
DWP’s £300m Pensions Dashboard Scheme Commissions Security Review Ahead of Provider Connections
The Department for Work and Pensions’ £300 million (≈ $381 million) Pensions Dashboards Programme has commissioned a £50,000 (≈ $63,500) security review as it approaches a six‑month deadline for private‑sector pension providers to connect. Leeds‑based cyber consultancy tmc3 will assess the security of the cloud‑based connection process and produce a repeatable assurance framework. The phased rollout aims to link all private schemes by the end of October, with the programme slated to close in March 2027. The initiative promises a unified digital view of state, occupational and personal pensions for UK citizens.

One Login: GDS to Create ‘Easily Digestible Version’ of Privacy Impact Report
The UK Government Digital Service (GDS) announced it will publish an "easily digestible" version of the Data Protection Impact Assessment (DPIA) for the GOV.UK One Login by the end of 2026, though the full unedited report is unlikely to be...

South Africa ‘Isn’t Ready’ for AI-Accelerated Cyberattacks
Anthropic unveiled Claude Mythos Preview, an AI model that can pinpoint software vulnerabilities within minutes, raising unprecedented cybersecurity concerns. A mis‑configuration leak revealed the model’s existence, underscoring the speed gap: 77% of organizations globally need over a week to patch,...
Network ‘Background Noise’ May Predict the Next Big Edge-Device Vulnerability
GreyNoise’s 103‑day study of network background noise identified 104 distinct traffic surges targeting 18 edge‑device vendors. The research found that roughly half of these spikes were followed by a public vulnerability disclosure within three weeks, with a median lead time...

Half of the 6 Million Internet-Facing FTP Servers Lack Encryption
A Censys study found roughly 6 million internet‑facing FTP servers, with 2.45 million (about 41%) offering no encryption. While the total number of FTP hosts fell 40% since 2024, the protocol still represents 2.72% of all visible internet services. Pure‑FTPd powers the...

NCSC Outlines Coordinated Plan to Boost NHS Cyber Resilience
The UK National Cyber Security Centre (NCSC) unveiled a coordinated plan to strengthen cyber resilience across the NHS, built on 18 months of government‑industry collaboration. The strategy pivots on five pillars, including the Active Cyber Defence 2.0 pilot, software‑supply‑chain hardening,...

The Hidden Cost of Healthcare Data Breaches
Health‑insurance data breaches have exposed over 400 million identities since 2021, yet plan sponsors, TPAs and carriers provide no post‑breach fraud protection. HIPAA settlements can reach $25,000 per stolen identity, while remediation averages more than $13,000 per individual, creating a lucrative...

Multi-Cloud Trust Integrity-Based Security Management Architecture for Blockchain- Enhanced Secure Network Slicing Using CKBNA and SFDA
A new multi‑cloud security framework introduces a Crystals‑Kyber Bickley‑Naylor (CKBNA) key‑establishment protocol and a Struve Function‑based Dilithium (SFDA) signature scheme to protect Secure Network Slicing (SNS). The architecture leverages an IpLUEN‑LSTM model for slice prediction, Hyperbolic Growth Gazelle Optimization for...

Phishing Attacks Concentrate on Big Tech as Identity Becomes Prime Target
Check Point Research's Q1 2026 Brand Phishing Ranking shows Microsoft remains the most impersonated brand, accounting for 22% of phishing attempts, with Apple, Google, Amazon and LinkedIn completing the top five. The four brands together represent nearly half of all phishing...

How Proactive DEX Strengthens IT Compliance in Financial Services
Financial services firms are grappling with tighter regulations and increasingly complex, distributed IT environments, making traditional reactive compliance models inadequate. Proactive Digital Experience (DEX) management, exemplified by TeamViewer DEX, continuously monitors device health, performance, and user‑experience signals to anticipate issues...
What the Ransom Note Won’t Say
In March 2024 a BlackCat ransomware affiliate complained on a cybercrime forum that it never received its share of the $22 million ransom paid after the Change Healthcare breach, alleging the gang vanished with the funds and posted a fake FBI seizure...
Shadow Data Is a Hidden Risk that AI Can Reveal
Shadow data—forgotten copies of sensitive information scattered across endpoints, cloud storage, SaaS tools and generative‑AI prompts—remains invisible to most security teams. Research from Palo Alto Networks shows over 80% of sensitive data lives outside traditional controls, a problem amplified by...

Beyond IT: Cybersecurity Is a Strategic Business Risk
On November 25, 2025 the SEC censured a national securities firm and imposed a $325,000 penalty after a breach exposed the personal data of roughly 8,500 people. The regulator highlighted the firm’s weak cyber‑governance, noting missing multi‑factor authentication and absent incident‑response plans....

UAE Cyber Security Council Warns 1 in 4 Public Files Contain Sensitive Personal Data
The UAE Cyber Security Council reports that 25% of publicly accessible files contain sensitive personal data, and up to 77% of privately shared files may be exposed due to weak controls. The advisory highlights a widening gap between rapid cloud...

Next.js Creator Vercel Hacked
Vercel, the creator of the Next.js framework and a leading frontend cloud platform, confirmed a breach on April 20, 2026 after a hacker group offered its stolen databases, source code, and access keys for $2 million. The intrusion stemmed from a...
Ransomware’s Next Phase: From Data Encryption to Business Extortion
Ransomware has morphed from simple file‑encryption attacks into a multi‑layered business extortion threat, driven by AI‑enhanced reconnaissance and data exfiltration. BlackFog’s 2025 State of Ransomware Report shows a 49% year‑on‑year rise in disclosed incidents and a growing shadow of undisclosed...

DeFi Users Pull $10 Billion Out of the Market as $292 Million Exploit Sparks Bank-Run Optics
A $292 million exploit of KelpDAO's cross‑chain bridge drained roughly $10 billion from DeFi markets, prompting a cascade of withdrawals. The attacker siphoned 116,500 rsETH, a liquid restaking token, and moved the funds through Tornado Cash before targeting lending platforms. Aave suffered...

Vercel Incident Linked to AI Tool Hack, Internal Access Gained
Vercel disclosed a security breach that stemmed from a compromised third‑party AI platform, Context.ai, which gave attackers access to an employee’s Google Workspace account and subsequently to internal systems. The intruders viewed non‑sensitive environment variables, while encrypted sensitive variables remained...

Cisco Patches Critical ISE Vulnerabilities Allowing Remote Code Execution Attacks
Cisco released emergency patches for its Identity Services Engine (ISE) and Webex Services after uncovering multiple critical vulnerabilities. Three ISE flaws (CVE‑2026‑20147, CVE‑2026‑20180, CVE‑2026‑20186) score 9.9 CVSS and enable remote code execution, privilege escalation, and potential denial‑of‑service. A separate Webex...

Analysis of 200 Education Dept-Endorsed School Apps Finds Most Are Selling BS when It Comes to the Privacy of Children’s...
Researchers at UNSW audited nearly 200 Android educational apps recommended by Australian schools and found pervasive privacy violations. Most apps begin transmitting device identifiers and location data within seconds of launch, and 80% embed hard‑coded API secrets accessible to anyone...
Global Financial Watchdog to Share Insights on Anthropic’s Mythos
The Financial Stability Board (FSB) is collecting data from its members on the potential systemic risks posed by Anthropic’s Mythos AI model, aiming to disseminate findings to regulators and central bankers worldwide. Bank of Canada Governor Tiff Macklem highlighted the urgency...
Top 3 Cyber Insurance Incident Claims
Cowbell’s 2026 Claims Report shows data breaches (33.5%), cybercrime (31.8%) and extortion (18.3%) dominate cyber‑insurance claims. Meanwhile, AM Best notes U.S. cyber premiums slipped to $9.14 B while claim frequency jumped 40%, signaling a loss‑heavy environment despite lower premium volume. Industry experts...
India’s AI Moment Isn’t About Speed, It Is About Control
India’s enterprises have moved AI from pilot projects to production, with nearly half running multiple AI use cases at scale. The conversation is shifting from deployment speed to maintaining control over these models, as behavioral failures can slip past traditional...

Australia’s Privacy Commissioner Tried, in Vain, to Sound the Alarm on Data Protection During the U16s Social Media Ban Trials
Australia’s Office of the Australian Information Commissioner (OAIC) warned that the Age Assurance Technology Trial (AATT), commissioned to test tech for the teen social‑media ban, overstated its privacy safeguards. The regulator flagged terms such as “privacy‑preserving” and “privacy by design”...

Zero-Trust Implementation: Understanding NSA’s Phase One and Phase Two Guidance
The National Security Agency released detailed Zero‑Trust Implementation Guidelines (ZIG) that split adoption into Phase One and Phase Two. Phase One requires 36 activities and 30 capabilities to build a foundational trust architecture, while Phase Two adds 41 activities and 34 capabilities for expanded...
Prepare Your Pipeline for AI-Discovered Zero-Days
Anthropic's Mythos preview model uncovered thousands of zero‑day vulnerabilities, including a 27‑year‑old OpenBSD bug, and chained four flaws into a functional browser exploit. The company warns that comparable AI‑driven attack tools could appear in the hands of adversaries within six...

Integrating Red Hat Lightspeed with CrowdStrike for Enhanced Malware Detection Coverage
Red Hat announced that its Lightspeed security service now integrates CrowdStrike’s malware intelligence, adding more than 2,400 CrowdStrike YARA signatures to the existing IBM X‑Force library for Red Hat Enterprise Linux (RHEL) customers. The joint offering lets users scan RHEL 9 and 10 systems...

GitHub Copilot's New Policy for AI Training Is a Governance Wake-Up Call
GitHub announced that, beginning April 24, 2026, interaction data from Copilot Free, Pro and Pro+ users—including prompts, code snippets and context—will be used to train its AI models by default, unless users opt out. Business and Enterprise customers are exempt...

Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation
Vercel, the cloud deployment platform behind Next.js, disclosed a supply‑chain breach that stemmed from a compromised third‑party AI tool, Context.ai. Attackers exploited Google Workspace OAuth scopes granted to Context.ai, gaining privileged access to Vercel’s internal environments. While Vercel says the...

The Potential Threats of Anthropic Mythos to the NHS
Anthropic’s Mythos model, a frontier large‑language model capable of autonomous vulnerability discovery and exploitation, marks a watershed in AI‑driven cyber offense. Independent testing shows Mythos achieving an 83.1% success rate on the CyberGym benchmark and a 72% end‑to‑end exploit rate,...

White House Fraud Crackdown Sharpens Focus on Digital Identity
The White House’s Executive Order 14390, issued on March 6, calls for tighter federal coordination to combat cyber‑enabled fraud and emphasizes stronger digital identity verification at government entry points. While the order focuses on law‑enforcement actions, industry leaders argue that...

TikTok’s US Joint Venture Gains Security Infrastructure Certification
TikTok USDS Joint Venture has secured ISO/IEC 27001:2022 certification, confirming its information‑security management system meets global standards. The certification follows the 2024 Protecting Americans from Foreign Adversary Controlled Applications Act, which forced the sale of TikTok’s U.S. operations to a U.S.‑owned...

Aave Sees $6 Billion Deposit Drop as Kelp Hack Exposes Structural Risk for DeFi Lender
Aave’s total value locked plunged from $26.4 billion to roughly $20 billion after a hack on the Kelp bridge allowed attackers to deposit 116,500 rsETH (about $292 million) as collateral and borrow $196 million of wrapped ether. The exploit did not breach Aave’s contracts...

A History of Global Hacking — and Where It’s Going Next
Allie Mellen’s new book *Code War* chronicles the evolution of nation‑state cyberattacks, from early exploits like Stuxnet to recent Iranian incursions against U.S. energy and water systems. Drawing on her Forrester analyst background, Mellen links historic hacks to emerging threats shaped...

Malicious Browser Extensions: An Overlooked Security Threat
Browser extensions, once seen as harmless utilities, have become cloud‑connected mini‑apps that can access every SaaS interaction a user performs. In early 2025 Google removed a batch of Chrome extensions that turned malicious after developer accounts were compromised, exposing over...

Crypto Hack Worth $290 Million Triggers DeFi Contagion Shock
On April 19, 2026, hackers exploited a LayerZero‑powered cross‑chain bridge to steal approximately 116,500 rsETH, valued at about $293 million, making it the largest DeFi breach of the year. The attack targeted the Kelp DAO’s rsETH token, a restaked Ether derivative,...

Why Satellite Cybersecurity Is Becoming a Board-Level Issue for Critical Infrastructure
Satellite communications have moved from niche links to the backbone of energy, transport, defense and emergency operations. Cyber risk now spans the entire space‑to‑ground stack—including spacecraft, ground stations, cloud services and customer terminals. The 2022 Viasat KA‑SAT hack showed how...

Singapore Ranks No 1 for Cyber Defences but Boardrooms Are the Weak Link
Singapore topped the Economist Impact‑Telstra study for overall digital resilience in APAC, excelling in risk management, workforce capability and cultural agility. Yet its executives ranked near the bottom on leadership, with 71% of boards not regularly reviewing resilience plans. Responsibility...
Old Cars 'Tell Tales' By Storing Data That's Never Wiped
Security researcher Romain Marchand recovered a telematic control unit from a Polish salvage yard and extracted its Linux file system, finding unencrypted GPS logs that tracked a BYD electric vehicle from its Chinese factory to the United Kingdom and finally...

2026's Biggest Crypto Exploit: $292 Million Gets Drained From Kelp DAO with Wrapped Ether Stranded Across 20 Chains
An attacker exploited Kelp DAO's LayerZero‑powered bridge, draining 116,500 rsETH worth about $292 million—roughly 18% of the token’s circulating supply. The hack triggered emergency freezes across DeFi platforms such as Aave, SparkLend, Fluid and Upshift, and contributed to a 10% drop...

The iPhone Hack That Could Max Out Your Visa Card
High‑tech thieves have demonstrated a method to drain funds from iPhones using Express Transit mode when linked to a Visa card. The hack requires the victim's phone to tap a compromised NFC reader, which then relays payment data to a...

I Encrypted My DNS with a Free App and It Works Brilliantly
Cloudflare has released a free app, 1.1.1.1 + WARP, that encrypts DNS queries on Windows, macOS, Linux, Android and iOS. The client offers two operating modes: a lightweight DNS‑only mode that protects lookups, and a full‑WARP mode that tunnels all traffic through...

Critical Flaw in Protobuf Library Enables JavaScript Code Execution
A critical remote code execution vulnerability was discovered in protobuf.js, a widely used JavaScript implementation of Google’s Protocol Buffers that sees roughly 50 million weekly npm downloads. The flaw, tracked as GHSA‑xq3m‑2v4x‑88gg, stems from unsafe dynamic code generation that lets malicious...
ShowDoc Vulnerability Patched in 2020 Now Used in Active Server Takeovers
Researchers have confirmed that the five‑year‑old ShowDoc vulnerability CVE‑2025‑0520 is being actively exploited to upload malicious PHP web shells, granting remote code execution and full server takeover. The flaw, an unrestricted file‑upload issue with a CVSS score of 9.4, was...
NAKIVO v11.2: Ransomware Defense, Faster Replication, vSphere 9, and Proxmox VE 9.0 Support
NAKIVO Backup & Replication v11.2 is now generally available, adding automated real‑time replication, full support for VMware vSphere 9 and Proxmox VE 9.0/9.1, and native OAuth 2.0 email authentication. The release embeds immutable backups, AES‑256 encryption and pre‑recovery malware scanning to harden ransomware...
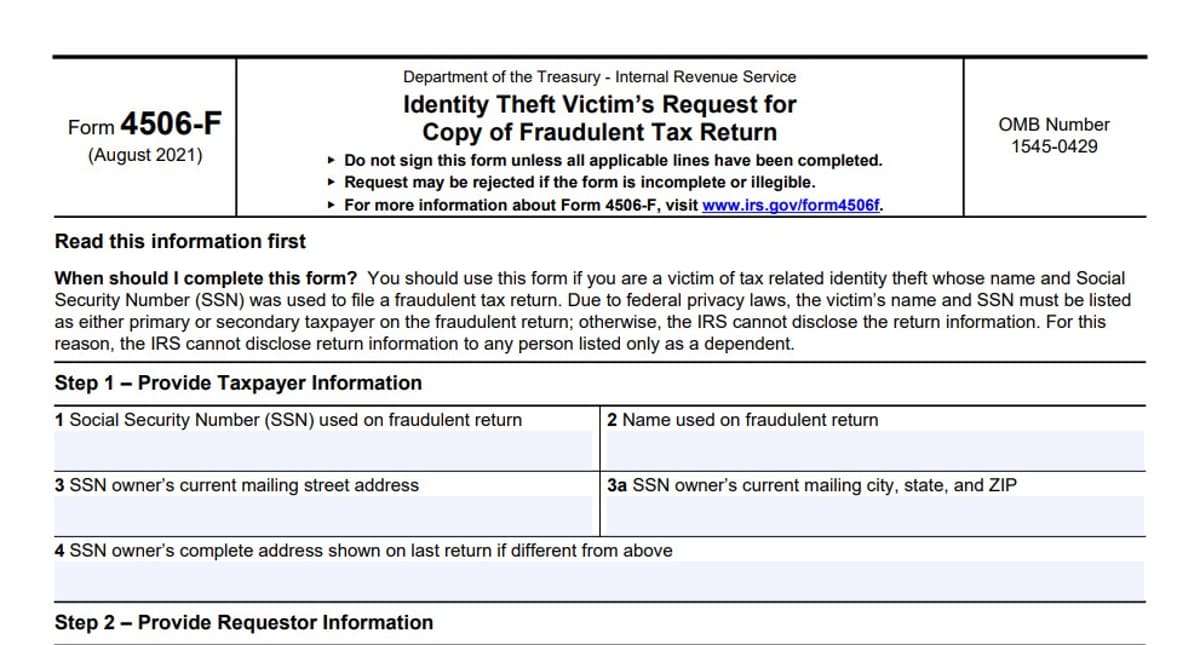
Tax Documents for School Employees Potentially Stolen Across Los Angeles County
The Los Angeles County Office of Education (LACOE) is probing a possible breach that exposed electronic tax documents of teachers and administrators after fraudulent filings were reported. Two school districts received letters about fake tax returns, but LACOE has not...
Judge Lets State Auditor’s Investigation Into Data Breach Affecting Blue Cross Blue Shield Members Move Forward
A Montana state district judge dismissed Health Care Service Corporation’s lawsuit, allowing the state auditor to continue probing a data breach that may have exposed the protected health information of roughly 462,000 Blue Cross Blue Shield of Montana members. The...
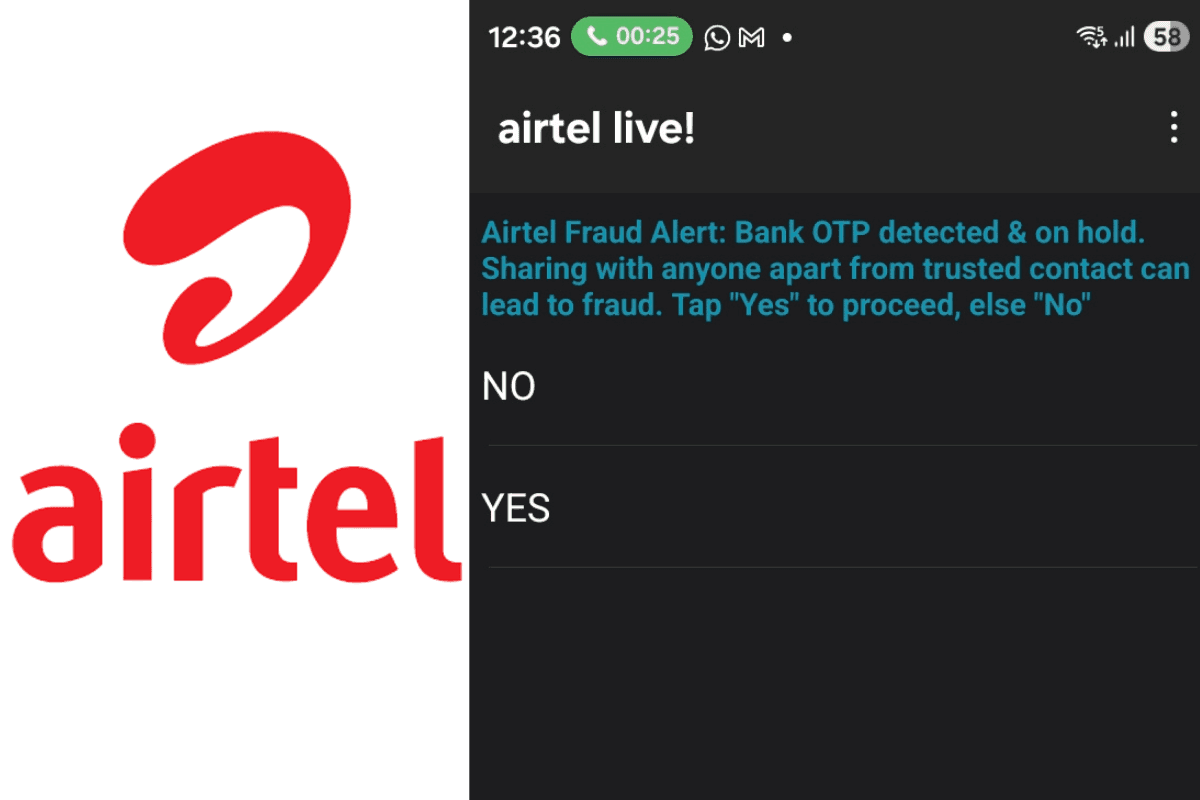
Airtel Starts Warning Users During Calls for OTP Fraud
Bharti Airtel has rolled out a real‑time on‑screen alert that triggers during live calls whenever a bank one‑time password (OTP) is detected. The feature nudges users to pause and reconsider sharing sensitive information, rather than blocking the call. By intervening...
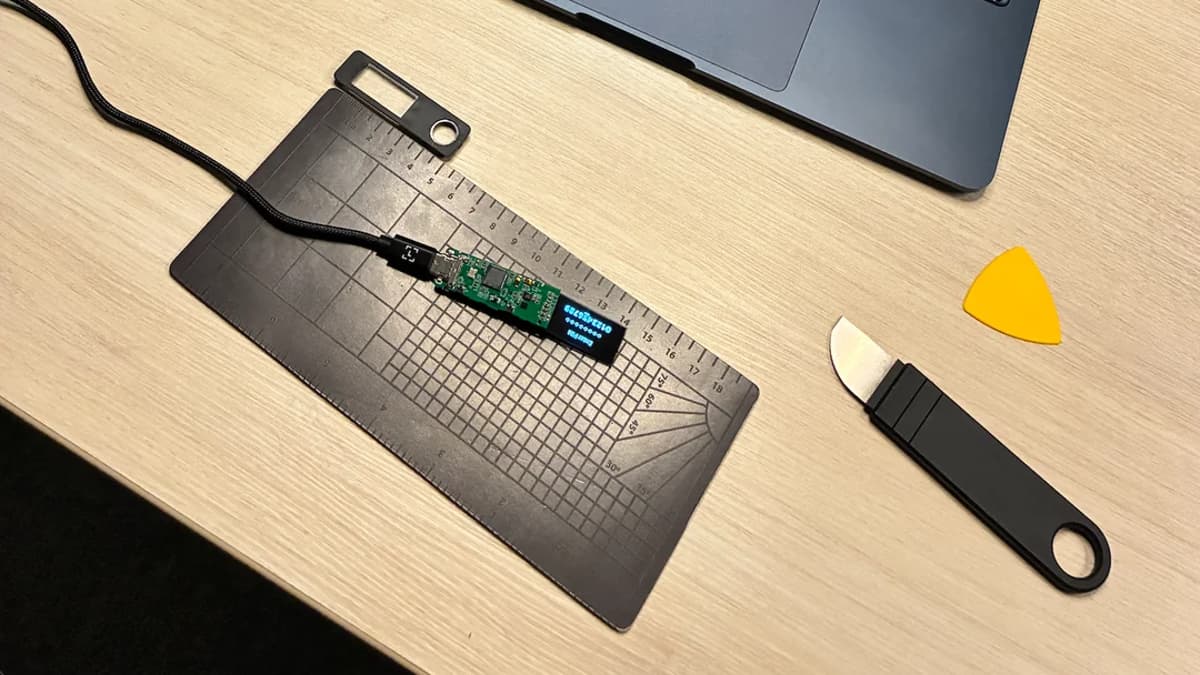
Techie Buys Fake Ledger Nano S+ Hardware Crypto Wallet and Almost Falls for Phishing — a Convincing Clone Would Have...
Brazilian cybersecurity professional Joje Mendes purchased a counterfeit Ledger Nano S+ from a Chinese marketplace and discovered the device was a sophisticated phishing tool. Ledger’s official software flagged the hardware as non‑genuine, prompting Mendes to open the case and find an...

JanelaRAT Malware Now Hijacking Banking Sessions of Users in Latin America : Research
Kaspersky’s GReAT team has identified a new JanelaRAT variant that specifically targets online banking customers in Brazil and Mexico. The malware disguises itself as a pixel‑art program and is delivered via phishing emails containing malicious VBS scripts. Unlike earlier versions,...