
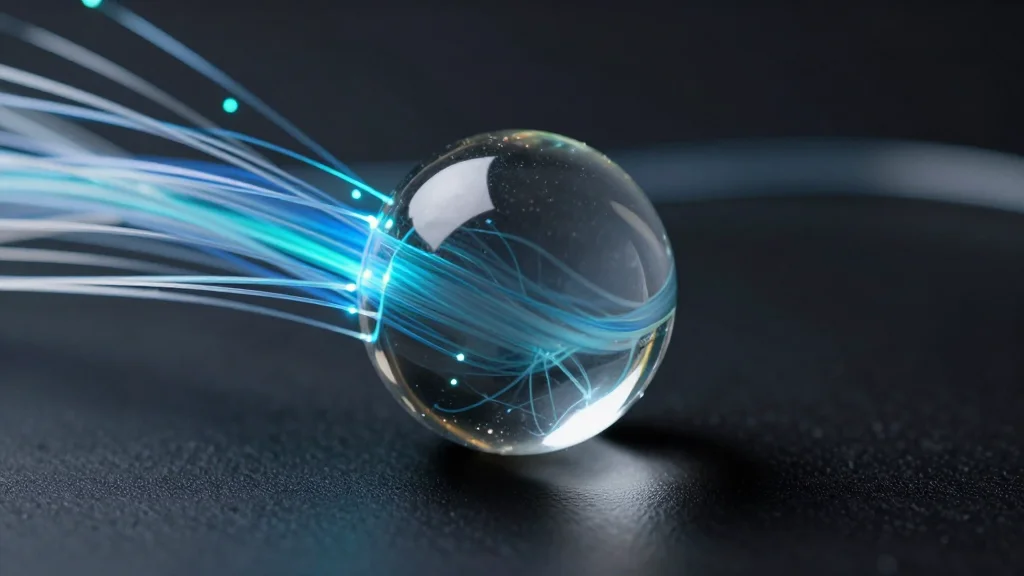
Delta Air Lines Chooses Amazon Leo Over Starlink for In‑Flight Wi‑Fi
Delta Air Lines announced it will replace Starlink with Amazon's Leo satellite platform for its inflight Wi‑Fi, signaling a strategic shift toward tighter cloud integration and higher bandwidth. The move positions Delta at the forefront of a new era of airline‑wide connectivity that blends passenger service with operational data streams.

CEO Survey Shows AI Yet to Boost Productivity, Reviving Solow Paradox
A new study of 6,000 chief executives across the U.S., U.K., Germany and Australia reveals that 90% see no productivity or employment gains from AI. Executives still expect modest future benefits, sparking a fresh debate over the Solow productivity paradox...

Hybrid Multi-Cloud Is Becoming the Default Architecture for AI and HPC
Hybrid multi‑cloud is emerging as the default architecture for AI and high‑performance computing as workloads outgrow the capabilities of any single environment. Training, inference, and simulation each have distinct cost, performance, and data‑locality requirements, making pure cloud or on‑prem solutions...

AI Security Shifts to Governance, Data Control, Real Risk
Great roundtable in NY last week with Zscaler on securing the next wave of AI in financial services. The conversation has changed. Less hype, more focus on governance, data control, and real risk.

Keeper Security Adds Enterprise-Grade Approval Governance and Real-Time Visibility to Endpoint Privilege Management
Keeper Security has upgraded its Endpoint Privilege Manager with enterprise‑grade governance tools. The update adds a centralized, role‑based approval framework, configurable approval windows, and real‑time visibility with expanded audit logging. Automated monitoring now enforces policies across Windows, macOS and Linux...

EuroStack and the Kill Switch
Four European vendors—Cubbit, SUSE, Elemento Cloud and StorPool—have announced the EU’s first EuroStack‑style sovereign disaster‑recovery pack, aiming to protect businesses from a potential U.S. kill‑switch that could block access to critical digital services. The initiative is part of a broader...
OpenClaw AI Deployment on Dedicated Servers: A Practical Infrastructure Guide
OpenClaw AI agents require dedicated server infrastructure to meet their persistent, memory‑intensive workloads. Shared or virtual environments cause CPU throttling, I/O latency, and unreliable context handling, forcing costly migrations later. The guide outlines hardware baselines—32 GB RAM, NVMe storage, and dedicated...

Court Ruling in Amazon-Perplexity Case Raises New Questions for Agentic AI in Enterprise Systems
A U.S. federal court in Northern California issued a preliminary injunction in Amazon.com Services LLC v. Perplexity AI, holding that AI agents accessing password‑protected platforms without explicit platform permission may violate the Computer Fraud and Abuse Act and California’s data‑access...

The Backup Myth that Is Putting Businesses at Risk
Businesses often equate backup with protection, but backup only restores data after an outage, leaving operations stalled. Research shows downtime costs average $9,000 per minute, or $540,000 per hour, making rapid recovery essential. While 60% of firms believe they can...

AI Security Fundamentals Unchanged, Just Faster and Messier
I keep hearing “AI security is different.” Not sure I buy that. Most of what teams are dealing with looks very familiar, just faster and messier. Shadow AI, identity, third parties. We’ve seen all of this before. The tooling changed. The fundamentals didn’t.

Legacy Replacements Drive Growth, Cut TCO by Half
Facts. The fastest growing part of 8090 is our practice of ripping out legacy systems for large enterprises and migrating them to pristine, new, well documented and easy to maintain alternatives. It also turns out to be less than 50%...

MUFG Bank Expands Finastra Partnership to Modernize U.S. ACH Payments
MUFG Bank has broadened its multi‑year collaboration with fintech vendor Finastra to modernize its U.S. Automated Clearing House (ACH) services using the Global PAYplus platform. The upgrade, the bank’s third regional rollout, lifts straight‑through processing to over 95% and aligns...

The VMware Deadline that Could Reshape Your IT Strategy
Broadcom’s acquisition of VMware culminates in a mandatory upgrade: all VMware customers must transition to VMware Cloud Foundation (VCF) 9 by October 2027. The compressed timeline forces organizations to evaluate hardware, licensing and operational changes while juggling hybrid‑cloud, container and...

Declaring Independence: Why We Are Starting the “Free Your IT” Movement
Ardoq announced the “Free Your IT” movement, a campaign aimed at breaking the traditional Big Tech lock‑in model that forces enterprises to surrender data control and roadmap autonomy. The initiative promotes open standards, interoperable architectures, and a community‑driven approach to...

The Architecture of Trust: How Enterprises Can Safely Deploy PII in LLMs
Enterprises can now safely process personally identifiable information (PII) within large language models by embedding the models in a purpose‑built protective architecture. The approach combines a fine‑grained entitlement layer that classifies and enforces access rules, end‑to‑end encryption that keeps data...
SK Hynix Begins Mass Production of 192GB SOCAMM2 AI Server Memory for Nvidia Vera Rubin
SK hynix announced on April 20 that it has entered mass production of the 192GB SOCAMM2 memory module, built on a 10‑nm LPDDR5X process and tuned for Nvidia's upcoming Vera Rubin AI platform. The new module delivers more than twice...

Visa Embeds Generative AI in Bank Infrastructure to Power Real‑Time Payments
Visa’s senior vice president and global head of issuing solutions, Kathleen Pierce‑Gilmore, unveiled a strategic push to embed generative AI across the core systems of its banking partners. The move targets legacy batch‑based architectures that hinder real‑time data use, positioning Visa...

South Africa ‘Isn’t Ready’ for AI-Accelerated Cyberattacks
Anthropic unveiled Claude Mythos Preview, an AI model that can pinpoint software vulnerabilities within minutes, raising unprecedented cybersecurity concerns. A mis‑configuration leak revealed the model’s existence, underscoring the speed gap: 77% of organizations globally need over a week to patch,...

7 Reasons You Keep Getting Passed over for CIO
The article identifies seven recurring gaps that keep IT leaders from landing CIO roles, from remaining order‑takers to lacking storytelling skills. It highlights the shift in the CIO’s mandate: 65% now report directly to the CEO, up from 41% a...

How Proactive DEX Strengthens IT Compliance in Financial Services
Financial services firms are grappling with tighter regulations and increasingly complex, distributed IT environments, making traditional reactive compliance models inadequate. Proactive Digital Experience (DEX) management, exemplified by TeamViewer DEX, continuously monitors device health, performance, and user‑experience signals to anticipate issues...
Making AI Actually Work in the Enterprise and More RSAC Conference 2026 Interviews - Aamir Lakhani, Camellia Chan, Ely Abramovitch,...
The episode explores why many enterprise AI initiatives stumble, emphasizing the need for security‑by‑design and clear governance. Fortinet’s 2026 Global Threat Landscape Report highlights a sharp rise in AI‑enabled cybercrime, prompting vendors like X‑PHY to deliver hardware‑enforced safeguards for AI...
Shadow Data Is a Hidden Risk that AI Can Reveal
Shadow data—forgotten copies of sensitive information scattered across endpoints, cloud storage, SaaS tools and generative‑AI prompts—remains invisible to most security teams. Research from Palo Alto Networks shows over 80% of sensitive data lives outside traditional controls, a problem amplified by...

Feroz Sheikh on AI as the Final Puzzle Piece in Modern Agriculture
In this episode, Peter Hai talks with Faraz Sheikh, Syngenta’s Chief Information and Digital Officer, about how AI and machine learning are becoming the missing puzzle piece that turns massive farm data into actionable decisions for growers. Sheikh explains Syngenta’s...

Cisco Patches Critical ISE Vulnerabilities Allowing Remote Code Execution Attacks
Cisco released emergency patches for its Identity Services Engine (ISE) and Webex Services after uncovering multiple critical vulnerabilities. Three ISE flaws (CVE‑2026‑20147, CVE‑2026‑20180, CVE‑2026‑20186) score 9.9 CVSS and enable remote code execution, privilege escalation, and potential denial‑of‑service. A separate Webex...

Sovereign AI Gains Ground in Asia as Control, Compliance, Infrastructure Collide
Sovereign AI is moving from policy talk to concrete actions across Asia, with India funding domestic GPU capacity and a national data platform, Singapore supporting a multilingual regional model, and Vietnam and South Korea tightening data‑control regulations. Enterprises see reliance...

Storage Implications of a Modern IT Architecture
IT leaders are accelerating container adoption, with 71% planning to shift VMs to Kubernetes and 58% targeting stateful workloads such as databases. Persistent storage has become a critical challenge, especially for edge, AI and satellite applications that require data resilience....

Gartner Forecasts 80% of Enterprise Apps Will Be Multimodal by 2030
Gartner projects that 80% of enterprise applications will support multimodal AI by 2030, up from less than 10% in 2024. The shift promises tighter integration of text, voice, image, video and data within single workflows, forcing vendors and CIOs to...

Wyoming Digital Government Summit 2026 to Spotlight State CIO Strategies for Digital Transformation
The Wyoming Digital Government Summit, scheduled for 2026, will convene state and local CIOs to share strategies on AI, cybersecurity, data governance and business continuity. Chief Information Officer Jeff Clines of Wyoming will speak about the value of peer collaboration...
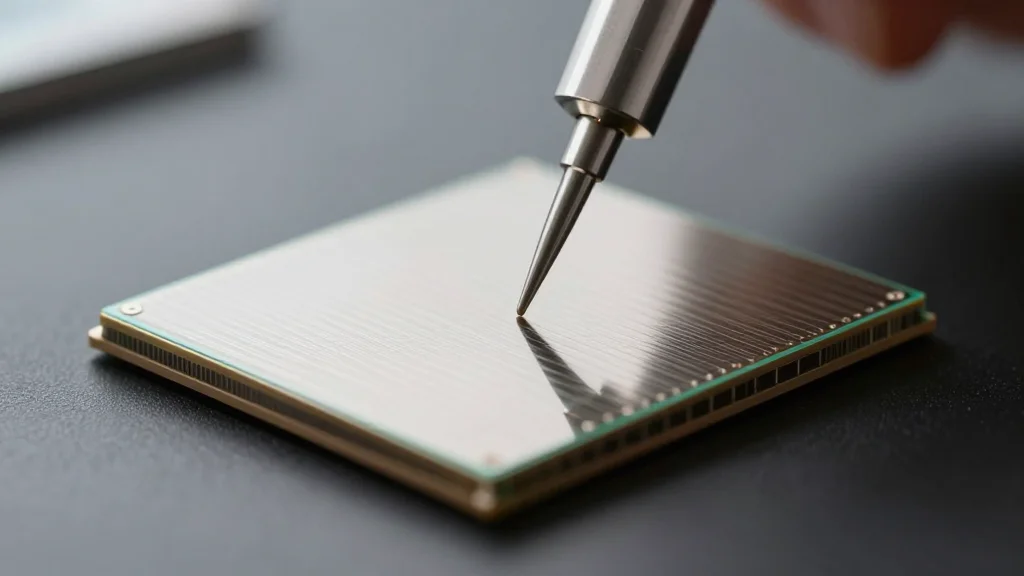
Teradyne Acquires TestInsight to Speed AI and Data‑Center Chip Testing
Teradyne has bought semiconductor software firm TestInsight to embed pre‑silicon validation, pattern conversion and virtual‑test capabilities into its automated test equipment. The move aims to cut debugging time and accelerate AI and data‑center chip roll‑outs, a priority for CIOs managing...

Start Acting Like a C‑Level Leader Today
RT Start acting like a C-level leader now: build your brand, mentor others, clarify priorities, and relentlessly align tech with strategy. #Leadership #CIO @Star_CIO https://t.co/XJxhEl8zHL
Services Australia Tips Virtual Desktop Consolidation
Services Australia announced an early‑stage request for information (RFI) to consolidate its virtual desktop infrastructure onto a cloud‑based desktop‑as‑a‑service (DaaS) platform. The agency is evaluating solutions that can support between 1,000 and 5,000 concurrent users across its own operations and...

TikTok’s US Joint Venture Gains Security Infrastructure Certification
TikTok USDS Joint Venture has secured ISO/IEC 27001:2022 certification, confirming its information‑security management system meets global standards. The certification follows the 2024 Protecting Americans from Foreign Adversary Controlled Applications Act, which forced the sale of TikTok’s U.S. operations to a U.S.‑owned...
Upgrade Only When ROI Declines, Not Vendor Pressure
Modernize systems when ROI diminishes, not just because of vendor pressure. Prioritize backbone tech with a clear plan, factoring in opportunity cost. Move at your own pace. #TechStrategy #DigitalTransformation https://t.co/6vawH0TMWD
MongoDB Global Field CTO Boris Bialek Says Data Layer Is the Bedrock of AI Strategy
In a RedMonk interview, Boris Bialek, VP of Industries and Global Field CTO at MongoDB, argued that data is the only asset enterprises truly control and must serve as the foundation for AI initiatives. He warned that while LLMs and...

Guardrails, Policy-as-Code, Self-Service Drive SaaS Agility
RT Enterprise release boards won't get you SaaS agility. Shift to guardrails over gates, policy-as-code, and self-service delivery. #DevOps #Cloud @Star_CIO https://t.co/e4TERhpY2r

State Leaders Push Expanded Privacy Rules, CIOs Warn of Data‑Security Gap
Amy Glasscock of the National Association of State Chief Information Officers told Broadcast Retirement Network’s Jeffrey Snyder that U.S. states are accelerating privacy and data‑security legislation. The discussion highlighted a rapid rise in chief privacy officer appointments and a widening...
Indeed CIO Rejects AI Token Leaderboard, Emphasizes Outcome Metrics
Indeed's chief information officer Anthony Moisant told Business Insider the company will never publish a public AI token‑usage leaderboard. He argues that tracking token counts creates perverse incentives and that the firm will instead measure AI success by faster product releases...

Cloud Security Maturity at the GovExperience Summit
The Carahsoft GovExperience Summit 2026 highlighted a growing awareness of cloud‑security challenges in the federal government, but revealed significant architectural gaps. Two panels showed that while some officials can articulate multi‑cloud governance, many still treat security as a procurement decision...

Cloudcomputing Acquires Innovate IT, Quadruples UK/US Delivery Capacity
Cloudcomputing, a Portuguese cyber‑security specialist, announced on April 13, 2026 that it has acquired UK‑based Innovate IT Ltd. The deal, whose price was not disclosed, is said to increase the combined firm’s delivery capacity in the United Kingdom and United...

Deloitte and IIF Release Study on Five Enablers Driving Digital Transformation in Finance
Deloitte and the Institute of International Finance (IIF) unveiled a new report pinpointing five overlapping themes that enable digital transformation in banks, insurers and regulators. The study draws on interviews with more than 80 senior leaders and marks the second...

Grant Thornton Survey Shows 78% of CIOs Doubt AI Audit Readiness
Grant Thornton's 2026 AI Impact Survey, featured in Fortune, found that 78% of CIOs lack confidence in passing an AI audit, 46% say AI underperforms due to weak controls, and only 12% consider their workforce ready. The data spotlights a...

India Launches AI Governance and Economic Group to Centralize AI Policy
The Indian government has created the AI Governance and Economic Group (AIGEG), a high‑level inter‑ministerial body chaired by Union Electronics and IT Minister Ashwini Vaishnaw with Minister of State Jitin Prasada as vice‑chair. The group will serve as the apex...

Guide Shows AI Can Pull DevOps Out of Break‑Fix Cycle
The New Stack has released a guide that details three practical steps for moving from a reactive break‑fix model to an AI‑assisted, proactive DevOps approach. It warns that 42% of organizations see major incidents hurting developer morale and argues that...

CISA Flags Critical Apache ActiveMQ RCE Flaw in KEV Catalog, Orders Federal Patch by April 30
The Cybersecurity and Infrastructure Security Agency (CISA) has added a high‑severity remote code execution vulnerability in Apache ActiveMQ (CVE‑2026‑34197, CVSS 8.8) to its Known Exploited Vulnerabilities catalog and ordered all federal agencies to patch the flaw by April 30, 2026. The flaw...

IMF Urges Global Bank Data Sharing to Counter Surge in Digital Fraud
International Monetary Fund Managing Director Kristalina Georgieva called on banks to share cyber‑fraud data after an IMF working paper found U.S. banks accounted for 46% of global incidents from 2014‑2023. The push aligns with recent FinCEN proposals and could reshape...

SugarCRM Rebrands as SugarAI, AI‑Driven CRM to Boost Channel Capabilities
SugarCRM announced a rebrand to SugarAI, positioning its platform as an AI‑driven CRM that emphasizes precision selling and deeper ERP integration. The move aims to turn data signals into actionable guidance for sales teams, addressing long‑standing limits of traditional CRM...

Lifecycle Management on Google Cloud: From Provisioning to Self-Healing with Red Hat and HashiCorp
Red Hat’s Ansible Automation Platform and HashiCorp’s Terraform are joining forces to deliver end‑to‑end infrastructure lifecycle management on Google Cloud. The partnership, highlighted in a webinar on April 20, 2026, demonstrates how provisioning, configuration, and Day 2 operations—including AI‑driven remediation—can be automated through a...

Microsoft, Stellantis Ink Five‑Year AI Deal to Transform Vehicle Software
Microsoft and Stellantis announced a five‑year strategic partnership to co‑develop more than 100 AI initiatives, migrate the automaker’s IT to Azure, and boost cybersecurity. The deal aims to close the technology gap with software‑centric rivals and give Stellantis a unified...
White House Moves to Deploy Anthropic’s Mythos AI Across Federal Agencies
White House OMB chief Gregory Barbaccia announced that the administration is setting up safeguards to let federal agencies use Anthropic’s Mythos AI. The move follows a high‑profile dispute with the Pentagon and a scheduled meeting between Anthropic CEO Dario Amodei...

Zoom Adds World ID Biometric Verification to Curb Deepfake Fraud in Meetings
Zoom announced a partnership with Sam Altman’s World ID to embed biometric human verification into its video‑conferencing platform. The new "Verified Human" badge, backed by iris‑scan technology, targets deep‑fake fraud that has already cost businesses more than $200 million in the...