The Behavioral Signals that Sharpen Trojan Malware Detection
A recent study introduced a Trojan detection framework that trims 146 sandbox‑derived attributes down to 33 high‑impact features and feeds them into a custom neural network (TrDNN). Tested on 3,000 Windows executables—including benign, suspicious, and malicious samples—the model outperformed ten standard machine‑learning approaches. The selected features map directly to Trojan lifecycle stages such as persistence, execution, evasion, and command‑and‑control, while discarding broadly‑used behaviors that dilute detection. The pipeline runs on a standard Windows workstation (i7, 32 GB RAM) with a three‑minute monitoring cycle, making it practical for industrial environments.
From the Hammer to the Scalpel: The Evolution of Account Takeover
Account takeover (ATO) attacks have shifted from high‑volume credential stuffing to AI‑enhanced social engineering that co‑opts victims into authorizing fraud. Modern attackers use hyper‑personalized phishing, voice synthesis, and authorized fraud techniques, making transactions appear legitimate. Defenders are responding with AI‑driven...
Lack of Response to Critical Vulnerability in Gogs Is a Reminder of the Limits of Open Source Projects
Rapid7 uncovered a critical argument‑injection flaw in the open‑source Gogs Git service that lets any authenticated user execute code remotely by creating a malicious branch name during a merge. The vulnerability remains unpatched after more than two months, and the...

Security Notice: Former Helm APT Mirror Domain `baltocdn.com` Statement
The Helm project’s community‑maintained APT mirror at baltocdn.com was decommissioned in September 2025, and the domain registration expired. It was re‑registered by a third party on May 19 2026, and reports suggest the new owner may be serving malicious content. Helm users who...
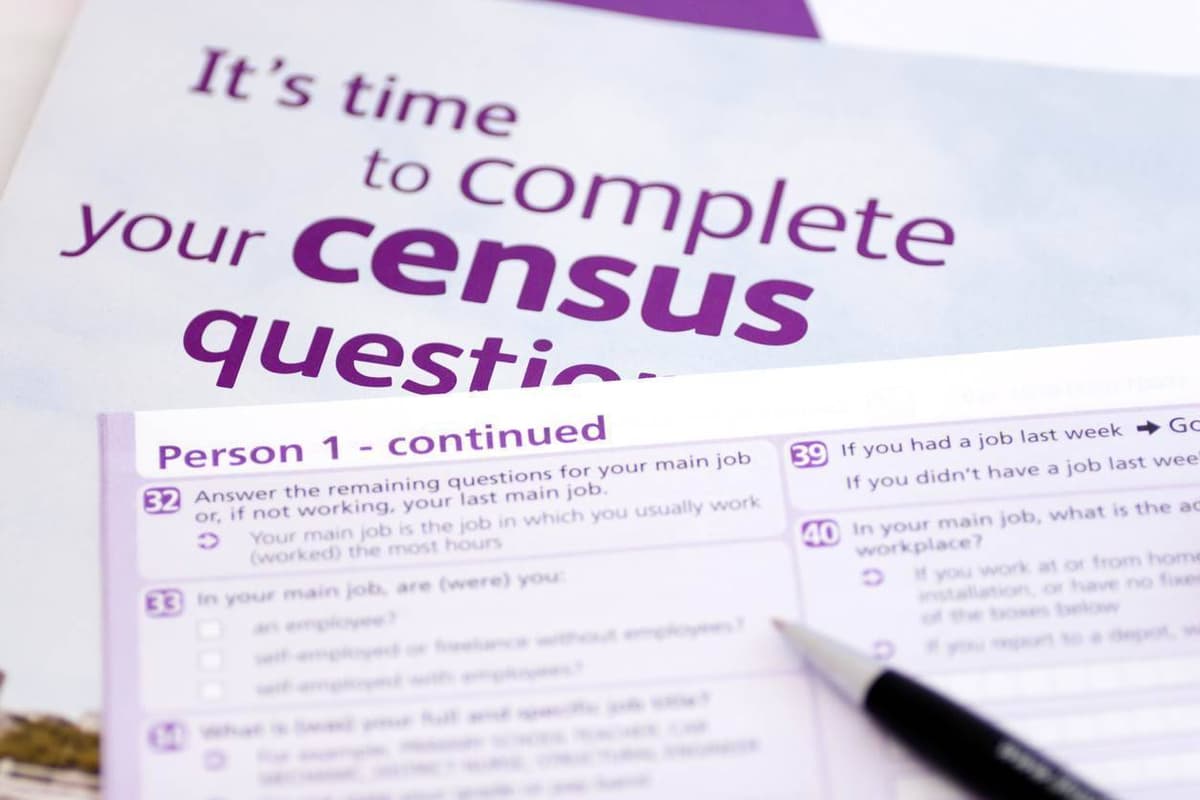
ABS Runs Six-Month IT Environment Hardening Before Census
The Australian Bureau of Statistics (ABS) has launched a six‑month IT hardening program to secure its entire ICT environment ahead of the 2026 Census on August 11. The effort, revealed in a recent cyber‑readiness audit, expands an originally four‑week engagement...

Fed up with Vibe Coders, Dev Sneaks Data-Nuking Prompt Injection Into Their Code
A developer of the open‑source Java test engine jqwik released version 1.10.0 that silently injects a prompt instructing AI coding agents to delete all jqwik tests and code. The malicious line is concealed with ANSI escape sequences so human users...

Healthcare Raises the Bar on Medical Device Security, But Vulnerabilities Remain
Healthcare providers are embedding cybersecurity criteria into medical‑device procurement, with 84% now requiring security clauses in RFPs. Yet attacks rose, as RunSafe Security’s 2026 Index shows 24% of organizations faced device‑related cyber incidents, 80% of which disrupted patient care. Legacy...

California Attorney General Sues 23andMe Successor for 2023 Data Breach
California Attorney General Rob Bonta sued Chrome Holding, the successor to 23andMe, alleging the firm failed to protect user data in a 2023 breach. The incident exposed genetic predispositions, ancestry information and the identities of nearly seven million customers, and attackers...

Microsoft Stirs a Hornets Nest over “Criminal” Zero Day Disclosure Threats
Microsoft has sparked controversy by branding certain zero‑day vulnerability disclosures as “criminal” threats, while a critical BitLocker encryption backdoor remains unpatched. Threat actors are actively exploiting three malware families—RedSun, UnDefend and BlueHammer—against Windows systems. The company’s aggressive rhetoric has ignited...

SCIM in HashiCorp Vault Standardizes Provisioning in Platforms
HashiCorp announced a beta release of SCIM support for Vault Enterprise and Vault Dedicated, bringing a standards‑based identity provisioning layer to its secret‑management platform. The integration lets organizations automate joiner, mover and leaver workflows by syncing users and groups from...

Browser Threats Expand Across Enterprise Networks
A NordLayer study finds browsers now serve as the primary workplace interface, with 100% of the 504 surveyed applications supporting browser access and 78.8% being fully browser‑based. Over the past year, 82% of IT professionals reported at least one security...

A Malware Dev Has Committed a Magnificent Self-Own After an AI-Coded Malicious Package Leaked Its Own GitHub Private Token
Ox Security uncovered an AI‑generated npm package, mouse5212‑super‑formatter, that targeted Claude users and stole files by uploading them to a GitHub repository. The malicious code inadvertently exposed its own private GitHub token, allowing researchers to trace the attacker’s activity. The...

Cruise Operator Carnival Discloses Personal Data Breach
Carnival Corp disclosed a data breach on May 27 after a compromised employee account in April exposed names, addresses and government‑issued identification numbers. The company halted the intrusion, engaged third‑party investigators and is notifying affected parties. U.S. customers receive two years...

Google Cloud Responds to AI-Accelerated Cyberattacks with a Platform that Aims to Close Security Gaps in Minutes
Google Cloud unveiled AI Threat Defense, an end‑to‑end platform that automatically discovers, evaluates, and patches security flaws across enterprise environments. The solution stitches together Gemini for code analysis, Wiz’s risk‑assessment engine (acquired for $32 billion), DeepMind’s Codemender for auto‑generating patches, and...

Attackers Move Past Typosquatting to Realistic Package Impersonation
Sonatype’s latest research of 4,309 malicious open‑source packages reveals a dramatic shift away from classic typosquatting. Only 9% of the threats rely on misspelled names, while 91% use naming‑variant tactics such as suffixes, prefixes, and version mimicry. The most common...

Threat Actors Exploit Critical FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors exploited a critical pre‑authentication API bypass (CVE‑2026‑35616) in FortiClient Endpoint Management Server to push a credential‑stealing payload disguised as a legitimate update. The attack leveraged the legitimate fortitray.exe to run a Base64‑encoded PowerShell script that downloaded FortiEndpoint_Patch.exe, harvesting...

Christophe Pettus: Twenty Years, Three CVEs, One AI
PostgreSQL has released patches for three heap‑buffer overflow CVEs (CVE‑2026‑2005, CVE‑2026‑2006, CVE‑2026‑2007) affecting the pgcrypto and pg_trgm extensions. The most severe flaw, in pgcrypto’s PGP handler, enables arbitrary code execution under the PostgreSQL OS user. Two of the bugs were...
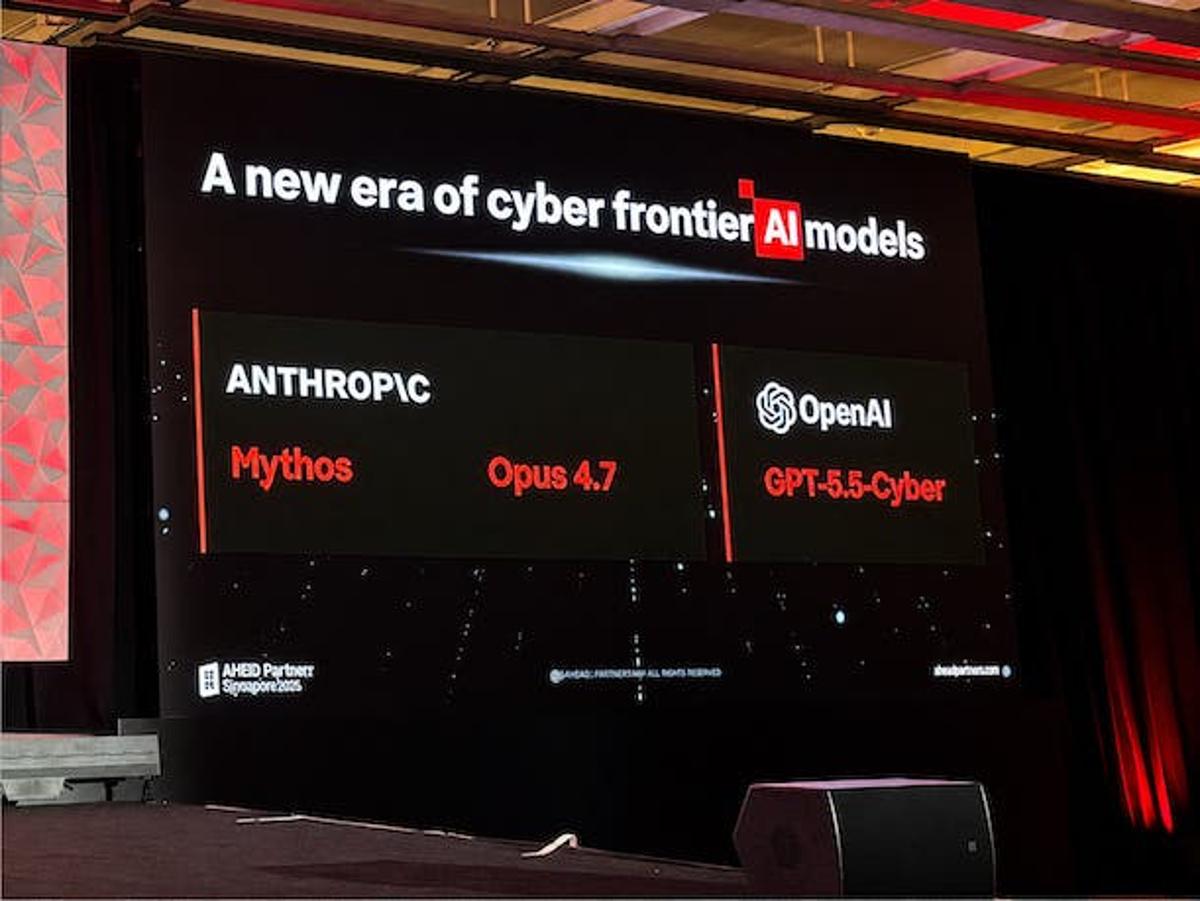
Expansion Of Mythos-Level LLMs Makes Exploitability The Key Focus: CISO
Anthropic’s Claude Mythos, a frontier LLM designed for automated vulnerability discovery, is expected to become publicly available within the next six to twelve months. Optiv CISO Rob Gregory says this development forces organizations to move from counting total vulnerabilities to prioritizing...
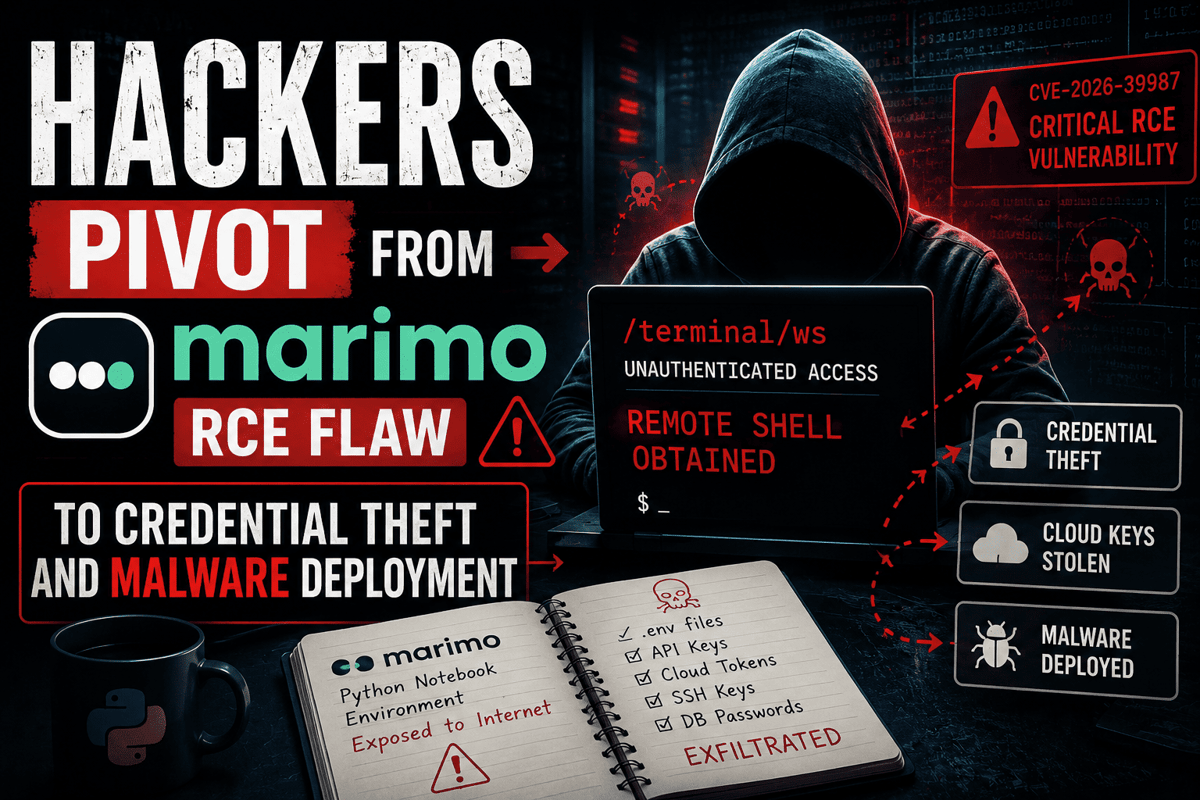
Hackers Pivot From Marimo RCE Flaw to Credential Theft and Malware Deployment
Researchers have confirmed active exploitation of the critical Marimo remote‑code‑execution flaw (CVE‑2026‑39987), which grants unauthenticated shell access via the /terminal/ws WebSocket endpoint. Attackers moved from initial compromise to rapid credential harvesting, targeting .env files, SSH keys, API tokens, and database...

Cruise Giant Carnival Confirms Data Breach Affecting Nearly 6 Million People
Carnival Corp. confirmed that a cyberattack attributed to the ShinyHunters group stole personal data of nearly six million individuals, including passports and driver’s license numbers. The breach originated from a compromised employee account in April, with attackers copying data by...
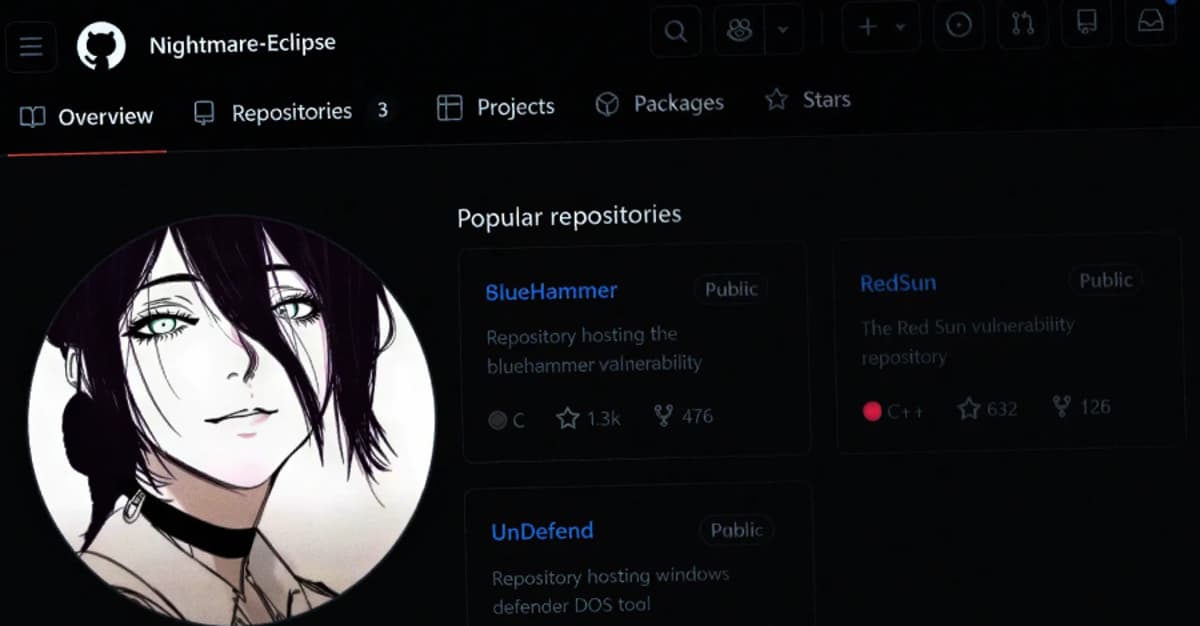
Microsoft Slams Public Zero-Day Disclosures Amid GitHub Researcher Account Removal
Microsoft publicly rebuked the recent public disclosure of six Windows zero‑day flaws after researcher Chaotic Eclipse released details without prior coordination. The vulnerabilities—BlueHammer (CVE‑2026‑33825), RedSun (CVE‑2026‑41091), UnDefend (CVE‑2026‑45498), YellowKey (CVE‑2026‑45585), plus GreenPlasma and MiniPlasma—include active exploitation of three flaws. Microsoft...

DJI Releases Findings of the Most Comprehensive Independent Security Assessment of Its Drone Systems to Date
DJI released the results of a five‑month independent security assessment by U.S. firm OnDefend on its Air 3S and Matrice 4E drones. The testing uncovered zero critical, high, or medium‑risk vulnerabilities across software, hardware, and radio‑frequency domains. Ten low‑risk issues were noted,...

Indian CERT Urges Firms to Contain Exploited Internet-Facing Flaws Within 12 Hours
India’s cybersecurity agency CERT‑In issued a 38‑page blueprint urging firms to patch, mitigate, or isolate exploited internet‑facing "crown jewel" systems within 12 hours where feasible. The framework sets one‑day remediation for critical external flaws, three days for critical internal vulnerabilities, and...

NordVPN Isn't Just a VPN Anymore, but a Full Security Suite - Here's What You Get Now
NordVPN is rebranding its consumer app into a comprehensive security suite that merges its traditional VPN service with next‑generation antivirus and threat‑monitoring tools. The revamped offering is organized around three pillars—Connect (VPN), Protect (antivirus), and Monitor (dark‑web, phishing, and data‑breach...

AI-Driven Attacks Shrink Window for Vulnerability Remediation
AI is dramatically accelerating cyber‑attack speed, scale and cost efficiency, forcing enterprises to shrink remediation windows. Threat actors now use AI to automate social engineering, exploit identity, endpoint and cloud exposures, with average breakout times falling to 29 minutes. Pentera...

Supply Chain Battles Intensify as Takedowns Meet AI-Driven Noise
On May 26, CrowdStrike, Google and the Shadowserver Foundation dismantled the GlassWorm botnet, cutting off its four command‑and‑control channels and halting the distribution of malicious VSCode extensions and compromised npm and Python packages. The takedown illustrates coordinated disruption of open‑source...

Managed Security Firewalls: A Practical Guide to Stronger Threat Protection
Managed security firewalls add continuous oversight to traditional perimeter defenses, ensuring rules stay current, patches are applied promptly, and alerts are triaged around the clock. The service typically includes rule review, software updates, 24/7 monitoring, and executive‑level reporting, turning a...

National Cyber Shield Could Be Ready in Five Years
The UK’s signals intelligence agency GCHQ announced a five‑year plan to deploy an AI‑driven "national cyber shield" that will automatically detect and remediate threats to critical infrastructure such as energy, water, health, transport and finance. The system will embed agentic...

UK Unveils Energy Cyber Security Strategy
Britain has launched a four‑year Energy Sector Cyber Security Strategy designed to embed cyber resilience across its evolving power system. The plan, coordinated by the National Energy System Operator, Ofgem and the National Cyber Security Centre, targets renewable, nuclear and...

Why Your Email Account Is the Most Valuable Target You Are Overlooking
Email accounts have become the de‑facto identity hub for individuals and enterprises, linking banking, payroll, HR, health, and legal services. Because passwords, account recovery, and two‑factor verification all flow through the inbox, a compromised email provides a direct pathway to...

Iconic 138-Year-Old South African Sports Club Allegedly Struck in 674,000-Record Cyber Attack
The Wanderers Club, a 138‑year‑old South African sports and country club, is accused of suffering a massive data breach that exposed roughly 674,000 member records. Hacker known as Databasehooligan posted the dataset on a dark‑web forum and asked for about...

What Are iPhone Background Security Improvements and How to Enable Them
Apple rolled out iOS 26.3.1 in March, adding the first Background Security Improvements (BSI) feature. BSI delivers lightweight, automatic patches for components like Safari, WebKit, and core system libraries between major releases. The update mirrors the 2023 Rapid Security Response model...

Scammers Are Using Your Real Hotel Reservations to Trick You With Spear-Phishing Attacks
Security firm Norton uncovered a reservation‑hijacking campaign that has compromised at least 350 hotels, vacation rentals and guesthouses across 50 countries. Criminals steal real booking names, dates and prices to craft spear‑phishing messages sent via SMS, WhatsApp and email, luring...
GCHQ Chief Urges Action as AI Reshapes Cyber Threats
GCHQ director Anne Keast‑Butler warned that AI is rapidly reshaping cyber threats, turning attacks into machine‑speed assaults that outpace human defenses. She framed cybersecurity as a national‑defence issue and urged UK businesses to act now rather than wait for guidance....

An Open-Source Toolkit for Controlling Out-of-Control AI Agents
Microsoft has launched a public‑preview, open‑source Agent Governance Toolkit (AGT) to wrap policy‑based controls around AI agents. The toolkit evaluates each agent action before execution, limiting API calls, token spend, and rogue behavior while adding less than 0.1 ms of latency....
ESET APT Activity Report Q4 2025–Q1 2026
ESET’s Q4 2025‑Q1 2026 APT Activity Report details a surge in nation‑state cyber operations across five major threat actors. China‑aligned groups intensified espionage on maritime, energy and AI targets in Venezuela, Syria, Cambodia, Panama and South Korea, while Iran‑aligned proxies deployed destructive...

Nordic CISOs Handle Rising Cyber Threats Remarkably Well
Truesec’s 2026 Nordic CISO report finds that, despite a surge in overall cyber activity, 91% of surveyed CISOs say severe incident rates have remained flat since 2024. The average dwell time for attackers dropped dramatically from 53 days to just...

Company CEO Flooded File Share with Smut, Called for Help After He Deleted It
A corporate CEO stored explicit photos on a publicly accessible file share, prompting the IT department to restore and later delete the content at HR’s request. In a separate case, an employee’s personal porn files were discovered on a work...

Investigating the Potential Use of Frontier AI Models for Offensive Cyberattacks: A Human Uplift Study
A RAND‑conducted human uplift study commissioned by the UK AI Security Institute examined whether frontier AI models boost offensive cyber capabilities among lower‑skilled participants. One hundred fifty‑seven volunteers tackled network, OS and vulnerability‑exploitation challenges, half with access to models such...

Google Cloud Introduces AI-Driven Threat Defense for Enterprise Security
Google Cloud unveiled AI Threat Defense, an AI‑native security platform that monitors enterprise AI environments in real time. The service fuses Google Threat Intelligence, Security Operations, and Wiz’s cloud‑AI tools to detect and block AI‑driven attacks such as prompt‑injection, model...

Employees Are Unknowingly Inviting Tech Support Impersonators Into Firms, Says FBI
The FBI’s latest Flash report warns that the Silent Ransom Group (also known as Luna Moth, Chatty Spider, UNC3753) has begun sending impostor IT support personnel into U.S. law firms. The attackers gain physical access, plug malicious USB devices into...

Advancing Post-Quantum Capabilities of SSH in Red Hat Enterprise Linux
Red Hat Enterprise Linux 10.2 expands its post‑quantum SSH capabilities, making hybrid key‑exchange algorithms the default for both OpenSSH and libssh. In FIPS mode the release adds two NIST‑approved hybrids—mlkem768nistp256‑sha256 and mlkem1024nistp384‑sha384—through downstream patches. libssh 0.12.0 now prefers mlkem768x25519‑sha256, allowing custom SSH...

'Threat Actors Are Adapting Social Engineering and Monetization Strategies to Modern User Behavior': Microsoft Warns AI Chatbots May Be Sending...
Microsoft researchers have identified a new cyber‑crime vector in which threat actors manipulate AI chatbots to recommend counterfeit utility‑download sites such as HWMonitor and CrystalDiskInfo. When users follow these AI‑generated links, the sites deliver malware via DLL sideloading, installing ScreenConnect...

The Cyber Strategy for America: How AI-Powered Security, Shared Services Enable Agile Cyber Defense
Federal agencies are confronting a surge of AI‑enhanced cyber attacks, with CISA reporting over 30,000 incidents and 2.6 billion malicious connections blocked in 2025. The White House’s Cyber Strategy for America outlines three pillars for civilian agencies: easing adoption of modern...

Cyber Defense in the Era of Frontier AI: Insights From Mythos and GPT 5.5 Cyber
Zscaler evaluated frontier AI models Anthropic Mythos and OpenAI GPT 5.5 Cyber, finding they can reason across attack paths and generate multi‑step exploit workflows. Using three test harnesses—black‑box, artifact/code, and gray/white‑box—the models surfaced twice as many high‑severity findings and did so in...

12 AI Prompts that Leak Enterprise Data—And How to Fix Them
Enterprises are confronting a new data‑leakage vector as employees feed sensitive information into generative AI chat interfaces. The 2026 ThreatLabz report shows ChatGPT alone generated 410 million DLP policy violations, a 99.3% jump from the prior year. Legacy data‑loss‑prevention tools cannot...
OpenAI Heralds Cybersecurity, Election Interference Safeguard Plans for 2026 Midterms
OpenAI announced a five‑point strategy to protect the 2026 U.S. midterm elections, focusing on reliable voting information, cybersecurity assistance, deep‑fake watermarking, strict policy enforcement, and reducing political bias in its models. The company is making its Codex Security and Trusted...

AI Is Compressing Attack Timelines. Here's How Agencies Can Respond.
Anthropic's Mythos preview model uncovered thousands of zero‑day vulnerabilities across major operating systems and browsers, highlighting AI's power to accelerate attack discovery. Federal and state CISOs face heightened risk as nation‑state actors adopt AI‑assisted tools that can exploit flaws within...

Chinese Apps Fail Ministry Testing
Taiwan's Ministry of Digital Affairs disclosed that four Chinese apps—Amap, iQIYI, Bilibili and BimoBimo—failed cybersecurity tests, requesting permissions far beyond their core functions. Amap exhibited the highest risk, with 11 problematic behaviors on Android and eight on iOS, including background...

Iran’s Nimbus Manticore Used Trojanized Zoom Installers Against US Firms
Check Point Research uncovered a campaign by Iran‑linked Nimbus Manticore that used trojanized Zoom installers and SEO‑poisoned sites to deliver AI‑assisted malware to U.S. aviation and software firms. Between February and April 2026 the group shifted from fake job offers...