
Stellar Cyber 6.4.0 Reduces Alert Noise and Speeds Investigations with Autonomous SOC Capabilities
Stellar Cyber has released version 6.4.0, adding autonomous SOC capabilities that automate alert triage and generate AI‑driven case summaries. The platform promises 60‑80% analyst time savings and up to 70% reduction in alert noise through its Agentic AI and Verdict Signal Check. New features include phishing auto‑triage, custom case queues, and enhanced detections for web‑app exploitation and VPN credential abuse. The update also expands the Open XDR ecosystem with seven connectors, 23 parsers, and 74 integration enhancements.

You're Doing Vulnerability Management Backwards: Here's the Fix
The article argues that vulnerability management should start with asset importance rather than CVSS scores. It proposes an asset‑first framework that classifies systems into business‑impact tiers and adds exploit likelihood to prioritize remediation. For MSPs handling many client environments, this...

Attackers Abuse LiveChat to Phish Credit Card, Personal Data
Researchers at Cofense have uncovered a new phishing campaign that hijacks the LiveChat SaaS support platform to steal sensitive data. The attackers impersonate Amazon or PayPal, using email lures that direct victims to a LiveChat‑hosted page where a human‑operated operator...

Kingston Debuts XTS-AES 256-Bit Secure Hardware USB Drive
Kingston Digital has launched the IronKey Locker+ 50 G2, a next‑generation hardware‑encrypted USB flash drive. The device features FIPS 197‑certified XTS‑AES‑256‑bit encryption, digitally signed firmware to block BadUSB attacks, and brute‑force password protection that locks out users after ten failed attempts. It supports both...

Handala Hackers Exploit RDP and NetBird in Coordinated Wiper Attacks
Handala Hack, an Iranian state‑linked group known as Void Manticore, has been conducting coordinated wiper attacks using compromised RDP sessions and the legitimate mesh‑networking tool NetBird. The actors gain initial access via stolen VPN credentials, dwell for months, harvest domain admin...

Orca Security Advances AI-First Cloud Defense with Autonomous Agents and Runtime AI Threat Detection
Orca Security unveiled a suite of AI‑first capabilities ahead of RSAC 2026, adding autonomous Threat Investigation and AppSec Triage agents, real‑time Runtime AI Threat Detection, Orca Missions, and Code Reachability Analysis. The enhancements aim to cut through alert overload, prioritize...

Escalated.io Releases Next Generation Software Update for Its Invalid Traffic Filtration Service
Escalated.io announced a next‑generation update to its invalid traffic filtration service, extending its JavaScript pixel and pre‑bid solutions. The upgrade accelerates detection, allowing many fraud types to be identified on the first impression rather than after accumulating data. Real‑time blocking...

Russia-Linked Espionage Campaign Targeting Ukraine Using Starlink and Charity Lures
A Russia‑linked hacker group known as Laundry Bear launched a new espionage campaign against Ukrainian entities in February, distributing a backdoor called DrillApp hidden in documents about Starlink terminals and the Come Back Alive charity. The malware activates through Microsoft...

Elisa Praises Placing Cybersecurity at Heart of Operations
Elisa, Finland's incumbent telco, consolidated its cybersecurity and service operations into a hybrid cSOC in 2011, merging monitoring and response functions. The integrated centre now watches services from the customer perspective, automatically rectifying deviations and involving engineers only when needed....

NinjaOne Launches AI-Driven Vulnerability Management to Speed Detection and Remediation
NinjaOne unveiled an AI‑driven Vulnerability Management module built directly into its unified endpoint platform. The service delivers real‑time vulnerability assessment, patch confidence scoring and autonomous remediation, aiming to slash mean time to remediate. By operating server‑side, it avoids endpoint performance...

Security Flaw in AWS Bedrock Code Interpreter Raises Alarms
Security researchers at Phantom Labs demonstrated a DNS‑based data exfiltration technique targeting AWS Bedrock AgentCore Code Interpreter. By embedding malicious instructions in a CSV file, attackers can force the interpreter to issue DNS queries that act as a covert command‑and‑control...

CamelClone Uses Public File-Sharing Sites in Government Cyberattacks
Operation CamelClone targets government, defense, diplomatic and energy agencies in Algeria, Mongolia, Ukraine and Kuwait, using spear‑phishing ZIP archives that contain LNK shortcuts to launch PowerShell commands. The shortcuts download a JavaScript loader, HOPPINGANT, from the public file‑sharing site filebulldogs.com,...

U.S., UK, Canada Start Operation Atlantic to Disrupt Crypto Approval-Phishing Scams
Operation Atlantic, a joint U.S., U.K. and Canadian initiative, was launched to dismantle crypto approval‑phishing scams that trick users into granting wallet permissions. These schemes helped generate $14 billion in on‑chain fraud in 2025, with projections near $17 billion for 2026. The...

Why Security Validation Is Becoming Agentic
Traditional security validation relies on disconnected tools like BAS platforms, periodic penetration tests, and vulnerability scanners, creating blind spots as attackers chain identity, cloud, and vulnerability exploits. This fragmentation forces manual data stitching, delaying insight and remediation. Emerging agentic exposure...

Fingerprint’s MCP Server Turns Device Intelligence Into Real-Time AI-Powered Fraud Insights
Fingerprint has launched an open‑source Model Context Protocol (MCP) Server that lets any AI assistant or chatbot query its device‑intelligence platform in real time. The server uses the open MCP standard, enabling fraud analysts to ask natural‑language questions—such as device...

AI Impersonation Is Here: How Industry Leaders Are Preparing for the Deepfake Fraud Era
The Deepfake Summit in Houston warned that AI‑driven impersonation, deepfakes and synthetic identities are outpacing traditional fraud defenses. Speakers highlighted how injection attacks and autonomous AI systems are accelerating fraud across banking, payments and government services. The event called for...

How to Defend Against Recruitment as the Attack Surface
Recruitment of software engineers is emerging as a critical attack surface, with nation‑state actors—most notably North Korea—exploiting new hires to infiltrate vulnerable systems. These insiders often receive deep privileges, allowing rapid lateral movement and data exfiltration. The article outlines a...

Google Unveils Android 17 Advanced Protection Mode to Stop Malicious Services
Google announced Android 17, featuring Android Advanced Protection Mode (AAPM) to harden mobile security for high‑risk users. AAPM blocks app sideloading, disables USB data signaling, restricts non‑accessibility services, and enforces always‑on Play Protect. The release also adds a privacy‑focused Contact Picker...

Microsoft Edge 146 Adds IP Privacy and Local Network Access Controls
Microsoft released Edge 146 stable on March 13, 2026, adding tracking protection changes, IP privacy via Private IP routing, and new enterprise network security policies. InPrivate windows now inherit the standard tracking prevention level, removing the separate setting. The update...
The Best Dark Web Monitoring Services and Bundles
Data breaches surged in 2025, with over 12,000 incidents recorded, prompting heightened demand for breach‑monitoring solutions. Dark web monitoring services scan both hidden forums and publicly accessible hacker sites to flag compromised personal data. Free tools such as Have I...

The Ransomware Economy Is Shifting Toward Straight-Up Data Extortion
Google Threat Intelligence Group reports a clear shift in cybercrime, with data‑theft extortion now accounting for more than 15% of financially motivated incidents in 2025, up from just 2% in 2020. Traditional ransomware deployments have fallen to roughly 31% of...

Singapore’s Malware Spike Reveals an Overlooked Cyber Risk: USB Drives
Kaspersky reported 3,888,967 on‑device threats blocked in Singapore during 2025, a 16.2% increase from the previous year. The majority were worms and file‑viruses spread via USB drives and other removable media. Unlike cloud‑based attacks, these infections require no user click,...

KEEQuant Advances Chip-Scale QKD for Telecom, Data Centers, and Critical Infrastructure
KEEQuant unveiled a commercial chip‑scale quantum key distribution (QKD) system that replaces traditional bulk optics with photonic integrated circuits. The miniaturized solution lowers hardware costs and simplifies deployment, making quantum‑safe key exchange viable for telecom operators, data‑center providers, and critical‑infrastructure...

DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage
The DRILLAPP backdoor, discovered by security researchers, is actively targeting Ukrainian entities, including government agencies and critical infrastructure. It exploits Microsoft Edge's remote debugging interface to execute malicious JavaScript, achieving fileless persistence while evading traditional antivirus solutions. The malware establishes...
.webp?ssl=1)
Fake FileZilla Downloads Spread RAT via Stealthy Multi-Stage Loader
Cybercriminals are distributing a counterfeit FileZilla installer that bundles a malicious DLL, turning the popular FTP client into a delivery vehicle for a sophisticated Remote Access Trojan. The DLL leverages Windows DLL search order to sideload, then launches a multi‑stage,...

Models Are Applying to Be the Face of AI Scams
A growing underground industry in Cambodia and surrounding Southeast Asian hubs is hiring young women as "AI face models" to conduct deep‑fake video calls for cryptocurrency and romance scams. Recruiters post the roles on Telegram, demanding long hours, high call...

The Mounting Cost of Voice Fraud: Revenue Loss, Broken Trust and Operational Strain
A Modulate and Retail Dive survey finds voice fraud now one of retail’s fastest‑growing threats, with eight‑in‑ten leaders experiencing moderate to highly sophisticated attacks in the past year. AI‑generated voice clones can be purchased for as little as $20, enabling...

Top 5 Security Mistakes Startups Make and How to Avoid Them
Startups often prioritize growth over security, leaving them vulnerable to increasingly sophisticated cyber threats. Recent data shows 59 % of SMBs faced attacks in the past year, with financial motives driving 99 % of breaches targeting small firms. Common mistakes include insufficient...

45,000 Malicious IP Addresses Taken Down, 94 Suspects Arrested
Operation Synergia III, an INTERPOL‑led international effort running from July 2025 to January 2026, dismantled more than 45,000 malicious IP addresses and servers used for phishing, malware, and ransomware. The crackdown resulted in 94 arrests, with another 110 suspects under investigation, and the seizure...

JSOC IT’s AUTOPSY Platform Puts Security Stacks Under Live API Verification
JSOC IT launched AUTOPSY, a security verification platform that uses live API integrations to assess an organization’s security stack before a breach occurs. Its flagship product, READY, replaces self‑reported questionnaires with telemetry‑based scores across more than 24 security tools, revealing...
Bliss Breaks Xbox One Security with a Hardware-Level Glitch Attack
At RE//verse 2026, security researcher Markus “Doom” Gaasedelen unveiled "Bliss," a double‑voltage‑glitch exploit that compromises the original Xbox One at the hardware level. The technique injects precise voltage faults into the CPU power rail during early boot, bypassing ARM Cortex memory...

AI Legal Risks: Lisa Fitzgerald on Why Businesses Must Vet AI Use Cases
AI adoption is accelerating, but businesses often overlook legal risks tied to generative tools. Lisa Fitzgerald, partner at Norton Rose Fulbright, warns that feeding confidential or personal data into public AI platforms can trigger cross‑border data transfers, privacy breaches, and...

What the Recent PayPal Breach Says About Modern Web Risk
In February 2026 PayPal disclosed that a coding flaw in its Working Capital loan app unintentionally exposed names, emails, phone numbers, addresses, dates of birth and some Social Security numbers for nearly six months, from July to December 2025. The...

What Are Your DDoS Testing Options in 2026?
Enterprises must validate DDoS defenses through simulated attacks, and three primary testing models exist in 2026: fully managed services, self‑service tools, and automated cloud‑based solutions. Managed testing offers the highest realism and expert reporting with low internal workload but requires...

China Demands Proof After Costa Rica Blames UNC2814 for ICE Cyberattack
Costa Rica’s state electricity and telecom provider ICE suffered a cyberespionage breach that extracted roughly nine gigabytes of internal email data, which officials linked to the China‑affiliated group UNC2814. The attribution, based on intelligence from Google’s Mandiant unit, follows a...

Hong Kong Watchdog Warns 24-Hour Gym Users of Hidden Costs, Data Privacy Risks
Hong Kong’s Consumer Council has flagged hidden fees and privacy risks at 24‑hour gyms after surveying 11 operators. Nearly half of the gyms impose non‑refundable surcharges that can double the cost for short‑term members. Monthly rates already vary widely, and...
Reliance Industries’ Durga Prasad Dube Outlines ‘10 Laws of Cyber Defence’ Inspired by Sun Tzu
Durga Prasad Dube, EVP & CISO of Reliance Industries, presented a "10 laws of cyber defence" at ETCISO Secufest 2026, framing modern security through Sun Tzu’s *Art of War*. He stressed that most breaches stem from visibility gaps rather than sophisticated attackers and...

When Insider Risk Is a Wellbeing Issue, Not Just a Disciplinary One
The article argues that insider risk should be viewed primarily as a wellbeing issue rather than a purely disciplinary or compliance problem. It highlights that most insider incidents develop gradually from stress, fatigue, disengagement, or external coercion, and are often...

Red Hat and NVIDIA Collaborate for a More Secure Foundation for the Agent-Ready Workforce
Red Hat announced a deeper partnership with NVIDIA to embed the open‑source NVIDIA OpenShell runtime and AI‑Q Blueprint into its Red Hat AI platform. The integration adds sandboxed, deny‑by‑default agent execution within Kubernetes, enabling secure, production‑grade autonomous agents. By coupling OpenShell with...

Malaysia: New Risk Policy Ensures Digital Payment Resilience
Bank Negara Malaysia has issued a new Technology Risk Management Policy for payment service providers, consolidating existing tech‑related requirements into a single framework. The policy introduces a tiered, proportional approach that aligns security and resilience obligations with the size and...

Why Must Businesses Be Certain About AI-Driven Operational Decisions
The article argues that effective management of Non‑Human Identities (machine identities) is essential for secure, AI‑driven operational decisions in cloud environments. It outlines how NHIs—comprising secrets and permissions—reduce breach risk, improve compliance, and cut costs through automation and lifecycle governance....

Venus Protocol Exploited for $3.7M Through Supply Cap Manipulation: On-Chain Analysis
Venus Protocol on BNB Chain suffered a $3.7 million exploit that manipulated its supply‑cap controls. The attacker leveraged Thena (THE) tokens to bypass maximum supply limits and borrow multiple assets, likely using flash‑loan or price‑manipulation techniques. In response, Venus paused borrowing...
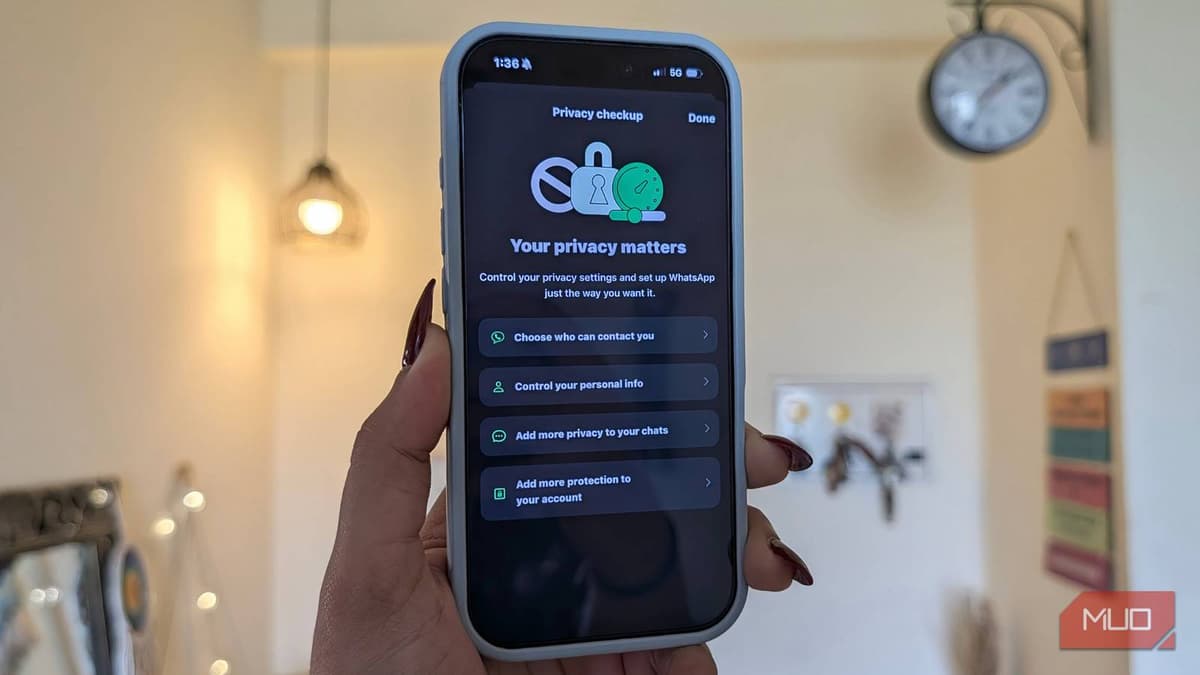
I Dug Through WhatsApp's Settings and Found some Surprisingly Useful Privacy Options
WhatsApp now offers several hidden privacy settings that can dramatically improve user security. On both iPhone and Android, users can enable block unknown account messages, protect IP addresses during calls, and disable link previews through the Advanced menu. Android adds...

Don't Panic over New Linux Exploits: How to Check if Your PC Is Affected in Under 5 Minutes
The article guides Linux users on quickly confirming whether a newly reported CVE affects their system. It outlines step‑by‑step checks for Debian, Ubuntu, and RHEL, including package version comparison and kernel verification. The author emphasizes that most distro teams release...

Betterleaks, a New Open-Source Secrets Scanner to Replace Gitleaks
Betterleaks, an open‑source secrets scanner created by the original Gitleaks author, aims to supersede Gitleaks with a faster, more accurate engine. It scans directories, files, and Git repositories using customizable CEL rules and BPE tokenization, achieving 98.6% recall on the...

Business Bosses Told to Check Details After Companies House Glitch
A technical fault in the UK Companies House web‑filing platform on Friday let users navigate back and edit or view other firms' records, exposing personal details of directors for up to five million companies. The glitch prompted an immediate suspension...

Resecurity Unveils Latest Threat Intelligence Solutions at CyberBay Summit 2026 (Tampa, FL)
Resecurity showcased its newest threat‑intelligence solutions at the CyberBay Summit 2026 in Tampa, engaging government, defense, academia, and private‑sector leaders. The company highlighted AI‑driven risk‑management tools and insights on malicious activity tied to the Iran conflict. It also warned of heightened...

‘DM Your Details’: Travellers Warned of Scam Airline Accounts as Iran War Disrupts Flights
Travelers seeking updates on flight delays caused by the Iran war are being targeted by scammers posing as airline support accounts on X. Fraudsters request direct messages, asking for personal or payment details and then use bogus refund links to...

Are Healthcare Data Systems Supported by NHIs Effectively
Non‑Human Identities (NHIs) are emerging as a cornerstone of healthcare data security, offering machine‑level authentication that mirrors a passport‑visa system for digital assets. By managing the full lifecycle—discovery, monitoring, threat remediation—organizations can automate secret rotation and enforce precise access controls...

How Reassured Can We Be with Our Current Cloud Security Strategies
Enterprises are increasingly turning to Non‑Human Identities (NHIs) to close gaps in cloud security. NHIs pair encrypted secrets with permission sets, offering a machine‑focused layer that traditional point tools lack. Integrated NHI platforms deliver end‑to‑end visibility, automated rotation, and decommissioning...