
Headless Commerce Adoption Jumps 312% as Retailers Ditch Monoliths
Adoption of headless commerce surged 312% in Q1 2026, according to the Commerce Architecture Institute. Retailers such as Athletic Nation and Modern Living report dramatic page‑load and conversion gains, underscoring a rapid move away from monolithic e‑commerce stacks.

Japan's IT Talent Gap Stalls Digital Modernization Plans
Japan faces an IT talent crisis: only 66% of demand is met locally, creating a skills gap for modernization. Alarmingly, just 12% of large companies have modernization plans, indicating a lack of urgency among leaders. #ITJobs #DigitalTransformation #Japan https://t.co/pPL0pqan5n

EY Teams with Rillet to Build Controls‑by‑Design Into AI Finance Platforms
EY US and AI‑native ERP provider Rillet have formed an alliance to embed risk management and audit‑ready controls into finance workflows from day one. The partnership targets firms that have outgrown mid‑market ERP solutions, promising a scalable, governance‑first operating model...

OpenHands Unveils Agent Control Plane to Scale AI Coding Agents Enterprise‑Wide
OpenHands announced the launch of its Agent Control Plane, a centralized operational layer that lets enterprises orchestrate, secure and observe fleets of AI coding agents. The platform targets the gap between experimentation and production, offering workflow‑level cost tracking and least‑privilege...

SAP to Acquire Dremio, Boosting Open Lakehouse Capabilities for Enterprise AI
SAP agreed to acquire Dremio, adding its open‑source lakehouse technology to the SAP Business Data Cloud and HANA Cloud portfolio. The deal, pending regulatory approval, is slated to close in the third quarter of 2026 and is positioned as a...

Bringing New Levels of Security to the Cloud-Native Frontier: Unified Posture Management and Real-Time Protection
Security teams face fragmented tools and “cluster‑blind” EDR in modern OpenShift environments. Palo Alto Networks and Red Hat have launched a deep, native integration that combines the KSPM Connector for continuous posture management with the Cortex XDR Agent for real‑time runtime...

Will SAP Open AI Access to Customers That Haven’t Moved to the Cloud?
SAP is reportedly preparing to let a subset of on‑premise ERP customers, including some SAP ECC users, access its Business AI suite before they complete a cloud migration. The move, expected to be announced at SAP Sapphire in Orlando, would...

Beyond the Inbox: Why Your Domain and Social Media Are the Next Front Lines
Email security alone no longer protects organizations as attackers pivot to brand impersonation. By hijacking subdomains, registering look‑alike domains and creating fake social‑media profiles, threat actors launch phishing and BEC campaigns that bypass SPF, DKIM and DMARC. Red Sift’s research...

Atos Secures $500 M Multi‑year Infrastructure Deal with CNA
Atos has inked a multi‑year contract with insurance giant CNA worth up to $500 million over a 67‑month base term. The deal expands infrastructure, mainframe, and cybersecurity services, cementing a partnership that began nearly ten years ago.

OroCommerce and iPaaS.com Launch Certified Integration to Streamline B2B Data Flows
OroCommerce announced a certified integration with iPaaS.com, giving manufacturers a low‑code, standards‑driven bridge between ERP, CRM and commerce systems. The integration is now live in the iPaaS.com Certified Integration Marketplace, promising real‑time data synchronization across fragmented tech stacks.
From AI Investment to Innovation: What It Takes to Deliver Real Business Impact
Organizations are pouring money into AI, yet many CIOs still see limited ROI. Jeff Baker of PwC argues that moving AI from isolated experiments to enterprise‑wide, business‑outcome‑driven initiatives is essential. He emphasizes pairing AI engineers with business units, securing clean...

Enterprise AI Deployment Is Creating a Security Blind Spot Traditional Architectures Can’t Handle
Enterprise AI deployments are stretching traditional security models, turning data pipelines, model training environments, identity systems and supply chains into new attack vectors. Dell’s senior cybersecurity evangelist Steve Kenniston says up to 90% of AI projects are paused because security...
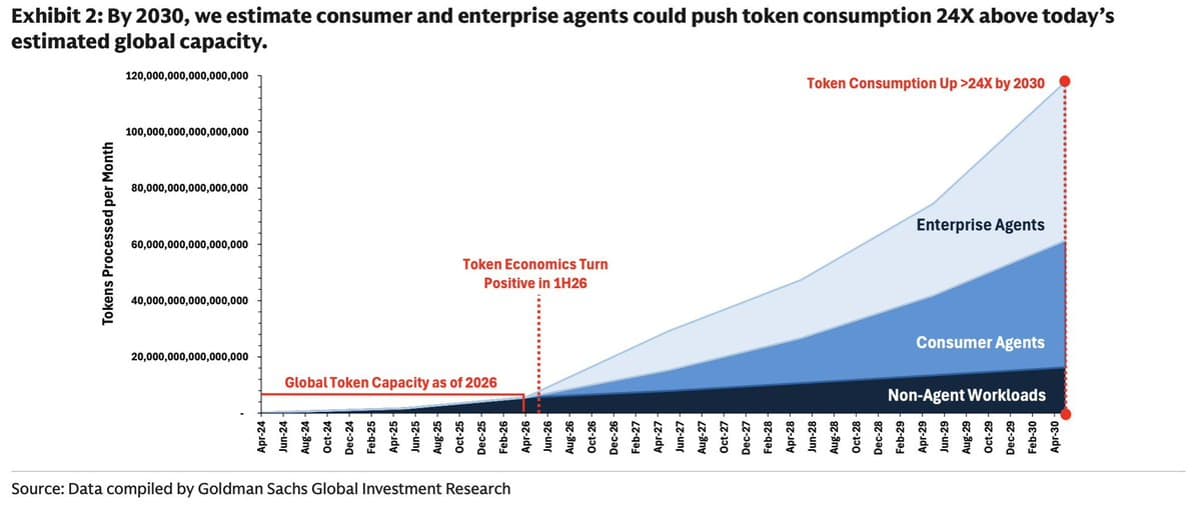
Cheap AI Agents Will Become Enterprise’s New Labor Layer
We are now increasingly able to quantify the enterprise agent inflection point. New data from Goldman Sachs helps paint the picture. When token economics turn positive, AI agents stop being expensive experiments and start becoming scalable digital labor. That changes everything for CIOs. The...

The “Golden Ticket” For Cloud-Native Modernization
Enterprises are reaching a cost‑driven inflection point where maintaining legacy hypervisors is pricier than migrating to cloud‑native platforms. Market consolidation and aggressive licensing shifts have narrowed the window for modernization, prompting firms to overhaul both legacy SAP estates and emerging...

Basware Secures SAP Clean Core Certification, Boosting AP Automation for Enterprises
Basware announced its Connector for SAP Cloud ERP has earned SAP Clean Core certification, making it one of the first accounts‑payable providers to meet SAP's strict integration standards. The certification promises upgrade‑safe AP automation for the thousands of firms facing...

ServiceNow Extends Build Agent to All Major AI Coding Tools, Enforcing Governance by Default
ServiceNow announced at its Knowledge 2026 conference that Build Agent is now generally available in ServiceNow Studio and integrated with every major AI coding assistant, including Cursor, Windsurf, Claude Code and GitHub Copilot. The integration embeds the platform’s governance layer...

ServiceNow Unveils Autonomous Security & Risk Platform with Armis and Veza Integration
ServiceNow announced the Autonomous Security & Risk platform at its Knowledge 2026 event, integrating Armis and Veza to provide a unified graph that governs AI agents, identities and connected assets. The move follows the company's security and risk portfolio crossing...

Pit Raises $16 Million to Offer AI‑Product‑Team‑as‑a‑Service
Pit, a Stockholm‑based AI startup, announced a $16 million seed round led by Andreessen Horowitz. The funding will back its “AI product team as a service” platform that builds custom, production‑grade software for enterprise workflows. The move signals a new approach...

Vodafone Signs German Sovereign Cloud Deal with AWS
Vodafone has sealed a partnership with Amazon Web Services to deliver a sovereign cloud offering for German enterprises and public‑sector clients. Leveraging its recent acquisition of Skaylink, Vodafone will provide migration assistance using AWS‑certified staff and ensure all data resides...

WealthArc Gains ISO 27001:2022 Certification for AI Data Push
Swiss‑born fintech WealthArc announced it has achieved ISO 27001:2022 certification from BSI, confirming its information security management system meets global standards. The certification follows a rigorous audit and underpins the company’s plan to scale to over 1,000 custodian data feeds...

AI in the Enterprise: The Illusion of Control
A recent Digital Boardroom session, led by Oliver Simonnet of Culture AI, highlighted a widening gap between rapid, user‑driven AI adoption and the slower, policy‑centric governance models in enterprises. Based on a survey of 300 senior tech, security and risk...

SA Records Highest Global Cyberattack Rate & Identity Visibility Gap, Study Reveals
Zoho’s State of Workforce Password Security 2026 report shows South Africa leading the world with 36% of organisations reporting cyber‑attacks, the highest global rate. A staggering 79% of firms lack complete visibility into user identities and access, while 71% have...

Sumo Logic Hires Veteran CISO and SVP to Boost AI‑Ready Security Platform
Sumo Logic announced the appointment of Jeremy Powell as chief information security officer and Ben Cody as senior vice president of product management. The hires are aimed at hardening the company’s AI‑ready platform and accelerating product innovation as the market...

AI Coding Agents Could Fuel Next Supply Chain Crisis
Researchers at Adversa.AI uncovered that Claude Code and similar agentic AI coding tools can be duped into executing malicious code with a single trust‑dialog confirmation, granting attackers one‑click remote code execution and opening a supply‑chain vector, especially in CI/CD pipelines....

Security Teams Juggle Frameworks Yet Still Question Risk Accuracy
Question for the security folks on Threads: how are you actually measuring risk? NIST CSF? CIS? Some Frankenstein blend of frameworks plus vendor assessments? Every conversation I have lately ends with "all of the above and we are still not sure it...

Avoid Circular Dependencies: Separate Monitoring From Observed Systems
Your status page or observability system probably shouldn't be using the same system it's supposed to be monitoring. Airbnb found some circular dependencies and made changes to ensure they could do monitoring reliably at scale. https://t.co/rmSAeYTZF2

AXA's Fraught Journey to the Cloud Starts to Pay Off
AXA, the French‑based global insurer, has finally seen tangible results from its decade‑long cloud migration effort. After a rocky virtual‑machine lift‑and‑shift, the company now runs heavily containerised applications in public clouds. The new architecture powers critical claim‑processing and underwriting workloads,...

AI Success Depends on Robust QA and DevOps Maturity
RT 77% of orgs are confident in AI outputs? while many still lack secure CI/CD, automated audit trails, and even basic defect escape metrics. Your QA and DevOps maturity will make or break AI agents in production. #AI #DevOps #QA @Star_CIO ...

Cloudflare Announces Future Plans and Support for Departing Staff
An update regarding the future at @Cloudflare. I’ve shared my full message to the team and details on the support we're providing those departing here: https://t.co/8djT55aVSP

Why the Future of Software Is No Longer Written — It Is Architected, Governed and Continuously Learned
The article argues that by 2026 software development will be driven by generative AI, shifting the CIO mandate from rapid code delivery to architecting and governing enterprise intelligence. AI agents now orchestrate the entire software lifecycle, compressing design and deployment...
AWS Connect Tools Augment, Don’t Replace Your EHR/ERP
AWS Connect Health and Connect Decisions aren’t designed to replace your EHR or ERP, but to augment them. By acting as "connective tissue," these agentic tools help CIOs extract more value from existing investments. https://t.co/sAseu3NKdj #CIO #WhatsNextWithAWS #AI #Cloud #HealthTech #SupplyChain
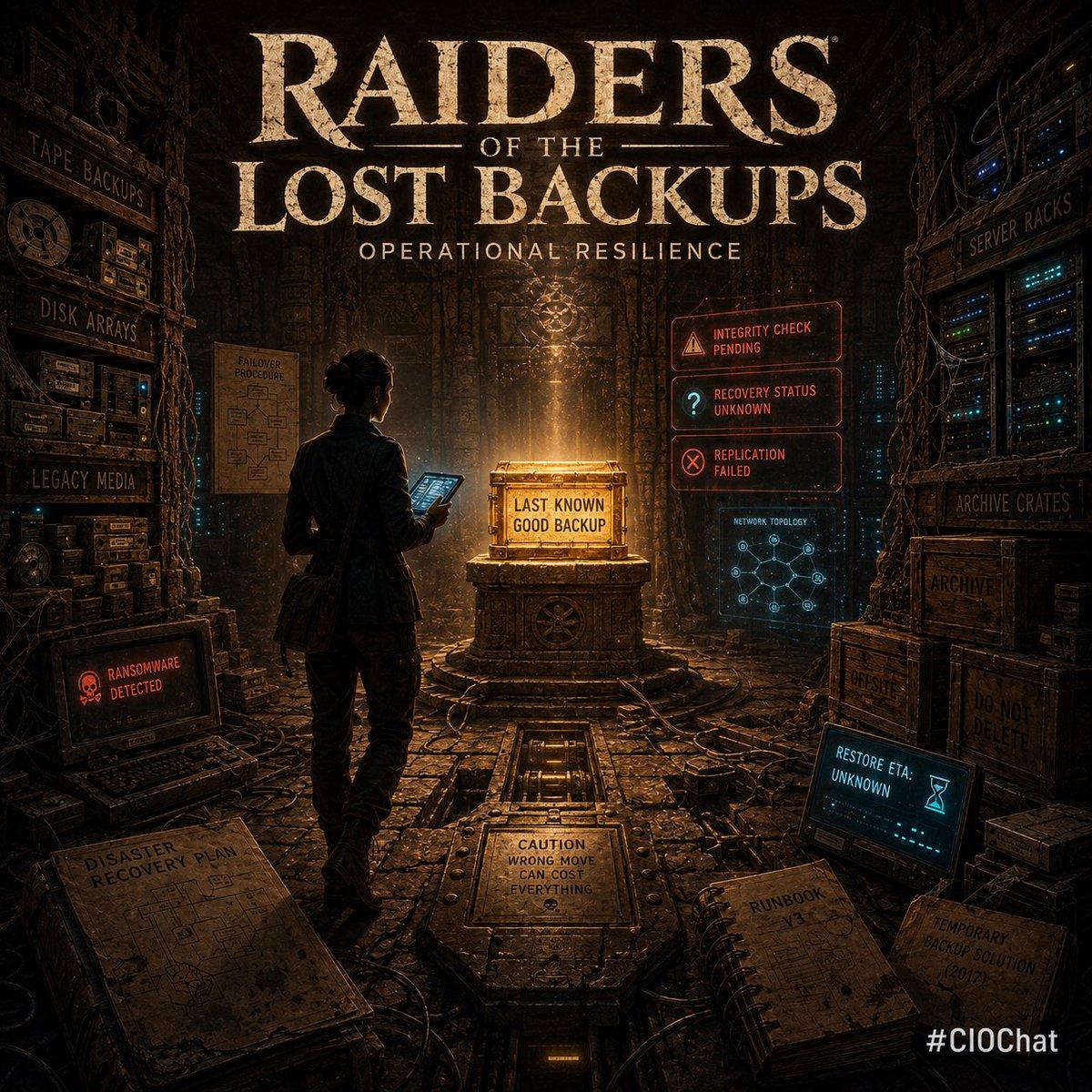
Join Thursday's CIOChat on Operational Resilience at 2 PM ET
#CIOChat Great chat today. Join us at 2pm ET next Thursday. Topic: Operational Resilience Hope you enjoy our movie tie-ins to intro next week’s topic. Please suggest topics and invite your IT colleagues. Every Thursday at 2pm ET. https://t.co/wrwwNUM0he

Why AI Regulation Is Now an Operating Model
Enterprises now face enforceable AI regulations rather than voluntary guidelines, with the EU AI Act fully in force and U.S. states implementing targeted rules such as the Take It Down Act. CIOs must shift from policy‑only approaches to operational controls...

Future CIOs Will Emerge From Diverse Tech & Business Paths
#CIOChat Q4: Looking ahead, where will the next great CIOs come from? Traditional infrastructure and ops paths, product organizations, data/AI teams, management consulting, cybersecurity, or somewhere entirely new? What should ambitious future CIOs be doing right now to prepare? https://t.co/m7f93f81cO

Future CIOs Must Blend Tech, Strategy, and Leadership
#CIOChat Q1: The CIO role has evolving considerably in recent years, from operator to transformation leader, AI strategist, growth partner, and board advisor. Given how much the job has changed, what skills and experiences now matter most in identifying the next...

Vermont Names Ashish Shukla as New Chief Technology and Enterprise Services Officer
Vermont announced Ashish Shukla, a former IRS chief digital officer, as its second chief technology and enterprise services officer, succeeding Mark Combs. Shukla brings federal digital‑government experience and a private‑sector background to lead the state’s digital agenda.

Google's Annual TPU Cycle Accelerates Enterprise AI Efficiency
Speed of innovation matters. Google’s move to an annual silicon cycle with the TPU 8t (training) and TPU 8i (inference) is a game-changer for enterprise AI performance and cost-efficiency. https://t.co/LRR1wOtC6I #CIO #AI #Cloud #Semiconductors #Innovation

Enterprise AI ROI Emerging—Who Captures Production Value?
Second report in our series on AI monetization: if ROI is starting to show up in enterprise workflows, who captures the value as those workloads move into production. Next week, we close the series with CIO/CTO survey results on AI...

Coherence: Where Leadership and AI Success Intersect
Leigh‑Ann Russell, BNY’s CIO, argues that "coherence"—the alignment of talent, clarity, and governance—is essential for scaling AI without creating chaos. BNY’s AI hub, Eliza, now hosts over 220 production solutions and has trained 100% of its workforce, exceeding a 65%...

Most Firms, Especially Japan's Biggest, Stuck in Legacy Systems
A staggering 61% of organizations, and 74% of Japan's largest, rely on outdated legacy systems. Many lack a digital strategy or replacement plan, with over half of modernizers re-customizing instead of adopting scalable solutions. #LegacySystems #DigitalTransformation https://t.co/Z7dKtrG0QJ

Early‑Morning LockBit Siege Revealed by Zach Lewis
#TimTalk - The 4:30 AM Wake-Up Call: Inside a Real-World LockBit Siege with Zach Lewis https://t.co/39y3CX0ybu

Zero Trust in the IT Ops Stack: Securing Hybrid Workloads
Zero‑trust operations are moving from a perimeter mindset to an identity‑centric model, driven by the expansion of hybrid and multi‑cloud workloads. Executives gain stronger risk governance, reduced blast radius, and clearer visibility by embedding continuous verification and least‑privilege controls into...

Define Narrow Tasks, Limit AI Output Scope
"You insert AI into the process with a specific job defined, not any job, and you must give the AI agent a narrow range of possible outputs - not just say, you're an agent, do whatever you want." #CIO #AIStrategy https://t.co/iNfGKDSPeN

Airtel’s Enterprise Arm Launches DPDP Act-Compliant Security Solution
Bharti Airtel’s enterprise division has launched Airtel Secure Workforce, a zero‑trust, fully managed security platform designed to meet India’s Digital Personal Data Protection (DPDP) Act requirements. The solution secures endpoints, devices, networks, applications and data while promising up to a...
Small Issues Stack Up Into Major Crises
A former HP CIO revealed how small, individual problems can combine into a 'perfect storm,' leading to significant failures. Often, it's not one big issue, but a series of manageable ones that create the crisis. #BusinessLessons #Leadership https://t.co/exbcQ8QaB2

Hexion Deploys 30 Petabyte Sovereign Data Archive in South Africa
South African storage firm Hexion has deployed a 30‑petabyte deep‑archive platform, one of the region’s largest privately operated data archives. The solution stores all customer data within South Africa, addressing data‑sovereignty, compliance, and cybersecurity concerns for sectors such as finance,...
Vendor Dependence and Talent Shortage Threaten Tech Modernization
Concerns rise over outdated, customized, and homegrown systems. A shrinking talent pool and over-reliance on vendors create significant risks for technology modernization. This dependency, as highlighted by METI, leaves the industry vulnerable. #TechRisks #DigitalTransformation https://t.co/x5sKgw4MA3

Palo Alto Networks Launches Cortex Cloud 2.1 with AI‑driven Visibility and Automated Remediation
Palo Alto Networks announced Cortex Cloud 2.1, a platform upgrade that expands AI‑model visibility, unifies governance across cloud assets and introduces automated remediation. The release targets enterprises wrestling with fragmented cloud security tools and rising AI adoption.

Executives Favor AI Tools Over Employee Upskilling
Executives are nearly twice as likely to invest in new AI tools than in upskilling their people for the AI era. The technology gap is narrowing. The human gap is widening. #CIO #FutureOfWork #AtlassianTeam26 https://t.co/X27BnHM7xc

Arctera Shifts to Unlimited SaaS Model for Enterprise Compliance
Arctera announced a transition to a fully SaaS operating model that removes traditional limits on data volume, user count and environments, giving large organizations a unified, cloud‑based compliance service. The change aligns product, engineering and go‑to‑market teams under one structure...