
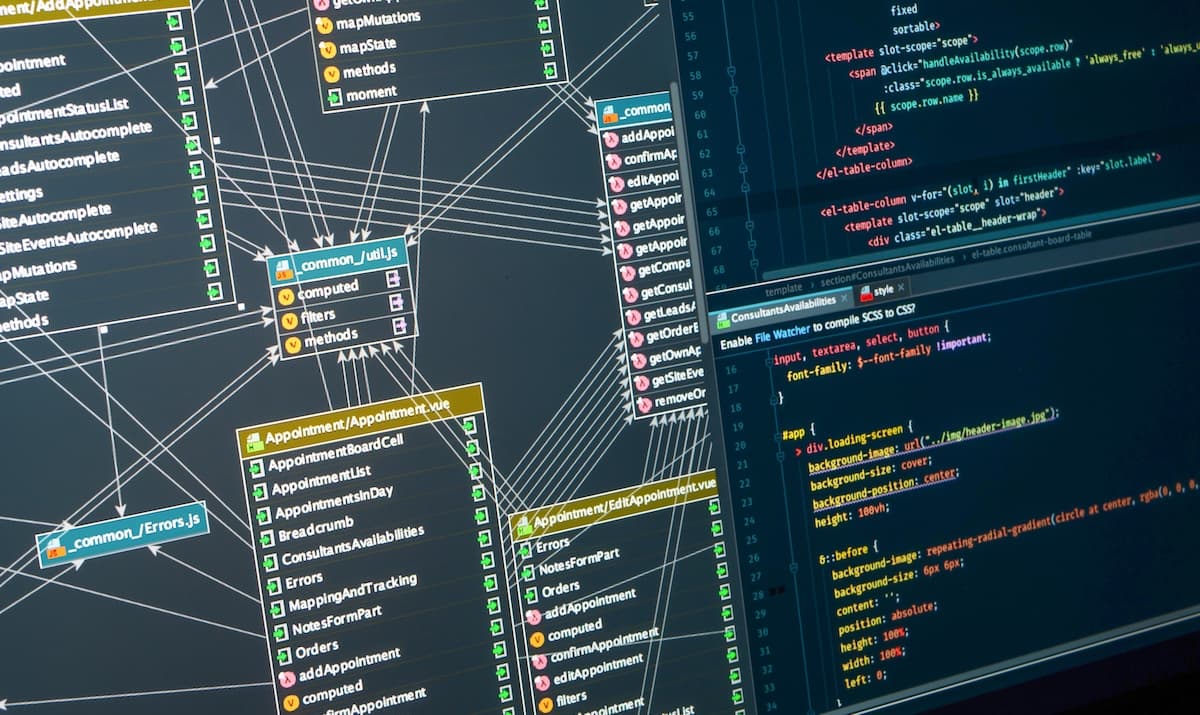
Enterprise Architecture in the Age of AI: More Critical Than Ever
Enterprise Architecture (EA) is becoming indispensable as organizations embed artificial intelligence across their tech stacks. The article argues that AI cannot replace the strategic oversight EA provides, especially when coordinating disparate SaaS solutions and ensuring data governance. It highlights how EA frameworks help manage AI‑driven complexity, reduce redundant tool purchases, and align technology initiatives with business goals. Ultimately, the piece calls for a renewed focus on EA to harness AI’s potential responsibly and profitably.

How the EU’s NIS2 Directive Is Changing How CIOs Think About Digital Infrastructure
The EU’s NIS2 directive reframes cybersecurity risk as an ecosystem issue, forcing CIOs to look beyond internal controls to the full supply‑chain of cloud providers, network operators and software vendors. It expands the definition of resilience to include how interconnected...

The Great Workload Reshuffle: Choices for AI and Analytics
IT leaders are moving from a simple cloud‑first mindset to a workload‑to‑environment alignment strategy as AI, real‑time analytics, and data‑intensive apps proliferate. The model matches each AI or analytics workload to public cloud, on‑premises, or hybrid environments based on performance,...
New Framework Allows EU Firms to Check if 'Sovereign' Cloud Services Are Truly Sovereign
The Cloud Infrastructure Services Providers in Europe (CISPE) has unveiled a Sovereign and Resilient Cloud Services Framework that issues certification badges to verify a provider’s data‑control claims. The scheme distinguishes "sovereign" services, which are owned and operated entirely within the...

OneSpan Adds Nok Nok Labs for $8 M, Boosting ARR to $178 M
OneSpan announced an $8 million acquisition of Nok Nok Labs, contributing $8 million to its annual recurring revenue, now $178 million. The deal expands its authentication suite as the firm pivots from hardware tokens to subscription‑based security, a trend CIOs must weigh.

Data Debt Will Cripple Your AI Strategy if Left Unaddressed
AI success hinges on clean data, yet many enterprises carry years of data debt from legacy practices, mergers, and ad‑hoc solutions. IDC warns that postponing remediation could increase AI project failure rates by 50 percent by 2027. CIOs are urged to...

H&M Appoints Former Inditex Executive as Chief Information Officer
H&M announced the appointment of Diego Teijeiro Ruiz, a veteran of Inditex, as its new chief information officer effective May 25. Ruiz spent two decades at the Spanish fast‑fashion giant, most recently serving as global chief data and analytics officer. He will report...
Cybersecurity Shifts to Executive Strategic Priority in AI Era
Anthropic’s Claude Mythos is reframing cybersecurity at the top level. The risk is no longer a technical issue to delegate, but a core business concern that requires executive attention. This is the wake-up call. In the AI era, cybersecurity becomes a strategic...

How to Close the Machine-Speed Gap in Cyber Defense with Nik Seetharaman of Wraithwatch
In this episode, Nick Seetharaman, founder and CEO of Wraithwatch, discusses how AI can close the speed gap between machine‑driven attackers and human‑limited defenders. He explains Wraithwatch’s AI‑native platform that unifies existing security tools into an intelligent command‑and‑control layer, enabling...

Covered California Teams with Google and Deloitte to Cut Eligibility Work by 40%
Covered California announced an expanded partnership with Google Public Sector and Deloitte to embed Google Cloud's Document AI into its CalHEERS platform. The AI upgrade reduces manual processing by 40%, delivering real‑time eligibility verification for millions of Californians and strengthening...

Hanoi Targets 95% E‑ID Coverage by Year‑End in New Digital Transformation Plan
Hanoi has approved a sweeping digital transformation plan that will require all municipal agencies to adopt artificial intelligence from Oct. 1 and aims to issue electronic IDs to 95% of its residents by the end of 2026. The initiative also sets...

EdgeCore Secures $1.5 Billion to Build Two Hyperscale Data Centers in Northern Virginia
EdgeCore Digital Infrastructure has closed a $1.5 billion construction financing package to build two fully leased hyperscale data centers in Sterling, Virginia. The facilities, slated for occupancy in late 2026 and mid‑2027, will provide 114 MW of power across 685,000 sq ft, positioning the...

Active Exploitation of Apache ActiveMQ Flaw Hits 6,400+ Servers
Shadowserver identified more than 6,400 online Apache ActiveMQ brokers vulnerable to CVE‑2026‑34197, a high‑severity code‑injection bug now being weaponized in the wild. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has flagged the flaw as actively exploited and mandated federal...

SOCs Drowning in Alerts Despite Tool Investment
Security operations centers (SOCs) are overwhelmed by the sheer volume of daily alerts, outpacing analysts' ability to manually enrich and contextualize them. The bottleneck stems from raw alert generation, not a lack of telemetry, leading to longer dwell times and...

Trump Nominates Third VA CIO Since the Start of His Administration
President Donald Trump nominated Gary Shatswell as the Department of Veterans Affairs chief information officer and assistant secretary for information and technology, marking the third White House pick for the Senate‑confirmed role this administration. Shatswell, a senior advisor to VA...

30% of Customers Will Stay
Gartner predicts 30% of customers will remain on-premise post-2030, totaling 10,000. This strategy could bridge the gap between ECC and S/4HANA, a move that's arguably overdue. #SAP #CloudMigration #TechTrends https://t.co/3mqBOMRPcz

CISA Director Pick Sean Plankey Withdraws His Nomination
Sean Plankey, the long‑sidelined nominee for CISA director, formally asked President Trump to withdraw his nomination after 13 months of Senate deadlock. The move follows the recent Senate confirmation of DHS Secretary MarkWayne Mullin, heightening pressure for a permanent CISA...

GTT Rolls Out 2026 Strategy Emphasizing Cloud Services and AI‑Enabled Security
GTT announced a 2026 roadmap that puts cloud services and AI‑enabled security at the core of its enterprise networking offering. The plan builds on the GTT Envision platform and introduces a new AI‑driven cybersecurity framework, aiming to serve thousands of...

Wasabi Lands $250 Million Bain Capital Credit Line for Cloud Storage Growth
Wasabi Technologies closed a $250 million credit facility led by Bain Capital to fund infrastructure upgrades, international expansion and new AI‑focused storage products. The financing follows a $70 million equity round and the recent acquisition of Lyve Cloud, positioning Wasabi to challenge...

AI Demand Is Forcing a Rethink of Data Center Power, Cooling
AI’s rapid expansion is straining data‑center power and cooling infrastructure, prompting operators to redesign projects mid‑construction. At the Data Center World conference, Aligned Data Centers reported a 50% power increase request on an ongoing build, while Omdia warned of supply‑chain...

CIO Reveals Where IT Wastes Time and Money
Where is IT wasting time and money? Former CIO Todd Richardson shares hard truths on labor, efficiency, and strategy in CIO Podcast Ep. 110. 👀 Check it out: https://t.co/JyGcyoFdkz @HCTecTN #healthcarelabor #HITSM

How To Evaluate Whether HCI Is Right for Your State or Local Government Organization
State and local government IT leaders are weighing hyper‑converged infrastructure (HCI) as a way to modernize data centers while meeting compliance, budget and sovereignty constraints. HCI bundles compute, storage and networking into a single, software‑defined platform that mimics cloud‑like elasticity...

CIOs Must Turn AI POCs Into ROI, Prevent Rogue AI
RT CIOs face pressure to go beyond AI POCs and deliver ROI while avoiding the risk of rogue AI. #CIO #AI @Star_CIO https://t.co/IkMrUQXpxe

The Role of Cloud-Native Infrastructure in Payments Modernization
Banks are racing to modernize payments, but legacy systems hinder real‑time processing, increase fraud exposure, and demand costly integrations. A webinar hosted by FIS and AWS highlighted the FIS Money Movement Hub, a cloud‑native solution built on AWS that promises...

Hackers Impersonate IT Help Desk on Microsoft Teams to Gain Access, Steal Data
Microsoft reports a rise in social‑engineering attacks that use Teams chats to impersonate IT help‑desk staff. Hackers request remote‑support sessions via Quick Assist, then leverage DLL sideloading and legitimate tools to infiltrate networks. The method bypasses traditional email‑focused defenses and...
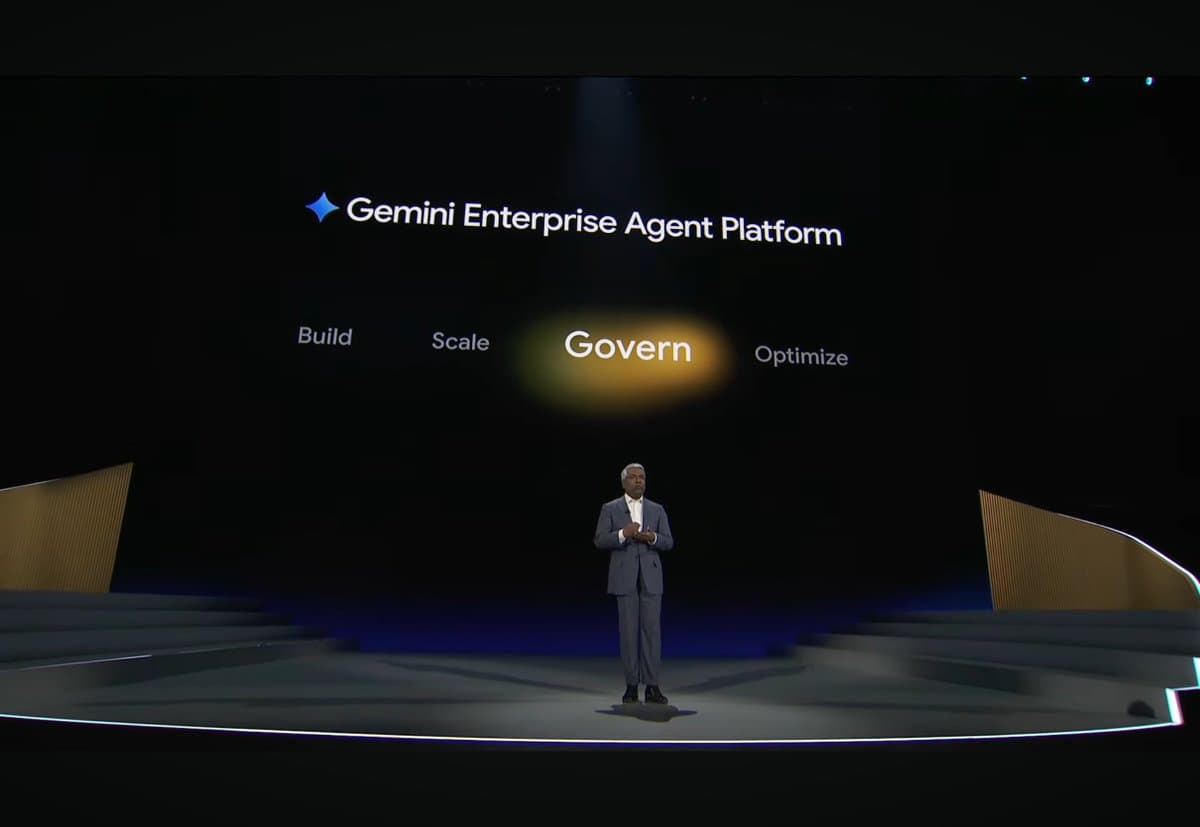
Governance Is the Overlooked Barrier in Enterprise AI
I've been closely following agentic technology. What is the one thing that is holding back enterprises...but most vendors don't discuss? Governance. @GoogleCloud is addressing governance head on with Agent Identity, Agent Gateway and Agent Observability. #CIO #Cloud #AI #GoogleCloudNext
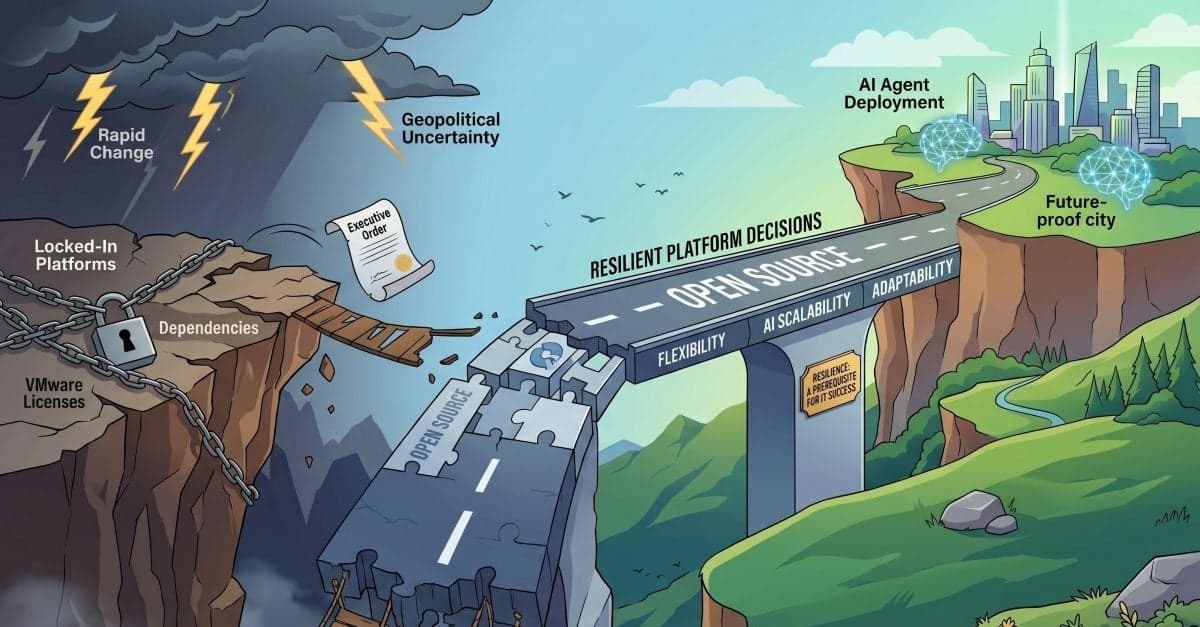
SUSE CTO: IT Teams Need to Become More Resilient in the Face of Rapid Change
At SUSECON 2026, CTO Dr. Thomas Di Giacomo warned that IT teams must prioritize resilient platform choices as rapid licensing shifts, geopolitical uncertainty, and AI adoption accelerate. He urged leaders to move toward open‑source stacks to avoid vendor lock‑in and to design...

Google Cloud Unveils Vision for a Unified Stack
One of the underlying messages customers need to take away from the event is how @GoogleCloud is thinking about the unified stack...and why. More to come on this. #CIO #Cloud #AI #GoogleCloudNext https://t.co/siTmrl9KxZ

Vodafone Business and Google Cloud Deploy AI Concierge and MDR Services for SMBs
Vodafone Business and Google Cloud announced two new SMB solutions—a managed detection and response security service and an AI Concierge powered by Gemini—marking the latest rollout in their $1 billion, ten‑year partnership. The offerings launch first in Germany, with AI Concierge...
NTT DATA Appoints Horace Blackman to Lead Federal Business Unit
NTT DATA announced Horace Blackman as the new leader of its Federal business unit. The former CGI Federal senior vice president brings over 20 years of government‑focused IT experience, positioning NTT DATA to accelerate cloud, AI and mission‑critical modernization for...

Data Center World 2026: AI Pushes Infrastructure to New Limits
At Data Center World 2026, leaders from Oracle, Nvidia and Google warned that AI is forcing a fundamental redesign of data‑center infrastructure. Facilities must now accommodate two distinct workload patterns—massive GPU‑driven training clusters and distributed inference services—while supporting rack power...

Haleon Selects SAP Solutions to Accelerate Growth
Haleon, the global consumer‑health leader, has chosen SAP Business Suite to modernize its digital backbone and embed artificial intelligence across core functions. The move will consolidate finance, supply‑chain, HR and sales processes into a single, real‑time platform, replacing fragmented legacy...

Red Hat Digital Sovereignty Take: Red Hat Confirmed Sovereign Support
Red Hat announced the general availability of Red Hat Confirmed Sovereign Support (RHCSS), a premium support service designed to keep all diagnostics, logs and communications within a customer’s chosen jurisdiction, initially the European Union. The offering builds on Red Hat’s...

BCG Expands Google Cloud Tie‑Up to Scale Gemini AI, Targeting Billions in Client Impact
Boston Consulting Group announced an expanded partnership with Google Cloud to accelerate enterprise‑wide adoption of Gemini AI agents. The collaboration, unveiled at Cloud Next ’26, promises to move clients beyond pilot projects and deliver billions of dollars in measurable impact.

OpenClaw AI Agents Expose Over 28,000 Enterprise Systems to Remote Takeover
SecurityScorecard researchers identified 28,663 unique IP addresses running OpenClaw AI agents that are directly reachable from the internet. About 63% of those deployments are vulnerable to remote code execution, and public exploits for three high‑severity CVEs are already available, putting...
Farmers & Merchants Bancorp Names Shalini Singhal as Chief Information and Technology Officer
Farmers & Merchants Bancorp has appointed Shalini Singhal as its Chief Information and Technology Officer. The move reflects a growing trend among regional banks to merge information and technology leadership under a single executive, aiming to accelerate digital transformation and...

Router Security Hardening Steps for 2026: From Default Credential Audits to Automated Firmware Risk Monitoring
Network edge devices, especially routers, have overtaken PCs as the primary cyber‑attack vector, a trend accelerated by hybrid work in the Netherlands. Threat actors exploit default credentials, unpatched firmware, and exposed management interfaces, making routers the weakest link in many...

Portworx by Everpure Is Redefining Modern Virtualization for Customers with Proven, Enterprise-Ready Solutions
Portworx by Everpure unveiled new Enterprise capabilities that let organizations run both virtual machines and containers on Kubernetes at scale. The platform now supports over 100,000 VM volumes across on‑prem, hybrid, and multi‑cloud environments, offering unified storage, data‑management, and built‑in...
The Silent Failure Between Approval and Delivery
The article argues that securing executive approval is often mistaken for securing execution momentum. After the green light, many initiatives languish in a limbo where ownership is unclear and daily work does not change, leading to silent, untracked failure. The...
Are SBOMs Failing? Supply Chain Attacks Rise as Security Teams Struggle With SBOM Data
Software Bills of Materials (SBOMs) and Vulnerability Exploitability eXchange (VEX) statements were mandated in 2021 to give organizations visibility into component inventories and exploitability. Five years later, supply‑chain attacks such as the March 2026 Trivy and Axios incidents have intensified,...

PCBB Names Matt Wallace EVP and CIO to Accelerate Digital Banking
Pacific Coast Bankers’ Bancshares (PCBB) has hired Matt Wallace as executive vice president and chief information officer. Wallace brings more than two decades of banking‑technology leadership, most recently from The Bancorp, where he oversaw AI, cloud and payments initiatives. The...

The Changing Face of IT: From Operator to Orchestrator
The article argues that the CIO’s role has shifted from maintaining stable IT systems to orchestrating business value across the enterprise. Modern IT must balance running reliable operations with driving digital transformation, linking every investment to measurable outcomes such as...

Ways CIOs Can Prove to Boards that AI Projects Will Deliver
CIOs are under mounting pressure from boards to prove AI projects generate measurable value, as surveys reveal most initiatives have yet to boost revenue or cut costs. Failure rates for AI efforts remain high—up to 95%—prompting a shift from speculative...

A&K Travel Journeys with Colt for Global Quantum-Safe Network
Travel operator A&K Travel Group has partnered with Colt Technology Services to build a global, quantum‑safe network for its portfolio of luxury travel brands. The solution incorporates Arqit’s quantum‑resistant encryption, enabling secure, low‑latency connectivity across more than 100 countries, including...

Default BitLocker Configuration Isn’t Enough: Defending Endpoints Against Physical Attacks
Physical‑access attacks on laptops are becoming commonplace as employees work from cafés, airports and hotels. While many enterprises rely on BitLocker’s default TPM‑only configuration to encrypt drives, researchers have shown that TPM‑bus snooping can capture the decryption key in under...

Silverfort and SentinelOne Partner to Tackle AI-Era Identity Security
Silverfort and SentinelOne announced a partnership that merges Silverfort’s identity discovery and runtime enforcement with SentinelOne’s AI‑powered Singularity Platform. The joint solution extends real‑time protection to human users, machine identities and autonomous AI agents, enabling automatic detection, blocking and isolation...

Enterprise IT Infrastructure Must Enable AI Upskilling, Says Workday UK&I Country Manager
Workday’s UK&I country manager warns that enterprise IT must evolve to support AI‑driven upskilling, as 85% of organisations aim to develop internal talent. Legacy, role‑based HR systems are seen as inadequate by more than half of HR leaders, prompting a...

BlackBox Hosting Bets on Everpure and Points to Growing UK Sovereign Cloud Demand
BlackBox Hosting, a UK‑based managed private‑cloud provider, is betting on Everpure’s all‑flash storage to deliver a truly sovereign cloud as demand for UK‑hosted data climbs. The firm swapped two HP 3PAR racks for two Everpure X50/C50 units, slashing storage footprint...
The Security Metric That’s Failing You
Security teams have let patch‑rate metrics become the de‑facto strategy, but clean patch reports hide far greater risks such as misconfigurations, stale permissions, and legacy network segments. The window for exploiting a disclosed vulnerability has collapsed from weeks to roughly...

Scale Computing Spotlights Edge Wins in Retail, K-12
Scale Computing used its Platform//2026 conference to showcase how its edge‑computing platform simplifies operations for wildly different customers. Taco Bell leverages the solution to standardize omnichannel ordering across dozens of international markets, freeing its internal teams for innovation. In northern...