
13 Hidden Costs of Password-Based Authentication (With Real ROI Math)
Passwords impose hidden, multi‑million‑dollar costs that span IT support, security breaches, compliance fines and lost revenue. A single reset averages $70, while credential‑based breaches cost $4.9 M on average and SMS OTP delivery can exceed $100 K annually. The article shows that these expenses often dwarf the price of a passwordless solution, delivering a clear ROI in 12‑18 months. A simple worksheet lets CFOs quantify the annual “password tax” and build a business case for passkey‑based authentication.

Essent Reduces Contact Centre Technology Costs by 50%
Essent, the Netherlands’ largest energy supplier, partnered with Sabio Group to migrate its contact‑centre infrastructure to the cloud in under 12 weeks. The phased rollout eliminated critical incidents and cut technology costs by 50%. Agent workplace NPS jumped from +19...

From Patchwork to Platform: How Blue Cross Blue Shield Meets the Modernization Challenge
Blue Cross Blue Shield plans are confronting legacy technology debt and fragmented data silos, prompting a shift toward modular, cloud‑ready architectures. A HIMSS session outlined practical strategies—multicloud adoption, data unification, and robust governance—to boost agility and member experience. Speakers from...

Meta’s Compute Grab Continues with Agreement to Deploy Tens of Millions of AWS Graviton Cores
Meta announced a partnership with Amazon Web Services to add tens of millions of Graviton5 CPU cores—each chip packing 192 cores—to its AI compute portfolio, bolstering the Llama builder platform. The agreement expands Meta’s already diverse hardware ecosystem that includes...

VA Names OIG CIO, Taps Nominee for Department-Wide IT Chief
The Department of Veterans Affairs announced two senior technology appointments: Lance Jenkinson was named Deputy Assistant Inspector General for Management and Administration and CIO of the VA Office of the Inspector General, while the White House nominated Gary Shatswell as...

How France’s Tech Dependency Plan Could Influence ERP Decisions
France has launched a government‑wide program requiring ministries to map all technology dependencies on non‑European vendors, covering infrastructure, AI, databases and core systems. The Interministerial Directorate for Digital Affairs is spearheading the effort, with the Direction interministérielle du numérique (DINUM)...
The SaaS Mess: How Enterprises Lost Control Of Their Software
Composable ERP was hailed as a modular, LEGO‑like strategy, but five years later it has left enterprises tangled in fragmented SaaS applications and siloed data. The resulting complexity drives higher licensing and maintenance costs while increasing downtime risk. Gartner’s vision...

IHS Leaders Tie Cybersecurity Directly to Patient Care
At the 2026 Splunk GovSummit, Indian Health Service leaders declared cybersecurity a core component of patient care. Serving 2.7 million patients across 37 states, IHS ties security to clinical continuity, emphasizing real‑time monitoring and resilience in remote and urban facilities. The...

Delivering an Impactful 15-Minute Board Briefing
Cyber risk oversight has shifted to audit committees, now covering 79% of S&P 500 firms, up from 71.2% two years earlier. Board briefings are limited to 10‑15 minutes each quarter, forcing CISOs to move from data‑heavy dashboards to concise, business‑focused narratives....

McDonald’s US CIO to Depart, Successor Named
McDonald’s announced that U.S. CIO Valerie Ashbaugh will depart at the end of April after less than a year in the role, concluding a five‑year tenure at the fast‑food giant. Mustafa Husain, the former vice‑president of restaurant technology engineering, will...

OpenText and Google Target the Data Layer Gap Holding Back Enterprise Agentic AI
OpenText and Google Cloud announced an expanded partnership to deliver a full agentic AI stack focused on context engineering, data sovereignty, and open interoperability. The collaboration builds on OpenText's Aviator Studio, a no‑code platform that governs and connects enterprise data...

What Google’s “Unified Stack” Pitch at Cloud Next ‘26 Really Means for CIOs
At Cloud Next ’26 Google Cloud CEO Thomas Kurian unveiled a “unified stack” that stitches together custom TPUs, Gemini Enterprise, the Agentic Data Cloud and security services into a single AI operating fabric. The pitch positions the stack as a turnkey...

Schneider Electric Innovation Summit
Schneider Electric released an eBook summarizing insights from its 2025 Innovation Summit, highlighting how AI‑driven data centers are being reshaped. The publication emphasizes megawatt‑scale racks and 800 VDC power architectures as a response to soaring compute loads. It also details the...
Glasswing Secured the Code. The Rest of Your Stack Is Still on You
Anthropic’s Project Glasswing, showcased by the Mythos Preview model, uncovered a 16‑year‑old FFmpeg vulnerability that five million conventional scans missed. The AI’s ability to read code intent, rather than merely enumerate patterns, marks a shift from signature‑based tools toward understanding‑driven security. While...

Reimagining the Smart Hospital, Cleveland Clinic Style
Cleveland Clinic’s chief information officer, Sarah Hatchett, says a truly smart hospital hinges on orchestrating a seamless, longitudinal patient journey rather than simply installing the latest devices. At HIMSS26, the health system showcased how AI‑driven analytics pull in pre‑admission data...

Meta Signs Multibillion-Dollar Deal With Amazon to Use Its CPU Chips for AI
Meta Platforms has inked a multiyear, multibillion‑dollar agreement with Amazon Web Services to run tens of millions of AWS Graviton5 CPU cores for its AI agents and related workloads. The contract, lasting three to five years, makes Meta one of...

Cybersecurity in the AI Age: Speed and Trust Define Resilience
Cybersecurity now hinges on speed and trust as AI reshapes threat dynamics. CrowdStrike reports e‑crime breakout time has collapsed from 582 minutes in 2019 to just 29 minutes today, forcing organizations to detect and contain attacks within half an hour....
The AI Architecture Decision CIOs Delay Too Long — and Pay for Later
Enterprise AI initiatives often appear successful early, but CIOs frequently postpone revisiting the underlying architecture as systems scale. This delay creates cost volatility, longer security and compliance reviews, and growing uncertainty about system behavior, even though dashboards remain green. The...

IT Reskilling: The Pressing CIO Imperative
CIOs are now the architects of enterprise IT reskilling, targeting fast‑evolving domains such as generative AI, cybersecurity, data analytics and automation while also emphasizing soft skills like communication and leadership. Leaders argue that internal upskilling delivers far higher ROI than...

Med Tech Solutions Appoints Dan Stoke as Chief Growth Officer and Matt Trevorrow as Chief Information Officer
Med Tech Solutions (MTS) announced the appointment of Dan Stoke as Chief Growth Officer and Matt Trevorrow as Chief Information Officer. Both executives bring senior leadership experience from major healthcare‑IT firms such as CTG, NTT Data, HP and Allscripts. Their hires are aimed...

EXL Picks Sharon White to Lead APAC Data Management
EXL announced the appointment of Sharon White as head of APAC data‑management solutions, based in Sydney. White will oversee client delivery in Australia and New Zealand, drive data‑modernisation initiatives, and expand the EXLdata.ai suite developed with Databricks. She arrives with more...

Weak Security Means Attackers Could Disable All of a City's Public EV Chargers
Researchers at Black Hat Asia demonstrated that rented IoT infrastructure—such as public EV chargers and shared e‑bikes—often sacrifices security for convenience. Hetian Shi of Tsinghua University uncovered shared authentication keys, exposed debug ports, and backend services that fail to verify users. Using his...

Data Lakes Do Not Leak, Permissions Do
Modern analytics platforms are failing not because data lakes store too much information, but because permission models lag behind platform ambition. Organizations often apply broad, shared‑folder style access for convenience, which becomes a governance nightmare as the lake expands to...

When Mythos Finds Thousands of Zero-Days, EU Regulators Won’t Wait for Your SOC to Catch Up
Mythos will disclose hundreds to thousands of zero‑day findings at once, instantly triggering reporting obligations under the EU’s NIS2, Cyber Resilience Act (CRA) and Digital Operational Resilience Act (DORA). A typical 10‑analyst SOC can process roughly 320 findings in 24 hours,...

States Deploy Desktop as a Service To Standardize Endpoints and Boost Security
State IT leaders in Kansas, Indiana and New Mexico are rolling out Desktop as a Service (DaaS) platforms to centralize device provisioning, patching and security across thousands of endpoints. Kansas is deploying Tanium Endpoint Management on Dell hardware, while Indiana...

Tackling Hybrid IT Infrastructure Challenges in the Government Sector
Federal agencies are wrestling with sprawling hybrid IT environments that combine aging on‑premises systems with cloud services. With an annual $130 billion IT spend, budget constraints—highlighted by 28% of leaders—limit security upgrades and modernization. Only 6% of agencies have completed a...

Why Clinical Care Resilience Is a Top Priority in Healthcare
Healthcare leaders warn that cyber‑threats and system failures can cripple clinical operations, making care‑resilience a top priority. Recent ransomware incidents at Michigan Medicine, University of Vermont Health Network, and Children’s National illustrate the need for cross‑departmental planning and frequent security...

Clorox Shows What SAP S/4HANA Transformations Require Before 2027
The Clorox Company completed a five‑year, $580 million SAP S/4HANA transformation, treating it as an enterprise reinvention rather than a simple system swap. Early decisions around strategic framing, realistic benchmarking, and a built‑in adoption network shaped the program’s stability after go‑live....

Collaboration Security and Governance Must Be Proactive
Collaboration platforms have become prime attack vectors as enterprises adopt a growing suite of messaging, video, and AI‑enhanced tools. Generative AI now creates meeting transcripts, summaries, and even presentations, expanding the data surface that must be protected. A proactive governance...

South Africa Planning Big Overhaul of Public Sector IT
South Africa’s Department of Communications & Digital Technologies has formalised a three‑year plan to overhaul the State IT Agency (Sita), with quarterly milestones beginning in 2026 and a draft business model due by March 2027. The overhaul follows an auditor‑general...

Navigating Federal Cloud Adoption
Federal health leaders are accelerating hybrid cloud adoption to boost scalability, security, and mission delivery. Former HHS CISO La Monte Yarborough and CMS infrastructure director Wade Zarriello highlighted how cloud strategies have evolved and outlined the next steps for agencies....

The Trillion-Dollar AIDC Boom Gets Real: Omdia Maps the Path From Megaclusters to Microgrids
Omdia raised its 2030 data‑center investment forecast beyond $1.6 trillion, driven by AI demand from hyperscalers, tier‑2 cloud providers, and enterprises. AI workloads are additive, pushing rack power density from roughly 20 kW today toward a potential 2 MW by the end of...

Hybrid Clouds Have Two Attack Surfaces and You’re Not Paying Enough Attention to Either
Researchers at Black Hat Asia uncovered four critical CVEs in Microsoft’s Windows Admin Center (WAC), exposing a two‑way attack surface for hybrid cloud environments. The flaws allow malicious actors to drop payloads on on‑premises WAC installations and forge proof‑of‑possession tokens...

“Africa Is the Next Industrial Growth Frontier” — AVEVA’s Jesus Hernandez on AI, Data, and Digital Transformation
AVEVA is positioning Africa as the next frontier for industrial growth, emphasizing the continent’s massive energy‑access gap and the need for digital infrastructure. Senior Vice President Jesus Hernandez highlighted AVEVA’s CONNECT cloud platform, which can be deployed in days to...

How the EU’s NIS2 Directive Is Changing How CIOs Think About Digital Infrastructure
The EU’s NIS2 directive reframes cybersecurity risk as an ecosystem issue, forcing CIOs to look beyond internal controls to the full supply‑chain of cloud providers, network operators and software vendors. It expands the definition of resilience to include how interconnected...

The Great Workload Reshuffle: Choices for AI and Analytics
IT leaders are moving from a simple cloud‑first mindset to a workload‑to‑environment alignment strategy as AI, real‑time analytics, and data‑intensive apps proliferate. The model matches each AI or analytics workload to public cloud, on‑premises, or hybrid environments based on performance,...
New Framework Allows EU Firms to Check if 'Sovereign' Cloud Services Are Truly Sovereign
The Cloud Infrastructure Services Providers in Europe (CISPE) has unveiled a Sovereign and Resilient Cloud Services Framework that issues certification badges to verify a provider’s data‑control claims. The scheme distinguishes "sovereign" services, which are owned and operated entirely within the...

Data Debt Will Cripple Your AI Strategy if Left Unaddressed
AI success hinges on clean data, yet many enterprises carry years of data debt from legacy practices, mergers, and ad‑hoc solutions. IDC warns that postponing remediation could increase AI project failure rates by 50 percent by 2027. CIOs are urged to...

H&M Appoints Former Inditex Executive as Chief Information Officer
H&M announced the appointment of Diego Teijeiro Ruiz, a veteran of Inditex, as its new chief information officer effective May 25. Ruiz spent two decades at the Spanish fast‑fashion giant, most recently serving as global chief data and analytics officer. He will report...

SOCs Drowning in Alerts Despite Tool Investment
Security operations centers (SOCs) are overwhelmed by the sheer volume of daily alerts, outpacing analysts' ability to manually enrich and contextualize them. The bottleneck stems from raw alert generation, not a lack of telemetry, leading to longer dwell times and...

Trump Nominates Third VA CIO Since the Start of His Administration
President Donald Trump nominated Gary Shatswell as the Department of Veterans Affairs chief information officer and assistant secretary for information and technology, marking the third White House pick for the Senate‑confirmed role this administration. Shatswell, a senior advisor to VA...

CISA Director Pick Sean Plankey Withdraws His Nomination
Sean Plankey, the long‑sidelined nominee for CISA director, formally asked President Trump to withdraw his nomination after 13 months of Senate deadlock. The move follows the recent Senate confirmation of DHS Secretary MarkWayne Mullin, heightening pressure for a permanent CISA...

AI Demand Is Forcing a Rethink of Data Center Power, Cooling
AI’s rapid expansion is straining data‑center power and cooling infrastructure, prompting operators to redesign projects mid‑construction. At the Data Center World conference, Aligned Data Centers reported a 50% power increase request on an ongoing build, while Omdia warned of supply‑chain...

How To Evaluate Whether HCI Is Right for Your State or Local Government Organization
State and local government IT leaders are weighing hyper‑converged infrastructure (HCI) as a way to modernize data centers while meeting compliance, budget and sovereignty constraints. HCI bundles compute, storage and networking into a single, software‑defined platform that mimics cloud‑like elasticity...

The Role of Cloud-Native Infrastructure in Payments Modernization
Banks are racing to modernize payments, but legacy systems hinder real‑time processing, increase fraud exposure, and demand costly integrations. A webinar hosted by FIS and AWS highlighted the FIS Money Movement Hub, a cloud‑native solution built on AWS that promises...

Hackers Impersonate IT Help Desk on Microsoft Teams to Gain Access, Steal Data
Microsoft reports a rise in social‑engineering attacks that use Teams chats to impersonate IT help‑desk staff. Hackers request remote‑support sessions via Quick Assist, then leverage DLL sideloading and legitimate tools to infiltrate networks. The method bypasses traditional email‑focused defenses and...
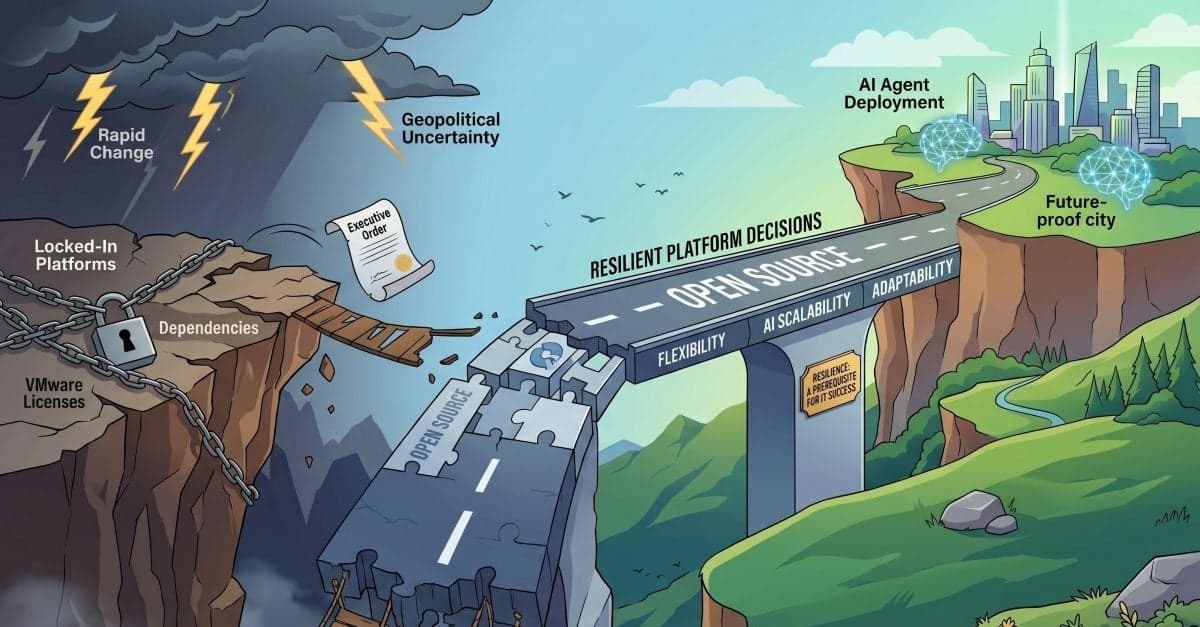
SUSE CTO: IT Teams Need to Become More Resilient in the Face of Rapid Change
At SUSECON 2026, CTO Dr. Thomas Di Giacomo warned that IT teams must prioritize resilient platform choices as rapid licensing shifts, geopolitical uncertainty, and AI adoption accelerate. He urged leaders to move toward open‑source stacks to avoid vendor lock‑in and to design...

Data Center World 2026: AI Pushes Infrastructure to New Limits
At Data Center World 2026, leaders from Oracle, Nvidia and Google warned that AI is forcing a fundamental redesign of data‑center infrastructure. Facilities must now accommodate two distinct workload patterns—massive GPU‑driven training clusters and distributed inference services—while supporting rack power...

Haleon Selects SAP Solutions to Accelerate Growth
Haleon, the global consumer‑health leader, has chosen SAP Business Suite to modernize its digital backbone and embed artificial intelligence across core functions. The move will consolidate finance, supply‑chain, HR and sales processes into a single, real‑time platform, replacing fragmented legacy...

Red Hat Digital Sovereignty Take: Red Hat Confirmed Sovereign Support
Red Hat announced the general availability of Red Hat Confirmed Sovereign Support (RHCSS), a premium support service designed to keep all diagnostics, logs and communications within a customer’s chosen jurisdiction, initially the European Union. The offering builds on Red Hat’s...