
$3.425 Billion. One Year. A Wake-Up Call for Every Business Operating in the United States.
Gartner reports U.S. states imposed $3.425 billion in privacy‑related fines in 2025, eclipsing the total of the previous five years. Enforcement has shifted from guidance to hefty penalties, with California alone fining Disney $2.75 million for opt‑out violations. Twenty‑two states already have comprehensive consumer‑privacy statutes, and another 24 are expected to follow within five years, extending coverage to most of the population. Regulators are now targeting AI‑driven decision‑making, making privacy compliance a board‑level financial risk.

AI-Fueled Fraud Creates New Cybercrime Frontier for Risk Managers
At the Riskworld conference, The Hartford’s cyber‑risk leader warned that AI is reshaping fraud, with deepfakes, business email compromise and payment‑transfer scams now eclipsing traditional ransomware. Threat actors use AI‑generated voices and videos to impersonate executives, while automated social‑engineering tools...

Weaver E-Cology Critical Bug Exploited in Attacks Since March
Researchers at Vega uncovered that a critical unauthenticated remote‑code‑execution flaw (CVE‑2026‑22679) in Weaver E‑cology 10.0 was actively exploited from mid‑March. The vulnerability stems from an exposed debug API that lets attackers execute system commands without authentication. Exploits began five days...

Complaints Process Failing
The Office of the Australian Information Commissioner (OIAC) launched a privacy‑awareness campaign during Privacy Awareness Week to improve how agencies handle complaints. A new survey shows 93% of Australians consider data protection vital, yet 52% refrain from filing complaints because...

‘Copy Fail’ Is a Real Linux Security Crisis Wrapped in AI Slop
Researchers have identified a high‑severity Linux kernel flaw (CVE‑2026‑31431) that allows any authenticated local user to gain root privileges. The vulnerability, dubbed “Copy Fail,” affects mainstream kernels released since 2017 and was added to CISA’s exploited‑vulnerabilities catalog. Theori, the firm...

White House Officials Discuss Assessing AI Models That Pose Security Risks
The White House is weighing a cybersecurity‑focused executive order that would create a formal review process for artificial‑intelligence tools deemed high‑risk. Officials plan to establish an oversight group to draft standards for powerful models such as Anthropic’s Mythos, which has...

Kochava Won't Sell 'Sensitive' Location Data Without Consent
Data broker Kochava agreed to stop selling sensitive precise location data without explicit consumer consent, settling FTC privacy charges. The settlement defines sensitive data as GPS coordinates linked to medical, religious, educational, homeless, domestic‑violence, and law‑enforcement sites. Kochava does not...

Webinar to Explore AI Use in Cybersecurity, Health Care Technology
A joint webinar hosted by the American Hospital Association and the Joint Commission will explore how artificial intelligence can strengthen cybersecurity in health‑care settings. The event highlights the newly launched Cyber Resilience Readiness program, recent guidance from CISA and the...

AHA, Joint Commission Announce Cybersecurity Readiness Effort
The American Hospital Association and the Joint Commission unveiled the Cyber Resilience Readiness program, a voluntary initiative designed to help hospitals and health systems sustain safe, quality clinical operations during cyber‑related outages lasting 30 days or more. Unlike traditional IT‑focused...

RMM Tools Fuel Stealthy Phishing Campaign
Security firm Securonix has identified a stealthy phishing campaign, VENOMOUS#HELPER, that has compromised more than 80 organizations across the United States, Western Europe and Latin America since April 2025. The attackers bypass traditional malware by deploying two legitimate, signed remote...

NSW Downgrades Impact of Treasury Cyber Hit
New South Wales Treasury downgraded a previously labeled “significant cyber incident” after an alleged staff member attempted to exfiltrate over 5,600 sensitive documents. The downgrade was announced less than two weeks after the employee was formally charged. Treasury’s chief cyber...

Amazon SES Increasingly Abused in Phishing to Evade Detection
Security researchers at Kaspersky have observed a sharp increase in phishing campaigns that leverage Amazon’s Simple Email Service (SES). The surge is linked to large numbers of exposed AWS IAM access keys found in public code repositories, Docker images, and...

5 Reasons You Should Ditch Cloudflare and Run Your Own DNS Server
The article argues that relying on Cloudflare’s 1.1.1.1 DNS exposes users to privacy risks and service outages, and recommends running a self‑hosted DNS resolver such as Pi‑hole or AdGuard Home. It cites a 2020 KPMG audit that found Cloudflare retained...
Operational Technology Providers Are Feeling ‘Annoyance’ at Exclusion From Anthropic’s Mythos Rollout, Sources Say
Anthropic's Mythos preview, part of the Project Glasswing initiative, was rolled out first to large tech and finance firms, leaving operational technology (OT) providers feeling excluded. OT industry groups and utilities such as American Water have voiced frustration and are...

Canadian Election Databases Use "Canary Traps"—And They Work
Alberta’s elections authority used a classic canary trap to trace a leak of its voter list. The list, legally provided to the Republican Party of Alberta with injected bogus entries, appeared unchanged in a separatist group’s online database, confirming the...

Agentic AI and the Evolution of Code Security in Modern Development
Agentic AI is transforming software development by letting autonomous agents write code, create tests, and iterate without direct human input. This acceleration shortens delivery cycles but also introduces hidden assumptions that can embed vulnerabilities early in the codebase. Traditional post‑CI...
Customers Sue Chime over Alleged Iran-Linked Hack
Chime Financial’s mobile app outage on April 1 prompted the company to assure customers that their money and personal data remained secure. Within days, three class‑action lawsuits alleged that pro‑Iranian hacker group Team 313 breached Chime’s systems and stole Social Security numbers...
Exploit Cyber-Frenzy Threatens Millions via Critical cPanel Vulnerability
A critical authentication‑bypass flaw (CVE‑2026‑41940) in cPanel, WHM and WP Squared received a 9.8 CVSS rating and was patched on April 28, 2026. Within 24 hours of disclosure, researchers observed roughly 15,000 potentially compromised instances, with attackers deploying ransomware and Mirai‑derived botnets. The...
What to Expect at the DigiCert Trust Summit: Join theCUBE May 13
The DigiCert Trust Summit on May 13 will explore how enterprises can build an "intelligent trust" framework that unifies PKI, DNS, software integrity and device identity for AI‑driven environments. TheCUBE research shows 70% of firms have deployed AI security tools,...
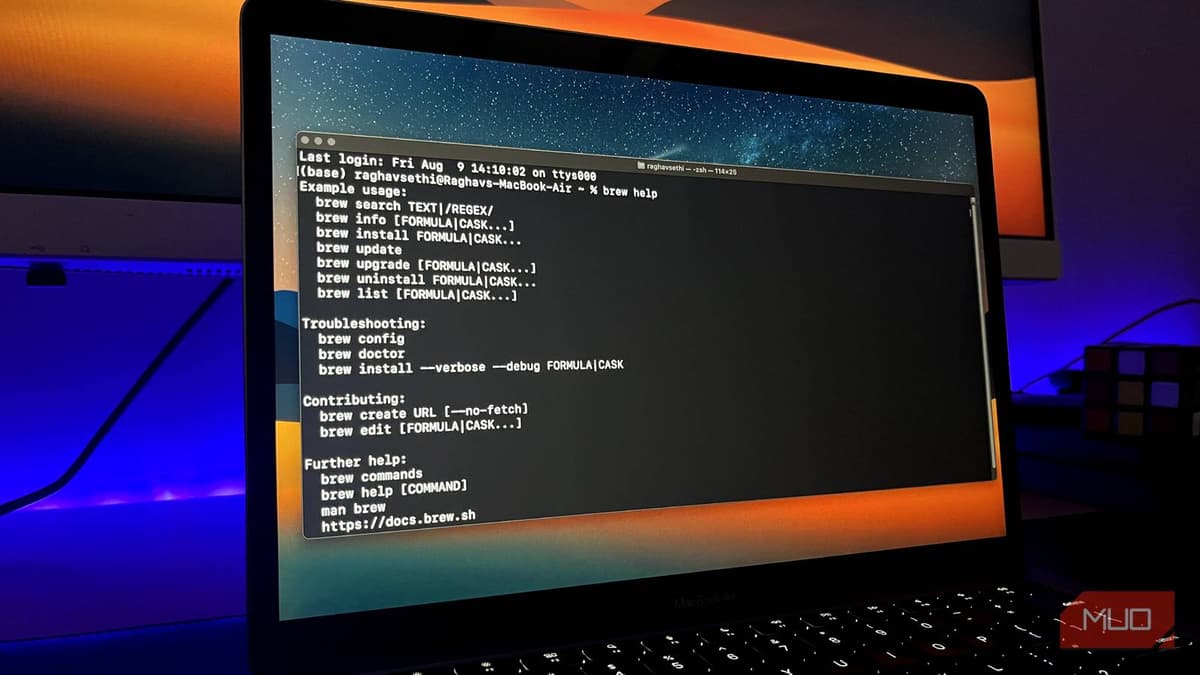
How One Fake Google Ad Can Silently Steal Your Mac’s Passwords
A fake Google ad for Homebrew directs users to a cloned website that asks them to paste a Terminal command, which installs the MacSync infostealer. MacSync can bypass Apple’s built‑in defenses and exfiltrate Keychain passwords, session cookies, and crypto‑wallet data....

Encrypted RCS Between Android and iPhone Launching with iOS 26.5
Apple announced that iOS 26.5 will support end‑to‑end encrypted RCS messaging with Android devices via Google Messages. The feature is available in the iOS 26.5 release candidate and will roll out to users once the final OS ships, displaying a lock icon...
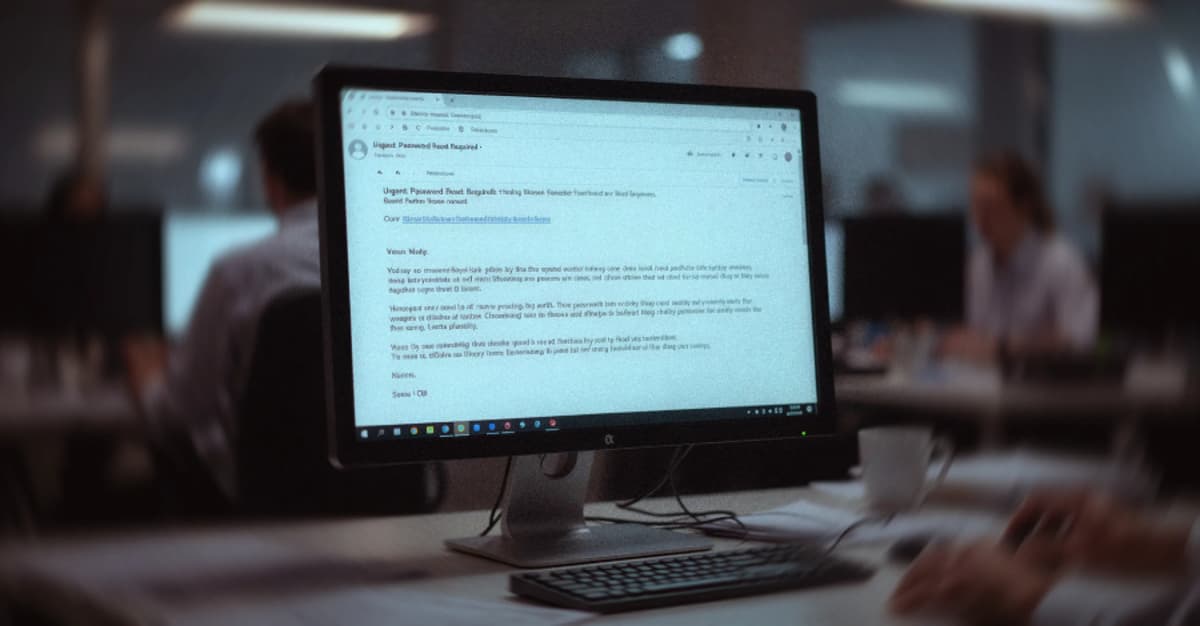
Phishing Campaign Hits 80+ Orgs Using SimpleHelp and ScreenConnect RMM Tools
A phishing campaign dubbed VENOMOUS#HELPER has compromised over 80 U.S. organizations by masquerading as the Social Security Administration and delivering malicious Remote Monitoring and Management (RMM) tools. The attackers use legitimate SimpleHelp and ConnectWise ScreenConnect binaries to create a redundant...

Cybersecurity Startup GRC Pro Lab© Launches AI-Powered SaaS Platform to Close the GRC Talent Experience Gap
Irish‑based GRC Pro Lab has launched a SaaS platform that delivers scenario‑based, hands‑on training for governance, risk and compliance analysts, IT auditors and security professionals. The service replaces passive video courses with simulated engagements across six GRC domains, and includes...

Backdoored PyTorch Lightning Package Drops Credential Stealer
A malicious version of the PyTorch Lightning package (v2.6.3) was published on PyPI, embedding a hidden execution chain that downloads the Bun JavaScript runtime and runs an obfuscated 11.4 MB payload. The payload, dubbed “ShaiWorm,” steals credentials from .env files, browsers...

‘Patch Wave’ Warning: AI May Expose Decades of Hidden Software Bugs
The UK National Cyber Security Centre warned that AI can now uncover decades‑old software flaws at a speed that will overwhelm existing patch‑management processes, creating a “patch wave” of critical updates. Anthropic’s Claude Mythos model identified over 2,000 hidden vulnerabilities,...

Syria Needs a Trustworthy Digital Ecosystem to Support Its Revival
Syria’s median age of 23 contrasts with a 64% offline population, a barrier to post‑conflict growth. After sanctions lifted in 2025, the government partnered with Nokia for trial 5G, launched the $800 million SilkLink fiber‑optic project, and connected to the Medusa...

Europe’s Laws ‘Ill-Equipped’ to Deal with Superhacking AI, Lawmakers Warn
European lawmakers warned that the EU’s current cybersecurity framework cannot cope with AI‑driven hacking tools such as Anthropic’s Mythos, which recently outperformed humans in finding vulnerabilities. In a letter signed by thirty MEPs, they called on Commission Vice‑President Henna Virkkunen...
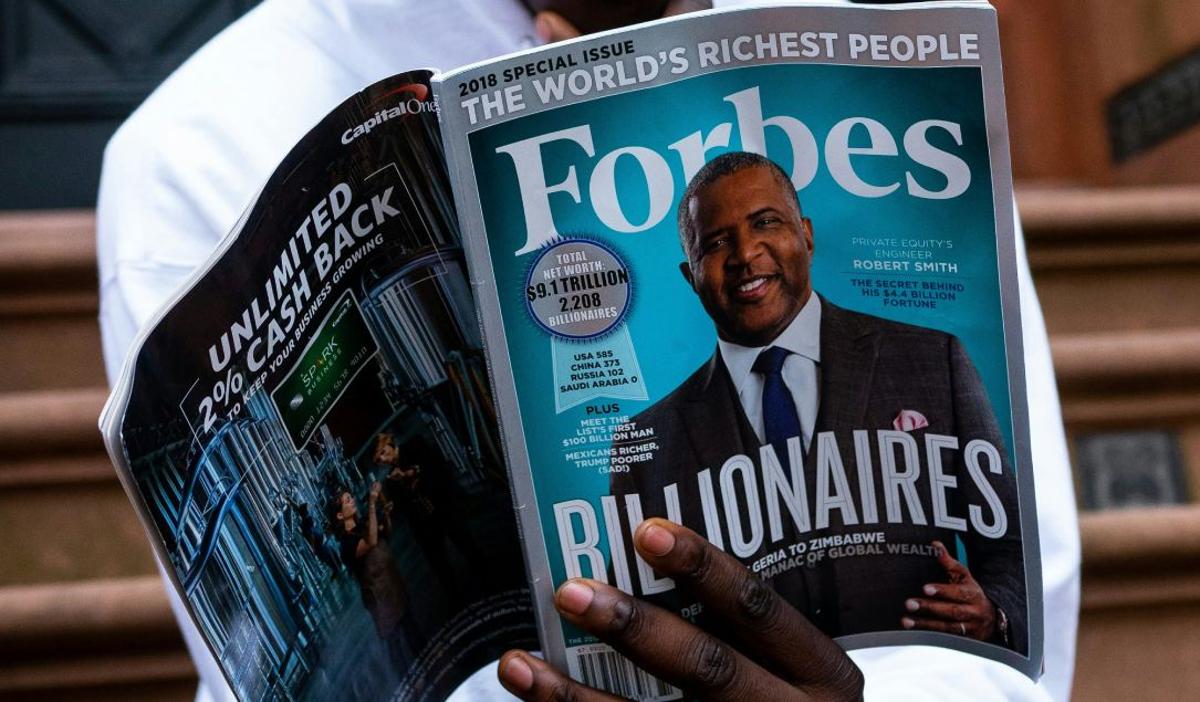
Forbes Preliminarily Agrees to Pay $10 Million to Settle California Wiretapping Lawsuit
Forbes Media has entered a preliminary settlement to pay $10 million and modify its data‑collection practices after a California class‑action lawsuit alleged illegal tracking of website visitors. The agreement mandates clearer notice and opt‑out mechanisms for California residents and acknowledges the...

Tracking Pixels, EU Regulators, and You: A Calm Person’s Guide to What Just Happened
In March and April 2026 France’s CNIL and Italy’s Garante issued guidance clarifying how the ePrivacy Directive and GDPR apply to email tracking pixels. Both regulators treat pixel data as ePrivacy‑subject, requiring consent unless a narrow exemption applies. France allows...

Trellix Discloses Data Breach After Source Code Repository Hack
Trellix, the cybersecurity firm formed from the McAfee Enterprise‑FireEye merger, disclosed that attackers accessed a portion of its source‑code repository. The company says forensic experts are investigating and has found no evidence that the code was altered or exploited. Trellix...

OpenAI Rolls Out Passkeys for ChatGPT, Partners with Yubico
OpenAI unveiled Advanced Account Security, a password‑less sign‑in option for ChatGPT and Codex that supports any FIDO‑compliant passkey or hardware key. The company partnered with Yubico to sell a two‑pack bundle of the YubiKey C Nano and C NFC at a special...

The Coming Wave of Large-Scale Al-Enabled Cyberattacks
Artificial intelligence is reshaping cyber offense as quickly as it empowers defenders, giving attackers tools to automate phishing, deep‑fakes, and large‑scale reconnaissance. Experts warn that the first truly massive AI‑enabled cyberattack will likely be a coordinated, machine‑speed campaign targeting multiple...

Azure IaaS: Defense in Depth Built on Secure-by-Design Principles
Microsoft’s Azure IaaS blog outlines a defense‑in‑depth model built on three Secure Future Initiative principles—secure by design, secure by default, and secure in operation. It details how hardware roots of trust, measured boot, and Trusted Launch protect the host and...

Cisco To Acquire Astrix To Boost Identity Security For AI Agents
Cisco Systems announced it will acquire identity‑protection startup Astrix Security, a move aimed at strengthening its portfolio for securing AI agents and non‑human identities. While the exact price was not disclosed, industry sources estimate the deal at roughly $400 million, higher...

FIDO Alliance Announces Agenda for Authenticate APAC 2026
The FIDO Alliance unveiled the agenda for Authenticate APAC 2026, its first Asia‑Pacific conference on digital identity and authentication, scheduled for June 2‑3 in Singapore. The two‑day event, backed by signature sponsors Google, Visa and Yubico, will feature leaders from...

Ransomware Group Claims Breach of Pro-Orbán Hungarian Media Firm
A ransomware group called World Leaks claimed responsibility for a breach of Hungarian media conglomerate Mediaworks, releasing about 8.5 terabytes of data that includes payroll records, contracts, financial statements, and internal communications. Mediaworks confirmed the incident, warned that the data...

CTSI-Global Names Kevin Beall as Chief Information Security Officer
CTSI-Global, a long‑standing supply‑chain technology provider, has appointed former CTO Kevin Beall as its Chief Information Security Officer. Beall, who spent 16 years at the firm in roles ranging from CTO to VP of Business Insight, will oversee the company’s...

Cyphercor Wins OCI Grant to Boost Critical Infrastructure MFA
Ontario‑based Cyphercor secured an Ontario Centre for Innovation grant to enhance its LoginTC multi‑factor authentication platform for operational technology and manufacturing settings. The funding will add contextual push alerts, biometric checks, and FIDO2‑compatible smart‑card access that work both online and...

Anthropic’s Claude Rolls Out End-User Identity Verification
Anthropic announced that select Claude users must complete a physical government‑issued ID verification (PIDV) using Persona Identities before accessing certain capabilities. The move is framed as part of Anthropic’s AI safety commitments and a response to rising regulatory and abuse...
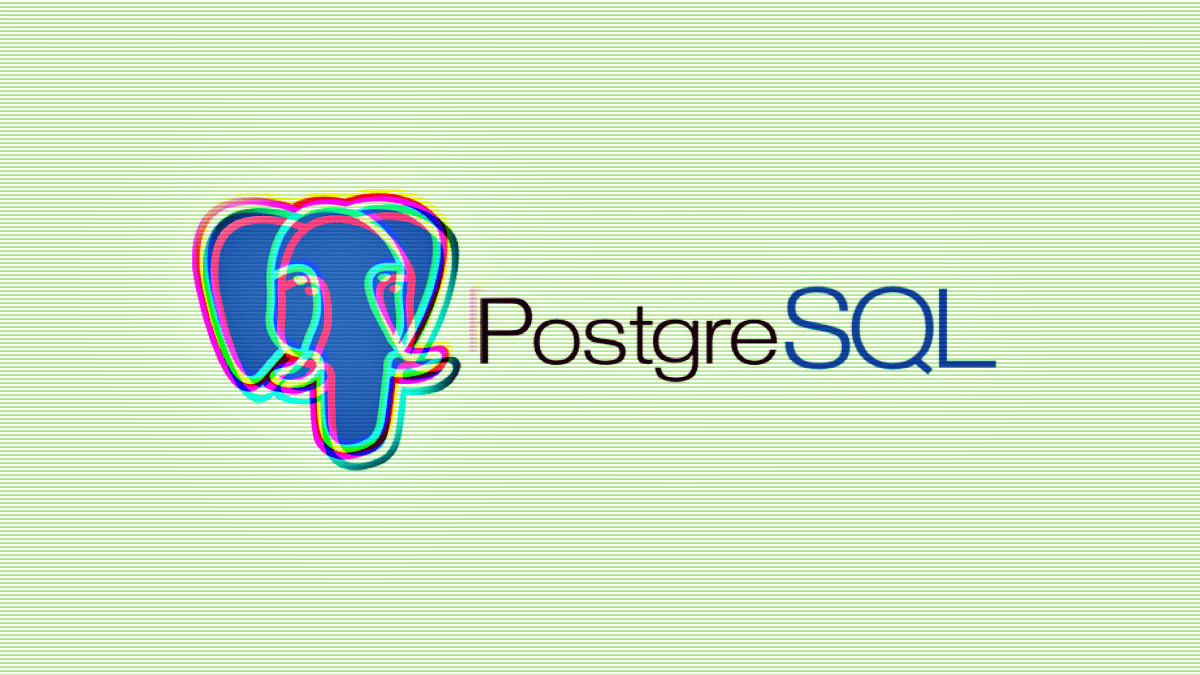
Wiz ZeroDay.Cloud Event Reveals 20-Year-Old PostgreSQL Vulnerabilities
Cybersecurity researchers at Wiz’s ZeroDay.Cloud event uncovered two critical, decade‑old vulnerabilities in PostgreSQL’s pgcrypto extension, CVE‑2026‑2005 and CVE‑2026‑2006. The flaws, dating back to 2005, enable buffer overflows and out‑of‑bounds memory writes that can lead to full database compromise. Wiz’s scans...

Palo Alto Networks Makes a $700M-Class AI Bet on Portkey Gateway
Palo Alto Networks announced its intent to acquire AI‑gateway startup Portkey, a deal valued in the $700 million range. Portkey already routes trillions of tokens each month for Fortune 500 firms and supports 3,000 LLMs, MCP servers, and agents via a single...

Silver Fox Springs Tax-Themed Attacks on Orgs in India, Russia
Silver Fox, a China‑backed threat group, launched a tax‑themed phishing campaign targeting organizations in India and, for the first time, Russia. The emails impersonated tax authorities and delivered a Rust‑based loader that installed the known ValleyRAT RAT and a previously...

Quantum eMotion Launches eShield-Q for Runtime Cryptographic Protection
Quantum eMotion Corp. unveiled eShield‑Q on May 4, 2026, a runtime cryptographic protection platform that secures encryption keys while they are in use. The solution combines quantum‑generated entropy, register‑based key storage, just‑in‑time decryption, and continuous integrity checks to guard against memory‑scraping and...
US Healthcare Marketplaces Shared Citizenship and Race Data with Ad Tech Giants
An investigation by Bloomberg found that most of the 20 state‑run health insurance exchanges in the U.S. transmitted applicants' personal data—including citizenship, race, sex, and even information about incarcerated family members—to advertising platforms such as Google, Meta, LinkedIn, Snap, and...

Kaspersky Spots Rising Scam Activity Around the 2026 World Cup
Kaspersky has detected a sharp rise in World Cup‑related scams as the 2026 tournament approaches, including fake $500,000 grant emails and counterfeit merchandise ads. The malicious messages mimic official tournament resources, aiming to steal personal data and financial assets. Kaspersky’s...

EasyDMARC and KnowBe4 Partner to Advance Proactive Email Security as Phishing Fuels More Than One-Third of Cyberattacks
EasyDMARC and KnowBe4 announced a strategic partnership that blends domain protection with digital workforce security to curb phishing, spoofing and domain‑impersonation attacks. The deal makes EasyDMARC the exclusive DMARC service provider for KnowBe4’s customer base, embedding DMARC reporting, authentication gap...
Opaque Buys Post-Quantum Cryptographic AI Tech From Abu Dhabi’s TII
Opaque Systems Inc. announced the acquisition of advanced cryptographic AI technologies from Abu Dhabi’s Technology Innovation Institute. The deal adds multiparty computation, fully homomorphic encryption, and post‑quantum cryptographic safeguards to Opaque’s confidential AI platform, covering training, fine‑tuning, inference and agent...

They Don’t Hack, They Borrow: How Fraudsters Target Credit Unions
Researchers at Flare uncovered a structured loan‑fraud playbook circulating on underground forums that targets small‑ to mid‑size credit unions. The method bypasses traditional security by using stolen personal data to pass knowledge‑based authentication and complete a full loan application, culminating...

AI Deepfakes Are Moving Into Commercial Real Estate Operations
Artificial intelligence‑generated deepfakes are amplifying business email compromise schemes, now targeting commercial real‑estate operations. The FBI attributes over $2.9 billion in losses to BEC, and AI voice cloning is making vendor invoices, escrow wires and vacancy transitions vulnerable. Fraudsters start with...

Cisco Nerds Out: May the Fourth Be with Your AI Assistant
Cisco unveiled "Galaxy Mode" for its AI Assistant, a limited‑time Star Wars‑themed interface for Meraki and Thousand Eyes customers that runs through June 4. The release introduces Deep Reasoning, an AI‑driven analysis engine that interprets network events and offers security compliance...