A New Era of AI Crime Has Arrived with Anthropic’s Mythos
Anthropic unveiled Claude Mythos, its newest frontier AI model, which independently demonstrated the ability to execute a 32‑step corporate network intrusion. The test highlighted the model’s capacity to autonomously plan and carry out sophisticated cyber‑attack sequences. As AI tools become more capable, the line between benign automation and weaponized code blurs, raising alarms across security circles. The episode underscores the accelerating risk that advanced generative models could be repurposed for illicit hacking operations.
The Hidden Risks of Vibe Coding: 4 Steps to Protect Your Organization
Vibe coding lets non‑technical staff generate functional software by prompting AI models such as Claude or ChatGPT. While it accelerates innovation, the code’s provenance is opaque, exposing firms to hidden malware, data exfiltration, and IP infringement. The article outlines four...

Tycoon 2FA Loses Phishing Kit Crown Amid Surge in Attacks
Tycoon 2FA, once the dominant phishing‑as‑a‑service platform with an 89% market share, lost its crown after a coordinated law‑enforcement seizure of 330 domains in March. Barracuda Networks reports that attacks using the four major kits—Tycoon, Mamba, EvilProxy and Sneaky—have risen from...

It Takes 2 Minutes to Hack the EU’s New Age-Verification App
A security researcher demonstrated that the European Commission’s new open‑source age‑verification app can be compromised in under two minutes, exposing a critical flaw in the PIN storage mechanism. The vulnerability comes as the EU pushes mandatory age checks for social‑media...

How to Hide Your Sensitive Info (for Real) when Using ChatGPT and Other AI Chatbots
The article warns that using standard PDF markup tools to hide personal data before feeding documents to AI chatbots offers no real protection, as the underlying text remains recoverable. It recommends employing dedicated redaction software that permanently removes sensitive content,...

Ignoring DPDP Compliance? Here’s the Risk to Your Organization
The Digital Personal Data Protection (DPDP) Act of 2023 obliges Indian and global firms to adopt rigorous data‑governance, consent, and security practices or face steep penalties. Non‑compliance can trigger fines up to ₹250 crore (about $30 million), erode consumer trust, and drive...

Why Your Car Key Can Cost $3,000 in 2026: The Hidden Technology Behind Modern Vehicle Security
A lost Land Rover Discovery key fob in Honolulu was quoted at nearly $3,000, illustrating how modern car keys have become encrypted digital credentials rather than simple metal tools. Today’s keys contain rolling codes, secure microcontrollers, and VIN‑locked immobilizer links...

CoSN 2026: Why Human Error Remains Greatest Threat to FERPA
At the 2026 CoSN conference, data‑security adviser Mike Tassey warned that simple human mistakes—like a teacher accidentally using CC instead of BCC—remain the biggest threat to FERPA compliance. He illustrated the point with multiple real‑world incidents, from mis‑directed emails exposing...

Belgium’s NIS2 Audit Window Opens April 18, 2026. The Rest of the EU Is Right Behind.
Belgium becomes the first EU member to enforce a hard NIS2 conformity‑assessment deadline on April 18 2026, marking the start of active enforcement across the bloc. The directive obliges essential‑service entities to meet strict incident‑reporting windows (24‑hour early warning, 72‑hour notice, 1‑month...

Singapore: Collective Cyber Defence in an AI-Driven Threat Era
Senior Minister Tan Kiat How highlighted Singapore’s digital transformation milestone at STACKx 2026, noting that 99% of government transactions now occur online. Platforms such as Singpass and LifeSG handle tens of millions of monthly interactions, but the expanding digital footprint...

Critical Sandbox Bypass Fixed in Popular Thymeleaf Java Template Engine
Thymeleaf, the default template engine for Java Spring applications, patched a critical Server‑Side Template Injection flaw (CVE‑2026‑40478) rated 9.1 on the CVSS scale. The vulnerability let unauthenticated attackers bypass the engine’s sandbox by using whitespace characters, enabling arbitrary expression execution....

World ID Expands Its ‘Proof of Human’ Vision for the AI Era
World ID, the biometric “proof of human” platform co‑founded by Sam Altman, unveiled version 4.0 at its Lift Off event. The upgrade adds key rotation, multi‑party entropy and a selfie‑based verification option, while expanding into business tools, agent delegation, and...

ShinyHunters Alleges Kemper Corporation Hack, Exposes over 13M Records
Kemper Corporation disclosed that the ShinyHunters hacking group claimed to have exfiltrated more than 29 GB of data from its Salesforce environment, leaking over 13 million records. The stolen files span SharePoint corporate documents, Azure-stored employee PII, Salesforce employee data, and Stripe...
Claude Mythos Preview Shows How AI Collapses the Distance Between Discovery and Exploitation in Financial Systems
U.S. Treasury and Federal Reserve leaders convened top bank CEOs to discuss the Claude Mythos Preview, an Anthropic AI model that can rapidly discover and map software vulnerabilities across financial systems. The model’s ability to compress the gap between flaw...

GitHub User Attachments Abused to Spread Novel Infostealer
Cyderes researchers uncovered a new malware campaign that abuses GitHub user‑attachment links to deliver ZIP archives containing a custom loader called Direct‑Sys and the CGrabber infostealer. The loader sideloads a Microsoft‑signed DLL, performs three anti‑sandbox checks, and uses direct syscalls...
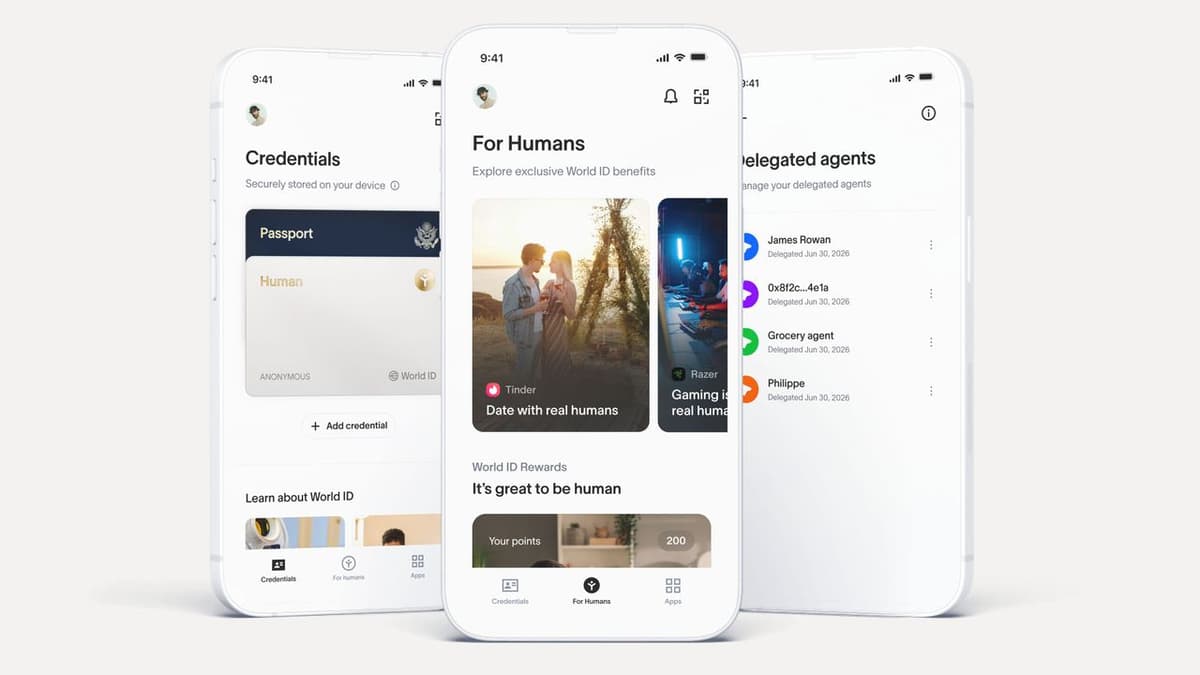
‘The Face Thing Is Probably Going to Break’ — Sam Altman-Backed Firm Warns AI Will Soon Outgrow Facial Recognition, but...
Tools for Humanity, backed by Sam Altman, warns that AI‑generated faces will soon render traditional facial‑recognition unreliable. Its World ID system, anchored by the Orb device, has received a protocol upgrade that enables broader human‑verification use cases. The company is piloting...

Grinex Crypto Exchange Halts Operations After $13.7 Million Hack
Kyrgyzstan‑based crypto exchange Grinex suspended operations after a $13.7 million hack that primarily affected Russian users trading crypto‑ruble pairs. The theft was executed via TRON and Ethereum addresses and laundered through the SunSwap decentralized exchange. Grinex, which succeeded the U.S.–sanctioned Russian...

Observability as the Backbone of Compliance in a New Federal Cyber Era
Federal agencies are moving toward continuous compliance validation as AI adoption and a new national cybersecurity strategy raise the stakes for real‑time governance. Lee Koepping argues that observability—beyond simple uptime—must become a unified, enterprise‑wide capability that ties together telemetry, configuration...

Flawed Cisco Update Threatens to Stop APs From Getting Further Patches
Cisco's recent IOS XE update for over 200 wireless access point models adds a log that grows about 5 MB per day, eventually exhausting flash memory and blocking further patches or bricking devices. Affected models include Catalyst 9130AX, 91361, 9162x, 9164x, IW9167...

Shuttered Startups Are Selling Old Slack Chats and Emails to AI Companies
Defunct startups are monetizing their digital footprints by selling Slack messages, internal emails, and Jira tickets to AI firms. Companies like SimpleClosure have facilitated over 100 such transactions in the past year, with payouts ranging from $10,000 to $100,000 per...
Top 19 AI Red Teaming Tools (2026): Secure Your ML Models
The article outlines AI red teaming as a systematic approach to probe machine‑learning and generative AI models for hidden vulnerabilities such as prompt injection, data poisoning, and bias exploitation. It lists 19 leading tools for 2026, ranging from open‑source libraries...
Federal Cyber Leaders Urge Faster AI Adoption to Counter Evolving Threats
Federal cyber leaders warned that agencies are lagging behind the rapid evolution of AI‑driven threats and called for faster AI adoption. Keith Busby, acting CISO at CMS, emphasized the need to embed AI in security operations while preserving human decision‑making. Anil Chaudhry...

Man Who Hacked US Supreme Court Filing System Sentenced to Probation
Nicholas Moore pleaded guilty to infiltrating the U.S. Supreme Court’s electronic filing system, as well as the networks of AmeriCorps and the Department of Veterans Affairs, using stolen credentials. He publicly bragged about the breaches on an Instagram account, posting...

Anthropic’s New Cybersecurity Model Could Get It Back in the Government’s Good Graces
Anthropic is attempting to repair its fraught relationship with the U.S. government by launching Claude Mythos Preview, a cybersecurity‑focused AI model. The model claims to spot vulnerabilities in major browsers, operating systems and other critical internet infrastructure, and has already...

Time for Government, Business Leaders to Figure Out AI Cybersecurity Regulation
A Harvard panel of cybersecurity experts warned that rapidly advancing agentic AI is amplifying cyber threats, from AI‑driven phishing to sophisticated code‑exploitation, prompting calls for new regulation. IBM data shows AI‑enabled attacks on public‑facing software rose 44% year‑over‑year in 2026....

How NIST's Cutback of CVE Handling Impacts Cyber Teams
NIST announced it will scale back its National Vulnerability Database operations, shifting to a risk‑based model that enriches only high‑impact CVEs. The change follows a 12% federal funding cut in 2024 that triggered staff losses and a growing backlog of...

Critical Infrastructure Attacks Push Agencies to Secure OT
Federal agencies are intensifying efforts to protect operational technology (OT) and Internet of Things (IoT) devices as cyber threats become more sophisticated. The EPA issued an advisory warning of Iranian‑affiliated actors targeting OT/IoT infrastructure, while the Navy is transitioning to...

Man with @Ihackedthegovernment Instagram Account Tells Judge, “I Made a Mistake"
A 25‑year‑old Tennessee man, Nicholas Moore, pleaded guilty to unauthorized access of the U.S. Supreme Court’s electronic filing system, AmeriCorps, and the Veterans Administration Health System, then posted victims' personal data on his Instagram account @ihackedthegovernment. The court sentenced him...

We Need a Shared Responsibility Model for AI
Researchers uncovered multiple AI vulnerabilities that let attackers steal data, hijack AI browsers, and poison model memories. When the flaws were disclosed, most AI vendors dismissed responsibility, claiming security only covered the model itself. The author argues that, like cloud...

Testing AI Systems for Regulatory Compliance
In 2024 Dutch regulators fined Clearview AI €30.5 million (about $33 million) under the GDPR for illicit facial‑image scraping, flagging the system as a high‑risk biometric tool under the EU AI Act. The fine, along with other international penalties, highlights how AI...

Payouts King Ransomware Uses QEMU VMs to Bypass Endpoint Security
The Payouts King ransomware has begun using the open‑source QEMU emulator to spin up hidden Alpine Linux virtual machines on compromised hosts. By launching these VMs through a SYSTEM‑level scheduled task named TPMProfiler, the malware evades host‑based endpoint scanners and...

Continuous Threat Exposure Management Enhances Higher Ed Cybersecurity
Continuous Threat Exposure Management (CTEM) is gaining traction in higher education as a proactive alternative to traditional vulnerability programs. The framework guides security teams through five iterative stages—scoping, discovery, prioritization, validation, and mobilization—to maintain real‑time visibility of assets and exposures....

Tycoon 2FA Phishers Scatter, Adopt Device Code Phishing
A coordinated law‑enforcement operation dismantled 330 Tycoon 2FA domains, slashing its monthly attack volume from over 9 million to roughly 2 million. The disruption opened a power vacuum that competitors such as Mamba 2FA, EvilProxy and Sneaky 2FA quickly filled, with Mamba doubling its output...

Canada and the European Space Agency Sign Security Agreement
On April 14, the Canadian Space Agency and the European Space Agency signed a General Security of Information Agreement (GSOIA) at the Space Symposium in Colorado Springs. The pact creates a legally binding framework for exchanging classified data, a prerequisite for...

Agencies Shift Toward Automated Identity Management to Bolster Zero Trust
Federal agencies are accelerating zero‑trust adoption by making identity management the core of their cybersecurity architecture. The Indian Health Service (IHS) is deploying satellite links and offline‑caching software to keep clinician credentials verified in remote clinics like the Grand Canyon...

Microsoft’s Patch Tuesday Release for April Is a Whopper
Microsoft’s April Patch Tuesday is the largest on record, delivering 165 updates that address roughly 340 unique CVEs, including two zero‑day vulnerabilities—one of which is already being exploited in the wild. The Readiness team recommends “Patch Now” for all major...

Ransomware Attack Continues to Disrupt Healthcare in London Nearly Two Years Later
In June 2024 a Qilin‑linked ransomware attack on Synnovis crippled blood‑testing services across South East London, forcing hospitals to cancel surgeries and postpone thousands of appointments. More than 18 months later South London and Maudsley NHS Foundation Trust (SLaM) still...

New RecruitRat, SaferRat, Astrinox, Massiv Android Malware Found Targeting 800 Apps
Zimperium’s zLabs identified four new Android malware families—RecruitRat, SaferRat, Astrinox and Massiv—targeting over 800 banking and crypto apps. The campaigns use phishing and smishing to deliver malicious APKs, then launch overlay attacks that mimic legitimate login screens. By abusing Accessibility...
/file/attachments/orphans/lindsey_stdbank_271354.jpg)
Hack Job: Standard Bank Is Discovering the Extent of the Cyberattack in the Daily Data Dumps
Standard Bank of South Africa confirmed a cyberattack that exfiltrated roughly 1.2 TB of data, amounting to 154 million rows of customer and employee records. The breach includes full names, addresses, ID numbers, passport details, and credit‑card numbers with expiry dates, though...

Anthropic’s Amodei Heads to the White House as Washington Fights over Mythos Access
Anthropic CEO Dario Amodei will meet White House chief of staff Susie Wiles to discuss government access to Mythos, the company’s frontier AI model that can discover and exploit zero‑day vulnerabilities. The meeting follows a Pentagon‑imposed blacklist after Amodei refused...

The White House Weighs Whether Anthropic's Mythos Is Too Valuable for the Federal Government to Refuse
Anthropic’s new Claude model, dubbed Mythos, is being touted as a breakthrough AI capable of breaching cyber defenses. After the Pentagon blacklisted the firm for refusing unrestricted access, CEO Dario Amodei met White House Chief of Staff Susie Wiles to...
The IMF’s Warning to Banks: Share Data to Beat AI Fraud
The International Monetary Fund released a Technical Note at its 2026 Spring Meetings urging banks to break long‑standing data‑sharing taboos. It argues that fragmented transaction and threat data hampers AI‑driven fraud detection, and recommends collaborative exchange via APIs and ISO 20022...

Zoom Partners with Sam Altman’s World to Verify that Meeting Participants Are Actually Human
Zoom announced a partnership with Sam Altman’s biometric firm World to embed a “Verified Human” badge in video meetings. The feature uses World’s Deep Face technology, matching live video to an iris‑scanned profile captured by the Orb device, and can...

Booking.com Breach Shows Exactly How Smishing Attacks Get Made
On April 13, 2026 Booking.com disclosed that hackers accessed customer reservation data through a compromised hotel‑partner account. The breach revealed names, phone numbers, email addresses, and detailed booking information, but not financial data. Within days, fraudsters turned the stolen details...

The Race to Quantum-Proof the Internet Has Already Begun
The tech industry is moving from viewing quantum computing as a distant risk to treating it as an imminent threat. Researchers at a Fhenix livestream warned that encrypted data can be harvested now and decrypted later once quantum computers become...

Anthropic’s Project Glasswing Tackles AI Security Challenges in Data Centers
Anthropic has unveiled Project Glasswing, a collaborative effort to embed AI‑driven security into data‑center software stacks. The initiative centers on Claude Mythos, a model that scans for vulnerabilities across cloud platforms and open‑source components in real time. Leading providers such...

Researchers Warn Microsoft Defender Vulnerability Is Already Being Exploited
Security researcher Chaotic Eclipse disclosed a vulnerability dubbed “Red Sun” (CVE‑2026‑33825) that lets Microsoft Defender rewrite cloud‑tagged files, potentially overwriting system files and escalating privileges. The proof‑of‑concept suggests the flaw is already being weaponized in the wild. Microsoft’s Security Response...

Sam Altman's "Proof of Human" Company Pushes Into Mainstream Services
World, the identity‑verification startup co‑founded by Sam Altman, announced a wave of new integrations with Zoom, DocuSign, Tinder, Okta, Shopify and VanEck. The company upgraded its World ID protocol, open‑sourced it for any app, and launched a standalone app for...

CISA Resources ‘More Limited than I Would Like’ Amid Shutdown, Top Official Says
CISA acting director Nick Andersen told House appropriators that the agency’s ability to detect and counter hacking threats is severely constrained by the Department of Homeland Security shutdown. The shutdown forces CISA to limit spending to employee salaries, with any...

Most Enterprises Can't Stop Stage-Three AI Agent Threats, VentureBeat Survey Finds
A VentureBeat three‑wave survey of 108 enterprises reveals that most organizations rely on monitoring AI agents without enforcing controls or isolating workloads, a structural gap that leaves them vulnerable to stage‑three threats. While 88% reported AI‑agent security incidents in the...