
UAE Advances One of the World’s First National Post-Quantum Migration Programs
The United Arab Emirates announced one of the world’s first national post‑quantum migration programs, outlining a roadmap to transition critical government infrastructure to quantum‑resistant cryptography by 2028. The initiative follows a broader surge in quantum activity, including a $28 M+ angel round for Chinese startup Juliang Guangqi to industrialize superconducting quantum devices and NIST’s advancement of nine digital‑signature candidates to the third round of its post‑quantum standardization process. These developments signal accelerating global investment and policy focus on quantum‑ready security.

The AI Security Gap Nobody Wants to Admit Is Already Here
On March 31, 2026 Anthropic mistakenly published the full Claude Code source—about 512,000 lines across 1,906 files—to a public npm bucket, where it was quickly mirrored on GitHub. The leak exposed the AI agent's permission‑enforcement logic, hidden feature flags and references to an...

If You're Still Hanging on to This Classic Android File Explorer, You Need to Switch Now
ES File Explorer, once a staple Android file manager, was pulled from the Google Play Store in 2019 after investigations revealed ad‑fraud and intrusive advertising. The app’s later versions added aggressive ads and background activity, turning it into a security...

The US Blacklisted Anthropic as a Security Threat. Its Spy Agencies Are Using Claude Anyway.
The Pentagon has officially blacklisted Anthropic as a national‑security supply‑chain risk, yet the NSA continues to run Anthropic’s Claude model because a critical chip shortage leaves it with no viable alternative. The White House approved a secret $9 billion emergency package...

DORA Compliance Is Not Resilience: Why Financial Services Need Continuous Validation
The EU’s Digital Operational Resilience Act (DORA) took effect in January 2025, obligating major financial firms to conduct a Threat‑Led Penetration Test (TLPT) at least every three years. Mark Kuhr argues that this three‑year cadence is out of step with a...

Cyber-Star Wars: Securing Satellites and Critical Infrastructure
Space systems are now classified as critical infrastructure, making them prime targets for cyber‑attacks amid heightened geopolitical tensions such as Russia’s war in Ukraine and the Iran conflict. Attack vectors include DDoS, spoofing, supply‑chain malware, and command hijacking, with a...

‘Underminr’ Vulnerability Lets Attackers Hide Malicious Connections Behind Trusted Domains
Security researcher ADAMnetworks has identified a new CDN‑based vulnerability called Underminr, a variant of domain fronting that lets attackers present a trusted SNI and Host while the request is routed to a different tenant’s IP. The technique exploits mismatches between...

Dirty Frag, Copy Fail, Fragnesia: The Start of a Worrisome Linux Security Trend
A trio of Linux kernel vulnerabilities—Dirty Frag, Copy Fail and Fragnesia—have been disclosed within a week, illustrating how AI‑driven analysis can surface page‑cache bugs almost instantly after a fix. Linus Torvalds and other leaders note that AI‑generated findings are no...
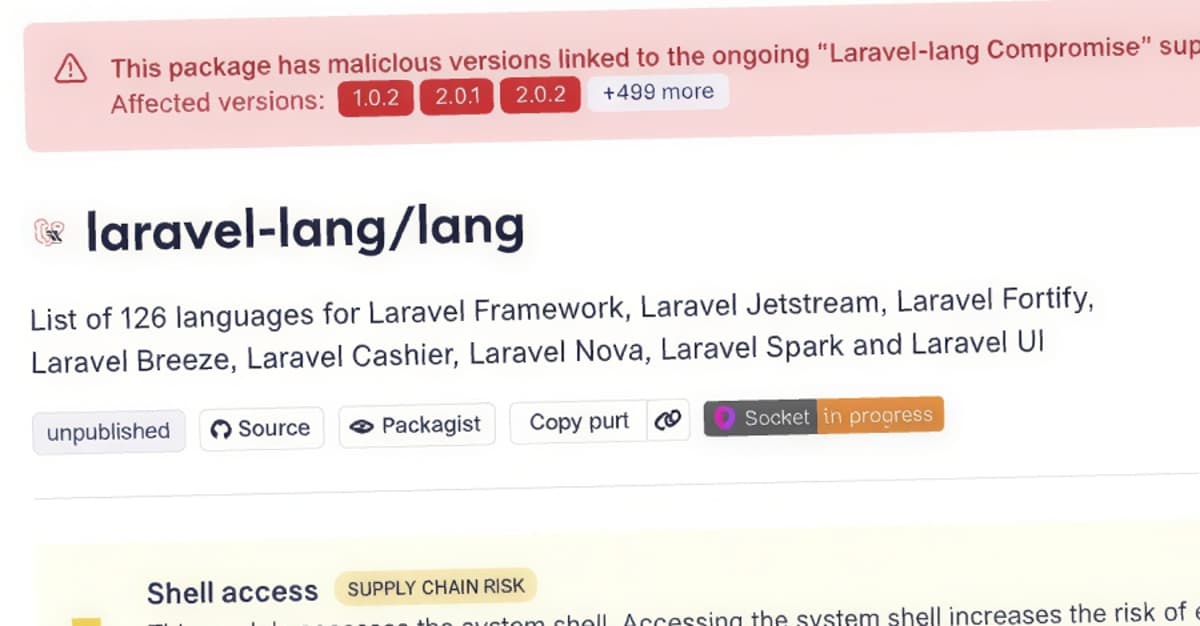
Laravel-Lang PHP Packages Compromised to Deliver Cross-Platform Credential Stealer
Researchers discovered a supply‑chain attack that compromised four Laravel‑Lang PHP packages by rewriting all existing Git tags to a malicious commit. The malicious src/helpers.php file is added to the Composer autoload files, causing automatic execution whenever a Laravel or other...

Google Leaks Details for Chromium Bug that Can Turn Browsers Into Bots
A long‑standing vulnerability in Chromium’s Service Worker and Background Fetch APIs allows malicious sites to keep a service worker alive indefinitely and run JavaScript across browser restarts. Reported three years ago by researcher Lyra Rebane, the flaw lets attackers hide background...

Valid Certificates, Stolen Accounts: How Attackers Broke Npm's Last Trust Signal
On May 19, attackers compromised a maintainer account to issue valid Sigstore certificates, allowing 633 malicious npm package versions to pass provenance verification. A day earlier, the Nx Console VS Code extension was hijacked, generating roughly 6,000 auto‑updates in under 40...

Data Sanitization Challenges Are Increasing in the AI Era
Blancco’s 2026 State of Data Sanitization Report warns that rising privacy regulations and AI adoption are reshaping end‑of‑life data management. While 94% of firms say they are confident in their sanitization processes, 38% still suffered data leaks, often from redeployed...

A Russian Speaker and Jailbroken Gemini Went on a Hacking Spree and Emptied at Least One MAGA Victim's Crypto Wallets
A Russian‑speaking solo threat actor leveraged a jailbroken Google Gemini model to orchestrate a sophisticated crypto‑fraud and credential‑theft campaign targeting MAGA and QAnon supporters. Between September 2025 and May 2026 the actor, known as bandcampro, built a Telegram channel with...
Middle East Malicious Infrastructure Report Highlights Concentration of C2 Servers
A Hunt.io study uncovered more than 1,350 command‑and‑control (C2) servers operating in 14 Middle Eastern nations, with Saudi Telecom Company (STC) alone responsible for over 72% of the activity. The servers span 98 providers, and the report highlights Turkish Telecom’s...

Even as AI Gets Better at Finding Digital Weak Spots, It Doesn’t Eliminate the Human Role in Cyber Conflict
Anthropic’s new AI model Mythos highlights how generative tools can scan code for zero‑day flaws faster than human analysts. Justin Miller, a cyber‑security professor at the University of Tulsa, argues that AI is a capability multiplier that speeds both attack...

Drupal Vulnerability in Hacker Crosshairs Shortly After Disclosure
Drupal warned that attackers are already probing the newly disclosed CVE‑2026‑9082, a highly critical SQL‑injection flaw in its database‑sanitization API. The vulnerability, which affects only PostgreSQL‑backed sites, was patched on May 20 but has triggered more than 15,000 exploitation attempts across...

Iran-Linked Hackers Target Key US, Allied Sectors with Sophisticated Spear-Phishing Messages
Iran‑backed hacking group Screening Serpens has launched a wave of spear‑phishing campaigns using six newly identified remote‑access trojans. The attacks focus on high‑value U.S. and Middle Eastern sectors, especially aerospace, defense and telecommunications, and employ highly personalized lures such as...
Christophe Pettus: Pgvector 0.8.2 and the Trouble With Parallel HNSW
pgvector 0.8.2 has been released to fix CVE‑2026‑3172, a heap buffer overflow that occurs during parallel HNSW index builds. The bug can leak data from other relations or crash the PostgreSQL backend. Many managed PostgreSQL services still run older pgvector...
Why CISA Accepting KEV Nominations Is So Important
The Cybersecurity & Infrastructure Security Agency (CISA) announced a new public nomination form for its Known Exploited Vulnerabilities (KEV) catalog, allowing vendors, researchers, and partners to submit exploitation data directly. The structured form replaces a simple email address, requiring CVE...

$20 per Zero-Day Is Already the WordPress Plugin Reality
Researchers from TrendAI and CHT Security demonstrated an AI‑driven pipeline that identified more than 300 critical zero‑day flaws across WordPress plugins in just 72 hours. The system combined static analysis, Docker provisioning, and Chrome DevTools verification, and each finding was...

5,561 GitHub Repositories Hit by Megalodon Supply Chain Attack in Six Hours
Cybersecurity firm SafeDep uncovered a rapid supply‑chain attack dubbed Megalodon that compromised 5,561 GitHub repositories within six hours on 18 May 2026, injecting 5,718 malicious code updates. The attackers created fake accounts and inserted hidden workflow files (.github/workflows/ci.yml) that act as dormant...

Most Data Breaches Start with a Stolen Password. Here’s How to Fix That
Data breaches still begin with stolen passwords, accounting for roughly 80% of web‑application incidents, according to Verizon’s 2024 report. The root cause is employee password reuse and insecure credential sharing, which traditional policies fail to stop. Proton Pass for Business...

Ubiquiti Patches Three Max Severity UniFi OS Vulnerabilities
Ubiquiti released security updates on May 22, 2026 that address three maximum‑severity vulnerabilities in UniFi OS, including improper access control, path traversal, and command injection. The patches also cover a critical command‑injection flaw (CVE‑2026‑33000) and a high‑severity information‑disclosure issue (CVE‑2026‑34911)....

Megalodon GitHub Attack Targets 5,561 Repos with Malicious CI/CD Workflows
Cybersecurity firm SafeDep uncovered the Megalodon campaign, which injected malicious GitHub Actions workflows into 5,561 repositories, pushing 5,718 commits within a six‑hour window on May 18, 2026. The workflows contain base64‑encoded bash payloads that harvest CI environment variables, cloud credentials (AWS, GCP,...

The Cyber Express Weekly Roundup: Supply Chain Breaches, AI Content Enforcement, And Event Disruption Attacks
The Cyber Express weekly roundup highlights a surge in distributed cyber threats, from a massive npm supply‑chain breach that compromised over 300 AntV packages to an attempted disruption of Vienna’s Eurovision event where nearly 500 attacks were blocked. The U.S....

Fake Gemini and Claude Code Sites Spread Infostealers Through SEO Poisoning
Security researchers at EclecticIQ uncovered a coordinated campaign that masquerades as Google Gemini’s CLI and Anthropic’s Claude Code installation pages. By leveraging SEO‑poisoning, the fake domains rank above legitimate results, directing developers to PowerShell‑based installers that deploy an in‑memory infostealer....

Shaun Thomas: Why Postgres Lacks Transparent Data Encryption
PostgreSQL remains the only major relational database without built‑in Transparent Data Encryption (TDE), even as Oracle, SQL Server, MySQL and MariaDB provide the feature. The open‑source community has wrestled for years with divergent threat models, engineering complexity, and the question...

Vulnerability Exploitation Overtakes Stolen Credentials in AI-Driven Cyberattacks
Verizon’s 19th Data Breach Investigations Report shows vulnerability exploitation now initiates 31% of cyber incidents, overtaking stolen credentials for the first time in two decades. Artificial intelligence is compressing the gap between vulnerability disclosure and active exploitation, shrinking response windows...

ITWeb TV: ‘Missing’ Basics Expose Cyber Vulnerabilities
South Africa is emerging as a prime target for global cyber attacks, with a Surfshark report estimating annual cyber‑crime losses of roughly R2.2 billion (about US$118 million). Ayanda Peta, chair of the Cloud Security Alliance South Africa, warned that a lack of...

Security Researcher: WordPress 7.0 Could Trigger Rush To Steal AI API Keys via @Sejournal, @Martinibuster
Security researcher Oliver Sild warns that WordPress 7.0 exposes AI API keys, sparking a potential rush by hackers to steal them. A bug in the AI integration setup form leaks keys via browser autofill, making credentials visible during screen sharing or...

Keepnet Contributes Voice and SMS Phishing Data to the 2026 Verizon DBIR
Keepnet’s voice and SMS phishing simulation data has been incorporated into Verizon’s 2026 Data Breach Investigations Report, marking the first DBIR edition to feature phone‑centric phishing at scale. The report records a median click rate of 2% for voice/SMS simulations...

Why Your AI Strategy Stops Where the PLC Starts: Hard Lessons From the OT Frontlines
C‑level executives are racing to embed AI in operational‑technology security, but the effort stalls because critical telemetry never reaches the models. Legacy devices—often an unpatched Windows 7 laptop that alone talks to protection relays—create a massive visibility gap. AI trained on...

Microsoft 365 Users Targeted by New Phishing Threat that Bypasses MFA
The FBI has identified a new Phishing‑as‑a‑Service platform, Kali365, that targets Microsoft 365 access tokens and bypasses multi‑factor authentication. First seen in April 2026, the service is distributed via Telegram and provides AI‑generated lures, campaign templates, and OAuth token‑capture tools. By exploiting...

Microsoft Patches Actively Exploited Defender Vulnerabilities Affecting Enterprise Systems
Microsoft disclosed active exploitation of two Defender flaws—CVE-2026-41091, a high‑severity privilege‑escalation bug, and CVE-2026-45498, a lower‑severity denial‑of‑service issue. Both vulnerabilities were confirmed in the wild and have been patched in Defender Antimalware Platform versions 1.1.26040.8 and 4.18.26040.7. A third flaw,...

Identity as the Primary Attack Surface: What Modern Breaches Are Really Exploiting
Modern breaches increasingly exploit identity rather than network perimeters. As enterprises migrate to cloud, SaaS, and hybrid work, authentication becomes the gatekeeper for financial systems, data, and admin controls. Attackers now rely on credential stuffing, OAuth consent phishing, and adversary‑in‑the‑middle...

GitHub Employee Device Breach Exposes Thousands of Internal Repositories
GitHub disclosed that attackers compromised an employee’s device and exfiltrated roughly 3,800 private repositories through a malicious Visual Studio Code extension. The breach was contained quickly; the affected endpoint was isolated and all credentials were rotated. Cyber‑criminal group TeamPCP claimed responsibility and...

EMEA Emerges as Global Hotspot for Financial Services DDoS Attacks
Akamai’s 2026 State of the Internet Security report reveals that financial services are now the most targeted sector for DDoS attacks, with median attack duration up 738% since 2024. The surge is driven by AI‑enabled botnets and hacktivist campaigns, especially...

China's Webworm Uses Discord, Microsoft Graphs to Hack EU Governments
China‑aligned APT group Webworm has pivoted from Asian targets to European government agencies, including Belgium, Italy, Serbia, Spain, Poland, and South Africa. In 2025 the group abandoned legacy malware for two novel backdoors—EchoCreep, which uses Discord, and GraphWorm, which exploits...

UK Cybersecurity Innovation SilentGlass Goes Global After Licensing Deal
The UK government has granted a global commercial licence for SilentGlass, a hardware‑based cyber‑security device originally created by the National Cyber Security Centre. The plug‑and‑play unit sits between a laptop and monitor to block video‑connection attacks, addressing a growing class...
MHCLG Launches CAF Support Fund
The Ministry of Housing, Communities and Local Government’s Local Digital team has unveiled a £6 million (about $7.7 million) Cyber Assessment Framework (CAF) Support Fund. The fund will provide grants to the 52 local councils that have completed a CAF self‑assessment, with...

Maritime Cyber Threats and AIS Assisted Collisions
Maritime cyber threats, especially GPS jamming and spoofing by U.S. and Russian militaries, are now routine, jeopardizing vessel navigation and prompting AIS‑assisted collisions. Insurers warn that even non‑malicious actions, such as a crew member’s phone malware, can cripple electronic chart...

Coro Joins Leader’s Marketplace
Leader has added Coro’s AI‑driven cyber security platform to its Australian Cloud marketplace, giving MSPs and reseller partners a unified solution for endpoint, email, cloud, and network protection. The modular platform lets partners deploy only the capabilities their customers need,...

Beware of Financial Scammers Wielding Deepfake Tech
Deepfake-enabled fraud has shifted from a novelty to a persistent corporate risk, with synthetic audio and video remaining in circulation for an average of 3.5 years. A voice clone of a German energy‑company CEO persisted nearly six years, causing a...

Google API Keys Remain Active After Deletion
Researchers at Aikido Security discovered that Google Cloud Platform API keys remain usable after deletion, with a median revocation window of about 16 minutes and a maximum of 23 minutes. The study showed wide variability across regions—some tests saw a...

Satoshi’s 1.1 Million Bitcoin and Millions More Can Be Saved From Quantum Attack, Says Expert
AmericanFortress unveiled a patent‑pending post‑quantum signature scheme that would protect existing crypto assets, including dormant wallets, via a backward‑compatible soft fork. The protocol aims to freeze and secure pre‑BIP32 Bitcoin addresses—such as Satoshi’s 1.1 million BTC and roughly 5 million dormant coins—while...
Microsoft Plans Significant Update to Windows Secure Boot
Microsoft is rolling out its first Secure Boot certificate update in 15 years, with the 2011‑based certificates set to expire between June 27 and October 2026. For Windows desktops, the fix requires a standard Windows Update plus a UEFI firmware...

Announcing Claude Compliance API Support with Cloudflare CASB
Cloudflare announced that its Cloud Access Security Broker (CASB) now integrates with Anthropic’s Claude Compliance API, giving enterprises direct visibility into Claude Enterprise and Platform usage from the Cloudflare dashboard. The integration surfaces DLP‑related findings for projects, chat files, messages,...

Americans Can’t Spot a Deepfake, and That’s a Business Crisis, Not Just a Consumer Problem
A Veriff‑Kantar 2026 survey of 3,000 adults in the U.S., U.K. and Brazil found Americans score just 0.07 on deep‑fake detection – essentially random guessing. While 63% of U.S. adults recognize the term “deepfake,” half claim confidence in spotting them,...

MFA Verifies Who Logged In. It Has No Idea What They Do Next.
Enterprises relying solely on multi‑factor authentication are vulnerable because once a user logs in, the session token is trusted indefinitely, allowing attackers to move laterally without triggering alerts. NOV’s CIO Alex Philips discovered this architectural blind spot and implemented rapid...
Deleted Google API Keys Remain Active up to 23 Minutes, Study Finds
Aikido Security discovered that Google API keys remain functional for up to 23 minutes after deletion, with an average lag of 16 minutes. The delay stems from eventual consistency across Google’s global authentication servers, allowing attackers to continue accessing enabled...