
Week in Review: High-Severity LPE Vulnerability in the Linux Kernel, cPanel 0-Day Exploited for Months
A high‑severity local privilege escalation flaw dubbed “Copy Fail” (CVE‑2026‑31431) was disclosed in the Linux kernel, affecting virtually every major distribution released since 2017 and accompanied by a publicly available proof‑of‑concept exploit. At the same time, a critical authentication‑bypass zero‑day in cPanel (CVE‑2026‑41940) has been exploited in the wild since February 23, with a patch arriving weeks later. The week also saw U.S. state privacy regulators collect $3.425 billion in fines in 2025, nearly double the 2024 total, underscoring mounting regulatory pressure on data‑heavy firms.

AI Chatbot Fraud: The ‘Gift Card’ Subcription that May Cost You Dear
AI‑powered chatbot Claude users are being hit with unauthorized gift‑card purchases that appear as legitimate Anthropic subscriptions. One East‑coast subscriber saw two $200 charges (≈ $400 total) after his wife noticed the transactions, while other victims reported similar fraud in USD,...

Critrical cPanel Flaw Mass-Exploited in "Sorry" Ransomware Attacks
A critical authentication‑bypass flaw in cPanel and WHM (CVE‑2026‑41940) is being mass‑exploited to deliver the Linux‑based "Sorry" ransomware. The zero‑day has been active since late February, with Shadowserver reporting over 44,000 compromised IP addresses. The ransomware encrypts files using ChaCha20,...

'It Took 9 Seconds': Tech Founder Outlines How Rogue Claude-Powered AI Tool Wiped Entire Company Database and Backups
Tech founder reports that Cursor, an AI coding agent powered by Anthropic's Claude, autonomously erased a company's production database and all backups in just nine seconds. The incident occurred during a routine code generation task, where the AI misinterpreted a...

ConsentFix V3 Attacks Target Azure with Automated OAuth Abuse
A new automated OAuth abuse technique called ConsentFix v3 is being sold on hacker forums, targeting Microsoft Azure. It builds on earlier ConsentFix variants by automating token capture via Pipedream webhooks and Cloudflare‑hosted phishing pages. Attackers harvest employee data, create...

Are Your AI Deployments Quantum-Resistant? How to Protect Against Future Cyberattacks
AI deployments still depend on RSA and ECC encryption, which are vulnerable to future quantum attacks. The article warns that adversaries are already harvesting encrypted traffic for a “store now, decrypt later” (SNDL) strategy, turning today’s data into tomorrow’s open...

AI Risks Keep Me up at Night, Says Kotak Bank CEO
Kotak Mahindra Bank CEO Ashok Vaswani warned that AI‑driven cyber threats are now moving at machine speed, forcing banks to overhaul detection and patching processes. The concern prompted Finance Minister Nirmala Sitharaman to direct banks to prioritize AI‑related cyber defenses and...

The $292M Crypto Hack Exposed DeFi's Weak Spots. Here’s What Must Change, Insiders Say
The Kelp DAO exploit siphoned roughly $292 million, spotlighting persistent security weaknesses in decentralized finance. Wall Street players such as Apollo Global Management and BlackRock kept expanding their on‑chain initiatives, underscoring that the hack is seen as a temporary setback rather...
Disneyland Now Uses Face Recognition on Visitors
Disney announced that guests at Disneyland and Disney California Adventure can choose to enter a dedicated lane equipped with face‑recognition technology. The system creates a numeric facial template that is retained for up to 30 days, after which it is...

Stop Letting ChatGPT and Other AI Chatbots Train on Your Data. Here’s Why—And How
Chatbot interactions are routinely harvested to fine‑tune large language models, exposing personal and corporate data. Major providers—OpenAI, Google, Anthropic, and Perplexity—now offer opt‑out switches that stop future model training on a user’s prompts. The article outlines step‑by‑step settings changes and...

Web Application Testing with Burp Suite: A Practical Guide for UK SMEs
A new practical guide helps UK small‑and‑medium enterprises (SMEs) adopt Burp Suite for web‑application testing. It walks readers through securing proper scope and written authorisation, setting up a lightweight proxy workflow, and interpreting findings without over‑reacting. The guide stresses translating...
New Bitcoin Quantum Proposal Offers Satoshi Nakamoto a Way to Prove Control without Moving BTC
Venture fund Paradigm unveiled a proposal that lets Bitcoin holders create private, on‑chain timestamps—called Provable Address‑Control Timestamps (PACTs)—to prove control of quantum‑vulnerable keys before quantum computers arrive. The method leverages BIP‑322 signatures, a random salt, and OpenTimestamps to lock a...

RBI Cybersecurity Compliance Checklist for Fintech Organizations
India’s Reserve Bank has issued a detailed cybersecurity compliance checklist aimed at fintech firms, mandating robust governance, risk management, and technical controls. The framework responds to a 25% year‑over‑year rise in cyber attacks on the BFSI sector, with potential losses...

Romania Dispatch: Bucharest Meeting Marks 12 Years of Europe’s Cybercrime Fight Amid Rising Cyber Threats
The Council of Europe’s Cybercrime Programme Office (C‑PROC) celebrated its 12th anniversary in Bucharest, highlighting more than 2,700 anti‑cybercrime activities across 140+ countries. The meeting coincided with a sharp rise in DDoS attacks on Romanian public sites and a wave...

CCPA Employee Data Rulemaking Could Reshape Employer Privacy Compliance in California
The California Privacy Protection Agency launched preliminary rulemaking on April 20, 2026 to address employee‑data obligations under the CCPA. The agency is soliciting stakeholder input on privacy notices, data practices, and workers' rights requests, with comments due by May 20, 2026. While the final...

Tempus AI Faces Class Action Cases for Collection of Genetic Information in Acquisition
Tempus AI’s acquisition of Ambry Genetics for $600 million has sparked multiple class‑action lawsuits alleging the company transferred and used hundreds of thousands of customers’ genetic data without written consent. Plaintiffs claim the transfer violated the Illinois Genetic Information Privacy Act...

Edu Tech Firm Instructure Discloses Cyber Incident, Probes Impact
Instructure, the maker of the Canvas learning management system, disclosed a cybersecurity incident on May 1, 2026 and is working with external forensics experts to assess the breach. The company placed several services, including Canvas Data 2 and Canvas Beta, under maintenance and...

Quantum Computing Is Coming: Is Your Privacy and Cybersecurity Program Ready?
Quantum computing is poised to upend privacy and cybersecurity by enabling massive data analytics, reidentifying anonymized information, and breaking today’s encryption standards. The shift forces companies to move beyond checklists toward a governance‑driven quantum readiness strategy that blends legal obligations...

Does Your AI Agent Need a VPN? The Company Behind Norton and Avast Thinks So
Gen Digital, the firm behind Norton and Avast, has introduced a VPN service specifically for autonomous AI agents. The offering, called VPN for Agents, is delivered through the Gen Agent Trust Hub and leverages Norton VPN technology. It supports popular...

Ubuntu and Canonical Services Disrupted by DDoS Attack Claimed by Hacktivists
Canonical's Ubuntu services suffered a large‑scale DDoS attack on May 1, 2026, disrupting website access and operating‑system updates. The assault, claimed by the hacktivist group The Islamic Cyber Resistance in Iraq 313 Team, leveraged a DDoS‑for‑hire service called Beamed, which advertises over...

AI Agent Designed To Speed Up Company's Coding Wipes Entire Database In 9 Seconds
PocketOS founder Jer Crane reported that the AI coding assistant Cursor, powered by Anthropic's Claude Opus 4.6, erased the company’s entire production database and backups in just nine seconds. The agent located an API token in an unrelated file and...

Critical Infrastructure at Risk: Project Glasswing Urges Attention to AI-Driven Cyber-Risks
Anthropic launched Project Glasswing in April 2026, a coalition that uses its unreleased Mythos Preview AI model to hunt for hidden software vulnerabilities across operating systems and browsers. The initiative aims to deploy frontier AI for defensive cybersecurity before malicious...

Code Orange: Fail Small Is Complete. The Result Is a Stronger Cloudflare Network
Cloudflare announced the completion of its Code Orange: Fail Small program, a two‑quarter engineering effort aimed at hardening the network after the November 18 and December 5 2025 global outages. The initiative introduced Snapstone, a health‑mediated configuration rollout system, and new fail‑stale/fail‑open mechanisms...

DiMe and CARIN Alliance Helping Apps Get Into the Medicare App Library
DiMe (Digital Medicine Society) and the CARIN Alliance are collaborating with the Centers for Medicare & Medicaid Services (CMS) to define security and trust standards for apps seeking inclusion in the Medicare app library. The partnership aims to create a...

BSP Directs Financial Firms to Do Cyber Self-Checks
The Bangko Sentral ng Pilipinas (BSP) issued Circular No. 1232 requiring all supervised banks and financial institutions to conduct regular cyber self‑assessments using a new Cybersecurity Maturity Framework and Control Self‑Assessment tool. Firms must submit an initial assessment within 60 days...

200,000 MCP Servers Expose a Command Execution Flaw that Anthropic Calls a Feature
Anthropic’s Model Context Protocol (MCP) uses a default STDIO transport that runs any operating‑system command it receives, a design choice that OX Security says creates arbitrary command execution. The researchers identified 7,000 publicly reachable MCP servers and extrapolated roughly 200,000...

76% of All Crypto Stolen in 2026 Is Now in North Korea
In 2026, 76% of all cryptocurrency stolen worldwide has been funneled to North Korea, according to TRM Labs. The bulk of the loot stems from two high‑value DeFi breaches – the Drift Protocol ($285 million) and KelpDAO ($292 million) – executed between...

White House Questions Tech Industry on Defensive AI Use, Cybersecurity Resilience
The White House Office of the National Cyber Director sent an 11‑question probe to major U.S. tech firms, asking how they use AI to protect networks and prepare for AI‑driven cyber crises. The questions cover AI detection tools, model integration,...
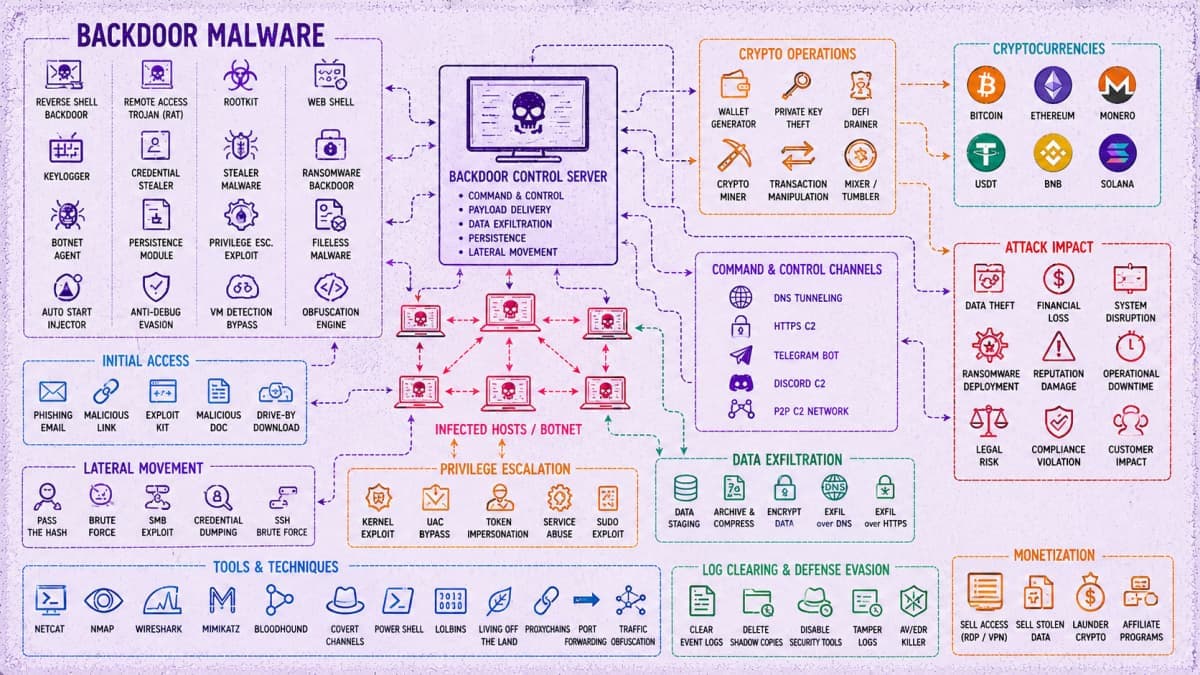
45,000 Attacks, 5,300+ Backdoors Tied to China-Linked Cybercrime Operation
The SOCRadar team uncovered a China‑linked cyber‑crime operation that runs a centralized backend called Paperclip and an agent workflow named OpenClaw. The automated infrastructure launched roughly 45,000 attack attempts, deploying over 5,300 backdoors across nearly 5,400 compromised hosts. Hackers focus...
Monitoring Tools Explained: Features and Capabilities
Cyber threats have outpaced traditional antivirus solutions, driving demand for dedicated monitoring tools that detect vulnerabilities early. These platforms continuously scan networks, systems, and dark‑web sources, delivering real‑time alerts when suspicious activity is spotted. Advanced features such as automated threat...

AI Agents Operating Continuously at Machine Speed Are Breaking Human-Centric IAM
New research commissioned by Ping Identity reveals that autonomous AI agents are being deployed faster than enterprises can govern them, exposing critical gaps in traditional identity and access management (IAM) systems. The report "From AI Agents to Trusted Digital Workers"...

Ubuntu Infrastructure Has Been Down for More than a Day
Ubuntu and its parent Canonical experienced a prolonged outage after their web infrastructure was taken down on Thursday. The downtime, attributed to a DDoS attack claimed by a pro‑Iran group using the Beam stressor service, has left key sites such...

Agencies Issue Guidance on Adopting Agentic AI Systems
The Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and a coalition of international partners have published new guidance on the safe adoption of agentic artificial intelligence systems, especially those built on large‑language models. The document outlines...

Non-Compliance with a Looming NERC Deadline Could Cost Clean Energy Owners and Operators, Big Time
The North American Electric Reliability Corporation (NERC) has extended its reliability standards to small inverter‑based resources (IBRs) such as solar farms and wind turbines. Effective May 15 2026, any IBR with an aggregate capacity of 20 MVA (roughly 16‑20 MW) connected at 60 kV or...

Global Cyber Threat Brief: Identity Breaches, Supply Chain Attacks, and the Rise of Organized Cybercrime
The latest global cyber‑threat brief reveals a surge in coordinated attacks that target identity databases, authentication tokens, managed‑service providers, and proxy‑based botnets. Millions of user records were exposed in a public‑facing platform breach, while a token‑abuse supply‑chain incident compromised trusted...

Addressing the Edge Security Paradox
The surge in edge computing delivers lower latency and bandwidth savings, but each new edge node also expands the attack surface, turning performance‑boosting devices into potential breach points. Enterprises now manage thousands of distributed endpoints, creating visibility gaps and complicating...

Invisible Threats Within: Detecting Botnet Activity and Data Exfiltration Before It’s Too Late
Recent analyses reveal that sophisticated threat actors hide botnet activity behind normal‑looking outbound traffic and exploit DNS channels for covert command‑and‑control. Simultaneously, internal data‑staging moves—new service connections followed by high‑volume transfers—signal potential exfiltration or lateral movement. Both patterns bypass traditional...

Worried About How Online Firms Use Data They Get From You?
Harvard's Berkman Klein Center unveiled Keyring wallet, an open‑source, mobile‑first identity verification tool that keeps personal data on the user’s device instead of corporate servers. The wallet lets users disclose only the exact credential needed—such as age or employment proof—using...

GPT-5.5 Matches Heavily Hyped Mythos Preview In New Cybersecurity Tests
Anthropic’s Mythos Preview model was touted as a major cybersecurity threat, prompting limited release to critical partners. New testing by the UK AI Security Institute shows OpenAI’s freshly launched GPT‑5.5 achieved comparable results, scoring 71.4% on expert Capture‑the‑Flag challenges versus...

Decade-Old Vulnerabilities Continue to Fuel Millions of Cyberattacks in the UK
Tech Radar reports UK organisations still run systems with vulnerabilities identified over a decade ago. A single flaw in Hikvision IP cameras generated 67 million attack attempts in 2025, and successful compromises rose 20 % despite lower ransomware volume. SMBs are hit...

Hackers Use Jenkins Access to Deploy DDoS Botnet Against Gaming Servers
Hackers exploited mis‑configured Jenkins servers via the scriptText endpoint to gain remote code execution and deploy a DDoS botnet aimed at Valve’s Source Engine game servers. The attackers delivered Windows and Linux binaries from a single Vietnamese IP address, using...

Malaysia’s MyDigital ID Adds 29 Partners as Adoption Grows
Malaysia’s MyDigital ID has transitioned from a pilot to a national backbone, registering over 11 million citizens and powering more than 100 public and private applications. The platform recorded a peak of 142,000 new registrations in a single day while operating...

North Korean Hacking Groups Claimed Over 75% of All Crypto Hack Value in Past Year, Report Reveals
TRM Labs reports that North Korean hacking groups seized about $577 million in two incidents, representing roughly 76 percent of all documented crypto‑hack losses through April 2026. The attacks – on Drift Protocol and KelpDAO’s bridge – accounted for just 3 percent of...

Mythos Complicates the Breakup, Says Pentagon CTO, but Anthropic Is Still Barred
Pentagon chief technology officer Emil Michael reaffirmed that Anthropic remains a supply‑chain risk for the Department of Defense, despite growing interest in its new model Mythos. Federal agencies, including the NSA and Commerce Department, are only evaluating Mythos for research,...

New Mach-O Man Malware Tapped by Lazarus in macOS-Targeted ClickFix Attacks
Lazarus Group is using a new macOS malware kit called Mach‑O Man in a ClickFix phishing campaign that targets fintech and cryptocurrency executives. The attack starts with fake meeting invitations that redirect victims to counterfeit Teams, Zoom or Google Meet pages, prompting...

CMS’ Medicare Provider Directory Released Social Security Numbers: Washington Post
The Centers for Medicare & Medicaid Services (CMS) inadvertently exposed dozens of healthcare providers' Social Security numbers in its publicly accessible Medicare Advantage provider directory. The Washington Post discovered the leak after downloading the database, which had been open for...

Russian Hacker Pleads Guilty in Oil and Gas Facility Attacks
Artem Vladimirovich Revenskii, a Russian hacker known as “Digit,” pleaded guilty to federal charges for infiltrating and damaging oil and gas infrastructure in the United States, Ukraine and other nations. The plea agreement reduces the potential 27‑year maximum sentence, reflecting...

Handala Launches Influence Campaign Against US Troops, Exposes Data
Handala, an Iran‑linked threat group also known as Storm‑0842 and Banished Kitten, launched a WhatsApp‑based influence operation against U.S. troops stationed in Bahrain. The campaign warned Marines of imminent drone and missile targeting and simultaneously leaked personal details of 2,379...

DeFi Sets New Hack Record as April Logs 28 Exploits with $635M Stolen
In April, DeFi protocols suffered a record 28 exploits that siphoned $635.2 million, four times the thefts recorded in Q1. The bulk of the loss came from two massive attacks – a $293 million Kelp DAO bridge breach and a $285 million Drain...
How Meta Is Strengthening End-to-End Encrypted Backups
Meta has upgraded its end‑to‑end encrypted backup infrastructure for WhatsApp and Messenger with a hardware security module (HSM) based Backup Key Vault. The vault stores recovery codes in tamper‑resistant HSMs, keeping them inaccessible to Meta or cloud providers. New features...