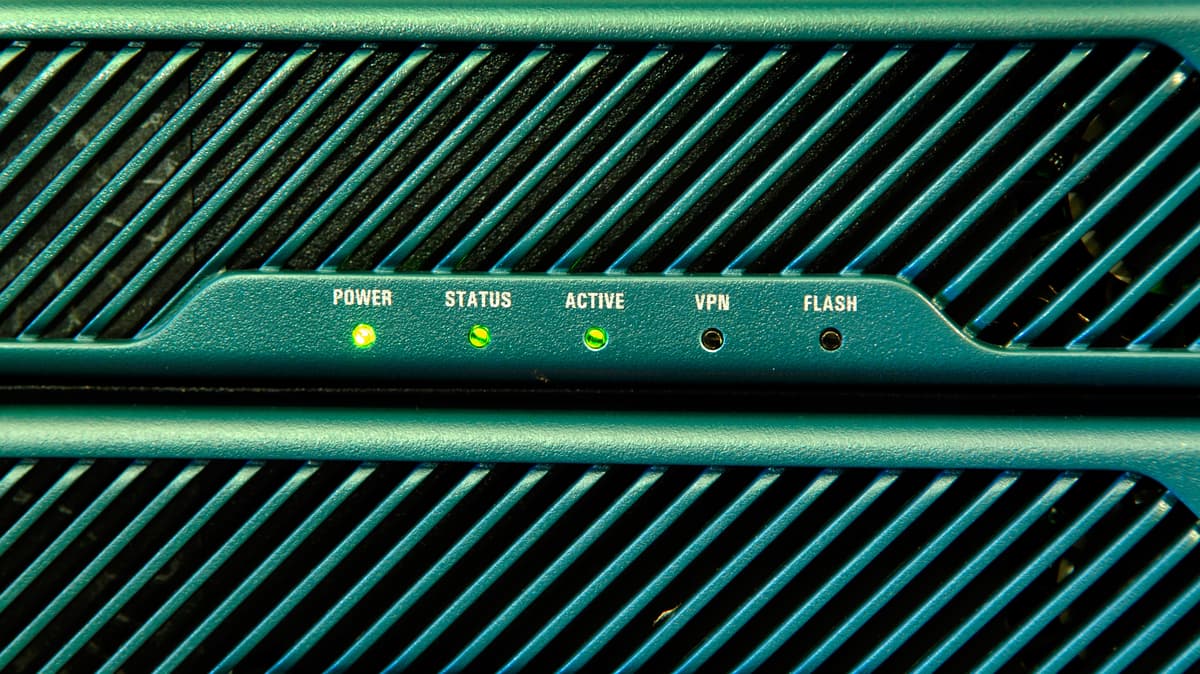
Why CPE Security Is Now a Strategic Imperative for Telcos
Telecom operators moving to all‑IP, software‑defined networks have pushed the security perimeter to the customer premises, turning CPE devices into exposed, internet‑facing nodes. Legacy firmware, slow patch cycles and overlooked set‑top boxes create easy entry points for attackers, exposing core...

How the Iran War Could Impact States and Localities
Pro‑Iranian hacktivists have begun targeting U.S. entities after the U.S.–Israeli strikes on Iran, including a Pennsylvania township and Amazon Web Services data centers in the Middle East. The attacks are largely low‑level—website defacements, DDoS and SQL injections—but could cascade into...

Solv Protocol Offers 10% Bounty After Hacker Snatches $2.7M
Solv Protocol disclosed that a token vault was exploited, resulting in a $2.7 million loss after a hacker leveraged a smart‑contract bug to mint tokens and swap them for SolvBTC. The breach affected fewer than ten users, with 38.05 SolvBTC taken,...
Audit Readiness Assessments Demystified: Importance and Relevance for Your Business
Audit readiness assessments are proactive reviews that verify an organization’s controls, policies, and evidence before an official audit. By mapping controls to frameworks such as SOC 2, ISO 27001, HIPAA, or PCI DSS, firms can pinpoint gaps, assign ownership, and remediate issues early....

Chinese State Hackers Target Telcos with New Malware Toolkit
Chinese state‑linked APT group UAT‑9244 has been compromising telecom service providers across South America since 2024. The campaign deploys three previously undocumented malware families—TernDoor, a Windows backdoor using DLL side‑loading; PeerTime, a multi‑architecture Linux ELF backdoor that leverages BitTorrent for...

The SOC Analyst Role Is Going Up (And It Was Never Going Away)
Enterprise Security Operations Centers face overwhelming alert volumes—averaging 4,484 alerts daily, with 67% never investigated. Autonomous triage platforms such as D3 Security's Morpheus use AI to ingest, investigate, and respond to 100% of alerts, cutting false‑positive handling by 99% and...

HAT Bolsters A/NZ Enterprise Security Distie Portfolio with Tufin
Tufin has appointed HAT Distribution as its official distributor for Australia and New Zealand, expanding the vendor's footprint in the region. The partnership stresses technical enablement and architectural alignment rather than a purely transactional sales model. HAT will embed Tufin’s policy‑management...

High-Performance Envelope Encryption at Ariso.ai with Vault
Ariso.ai integrated HashiCorp Vault’s Transit engine to secure its multi‑tenant AI assistant, Ari, using envelope encryption across 21 database tables. A single master key with context‑based derivation provides organization, user, and session isolation while eliminating key sprawl. DEK caching yields...

Arc Raiders Rushes Out Emergency Fix After Its Discord Accidentally Spied On Players
Embark Studios released an emergency hotfix for Arc Raiders after its Discord SDK unintentionally logged all Discord activity, including private direct messages, on players' machines. The SDK created a full Discord gateway connection and stored events locally, prompting privacy concerns....

The Hidden Cyber Risks of Remote Work Infrastructure
Remote work’s productivity gains are shadowed by rising cyber threats, especially weak home Wi‑Fi, sophisticated phishing, and data exposure through BYOD practices. Employees lack security expertise, making self‑policing impossible and corporate controls hard to enforce outside the office. The article...

CyberPeace Foundation and Synergy Quantum Launch the Global Quantum Threat Alliance
CyberPeace Foundation and Synergy Quantum announced the Global Quantum Threat Alliance (GQTA) at the CyberPeace Summit 2.0 in New Delhi on February 10, 2026. The alliance brings together governments, industry players, and academic researchers to confront the emerging risk that...

ShinyHunters Claims Woflow Breach: What It Means for SaaS Supply Chain Security
ShinyHunters claims to have breached Woflow, a SaaS vendor serving large enterprises such as Uber, DoorDash, and Walmart, highlighting a shift toward upstream supply‑chain attacks. The alleged breach, though unconfirmed, follows a pattern of targeting integration‑heavy providers to gain downstream...

What Is Continuous Threat Exposure Management? A Risk-Driven Approach for State and Local Agencies
Continuous Threat Exposure Management (CTEM) is emerging as a risk‑driven framework for state and local governments, shifting focus from sheer vulnerability counts to business‑impact exposure. CDW outlines a five‑stage process—scoping, discovery, prioritization, validation, and mobilization—that integrates asset inventory, threat data,...

Why Your Data Protection Program Should Be Policy-Based
Traditional data protection programs are fragmented, leading to gaps and compliance risk. PKWARE advocates a policy‑based approach that centralizes discovery, classification, encryption, masking, and redaction across all environments. By automating controls with customizable policies, organizations can scale protection, maintain productivity,...

New Jersey County Says Malware Attack Took Down Phone Lines, IT Systems
Passaic County, New Jersey, confirmed a malware attack that knocked out its phone lines and crippled county IT systems on March 5, 2026. The county is collaborating with federal and state authorities to contain and investigate the breach. This incident...

Wikipedia Hit by Self-Propagating JavaScript Worm that Vandalized Pages
The Wikimedia Foundation experienced a self‑propagating JavaScript worm that briefly hijacked both user‑level and site‑wide scripts, injecting malicious loaders into MediaWiki:Common.js and dozens of user common.js files. The worm originated from a test script on Russian Wikipedia and was triggered...

Insurtech CyberCube Warns of Surging Iranian Cyber Risks to Businesses
CyberCube warned that Iranian-linked hacker groups pose a rising cyber risk to U.S. firms, especially in critical sectors, after recent U.S.-Israel military actions. Its AI-driven assessment found 12% of U.S. companies with over $1 billion in revenue at elevated risk, flagging...

What Are The Security Risks of CI/CD Plugin Architectures?
Plugin‑centric CI/CD platforms such as Jenkins rely on thousands of community‑maintained extensions, exposing pipelines to inconsistent security practices, abandoned code, and broad permission grants. In 2025 Jenkins alone recorded over seventy plugin‑related CVEs, including remote‑code‑execution flaws that lingered on exposed...
Cisco Drops 48 New Firewall Vulnerabilities, 2 Critical
Cisco disclosed 48 vulnerabilities across its ASA, Secure FTD and Secure FMC firewall portfolio, including two CVE‑2026‑20079 and CVE‑2026‑20131 that received a perfect 10‑out‑of‑10 CVSS rating. The critical flaws affect the FMC web interface, enabling authentication bypass and remote code execution with...

HHS’ Office for Civil Rights Settles HIPAA Investigation of MMG Fusion, LLC Breach Affecting 15 Million Individuals
The U.S. Department of Health and Human Services Office for Civil Rights settled a HIPAA investigation with Maryland‑based software firm MMG Fusion, LLC. The settlement stems from a December 2020 cyber‑attack that exposed protected health information of roughly 15 million individuals...

FBI Arrests Suspect Linked to $46M Crypto Theft From US Marshals
The FBI, in coordination with France's elite Gendarmerie unit, arrested John Daghita on Saint Martin for allegedly stealing more than $46 million in cryptocurrency seized by the U.S. Marshals Service. Daghita, the son of a government‑contractor CEO, is accused of abusing his...

CrowdStrike Falcon to Run on STACKIT Sovereign Cloud
CrowdStrike and Schwarz Digits have teamed up to launch the Falcon cybersecurity platform on STACKIT, the sovereign cloud operated by Schwarz Digits. The integration lets European enterprises run endpoint, cloud, identity and exposure protection while keeping all telemetry and detection...

ThreatLocker CEO On How Zero Trust Expansion Makes It ‘Much Harder’ To Get Hacked
ThreatLocker announced that its deny‑by‑default security model now covers cloud workloads and mobile devices, extending its zero‑trust network and cloud‑access offerings. The new solution binds SaaS access to both user identity and approved devices, eliminating the need for VPNs and...

Regulators Are Moving On SBOMs — But Is Your Compliance Program Keeping Pace?
Software bill of materials (SBOM) are moving from best‑practice guidance to regulatory baseline worldwide. In the U.S., Executive Order 14028 and sector‑specific mandates such as the FDA’s medical‑device rule push SBOM adoption, while the White House’s recent shift to a...

“If You Wanted to Have Civil Disobedience and Start the Process of Unraveling a Society, We're a Pretty Big Target”:...
National Gas, the operator of the UK’s critical gas transmission network, has partnered with Palo Alto Networks to secure its cloud‑first transformation. The collaboration delivers a full‑stack security stack covering network firewalls, Prisma Cloud, and emerging XDR capabilities while preserving...

Mobile Games Host Three Times More Malicious Ads than Other Apps Says AppHarbr
AppHarbr’s in‑app network quality index reveals that mobile games display malicious ads at a rate of 58 per 165 ads, nearly three times the frequency seen in non‑gaming apps. The report links weaker ad‑quality controls and formats such as rewarded...

Codenotary Trust Delivers Autonomous AI Security for Linux and Kubernetes
Codenotary unveiled Codenotary Trust, a SaaS platform that leverages artificial intelligence to detect, prioritize, and autonomously remediate security, configuration, and performance issues across Linux, containers, VMs, and applications. The solution is built for junior and mid‑level administrators, addressing the talent gap...

Fortanix Showcases Confidential AI Innovation at NVIDIA GTC 2026
Fortanix announced its participation at NVIDIA GTC 2026, where it will showcase the Confidential AI platform that protects AI models, prompts, and sensitive data throughout the training and inference lifecycle. The solution leverages encryption‑in‑use and hardware‑isolated trusted execution environments to...

Push Security Adds Malicious Browser Extension Detection to Block Threats in Employee Browsers
Push Security has introduced a malicious browser‑extension detection and blocking feature within its browser‑based security platform. The capability leverages a continuously updated intelligence database to automatically block known‑bad extensions and provide real‑time visibility into all extensions across employee browsers. Administrators...

HHS Launches Cybersecurity Module Within RISC 2.0 Toolkit
The Administration for Strategic Preparedness and Response (ASPR) has added a cybersecurity module to its Risk Identification and Site Criticality (RISC) 2.0 Toolkit, giving health systems a standardized way to assess cyber risk. The module uses a questionnaire scored against the...

Ending the "Silent Drop": How Dynamic Path MTU Discovery Makes the Cloudflare One Client More Resilient
Cloudflare One’s client now incorporates Dynamic Path MTU Discovery (PMTUD), allowing it to actively probe and adjust packet sizes instead of waiting for ICMP feedback. By testing packet sizes up to 1281 bytes and beyond, the client automatically selects the optimal...

ContextCrush Flaw Exposes AI Development Tools to Attacks
Security researchers at Noma Labs disclosed a critical flaw named ContextCrush affecting the Context7 MCP Server, a popular component that feeds documentation to AI coding assistants. The vulnerability stems from unsanitized custom‑rule entries, allowing attackers to embed malicious instructions that...

LatAm Now Faces 2x More Cyberattacks Than US
Latin America is now the world’s most targeted region for cyber threats, with organizations confronting roughly 3,100 attacks per week—about twice the volume seen in the United States. Check Point’s March 2026 report shows ransomware, infostealers, banking malware and botnets...

Exposure Is the New Currency of Risk: Why Cybersecurity Speaks the Language of Business
Cybersecurity is evolving from a patch‑centric practice to Exposure Management (EM), a framework that quantifies an organization’s attack surface in business terms. EM aggregates vulnerability, cloud, identity and attack‑surface data into exposure scores tied to revenue, compliance and brand reputation....

Manufacturers Spending More On Cybersecurity Yet Cyberattacks Only Account for 5% of Downtime, Research Reveals
Manufacturers are boosting cybersecurity budgets, yet a new Macrium‑Newton X study finds cyber incidents account for just 5% of production downtime. The bulk of costly outages stem from internal operational failures—mis‑planned maintenance, configuration errors, and network glitches—creating a widening "recovery gap."...

The Security Playbook Every Journalist Should Know
Journalists face escalating digital threats—from commercial spyware to FBI raids—making robust security protocols essential. A recent Nieman‑to‑Nieman seminar featured experts from the EFF, GIJN, and CISI who outlined practical steps such as threat modeling, device hardening, and emergency response planning....

Uptycs and SAP Team up to Bring Verifiable AI Analysts to Enterprise Cybersecurity Operations
Uptycs and SAP announced a strategic partnership to integrate Uptycs’ AI analyst platform, Juno, into enterprise cybersecurity operations. Juno functions as a virtual analyst, using a glass‑box approach that links AI‑generated insights to a unified telemetry set of roughly 150,000...

Irish-Founded Startup Evervault Raises €21 Million to Advance Encrypted Data Orchestration
Irish‑founded Evervault announced a €21 million Series B round, led by Ribbit Capital with Sequoia Capital and Index Ventures participating, bringing its total financing to €39 million. The developer‑first platform encrypts and orchestrates sensitive data, chiefly for card‑payment workflows, and now processes over...

Detego Global Launches Artefact_Compare For Rapid Device Integrity Verification
Detego Global introduced Artefact_Compare, a new feature within its Detego Analyse AI+ suite that automates device integrity verification before and after field deployment. The tool captures pre‑deployment snapshots, re‑captures post‑deployment data, and automatically flags added, removed or modified files across...

Nigerian Communication Commission Orders Telecoms to Report Cyber Threats Within 4 Hours
Nigeria’s Communications Commission (NCC) has issued a Cyber Resilience Framework requiring telecom operators to report any cyber‑attack to the regulator within four hours of detection. The rule, effective February 2027, applies to major providers such as MTN Nigeria, Airtel Nigeria, Globacom...

Why Portfolio Companies Struggle with Third-Party Cyber Risk
Portfolio companies are grappling with third‑party cyber risk as digital ecosystems expand and vendor reliance grows. Traditional perimeter defenses have eroded, leaving sensitive data and operational resilience dependent on external partners. Lean security teams and rapid onboarding prioritize speed over...

Unanimous Vote Passed on SB 275, the State-Endorsed Digital Identity Program Amendments Bill
Utah’s Senate voted unanimously to pass SB 275 Sub 2, amending the State‑Endorsed Digital Identity Program. The legislation authorizes a wallet‑based digital ID that places data control and privacy in the hands of citizens. It builds on the SB 260...

DPRK Hackers Target Crypto Firms, Steal Keys and Cloud Assets in Coordinated Attacks
Suspected North Korean‑linked threat actors launched a coordinated campaign against cryptocurrency firms, exploiting the critical React2Shell (CVE‑2025‑55182) remote code execution flaw in React Server Components and Next.js. After gaining initial web‑app access, they leveraged stolen AWS tokens to enumerate and...

Where Multi-Factor Authentication Stops and Credential Abuse Starts
Multi‑factor authentication (MFA) is effective for cloud and federated apps, but many Windows authentication paths—interactive logons, RDP, NTLM, Kerberos tickets, and service accounts—remain outside its protection. Attackers exploit these gaps using stolen passwords, pass‑the‑hash, or forged tickets, gaining lateral movement...

Arknights: Endfield Community Raises Alarm over Pull Tracker Tools After Reports of Hacked Computers
The Arknights: Endfield community is warning players against third‑party pull‑tracker sites after reports that uploaded game logs exposed session tokens, leading to compromised computers and stolen data. The most cited case involves streamer Fobm4ster, who had to reinstall Windows 11 following...