
Some College Finals Delayed After Canvas Online Platform Hacked
Instructure Inc., the KKR‑owned operator of the Canvas learning platform, suffered a cyber‑attack that forced a temporary shutdown of the portal used by thousands of colleges worldwide. Hackers exploited a vulnerability in teacher accounts, gaining access to exam and grading sites. The breach prompted the suspension of finals at institutions such as Princeton University, the University of Manchester, and Universidad del Desarrollo, pushing assessments into the weekend. Most Canvas services were restored Thursday, though teacher accounts remain disabled pending further investigation.

Bring AI Agents Into the Identity Fabric
Okta’s partner content warns that AI‑driven agents are emerging as a non‑human identity layer that expands the cyber‑attack surface. It calls for standardized AI lifecycle management to prevent machine‑speed threats from compromising agency missions. The piece positions the identity fabric...

Microsoft Warns of Sophisticated Phishing Campaign Heavily Targeting Health Care Organizations
Microsoft Threat Intelligence has identified a large‑scale, multistage phishing campaign that disproportionately targeted the U.S. health‑care sector. The operation sent “code of conduct” themed emails to more than 35,000 users across 13,000 organizations, using adversary‑in‑the‑middle techniques to hijack authentication tokens...
'The Biggest Student Data Privacy Disaster in History': Canvas Hack Shows the Danger of Centralized EdTech
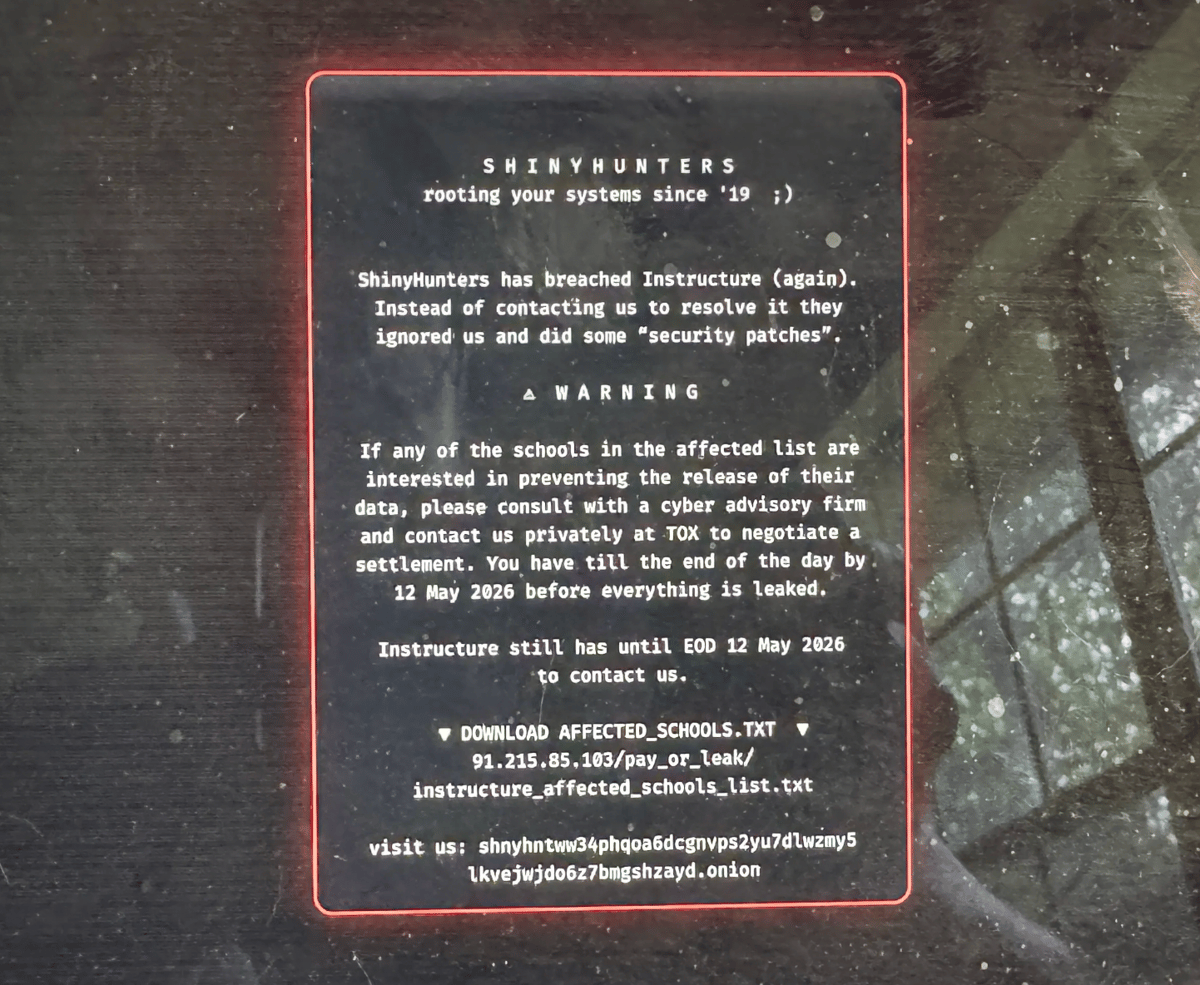
On Thursday, ransomware group ShinyHunters breached Instructure’s Canvas platform, locking out millions of students and stealing data tied to more than 275 million users. The attackers claimed to have exfiltrated names, email addresses, student IDs and private messages, prompting a rapid,...

The Human Factor: Why AI-Powered SOCs Still Need People in Charge
Artificial intelligence is reshaping security operations centers (SOCs), especially when paired with managed detection and response (MDR) services. Sophos’ white paper shows its AI agents can trim alert noise by more than 60% and cut investigation time by up to...

Your Instagram Conversations Won’t Be so Private Anymore
Effective May 8, 2026, Instagram Direct Messages lost end-to-end encryption, meaning Meta and any third party with access can read the content of private chats. The change was quietly noted in a help‑center update in March, with no public announcement...

Mobile Credentials Are an Operational Commitment. Evaluate Them Like One
Mobile credential programs on campuses transition from a technical procurement focus to an operational reality where the system is live the moment a student uses their phone. Unlike traditional enterprise rollouts, there is no soft‑launch window; failures surface immediately and...

5 Steps for Frontier AI Readiness
Frontier AI models such as Anthropic's Claude Mythos and OpenAI's GPT‑5.4‑Cyber can autonomously discover software flaws and generate exploits, compressing the gap between vulnerability discovery and attack. This acceleration forces a move from traditional vulnerability management to continuous exposure management,...

Privacy and Security Rules Extend to Paper Records
Health systems that revert to paper charts during electronic health record (EHR) downtime remain subject to HIPAA’s privacy and security rules, warns Polsinelli attorney Rebecca Romine. The guidance emphasizes that paper‑based protected health information (PHI) must be handled, stored, and...

The 7 Best Endpoint Encryption Software Choices in 2026
The article lists the seven top endpoint encryption solutions for 2026, from free open‑source tools like VeraCrypt to enterprise suites such as ESET PROTECT Complete. It evaluates each product on price, support, password‑manager integration, on‑the‑fly decryption, and enterprise‑grade encryption. Modern solutions...

Healthcare Cybersecurity Has Become an Operational Risk, Not Just a Security Function
Healthcare cybersecurity has moved from a back‑office IT issue to a core operational risk that directly affects patient care, revenue, and regulatory compliance. Ransomware and other attacks now disrupt electronic health records, scheduling, imaging and connected devices, forcing hospitals into...

Multiple Colleges Hit by Disruptions After Canvas Service Hack
Education technology provider Instructure, owner of the Canvas learning platform, suffered a cyber‑attack on May 1 that forced a temporary shutdown of teacher accounts across thousands of colleges, including Harvard, Princeton and Stanford. The breach, attributed to the ShinyHunters group, exploited...

In Other News: Train Hacker Arrested, PamDOORa Linux Backdoor, New CISA Director Frontrunner
The U.S. government is proposing a drastic cut to its critical‑vulnerability remediation window, moving from 14 days to just three days as AI‑driven exploits accelerate. Meanwhile, a new Linux backdoor called PamDOORa is being sold for $900, offering persistent SSH...

What's the Playbook for Continuity and Compliance when IT Systems Are Down
Rebecca Romine of Polsinelli outlines a practical playbook for health‑care providers to preserve patient privacy when cyberattacks force a switch from electronic health records to paper‑based workflows. She stresses pre‑approved paper‑form templates, strict access controls, and real‑time documentation of manual...

'Dirty Frag' Linux Flaw One-Ups CopyFail with No Patches and Public Root Exploit
A new Linux privilege‑escalation vulnerability dubbed "Dirty Frag" has been disclosed without a CVE, patches, or coordinated mitigation. Security researcher Hyunwoo Kim revealed that the flaw chains a 2017 xfrm‑ESP kernel issue with a 2023 RxRPC bug, allowing unprivileged users...

Eyewitness Accounts and Recommended Actions to Counter AI’s Strain on Cyber Defense
Cooley partner Michael Egan warned that artificial intelligence is enabling attackers to develop exploits and ransomware faster, exposing many organizations to heightened risk. He highlighted a pervasive gap: firms often lack incident‑response plans for supply‑chain failures. Egan emphasized the need...

Pam Backdoor Targets Linux Systems to Steal SSH Credentials
Researchers at Group‑IB have identified a new Linux backdoor called Pam that abuses the Pluggable Authentication Modules (PAM) framework, specifically the pam_exec module, to capture SSH credentials. By inserting a malicious entry into /etc/pam.d/sshd, the backdoor runs a hidden script...

Pro-Ukraine BO Team and Head Mare Hackers Appear to Team up in Attacks Against Russia
Pro‑Ukraine hacktivist groups BO Team and Head Mare appear to be coordinating cyber attacks against Russian and Belarusian entities, according to Kaspersky. The firms identified shared command‑and‑control infrastructure and overlapping malware toolsets, suggesting joint operations. BO Team, previously known for autonomous activity, now...

10 Data Breaches to Know About (April 2026)
In April 2026, Security magazine cataloged ten high‑profile data breaches spanning AI startups, government agencies, and consumer brands. Notable incidents include Mercur’s 4 TB loss via a LiteLLM supply‑chain flaw, a breach of an FBI surveillance system allegedly tied to Chinese hackers,...

Wits Restores Learning Platform After Cyber Attack
The University of Witwatersrand (Wits) has restored its Ulwazi learning management system after it was taken offline by a cyber‑extortion attack linked to the ShinyHunters group. The breach originated from a vulnerability in Instructure’s Canvas platform, which affected roughly 8,800...

Fiber Optic Cables Can Eavesdrop on Nearby Conversations
Scientists demonstrated that distributed acoustic sensing (DAS) on fiber‑optic cables can capture nearby speech and convert it into real‑time transcripts using free AI software. The method works best on surface‑coiled fibers within five metres of the sound source, while burial...

The Cyber Express Weekly Roundup: EU AI Act Updates, Malware Expansion, Critical Vulnerabilities, and Rising Cybercrime Trends
The European Union has revised its AI Act, streamlining compliance rules while imposing stricter bans on harmful AI‑generated content. Microsoft‑confirmed ClickFix malware has expanded its campaign to target macOS users with fake troubleshooting pages. A critical PAN‑OS vulnerability (CVE‑2026‑0300) with...

R1.6 Billion Missing After Hackers Ran Free Inside Major South African Metro’s Systems
The City of Ekurhuleni disclosed a massive cyberattack that left R1.19 billion missing, with only R891 million recovered through back‑billing. Hackers exploited an unsecured municipal Wi‑Fi and VPN to infiltrate billing systems, manipulate invoices and erase debts. An internal investigation revealed insider...

How Dangerous Is Anthropic’s Mythos AI? | Bruce Schneier
Anthropic announced Claude Mythos Preview, a generative‑AI model so adept at spotting software flaws that it will be limited to a handful of enterprise partners. The UK AI Security Institute and independent tests show OpenAI’s GPT‑5.5 and smaller, cheaper models...

Modular RAT Campaign Steals Credentials and Captures Screenshots
Seqrite Labs uncovered Operation GriefLure, a spear‑phishing campaign aimed at senior executives of Vietnam’s Viettel Group and the Philippines’ St. Luke’s Medical Center. The attackers delivered a malicious LNK file that leverages the native ftp.exe utility to assemble a modular remote‑access trojan...

Google Ads To Require Passkey For Certain Sensitive Actions After July 15
Google announced that, beginning July 15, 2026, Google Ads will require advertisers to use passkeys for certain sensitive actions. The policy shift follows a recent spike in account hijacks targeting the platform. Passkeys are password‑free credentials that rely on device‑based cryptography, making...

Fake Moustache Trick Raises Questions Over UK Online Safety Act Age Checks
The UK’s Online Safety Act, launched in July 2025, introduced stricter age‑verification and content‑moderation rules to protect children online. Early testing shows simple tricks—such as a 12‑year‑old drawing a fake moustache—can fool AI‑driven facial age checks, exposing a critical vulnerability....

Fake OpenClaw Installer Targets Crypto Wallets and Password Managers
A fake OpenClaw installer is being used to deliver a Rust‑based infostealer called Hologram, which targets over 250 crypto‑wallet and password‑manager browser extensions. The 130 MB dropper evades detection with layered anti‑VM checks, a mouse‑gate, and a PowerShell payload that disables...

68% of Passwords Can Be Cracked Within a Day
Kaspersky’s analysis of 231 million leaked passwords reveals that 68 % can be cracked within a day using AI‑driven brute‑force tools. Predictable structures dominate: 53 % end with digits, 10 % use the “@” symbol, and even 15‑character passwords are broken in under a...

Zara Data Breach Exposed Personal Information of 197,000 People
Spanish fast‑fashion retailer Zara, part of Inditex, suffered a data breach affecting over 197,000 customers. Hackers accessed databases hosted by a former technology provider, extracting email addresses, geographic data, purchase histories, and support tickets, but not names, phone numbers, or...
One Missed Threat Per Week: What 25M Alerts Reveal About Low-Severity Risk
The new Intezer AI SOC report analyzed more than 25 million security alerts across 10 million endpoints and identities. It found that roughly 1 % of alerts classified as low‑severity or informational correspond to real breaches—about one missed incident per week for a...

Google Is Turning Android Studio Into a Policy Watchdog
Google is embedding Play Policy Insights into Android Studio, giving developers real‑time warnings about policy violations and SDK compliance. The upgraded Play Integrity API and post‑quantum support boost fraud detection and cryptographic security. New privacy widgets, developer verification, and AI‑driven...

Your CTEM Program Is Probably Ignoring MCP. Here’s How to Fix It
The piece highlights Model Context Protocol (MCP) as a hidden vulnerability in modern AI toolchains, warning that many security programs overlook it. It details real‑world breaches—such as a malicious npm MCP package that infected 300 firms and high‑severity CVEs that...
I Analyzed the 5 Best Incident Response Tools in 2026
The article reviews the five top incident‑response platforms for 2026—KnowBe4 PhishER, Datadog, Tines, Torq, and Dynatrace—based on G2 ratings, user feedback, and feature depth. Each tool is matched to a specific use case, from phishing triage to AI‑driven root‑cause analysis, and...

ZiChatBot Malware Abuses Zulip APIs for Stealthy C2 Operations
Security researchers have uncovered ZiChatBot, a cross‑platform malware family that hijacks legitimate Python Package Index (PyPI) wheel packages to deliver malicious code to Windows and Linux developers. The payloads are dropped via DLL or SO files, achieve persistence through Run‑registry...

A New Frontier: Identity Stack Evolves for Agentic Systems
Current IAM solutions are built for human users and static applications, relying on RBAC and MFA. Agentic AI systems introduce autonomous, non‑human identities that act at machine speed, creating ambiguous credentials and expanded attack surfaces. To secure these agents, a...

Disruptions to Digital Services and a Surge in Phishing Emails
In April, Estonia’s Information System Authority logged 1,138 cyber incidents that disrupted a range of public digital services, from health‑insurance prescriptions to digital signature platforms. A software error halted the Health Insurance Fund’s e‑prescription system for about 30 minutes, while...

Global Data Leaks up 22% in Early 2026, 259.4k Irish Accounts Exposed
Surfshark’s Q1 2026 data‑breach report shows global leaks jumped 22% year‑over‑year, with 210.3 million accounts compromised. The United States accounts for 29% of those breaches, while Ireland contributed 260 thousand exposed accounts, ranking 39th worldwide and fourth in Northern Europe since 2004....

Windows 11 Can Block Google Chrome's 4GB AI Model From Reinstalling Itself on Your PC — A Simple Registry Tweak...
Google Chrome and Microsoft Edge now download a 4 GB on‑device Gemini Nano AI model by default, prompting privacy and storage concerns. Windows 11 Pro introduces a Registry policy, GenAILocalFoundationalModelSettings, that lets administrators block or remove the model for both browsers. The setting...

ASIC Urges Financial Firms to Boost Cyber Defences
The Australian Securities and Investments Commission (ASIC) has issued an open letter urging all licensed financial firms to urgently strengthen cyber resilience in light of frontier artificial intelligence threats. ASIC stresses that AI‑driven attacks can expose vulnerabilities faster and at...

Pen Tests Show AI Security Flaws Far More Severe than Legacy Software Bugs
Penetration testing of AI and large language model (LLM) applications reveals a disproportionate share of high‑risk flaws. Cobalt’s 2026 State of Pentesting Report finds 32% of AI/LLM findings are high risk—about 2.5 times the 13% rate in traditional enterprise software—yet...

Your Refresh Plan Has a CVE Blind Spot
A healthcare client bought servers in 2017 and, due to COVID‑driven supply‑chain delays, extended the vendor’s end‑of‑life timeline to 2026 for software updates and 2028 for security patches. With new hardware now unavailable for up to a year and costs...

PCPJack Campaign Boots TeamPCP Off Compromised Machines
Security researchers have uncovered PCPJack, a new credential‑theft framework that first wipes traces of the notorious TeamPCP group before worming through exposed cloud environments. The worm targets Docker, Kubernetes, Redis, MongoDB, RayML and vulnerable web applications, stealing credentials for later...

Your Databases Are Being Watched – Just Not by You
The article warns that most enterprises leave databases unmonitored, allowing attackers to linger for an average 241 days before detection. This governance deficit fuels costly breaches and exposes firms to South African POPIA penalties of up to R10 million (≈$540 k) and average...

Snyk Integrates Claude to Advance AI-Native Application Security
Snyk has integrated Anthropic’s Claude large‑language model into its AI Security Platform, enabling automated discovery, prioritization, and developer‑ready remediation of vulnerabilities across code, dependencies, containers, and AI‑generated artifacts. The platform, called Evo, extends protection to AI models, agents, datasets, and...

City of London Calls for Tech-Led Fraud Fight
The City of London Corporation is urging technology firms to create stronger digital identity‑verification services to curb financial‑sector fraud. It proposes a voluntary, secure network that lets users verify once with a trusted provider and reuse that proof across multiple...

Securonix Launches AI Threat Research Agent and ThreatWatch Validation Tool
Securonix unveiled two new capabilities – the AI‑driven Threat Research Agent and the ThreatWatch validation tool – built on its ThreatQ platform. The Research Agent transforms raw threat intelligence into structured, role‑specific findings with source attribution, while ThreatWatch automatically generates...

OpenAI Tunes GPT-5.5-Cyber for More Permissive Security Workflows
OpenAI has begun a limited preview of GPT‑5.5‑Cyber, a more permissive variant of its latest GPT‑5.5 model, available only to verified cybersecurity professionals through the Trusted Access for Cyber program. The new tier relaxes restrictions on security‑related prompts, enabling authorized...

Does Shein Send Data to China? Irish Watchdog Investigates
The Irish Data Protection Commission has opened an investigation into Shein Ireland, the European hub of the fast‑fashion e‑commerce giant. Regulators suspect the retailer may have illegally transferred personal data of EU users to China, breaching GDPR rules. The probe...

Ransomware Group Takes Credit for Trellix Hack
RansomHouse, a ransomware‑as‑a‑service group, has claimed responsibility for the recent breach of Trellix’s source‑code repository. Trellix confirmed the intrusion but said its code release process appears untouched and no exploitation has been detected. The attackers posted screenshots of internal dashboards,...