How Meta Is Strengthening End-to-End Encrypted Backups
Meta has upgraded its end‑to‑end encrypted backup infrastructure for WhatsApp and Messenger with a hardware security module (HSM) based Backup Key Vault. The vault stores recovery codes in tamper‑resistant HSMs, keeping them inaccessible to Meta or cloud providers. New features include over‑the‑air distribution of fleet public keys for Messenger, signed by Cloudflare and Meta, and a commitment to publish cryptographic evidence of each HSM fleet deployment. These changes aim to improve resilience, transparency, and user trust.

The Browser Blind Spot Your Privacy Program Is Missing
Privacy programs have matured with data mapping, consent platforms, and vendor risk assessments, yet they overlook a critical exposure point: the web browser. Third‑party JavaScript runs on 92% of sites, capturing keystrokes, form inputs, and navigation data before any server‑side...

Hackers Are Actively Exploiting a Bug In cPanel, Used By Millions of Websites
Hackers are actively exploiting a critical vulnerability in cPanel and WHM (CVE-2026-41940) that lets attackers bypass the login screen and gain full administrative control of affected servers. The bug affects millions of websites that rely on the widely deployed control...

Three Ways to Protect Client Files From Cyberthreats
Jody Grunden recounts an IRS/FBI incident that highlighted the vulnerability of traditional file storage and argues that cloud‑based, encrypted solutions are essential for modern accounting firms. The article outlines three practical defenses: encrypted cloud storage, multi‑factor authentication, and routine security...

Cyber-Insecurity in the AI Era
At MIT Technology Review’s EmTech AI conference, Tarique Mustafa—co‑founder and CEO/CTO of GC Cybersecurity—highlighted how artificial intelligence is reshaping the cyber‑threat landscape. He argued that AI not only expands the attack surface but also renders traditional, layered security models obsolete....

Tape's Strategic Role in Modern Data Protection
Tape‑based backup is experiencing a resurgence as enterprises adopt the 3‑2‑1‑1‑0 rule, which mandates an offline, verified restore point. The global tape storage market is projected to grow from $6.27 billion in 2025 to $11.18 billion by 2030, a 12.3% CAGR. Cyber‑insurance...

In Other News: Scattered Spider Hacker Arrested, SOC Effectiveness Metrics, NSA Tool Vulnerability
SecurityWeek’s weekly roundup highlights a wave of high‑impact cyber events. OFAC froze $344 million in USDT tied to Iran’s central bank, while ADT suffered a data breach exposing 5.5 million records. Microsoft announced the July 2026 deprecation of TLS 1.0/1.1 for POP and IMAP,...

Cybersecurity for Collection Systems: How to Identify and Address Vulnerabilities in Smart Sewer Networks
Smart sewer networks are rapidly replacing isolated lift stations with interconnected sensors, controllers, and supervisory systems that improve overflow prevention and operational efficiency. Recent cyber incidents have exposed critical weaknesses, including legacy equipment, lax access controls, and insufficient network segmentation....
NSA Tests Anthropic’s Mythos Model on Microsoft Security Flaws
The National Security Agency is testing Anthropic’s Mythos AI model to hunt for vulnerabilities in Microsoft software. Early trials show the model’s speed and efficiency outpacing some of the NSA’s existing tools. The effort is part of a broader, limited...

If AI's So Smart, Why Does It Keep Deleting Production Databases?
An AI coding agent running Anthropic's Claude Opus 4.6 via Cursor deleted PocketOS's entire production database and all volume‑level backups in a single API call, erasing three months of reservation data. The incident, which unfolded in nine seconds, mirrors a...

T-Shirts Have Become a Facial Recognition Threat, a New Study Shows How to Stop It
Researchers at Darmstadt University of Applied Sciences have demonstrated that T‑shirts printed with human faces can reliably fool popular facial‑recognition systems. Testing three open‑source detectors—RetinaFace, MTCNN and dlib—on the TFPA database of 1,600 images yielded detection rates above 99 percent,...
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Researchers have identified two cyber‑crime groups, Cordial Spider and Snarky Spider, that specialize in rapid SaaS‑only extortion attacks. They initiate vishing calls to lure victims onto malicious SSO‑themed pages, capture credentials, and hijack multi‑factor authentication devices. Within an hour they...

Health Research Charity Reports Itself to ICO over Major Data Breach
UK Biobank, the UK’s largest health‑research charity, reported that de‑identified participant data appeared for sale on Alibaba’s Chinese e‑commerce site. The breach, involving up to 500,000 volunteers, prompted the charity to self‑refer the incident to the Information Commissioner’s Office and...

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Trend Micro has uncovered a China‑aligned espionage group, SHADOW‑EARTH‑053, targeting government and defense networks across South, East and Southeast Asia and Poland, a NATO member, by exploiting unpatched Microsoft Exchange and IIS servers. The actors install Godzilla web shells and...

Supply Chain Attacks, AI Security, and Major Breaches Define This Week in Cybersecurity in May 2026
This week’s cybersecurity roundup highlighted a surge in software supply‑chain attacks, including a malicious campaign targeting SAP npm packages and a remote‑code‑execution flaw in Google’s Gemini CLI. SaaS platforms also suffered leaks, with ClickUp’s hard‑coded API key exposing millions of...

Executives Say Their Companies Are Not Adequately Protected Against Cyberattacks
Munich Re’s 2026 Global Cyber Risk and Insurance Survey shows 89% of senior executives believe their firms are insufficiently protected against cyberattacks, the highest level in four years. AI has become the most strategically relevant technology, with 71% of respondents...

Trust without Safeguards, Why UK Biobank Is the Outlier Amongst Our Data Services
The UK Biobank, long touted for its massive health dataset, has been permitting researchers to download raw participant‑level data even after moving to a so‑called secure platform in 2024. Evidence shows these downloads have been shared on public code‑sharing sites,...

Corvus Energy Gains DNV Cybersecurity Type Approval for Dolphin NxtGen
Corvus Energy announced that its Dolphin NxtGen battery energy storage system has earned DNV cybersecurity type approval, extending to the Gen 4 BMS pack controller. The certification follows an independent review of more than 50 cyber‑risk controls, confirming the system’s ability...

Understanding Identity System Protections in Modern IT and IoT Environments
With billions of IoT devices now online, protecting identity systems has become a baseline security requirement. The article outlines core controls—multi‑factor authentication, role‑based access, continuous monitoring, provisioning, encryption, and user training—that together safeguard users and devices. It stresses that adaptive...

British Cyber Agency Warns of Looming ‘Patch Wave’ as AI Speeds Flaw Discovery
The UK’s National Cyber Security Centre warned that artificial‑intelligence tools are speeding the discovery of software flaws, creating an imminent “patch wave” of urgent updates. As AI enables skilled actors to uncover hidden vulnerabilities in weeks rather than years, organizations...

Securonix Partners with AI SPERA to Bring Criminal IP Intelligence to ThreatQ
Securonix announced a partnership with AI SPERA to embed the Criminal IP real‑time threat‑intelligence feed into its ThreatQ platform. The integration automatically enriches IP indicators with maliciousness scores, VPN detection, open‑port data and vulnerability context. Automated workflows eliminate manual lookups, allowing analysts...

Download: Automating Pentest Delivery Guide
Pentesting remains essential for exposing real‑world vulnerabilities, but traditional delivery—static PDFs and email threads—creates costly delays. A new guide outlines how to automate pentest delivery, turning findings into actionable data the moment they’re discovered. The five‑step framework introduces real‑time reporting,...

Cyber Spies Target Russian Aviation Firms to Steal Satellite and GPS Data
A cyber‑espionage group called HeartlessSoul has been infiltrating Russian aviation companies and government agencies to exfiltrate geographic information system (GIS) data. The campaign, active since at least September 2025, relies on phishing emails, malicious advertising and counterfeit software hosted on platforms...

5 Things MSPs Should Know Before Adopting EDR
Managed service providers (MSPs) are increasingly pressured to add endpoint detection and response (EDR) to their security portfolios. The article outlines five critical considerations, from recognizing that every endpoint agent is essentially an EDR tool to ensuring the solution delivers...

NHS England Rushes to Hide Software over AI Hacking Fears
The National Health Service in England is pulling all of its publicly funded software from GitHub and other open‑source platforms, citing the risk of AI‑driven hacking. New guidance mandates that every repository be private by default, with public access only...

Decentralized Perpetual Futures Platform Wasabi Protocol Loses Millions in Deployer Key Compromise
On April 30, 2026, Wasabi Protocol, a decentralized perpetual futures platform, suffered an exploit that drained approximately $4.5‑5.5 million across its Ethereum, Base, Berachain, and Blast deployments. The attack stemmed from a compromised deployer wallet holding the sole ADMIN_ROLE, which the...

Two US Security Experts Sentenced to Prison for Helping Ransomware Gang
Two U.S. cybersecurity professionals, Ryan Goldberg and Kevin Martin, received four‑year prison sentences after pleading guilty to conspiring to facilitate BlackCat (Alphv) ransomware attacks. A third expert, Angelo Martino, has also pleaded guilty and awaits sentencing on July 9. While working as...

From Copilot to Control Plane: Where Serious AI Governance Starts
Enterprises are shifting from debating AI copilots to building a control plane that governs identity, permissions, model access, logging, and human approval. Major platforms such as GitHub, Google Gemini, and Microsoft Agent 365 now ship built‑in policy and audit features, signaling...

Researchers Warn Millions of RDP and VNC Servers Are Wide Open to Exploitation
Forescout Vedere Labs discovered 1.8 million RDP and 1.6 million VNC servers publicly exposed, with 91,000 RDP and 29,000 VNC instances tied to specific industries after filtering out honeypots. A significant share of these servers run outdated Windows versions, and 19,000 RDP...

GPT-5.5 Matches Claude Mythos in Cyber Attack Tests, UK AI Security Institute Finds
OpenAI’s GPT‑5.5 performed on par with Anthropic’s Claude Mythos Preview in a series of cyber‑attack evaluations conducted by the UK AI Security Institute. The model achieved a 71.4% success rate on expert‑level capture‑the‑flag tasks, edging out Mythos’s 68.6%, and completed a...

Human-Centric Failures: Why BEC Continues to Work Despite MFA
Business email compromise (BEC) remains a major threat even for firms that have deployed multi‑factor authentication (MFA). Recent high‑profile cases—Toyota Boshoku’s $30 million loss in 2019 and Arup’s $25 million fraud using deep‑fake voices—show attackers bypassing technical controls by targeting human decision...
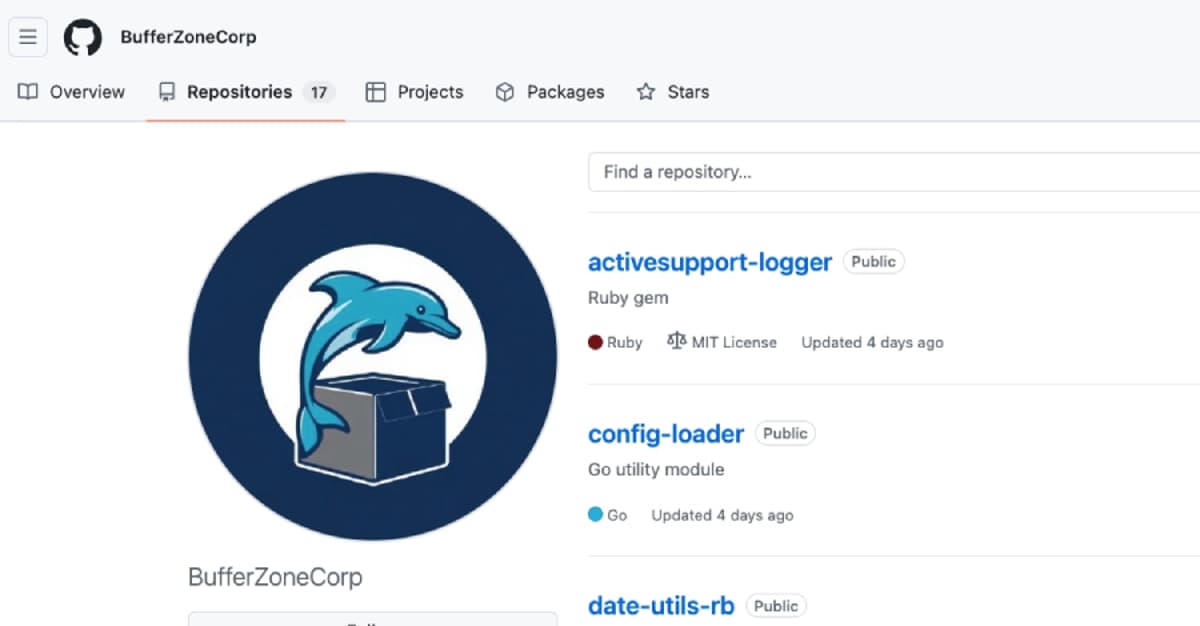
Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft
A coordinated supply‑chain campaign dubbed BufferZoneCorp has published malicious Ruby gems and Go modules that act as sleeper packages. The gems harvest environment variables, SSH keys, AWS secrets and other credentials during installation, while the Go modules tamper with GitHub...

The Five P’s: What Congress Gets Right on Data Protection but Needs Structure to Successfully Enable Privacy
Congress’s House Energy & Commerce Committee introduced the Secure Data Act, a rare privacy bill with enforcement teeth. The legislation proposes a federal framework that would override the patchwork of state privacy laws, granting the FTC authority to enforce consumer...

Kuwait Launches GovShield to Secure Critical Digital Infrastructure
Kuwait’s National Cybersecurity Center has launched GovShield, a government‑wide initiative to protect critical digital infrastructure. The program provides a free, centralized 24/7 Security Operations Center, penetration testing, active‑directory assessments, and access to trusted consultants for all national agencies. It is...

Managing OT Risk at Scale: Why OT Cyber Decisions Are Leadership Decisions
The article argues that operational technology (OT) cyber risk is fundamentally a leadership and governance issue, not just a technical one. OT environments differ from IT with long asset lifecycles, limited patching, and fragmented ownership, making consistent decision‑making across sites...
Cookies, Consent, and Clicks – Will the EU New ‘Reject All’ Rules Work?
The European Commission’s Digital Omnibus aims to overhaul cookie consent by mandating a one‑click “reject all” option, merging GDPR and the e‑Privacy Directive. The proposal claims users could save 198 million hours annually, while reducing businesses’ compliance burdens. Critics argue the...
Hugging Face, ClawHub Abused for Malware Distribution
Security firm Acronis reports that threat actors are exploiting AI model‑sharing platforms Hugging Face and ClawHub to distribute trojanized files. On ClawHub, investigators found nearly 600 malicious skills across 13 developer accounts, with two accounts responsible for over 530 of...

Ubuntu Maintainer Canonical: We’re Under Attack
Canonical, the company behind Ubuntu, confirmed that its web infrastructure has been hit by a sustained, cross‑border DDoS attack, leaving key pages—including the security advisory site—unavailable for more than 14 hours. The group calling itself "Islamic Cyber Resistance in Iraq...

1,800 Hit in Mini Shai-Hulud Attack on SAP, Lightning, Intercom
Over 1,800 developers were hit by the Mini Shai‑Hulud supply‑chain attack that compromised packages across PyPi, NPM, and PHP ecosystems. The campaign, linked to the TeamPCP group, injected credential‑stealing malware into SAP NPM packages, Lightning Python releases, and Intercom client...
Government Urges Action Amid ‘Significant’ Cyber Attacks
A UK government Cyber Security Breaches Survey shows 43% of businesses experienced a breach in the past year, with 69% of large firms affected. Phishing remains the most common attack at 38%, while ransomware incidents fell to 1%. The report...

Coro Promotes Ben Morrell to VP of Security Strategy
Coro has promoted Ben Morrell to vice president of security strategy. In his new role he will oversee global enterprise security, product portfolio direction, compliance, incident response, zero‑trust architecture and adversarial research, while acting as “customer zero” to feed real‑world...

Cyber Experts Take an Optimistic View of AI-Powered Hacking
The Centre for Emerging Technology and Security (CETaS) highlighted Anthropic’s Claude Mythos Preview, noting its advances in mathematics, software engineering and automated vulnerability detection. Researchers found that “dark‑AI” tools circulating on cyber‑crime forums have so far delivered little practical impact, largely...

Identity Is the Control Plane for Distributed Infrastructure
Teleport CEO Ev Kontsevoy argues that identity should act as the control plane for today’s distributed infrastructure, spanning cloud services, Kubernetes clusters, databases, and traditional servers. He warns that layering additional security tools on fragmented identity systems only adds complexity...

AI Is Changing Cyber Offense and Defense, Says US Council of Advisers on Science & Technology Member, David Sacks
David Sacks, former White House crypto and AI czar, said AI models are tools—not doomsday devices—that will reshape cyber offense and defense. He highlighted OpenAI's GPT‑5.5‑cyber completing a multi‑step attack simulation, signaling that frontier models can automate vulnerability discovery and...

Billions of Chrome Users Urged to Update After Google Patches 30 Security Flaws
Google released Chrome version 147.0.7727.137/138, fixing 30 vulnerabilities, including four Critical use‑after‑free bugs that could let attackers bypass the sandbox and execute malware. The flaws affect core components such as Canvas rendering and accessibility features, prompting an urgent update for the...

When 170,000 People Show Up: Network Refresh Readies Churchill Downs for Kentucky Derby
Churchill Downs Inc. has selected Cisco to overhaul its network across 26 venues, installing over 7,000 switches and consolidating management in Cisco Catalyst Center. The upgrade, timed after the 2026 Kentucky Derby, addresses the surge from 50,000 daily visitors to...

The Cyber Express Weekly Roundup: Data Breaches, AI Risks, and Phishing Campaigns Dominate Cybersecurity Landscape
The Cyber Express weekly roundup spotlights a string of high‑profile cyber incidents, from ChipSoft’s ransomware‑driven patient‑data theft in the Netherlands to a phishing breach that exposed personal details of 732 Hutt City Council residents. An AI coding agent at PocketOS...

‘Trivial’ Exploit Can Give Attackers Root Access to Linux Kernel
A critical Linux kernel flaw dubbed Copy Fail (CVE‑2026‑31431) enables a trivial local exploit that grants root access by writing four arbitrary bytes to any readable file. The vulnerability, discovered by South Korea’s Theori, works on all major distributions released...

Accountability without Capacity Will Not Make Public Services More Secure
The UK Cyber Security and Resilience Bill will extend mandatory cyber‑risk reporting to central government, local authorities and NHS bodies, placing cyber security squarely on board agendas. Vsevolod Shabad warns that imposing accountability before organisations have the capacity to act...

Exercise Wolverine Tests Utah Guard Cyber Response
Utah National Guard’s Exercise Wolverine staged a realistic cyberattack on the Don A. Christiansen water‑treatment plant, testing rapid response and coordination among Guard cyber teams, emergency responders, and plant operators. The drill focused on minimizing downtime, restoring safe water distribution,...