
Goldman Sachs CIO Prioritizes Idea‑to‑Production Speed Over AI Usage Tracking
Goldman Sachs chief information officer Marco Argenti says the firm does not track each employee’s AI tool usage. Instead, he gauges productivity by the velocity at which his 12,000 engineers turn ideas into production‑ready software, a shift that challenges the usage‑monitoring trend at peers like JPMorgan and Meta.

ServiceNow Launches Agentic AI Suite, Exposing HR‑IT Priority Clash
ServiceNow introduced its latest agentic AI tools, including Otto and EmployeeWorks, at the Knowledge 2026 conference, revealing a split between IT’s drive for efficiency and HR’s focus on compliance. Executives from CVS Health and analysts warned that misaligned expectations could...

Ray Naicker Named Group CIO of Bank South Pacific, Set to Start Q3 2026
Bank South Pacific (BSP) has appointed Ray Naicker as its new group chief information officer, with his start date slated for the third quarter of 2026. Naicker brings more than two decades of technology leadership, including an 18‑year tenure at...

59% OF CIOs EXPECT A.I. INVESTMENTS TO REDUCE HEADCOUNT AND 86% EXPECT SAVINGS WITHIN 2 YEARS: Is the Equilibrium About...
A Citi Research survey finds 59% of CIOs expect generative AI to cut headcount while 86% anticipate cost savings within two years. The data marks a transition from speculative AI spend to measurable ROI and operational efficiency. Analysts caution that...

Wipro Consulting Chief Says Organizational Readiness, Not AI, Limits Adoption
Wipro Consulting’s managing partner Amit Kumar told Newsweek that the primary obstacle to enterprise AI is organizational capability, not the technology itself. He argues that firms must overhaul governance, talent and change‑management to move from pilots to production‑grade AI.
Govt Pushes IT Governance Amid Enterprise Tech Hodgepodge
Organizations struggle with a tech hodgepodge due to evolved, customized systems lacking clear end-to-end understanding. Government now eyes IT governance and architecture needs. #ITGovernance #TechStrategy https://t.co/rdL9uuKsJl

Accenture Becomes Official Business and Technology Consulting Partner for the WTA
Accenture has been named the official Business and Technology Consulting Partner of the Women’s Tennis Association. The multi‑year deal will start with a revamp of the WTA Player Zone, using AI and data tools to create a seamless digital hub...

Pluralsight Launches Cloud Ready Program to Upskill Enterprise Teams for AI-Driven Cloud Work
Pluralsight announced the Cloud Ready program, a structured upskilling track for enterprise cloud and AI teams. The initiative targets the skill shortfall that hampers cloud ROI, with 75% of cloud leaders planning higher spend yet only half meeting expectations.

ShinyHunters Extorts Universities in New Instructure Canvas Hack
AWS open‑sourced Trusted Remote Execution (Rex) on May 4, 2026, providing an open‑source runtime that intercepts every system call from AI‑generated scripts and evaluates it against host‑defined Cedar policies. The framework is designed to block three common agentic AI failure modes—hallucinated code,...

5,000 Vibe-Coded Apps Just Proved Shadow AI Is the New S3 Bucket Crisis
RedAccess, an Israeli cyber‑security firm, identified 380,000 publicly accessible apps built with low‑code AI platforms such as Lovable, Replit, Base44 and Netlify, and found roughly 5,000 (1.3%) containing sensitive corporate data. The exposures span shipping schedules, clinical trial details, bank...

How to Manage a Virtualization Migration in Healthcare
Healthcare providers are accelerating migrations to new virtualization platforms as rising license fees and bundled pricing strain budgets. Executives like Nutanix’s Scott Ragsdale warn that a migration touches a decade of operational procedures, technical debt, and clinical workloads. Successful moves...

Milwaukee Police Probe Possible Misuse of Flock License‑Plate Reader System
Milwaukee police announced an internal investigation into possible misuse of the city’s Flock license‑plate reader cameras after a former officer was charged for personal tracking. The department has overhauled its audit process, slashing authorized users from roughly 400 to just...

Unleashing AI Across the US Government: The Data Security Challenge Holding Back Decision Advantage
Former DoD CIO Terry Halvorsen warns that while federal agencies are rapidly deploying AI, most of their most valuable data remains locked away because current security architectures require decryption during processing. This "decrypt‑to‑use" vulnerability especially hampers Retrieval‑Augmented Generation (RAG) models,...

Katalyst, E4n Partner To Build AI-Enabled Cybersecurity, Infrastructure MSP Platform
Midmarket MSP Katalyst has partnered with New York‑based e4n to launch an AI‑enabled cybersecurity and infrastructure platform. The deal makes Katalyst the founding company of e4n’s managed services platform, combining Katalyst’s service base with e4n’s AI engineering and acquisition expertise....

Turn Off Direct Send in Microsoft Exchange to Protect Yourself From Phishing
Microsoft Exchange’s Direct Send feature allows legacy devices to transmit email without authenticating, a convenience that can be weaponized by cybercriminals. Attackers harvest public staff content, use AI to mimic writing styles, and send phishing messages that appear legitimate, bypassing...

monday.com Rebuilds Platform Around AI Work Agents for 250,000 Enterprises
monday.com has re‑engineered its software into an AI work platform, placing autonomous agents at the heart of workflows for more than 250,000 enterprise customers. The overhaul adds one‑click links to OpenAI, Anthropic and Microsoft 365 Copilot and promises tighter security...

Canvas Breach Cripples California Colleges, Exposes 280 Million Records
The learning management system Canvas was taken offline after the hacker group ShinyHunters announced it had stolen 280 million records from 8,809 schools. California’s UC and CSU campuses were among the hardest hit, leaving thousands of students unable to access coursework...

The Human Factor: Why AI-Powered SOCs Still Need People in Charge
Artificial intelligence is reshaping security operations centers (SOCs), especially when paired with managed detection and response (MDR) services. Sophos’ white paper shows its AI agents can trim alert noise by more than 60% and cut investigation time by up to...

Oracle Applications Analyst Summit: Fusion Agents Are Shifting From Assist To Decide
At Oracle’s Applications Analyst Summit, the company announced that AI‑driven agents will be exclusive to its Fusion SaaS platform, abandoning on‑premise suites such as EBS, JD Edwards, PeopleSoft, and Hyperion. Oracle is moving from generic assistants to productized agentic applications that...

AI Resurgence Revives Demand for Legacy IT Infrastructure
The AI boom may be reviving parts of the tech industry many thought were obsolete. As AI moves deeper into enterprise adoption, older infrastructure like servers, storage, software stacks and general-purpose chips are becoming relevant again. The pendulum is swinging. AI may...

The Visibility Gap Haunting Autonomous IT
Autonomous IT promises self‑healing networks, but most enterprises lack the visibility needed for reliable AI action. Auvik’s 2026 IT Trends Report shows 70% of leaders are optimistic about AI, yet only 5% have AI embedded in daily operations. The gap...

California Signs $194 Million Bridge Contract with Atos to Keep NG9‑1‑1 on Track
California’s Governor’s Office of Emergency Services awarded a $194 million, 30‑month bridge contract to Atos Public Safety to maintain and expand Next Generation 9‑1‑1 services after scrapping a $450 million regional design. The move aims to keep emergency communications functional for the...

IMF Warns AI-Driven Cyber Attacks Could Trigger Funding Strains for Emerging-Market Banks
The International Monetary Fund warned that AI‑enhanced cyber attacks could cause extreme losses, strain funding and raise solvency concerns for banks and sovereign debt holders in emerging markets. The IMF’s blog highlighted the rapid diffusion of advanced models like Anthropic’s...

Secure Halo Flags Critical CVE-2026-40372 Flaw in Microsoft ASP.NET Core
Secure Halo has warned that a newly disclosed CVE‑2026‑40372 flaw in Microsoft’s ASP.NET Core DataProtection package (versions 10.0.0‑10.0.6) carries a 9.1 severity rating and can let unauthenticated attackers gain system‑level privileges on Linux and macOS. The firm urges immediate key‑ring...

Temporal Launches Serverless Option for Durable Execution Platform
Temporal announced a serverless offering for its Durable Execution workflow platform at the Replay 2026 conference in San Francisco. The new model lets customers run fault‑tolerant workflows on a consumption‑based basis, targeting AI‑driven and long‑running applications.

Why Broadcasters Are Rethinking Infrastructure One Practical Step at a Time
Broadcasters are moving away from piecemeal, hardware‑heavy setups toward software‑defined, hyperconverged infrastructure. The industry’s focus has expanded from pure reliability to include flexibility, efficiency, and the ability to adapt quickly to new formats or remote production models. By consolidating functions...

R1.6 Billion Missing After Hackers Ran Free Inside Major South African Metro’s Systems
The City of Ekurhuleni disclosed a massive cyberattack that left R1.19 billion missing, with only R891 million recovered through back‑billing. Hackers exploited an unsecured municipal Wi‑Fi and VPN to infiltrate billing systems, manipulate invoices and erase debts. An internal investigation revealed insider...

Druva Expands Cyber Resilience to Microsoft Power Platform
Druva announced native support for Microsoft Power Platform, beginning with Power BI, to extend its cyber‑resilience portfolio to AI‑driven analytics workloads. The solution backs up workspaces, reports, dashboards and underlying metadata with immutable, air‑gapped copies that can be restored at a...

Unoptimized Infrastructure Compounds Like Technical Debt
The thing about infrastructure costs: They compound just like technical debt. One unoptimized resource is fine. Fifty unoptimized resources is a budget conversation nobody wants to have…
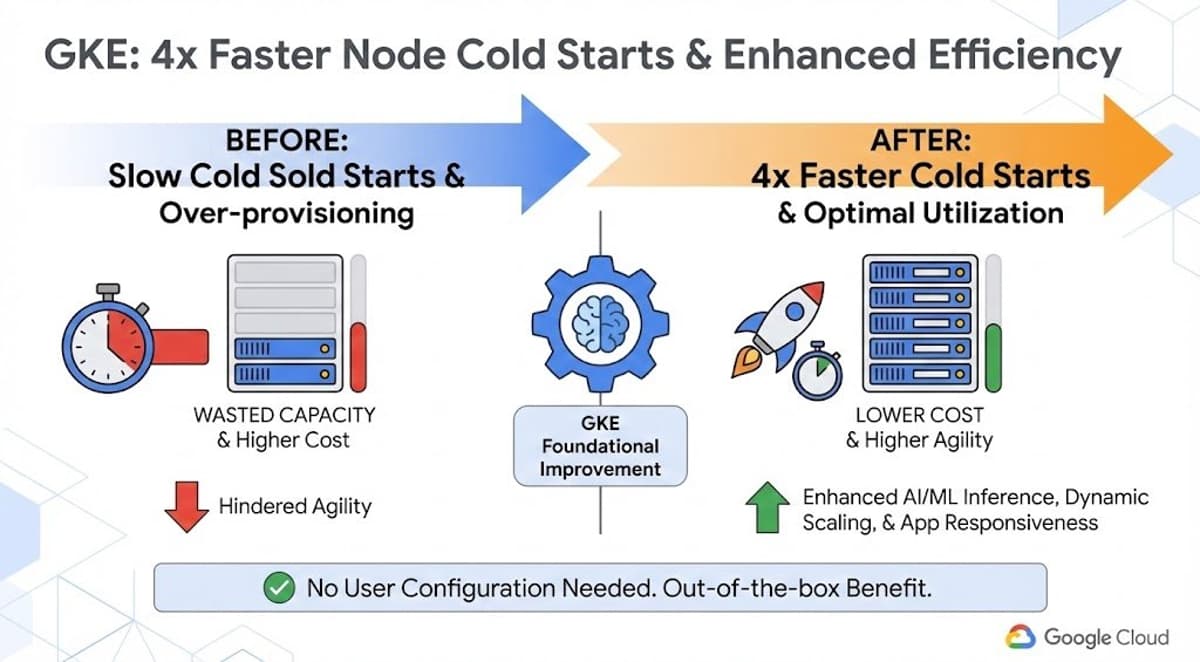
Google Cloud Cuts Cold Starts, Adds Sub‑ms Bigtable Tier
It's apparently "faster performance" Friday at @GoogleCloudTech. With faster node startup for GKE, say goodbye to cold-start latency https://t.co/NU88mzkOPj New Bigtable in-memory tier for sub-millisecond read latency https://t.co/s0GBEMEBQr https://t.co/2JdqpUcLmO

Managing Tech Costs in a Volatile Market
Enterprises face mounting technology spend as cloud AI pricing, licensing and volatile energy costs surge. Companies that rely on public clouds see budgets blown out in months, while on‑premise AI workloads are hit by soaring oil‑driven electricity rates. Greg Holmes...

Agentic Workflows: Google’s Gemini Empowers CIOs
The next frontier isn't just LLMs—it’s Agentic Workflows. Google’s Gemini Enterprise Agent Platform is designed to help CIOs build, scale, and govern autonomous agents. Here are the key takeaways from Google Cloud Next: https://t.co/CqZ5slgQDX #CIO #AI #Cloud #Automation #EnterpriseTech

Shift IT Focus From Spend to Real Value Metrics
RT IT is great at tracking spend, not so great at proving benefits. Time to move beyond inputs and measure "honest time savings, productivity gains, and market share." #CIO @Star_CIO https://t.co/qPKuOVY8TH

CIOs Are Now Orchestrators of AI Business Value
CIOs have shifted from back‑office technology managers to orchestrators of AI‑driven business value. A Deloitte survey shows 80% of CIOs see expanded roles, with more than a third now managing profit‑and‑loss statements. Executives at Marriott and Jabil illustrate how firms...

Manual Updates Reveal Outdated Security Practices
"If your security strategy relies on a sysadmin logging into a server to run apt-get upgrade on a Tuesday morning, you aren't running a modern security program; you’re running a historical reenactment society." #overheard

CIOs Must Prioritize Plugin Security Over AI Hype
A personal agent is only as safe as its plugins. In the wild, we're already seeing extensions act as conduits for malware. CIOs: It’s time to move from "opportunity" to "risk mitigation." 📉 https://t.co/5poCN8at4u #CIO #AI #Cybersecurity #RiskManagement #InfoSec

VA Cuts Disability Claim Backlog 70% with $485M AI Automation Push
The Department of Veterans Affairs has reduced its disability‑claims backlog by over 70% and trimmed average processing time from five months to under three months by deploying AI‑driven automation. A $485 million IBM contract powers the Automated Decision Support system that...
Fragmented AI Costs Fortune 500 $161 B Annually
Non-strategic AI implementations are costing the Fortune 500 an estimated $161B a year in what researchers call the "fragmentation tax" - duplicative work, misaligned priorities, & coordination chaos eroding productivity gains. #AtlassianTeam26 #CIO #AI https://t.co/X27BnHM7xc

AI LLMs Threaten and Bolster Enterprise Cybersecurity, Frontier AI Report Warns
Frontier AI’s new report flags Anthropic’s Claude Mythos as capable of uncovering tens of thousands of high‑severity software flaws in hours, a capability already being leveraged by firms like Mozilla to patch Firefox. The rapid scale of AI‑driven bug hunting...

AI Sprawl: Why Your Productivity Trap Is About to Get Expensive
The article warns that AI adoption is outpacing governance in insurers, creating an "AI sprawl" of isolated models and agents. Rapid, low‑cost tools let claims, underwriting and customer‑service teams launch independent solutions without shared data or oversight. This fragmentation drives...

When Cloud Giants Meddle in Markets
Hyperscale cloud providers are buying massive volumes of DRAM and high‑bandwidth memory to fuel AI workloads, effectively hoarding a finite supply. Their pre‑emptive procurement pushes component prices higher for downstream enterprise buyers, inflating refresh costs and lengthening lead times. As...

Your Refresh Plan Has a CVE Blind Spot
A healthcare client bought servers in 2017 and, due to COVID‑driven supply‑chain delays, extended the vendor’s end‑of‑life timeline to 2026 for software updates and 2028 for security patches. With new hardware now unavailable for up to a year and costs...

The CIO Succession Gap Nobody Admits
The article highlights a hidden CIO succession crisis: most CIOs groom technical architects rather than leaders, leaving a shallow bench when they try to exit. CEOs and boards struggle to identify credible successors because deputies lack decision‑making experience and board...

Your Databases Are Being Watched – Just Not by You
The article warns that most enterprises leave databases unmonitored, allowing attackers to linger for an average 241 days before detection. This governance deficit fuels costly breaches and exposes firms to South African POPIA penalties of up to R10 million (≈$540 k) and average...

Snyk Integrates Claude to Advance AI-Native Application Security
Snyk has integrated Anthropic’s Claude large‑language model into its AI Security Platform, enabling automated discovery, prioritization, and developer‑ready remediation of vulnerabilities across code, dependencies, containers, and AI‑generated artifacts. The platform, called Evo, extends protection to AI models, agents, datasets, and...
AI-Driven Threats Make Cyber Resilience Essential for Survival
Cybersecurity is entering a different era. Frontier AI models can now discover and exploit vulnerabilities continuously and at scale, shrinking attack timelines and expanding risks far beyond traditional defenses. The priority is changing fast. Cyber resilience is no longer optional infrastructure, it...

On the Record - Systems of Everything & Nothing? (1/2)
The article contrasts traditional Systems of Record (SOR)—transaction‑processing platforms like ERP—with emerging Systems of Outcomes (SOO) that deliver purpose‑driven results in the AI era. While SORs provide reliable, auditable data, they are only one input for AI models that now...

CIOs Now Steer Banks' Future, Not Just IT
The CIO is no longer running IT … they’re running the future of the bank - https://t.co/5uAP8RzEpN

The CIO Is No Longer Running IT … They’re Running the Future of the Bank
Boston Consulting Group’s latest report declares the chief information officer the most pivotal role in modern banks. The CIO’s remit has shifted from maintaining legacy systems to orchestrating AI, strategy, and organizational redesign. Executives now must decide which tasks are...
ERP Success Requires Customer and Employee Experience Focus
Executives may see ERP implementation as a necessity, but justification needs more. Focus on improving customer and employee experience with detailed future-state operating and organizational models. #ERP #BusinessTransformation https://t.co/fjPFiG70fH